生成的公钥私钥格式是固定的,秘钥中间无空格无换行,秘钥末尾也空格无换行。
公钥长这样,一般比较短。
私钥长这样,一般比较长。
2.使用公钥加密
import base64
from Crypto.PublicKey import RSA
from Crypto.Cipher import PKCS1\_v1\_5 as Cipher\_pkcs1\_v1\_5
# rsa加密
def rsa\_encrypt(message):
public_key = """-----BEGIN PUBLIC KEY-----
MIGfMA0GCSqGSIb3DQEBAQUAA4GNADCBiQKBgQCfgDPRwaAYZFyNg7EyjMZOnjIR
vPPPu4sC6Iu25SDK9z6aE/yKwNSXI4JF/7gsFlXpV8rjB/SfIjNAunHy0++2djAT
1aWJYZSTujBkPblqR/NxRTilTwoc/oRjLHLF3RuoPOIL4on303Uc9Jgzj1CKbIDU
SSk4+gy2rfs2SUZ/uwIDAQAB
-----END PUBLIC KEY-----"""
rsa_key = RSA.importKey(public_key)
cipher = Cipher\_pkcs1\_v1\_5.new(rsa_key) # 创建用于执行pkcs1_v1_5加密或解密的密码
cipher_text = base64.b64encode(cipher.encrypt(message.encode("utf-8")))
return cipher_text.decode("utf-8")
if __name__ == "\_\_main\_\_":
message = "Hello, 你好, 这是一段RSA加密测试代码!"
result = rsa\_encrypt(message)
print(result)
跑一下看看结果:
jVzxl5vJ9OsDHqii/uPTCoujxSNFQOBOIvPDno9er6OcMgPhnbqfjnoEfLCSndghPT9x5vUKTC/jy8MK8TezmUVJSho9AVRi/Z3GKGjMXWFRTOfe18K6Ml6U0GaZGiacHZkIG1XOKTQs0HDbY1WhBzeMIakpsqgBEAoU+9wmkpo=
再跑一下看看结果:
OdLiI6XPqXAQKbE9t3GX4NjFArQOp6winRSV8xVaEcKm5NstgFD+e+iTZUSLGJrrdys3Ah7+bMW2sa6R3s8Sly3JSDyHVae5fhsKQ7/ouYFFXZf6Umj3BbE5Mykf6L9DM5U4fp2z5ZJ9EyAfXel8t84xIWpRnt8Ym6UOg+JFW8A=
对比两次你会发现,这里每次使用公钥加密后的结果都不一致,跟对数据的padding即填充有关。
3.使用私钥解密
import base64
from Crypto.PublicKey import RSA
from Crypto.Cipher import PKCS1\_v1\_5 as Cipher\_pkcs1\_v1\_5
# rsa解密
def rsa\_decrypt(cipher_text):
private_key = """-----BEGIN RSA PRIVATE KEY-----
MIICWwIBAAKBgQCfgDPRwaAYZFyNg7EyjMZOnjIRvPPPu4sC6Iu25SDK9z6aE/yK
wNSXI4JF/7gsFlXpV8rjB/SfIjNAunHy0++2djAT1aWJYZSTujBkPblqR/NxRTil
Twoc/oRjLHLF3RuoPOIL4on303Uc9Jgzj1CKbIDUSSk4+gy2rfs2SUZ/uwIDAQAB
AoGAAiZ0zGGbWmjT9JZvZ5qNO9cXHrUY5laFZ7sh0wvgtsvBfMtDLs2tsAHrCi2J
2pJMgzJLSmc7jX+lCDzbN2ZTB3Gz57jhx8ytvOZQod2MlEA52oUQGWeIim91hWYW
TKF8EoaQMfjUGzKXcZHjkPbZbajRFoad9+8w779jpDVJ/QkCQQC3Gd+cR1d0PI3L
/roRRVJKessFk4upqxbRTvqbD5S0pPQjOmzHEUwhluyKJJXfdBuwMbZKfBhO/FdI
fpe+m375AkEA3wDtuuNuNVZoJIOdFP/QeglPx8vKyzNHqWHITRels+wyZRKIEJU0
QfseNa0s2egqSDCX7EdDZIuujO0ERDM9UwJAGcVCe7Ru0qVTL8sCVTv0gRcXTAmg
Npkl9P+wtfJTc7ljwzGN7da5aGDdmfPcRD8LRpk4lvMwWK2be1CV+vXXwQJAfKQy
