新建2个asp.net core 项目使用空模板
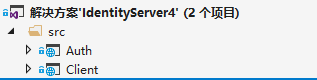
Auth 身份认证服务
Client客户端
Auth项目打开安装相关依赖
IdentityServer4 和 EF 实体框架
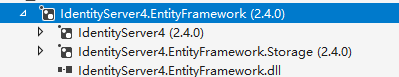
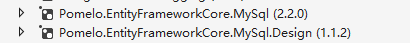
Mysql EF Provider
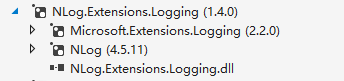
Nlog日志组件
打开Startup.cs 文件配置 管道
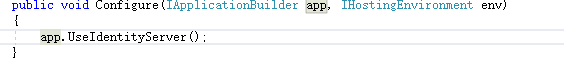
配置 identity server
还是Startup.cs,编辑ConfigureServices方法:
添加Nlog日志
services.AddLogging(logBuilder =>{
logBuilder.AddNLog();
});
日志配置文件(右键属性选择始终复制)
日志配置内容
添加IdentityServer服务
services.AddIdentityServer()
添加身份验证方式
services.AddIdentityServer()
.AddResourceOwnerValidator()
ResourceOwnerPasswordValidator 类实现接口 IResourceOwnerPasswordValidator
实现验证ValidateAsync异步方法
public asyncTask ValidateAsync(ResourceOwnerPasswordValidationContext context)
{try{//根据context.UserName和context.Password与数据库的数据做校验,判断是否合法
if (context.UserName == "wjk" && context.Password == "123")
{
context.Result= newGrantValidationResult(
subject: context.UserName,
authenticationMethod:"custom",
claims: GetUserClaims());
}else{//验证失败
context.Result = new GrantValidationResult(TokenRequestErrors.InvalidGrant, "invalid custom credential");
}
}catch(System.Exception exception)
{
context.Result= new GrantValidationResult(TokenRequestErrors.InvalidGrant, "Invalid username or password");throw;
}
}
设置Claims
private static IEnumerableGetUserClaims()
{return new[]
{new Claim("uid", "1"),new Claim(JwtClaimTypes.Name,"wjk"),new Claim(JwtClaimTypes.GivenName, "GivenName"),new Claim(JwtClaimTypes.FamilyName, "yyy"),new Claim(JwtClaimTypes.Email, "977865769@qq.com"),new Claim(JwtClaimTypes.Role,"admin")
};
}
设置验证方式
services.AddIdentityServer()
.AddResourceOwnerValidator()
.AddSigningCredential(cert)
使用pfx 证书验证
cert证书读取
var certAbsolutePath = PathResolver.ResolveCertConfigPath(Configuration["AuthOption:X509Certificate2FileName"], Environment);var cert = new X509Certificate2(certAbsolutePath, Configuration["AuthOption:X509Certificate2Password"]);
public static classPathResolver
{public static string ResolveCertConfigPath(stringconfigPath, IHostingEnvironment environment








 最低0.47元/天 解锁文章
最低0.47元/天 解锁文章















 550
550











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








