Android 5.0以下版本(API 21以下),系统默认没有开启TLS协议,因此如果直接使用OKHTTP请求HTTPS链接,会出现SSL超时的问题。
先来看下SSL在android版本中支持的情况:
Android在5.0的行为变更里面提到:
https://developer.android.google.cn/about/versions/android-5.0-changes#ssl
TLS/SSL 默认配置变更 Android 5.0 针对 HTTPS 和其他 TLS/SSL 通信引入了对应用使用的默认 TLS/SSL。
配置的变更:
TLSv1.2 和 TLSv1.1 协议现已启用, AES-GCM (AEAD) 加密套件现已启用, MD5、3DES、导出和静态密钥ECDH 加密套件现已停用, 首选使用 Forward Secrecy 加密套件(ECDHE 和 DHE)。
在下面列出的少数情况下,这些变更可能会导致 HTTPS 或 TLS/SSL 连接断开。
请注意,来自 Google Play 服务的安全性 ProviderInstaller 自 Android 2.3 开始就已在Android 平台版本上提供这些变更。
Android5.0开始默认启用了TLSv1.1和TLSv1.2,但是从Android4.1开始TLSv1.1和TLSv1.2其实就被支持了,只是默认没有启用而已。
我们最常用到的几种协议是SSLv3、TLSv1、TLSv1.1和TLSv1.2,解决上面两个问题要搞清楚的是这几个协议在Android系统中被支持的情况和被启用的情况,然后我们结合minSdkVersion和targetSdkVersion来选择协议即可,不同版本的Android系统对上述协议的支持情况:
客户端(SSLSocket)的支持情况:
| 协议 | 被支持(Api级别) | 被启用(Api级别) |
|---|---|---|
| SSLv3 | 1–25 | 1–22 |
| TLSv1 | 1+ | 1+ |
| TLSv1.1 | 16+ | 20+ |
| TLSv1.2 | 16+ | 20+ |
服务端(SSLServerSocket)的支持情况:
| 协议 | 被支持(Api级别) | 被启用(Api级别) |
|---|---|---|
| SSLv3 | 1–25 | 1–22 |
| TLSv1 | 1+ | 1+ |
| TLSv1.1 | 16+ | 16+ |
| TLSv1.2 | 16+ | 16+ |
因此若要支持android4.4的设备,就要开启TLSv1.1和TLSv1.2。
废话不多说,先上代码:
//5.0以下,开启TLS
if (Build.VERSION.SDK_INT < Build.VERSION_CODES.LOLLIPOP) {
//builder为OKHTTPBuilder
builder.sslSocketFactory(new TLSSocketFactory(trustAllCert), trustAllCert);
}
定义好证书,忽略证书
private static X509TrustManager trustAllCert = new X509TrustManager() {
@Override
public void checkClientTrusted(java.security.cert.X509Certificate[] chain, String authType) throws CertificateException {
}
@Override
public void checkServerTrusted(java.security.cert.X509Certificate[] chain, String authType) throws CertificateException {
}
@Override
public java.security.cert.X509Certificate[] getAcceptedIssuers() {
return new java.security.cert.X509Certificate[]{};
}
};
然后我们看看这个自定义的TLSSocketFactory,里面开启了TLS
package com.example.tests.base;
import java.io.IOException;
import java.net.InetAddress;
import java.net.Socket;
import java.net.UnknownHostException;
import java.security.GeneralSecurityException;
import java.util.Arrays;
import java.util.HashSet;
import java.util.LinkedList;
import java.util.List;
import javax.net.ssl.SSLContext;
import javax.net.ssl.SSLSocket;
import javax.net.ssl.SSLSocketFactory;
import javax.net.ssl.X509TrustManager;
// Android 5.0+ (API level21) provides reasonable default settings
// but it still allows SSLv3
// https://developer.android.google.cn/about/versions/android-5.0-changes.html#ssl
public class TLSSocketFactory extends SSLSocketFactory {
private SSLSocketFactory defaultFactory;
static String protocols[] = null, cipherSuites[] = null;
static {
try {
SSLSocket socket = (SSLSocket) SSLSocketFactory.getDefault().createSocket();
if (socket != null) {
/* set reasonable protocol versions */
// - enable all supported protocols (enables TLSv1.1 and TLSv1.2 on Android <5.0)
// - remove all SSL versions (especially SSLv3) because they‘re insecure now
List<String> protocols = new LinkedList<>();
for (String protocol : socket.getSupportedProtocols())
if (!protocol.toUpperCase().contains("SSL"))
protocols.add(protocol);
TLSSocketFactory.protocols = protocols.toArray(new String[protocols.size()]);
/* set up reasonable cipher suites */
//if (Build.VERSION.SDK_INT < Build.VERSION_CODES.LOLLIPOP) {
// choose known secure cipher suites
List<String> allowedCiphers = Arrays.asList(
// TLS 1.2
"TLS_RSA_WITH_AES_256_GCM_SHA384",
"TLS_RSA_WITH_AES_128_GCM_SHA256",
"TLS_ECDHE_ECDSA_WITH_AES_128_CBC_SHA256",
"TLS_ECDHE_ECDSA_WITH_AES_128_GCM_SHA256",
"TLS_ECDHE_ECDSA_WITH_AES_256_GCM_SHA384",
"TLS_ECDHE_RSA_WITH_AES_128_CBC_SHA256",
"TLS_ECHDE_RSA_WITH_AES_128_GCM_SHA256",
// maximum interoperability
"TLS_RSA_WITH_3DES_EDE_CBC_SHA",
"TLS_RSA_WITH_AES_128_CBC_SHA",
// additionally
"TLS_RSA_WITH_AES_256_CBC_SHA",
"TLS_ECDHE_ECDSA_WITH_3DES_EDE_CBC_SHA",