O6DeemVfM/l0FMaeqXcG5m8bW9O/nAaRQ7WR4iyERkXDUzFx0ecfjXTLesfuygaP
A3sZSdtgplfbaJsTDQJAdg5IvgiGOksvjvOf5wr3vHy0v0na/pMJVLol7t0GXFtj
LHntk5bjwJVx/ltaFSR/zG8nM7zASpid3B9BH3H5qA==
-----END RSA PRIVATE KEY-----"""
decode_text = base64.b64decode(cipher_text)
cipher = Cipher\_pkcs1\_v1\_5.new(RSA.importKey(private_key)) # 创建用于执行pkcs1_v1_5加密或解密的密码
decrypt_text = cipher.decrypt(decode_text, b"rsa")
return decrypt_text.decode("utf-8")
if __name__ == "\_\_main\_\_":
result = "OdLiI6XPqXAQKbE9t3GX4NjFArQOp6winRSV8xVaEcKm5NstgFD+e+iTZUSLGJrrdys3Ah7+bMW2sa6R3s8Sly3JSDyHVae5fhsKQ7/ouYFFXZf6Umj3BbE5Mykf6L9DM5U4fp2z5ZJ9EyAfXel8t84xIWpRnt8Ym6UOg+JFW8A="
message = rsa\_decrypt(result)
print(message)
运行结果:
Hello, 你好, 这是一段RSA加密测试代码!
可以看到,和加密前的数据一模一样。
4.使用私钥加签
import base64
from Crypto.Hash import SHA
from Crypto.PublicKey import RSA
from Crypto.Signature import PKCS1\_v1\_5 as Signature\_pkcs1\_v1\_5
# 私钥加签名
def rsa\_encrypt(message):
private_key = """-----BEGIN RSA PRIVATE KEY-----
MIICWwIBAAKBgQCfgDPRwaAYZFyNg7EyjMZOnjIRvPPPu4sC6Iu25SDK9z6aE/yK
wNSXI4JF/7gsFlXpV8rjB/SfIjNAunHy0++2djAT1aWJYZSTujBkPblqR/NxRTil
Twoc/oRjLHLF3RuoPOIL4on303Uc9Jgzj1CKbIDUSSk4+gy2rfs2SUZ/uwIDAQAB
AoGAAiZ0zGGbWmjT9JZvZ5qNO9cXHrUY5laFZ7sh0wvgtsvBfMtDLs2tsAHrCi2J
2pJMgzJLSmc7jX+lCDzbN2ZTB3Gz57jhx8ytvOZQod2MlEA52oUQGWeIim91hWYW
TKF8EoaQMfjUGzKXcZHjkPbZbajRFoad9+8w779jpDVJ/QkCQQC3Gd+cR1d0PI3L
/roRRVJKessFk4upqxbRTvqbD5S0pPQjOmzHEUwhluyKJJXfdBuwMbZKfBhO/FdI
fpe+m375AkEA3wDtuuNuNVZoJIOdFP/QeglPx8vKyzNHqWHITRels+wyZRKIEJU0
QfseNa0s2egqSDCX7EdDZIuujO0ERDM9UwJAGcVCe7Ru0qVTL8sCVTv0gRcXTAmg
Npkl9P+wtfJTc7ljwzGN7da5aGDdmfPcRD8LRpk4lvMwWK2be1CV+vXXwQJAfKQy
O6DeemVfM/l0FMaeqXcG5m8bW9O/nAaRQ7WR4iyERkXDUzFx0ecfjXTLesfuygaP
A3sZSdtgplfbaJsTDQJAdg5IvgiGOksvjvOf5wr3vHy0v0na/pMJVLol7t0GXFtj
LHntk5bjwJVx/ltaFSR/zG8nM7zASpid3B9BH3H5qA==
-----END RSA PRIVATE KEY-----"""
rsa_key = RSA.importKey(private_key)
signer = Signature\_pkcs1\_v1\_5.new(rsa_key)
digest = SHA.new()
digest.update(message.encode("utf-8"))
sign = signer.sign(digest)
signature = base64.b64encode(sign)
return signature.decode("utf-8")
if __name__ == "\_\_main\_\_":
message = "Hello, 你好, 这是一段RSA加密测试代码!"
signature = rsa\_encrypt(message)
print(signature)
跑一次:
ai3x9IMY+UQysZ+KNlnXsUi29ykqvtOUue6kdysFXvdnviQXKKDb6phGzd1mZEHYOTh81HiB6kS/vN93PRRDpPwCsKxbkB3SPjQnM/we2cZnZGK/bFUXoulL/a0V86UKEwL8vqRMNyDn1zrv9YwhvblTzdu8ywkawXuH6O/8SRw=
再跑一次:
**自我介绍一下,小编13年上海交大毕业,曾经在小公司待过,也去过华为、OPPO等大厂,18年进入阿里一直到现在。**
**深知大多数Python工程师,想要提升技能,往往是自己摸索成长或者是报班学习,但对于培训机构动则几千的学费,着实压力不小。自己不成体系的自学效果低效又漫长,而且极易碰到天花板技术停滞不前!**
**因此收集整理了一份《2024年Python开发全套学习资料》,初衷也很简单,就是希望能够帮助到想自学提升又不知道该从何学起的朋友,同时减轻大家的负担。**




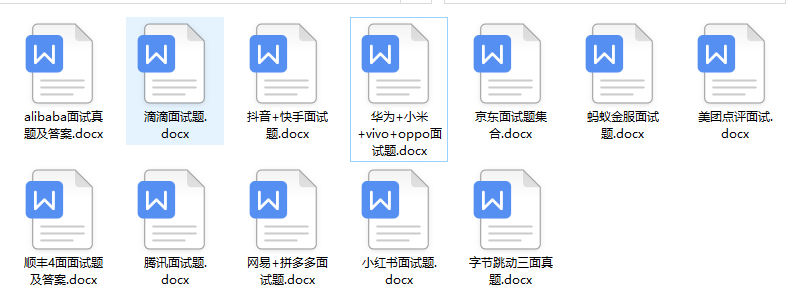
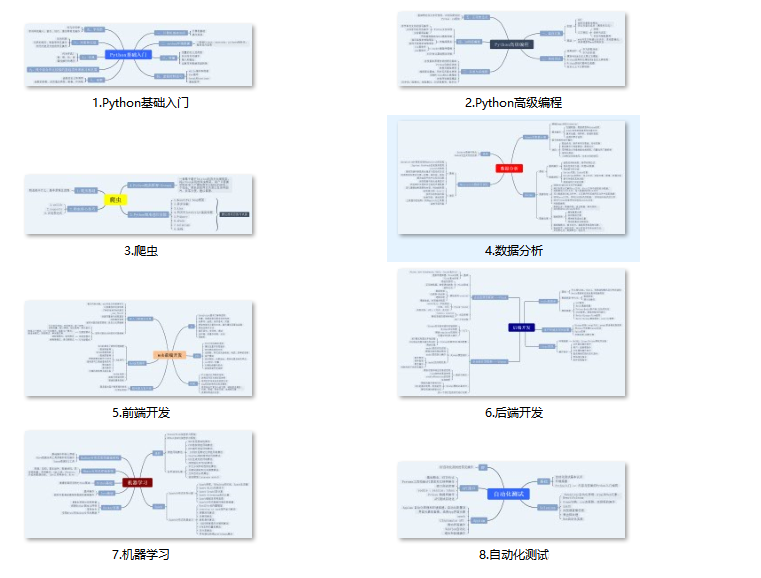
**既有适合小白学习的零基础资料,也有适合3年以上经验的小伙伴深入学习提升的进阶课程,基本涵盖了95%以上前端开发知识点,真正体系化!**
**由于文件比较大,这里只是将部分目录大纲截图出来,每个节点里面都包含大厂面经、学习笔记、源码讲义、实战项目、讲解视频,并且后续会持续更新**
**如果你觉得这些内容对你有帮助,可以扫码获取!!!(备注Python)**
edf79.png)
**既有适合小白学习的零基础资料,也有适合3年以上经验的小伙伴深入学习提升的进阶课程,基本涵盖了95%以上前端开发知识点,真正体系化!**
**由于文件比较大,这里只是将部分目录大纲截图出来,每个节点里面都包含大厂面经、学习笔记、源码讲义、实战项目、讲解视频,并且后续会持续更新**
**如果你觉得这些内容对你有帮助,可以扫码获取!!!(备注Python)**
<img src="https://img-community.csdnimg.cn/images/fd6ebf0d450a4dbea7428752dc7ffd34.jpg" alt="img" style="zoom:50%;" />






















 215
215











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