"TLS_ECDHE_ECDSA_WITH_AES_128_CBC_SHA",
"TLS_ECDHE_RSA_WITH_3DES_EDE_CBC_SHA",
"TLS_ECDHE_RSA_WITH_AES_128_CBC_SHA");
List<String> availableCiphers = Arrays.asList(socket.getSupportedCipherSuites());
// take all allowed ciphers that are available and put them into preferredCiphers
HashSet<String> preferredCiphers = new HashSet<>(allowedCiphers);
//留下系统支持的协议
preferredCiphers.retainAll(availableCiphers);
/* For maximum security, preferredCiphers should *replace* enabled ciphers (thus disabling
* ciphers which are enabled by default, but have become unsecure), but I guess for
* the security level of DAVdroid and maximum compatibility, disabling of insecure
* ciphers should be a server-side task */
// add preferred ciphers to enabled ciphers
HashSet<String> enabledCiphers = preferredCiphers;
enabledCiphers.addAll(new HashSet<>(Arrays.asList(socket.getEnabledCipherSuites())));
TLSSocketFactory.cipherSuites = enabledCiphers.toArray(new String[enabledCiphers.size()]);
//}
}
} catch (IOException e) {
throw new RuntimeException(e);
}
}
public TLSSocketFactory(X509TrustManager tm) {
try {
SSLContext sslContext = SSLContext.getInstance("TLS");
sslContext.init(null, (tm != null) ? new X509TrustManager[]{tm} : null, null);
defaultFactory = sslContext.getSocketFactory();
} catch (GeneralSecurityException e) {
throw new AssertionError(); // The system has no TLS. Just give up.
}
}
private void upgradeTLS(SSLSocket ssl) {
// Android 5.0+ (API level21) provides reasonable default settings
// but it still allows SSLv3
// https://developer.android.com/about/versions/android-5.0-changes.html#ssl
if (protocols != null) {
ssl.setEnabledProtocols(protocols);
}
//if (Build.VERSION.SDK_INT < Build.VERSION_CODES.LOLLIPOP && cipherSuites != null) {
ssl.setEnabledCipherSuites(cipherSuites);
//}
}
@Override
public String[] getDefaultCipherSuites() {
return cipherSuites;
}
@Override
public String[] getSupportedCipherSuites() {
return cipherSuites;
}
@Override
public Socket createSocket(Socket s, String host, int port, boolean autoClose) throws IOException {
Socket ssl = defaultFactory.createSocket(s, host, port, autoClose);
if (ssl instanceof SSLSocket)
upgradeTLS((SSLSocket) ssl);
return ssl;
}
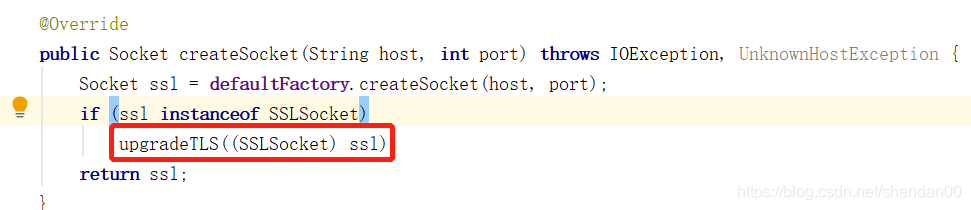
@Override
public Socket createSocket(String host, int port) throws IOException, UnknownHostException {
Socket ssl = defaultFactory.createSocket(host, port);
if (ssl instanceof SSLSocket)
upgradeTLS((SSLSocket) ssl);
return ssl;
}
@Override
public Socket createSocket(String host, int port, InetAddress localHost, int localPort) throws IOException, UnknownHostException {
Socket ssl = defaultFactory.createSocket(host, port, localHost, localPort);
if (ssl instanceof SSLSocket)
upgradeTLS((SSLSocket) ssl);
return ssl;
}
@Override
public Socket createSocket(InetAddress host, int port) throws IOException {
Socket ssl = defaultFactory.createSocket(host, port);
if (ssl instanceof SSLSocket)
upgradeTLS((SSLSocket) ssl);
return ssl;
}
@Override
public Socket createSocket(InetAddress address, int port, InetAddress localAddress, int localPort) throws IOException {
Socket ssl = defaultFactory.createSocket(address, port, localAddress, localPort);
if (ssl instanceof SSLSocket)
upgradeTLS((SSLSocket) ssl);
return ssl;
}
}
里面是在createSocket时,更新了协议
private void upgradeTLS(SSLSocket ssl) {
if (protocols != null) {
ssl.setEnabledProtocols(protocols);
}
if (cipherSuites != null) {
ssl.setEnabledCipherSuites(cipherSuites);
}
}
这样就可以请求HTTPS啦。








 本文解析了Android5.0以下版本中HTTPS请求出现SSL超时的问题,详细介绍了TLS协议在不同Android版本中的支持与启用情况,并提供了自定义TLS Socket Factory的代码实现,确保在低版本Android中正确开启TLSv1.1和TLSv1.2。
本文解析了Android5.0以下版本中HTTPS请求出现SSL超时的问题,详细介绍了TLS协议在不同Android版本中的支持与启用情况,并提供了自定义TLS Socket Factory的代码实现,确保在低版本Android中正确开启TLSv1.1和TLSv1.2。

















 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








