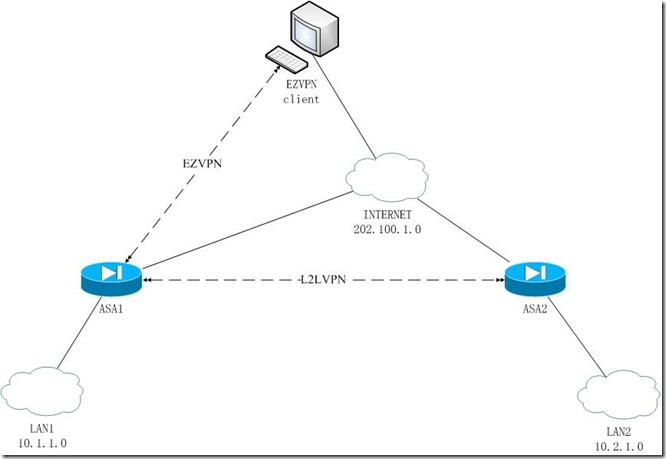
实验环境,两台ASA(8.4),ASA1与ASA2建立L2L×××,ASA1与测试PC建立EZ×××
拓扑
配置步骤:
1.基础配置(接口,路由,PAT)
2.L2L×××配置
3.EZ×××配置
4.NAT调整
关键点:经实验验证,在ASA上同时存在L2L×××和EZ×××时,在配置加密图(crypto map)时,L2L×××的序号应小于EZ×××的序号,即先配置L2L×××在配置EZ×××,才能保证L2L×××的正常通讯
ASA1(config)# sh run
: Saved
:
ASA Version 8.4(2)
!
hostname ASA1
!
interface GigabitEthernet0 //接口配置
nameif outside
security-level 0
ip address 202.100.1.1 255.255.255.0
!
interface GigabitEthernet1
nameif inside
security-level 100
ip address 10.1.1.1 255.255.255.0
!
object network nat //定义PAT对象
subnet 10.1.1.0 255.255.255.0
object network ez*** //定义EZ×××客户端对象
subnet 10.1.2.0 255.255.255.0
object network l2l*** //定义L2L×××客户端对象
subnet 10.2.1.0 255.255.255.0
!
access-list outside extended permit icmp any any //放行ICMP的ACL
access-list ez***.acl extended permit ip 10.1.1.0 255.255.255.0 any //用于ez***的隧道分割列表ACL
access-list l2l***.acl extended permit ip 10.1.1.0 255.255.255.0 10.2.1.0 255.255.255.0 //用于L2L×××的感兴趣流的ACL
!
ip local pool ez***.pool 10.1.2.1-10.1.2.10 mask 255.255.255.0 //定义EZ×××客户端的地址池
!
nat (inside,outside) source static nat nat destination static ez*** ez*** //用于EZ×××的twice NAT(NAT旁路)
nat (inside,outside) source static nat nat destination static l2l*** l2l*** //用于L2L×××的twice NAT(NAT旁路)
!
object network nat
nat (inside,outside) dynamic interface //LAN1的PAT
!
access-group outside in interface outside //outside接口上的ACL调用
route outside 10.2.1.0 255.255.255.0 202.100.1.2 1 //指定的到L2L×××远端网络的静态路由(此例中没有配置默认路由,此路由对于L2L×××必要)
!
crypto ipsec ikev1 transform-set ***.tran esp-des esp-md5-hmac //IPSec转换集
crypto dynamic-map ***.dymap 10 set ikev1 transform-set ***.tran // EZ×××的动态map
crypto map ***.map 20 match address l2l***.acl //以下三条命令定义L2L×××的map,请注意L2L×××的map序号要比EZ×××的map序号要小,即在其前,否则L2L×××不通
crypto map ***.map 20 set peer 202.100.1.2
crypto map ***.map 20 set ikev1 transform-set ***.tran
crypto map ***.map 30 ipsec-isakmp dynamic ***.dymap //定义EZ×××的map,序号要大于L2L×××
crypto map ***.map interface outside //outside接口下调用map
crypto ikev1 enable outside //outside接口下启用IKEV1
crypto ikev1 policy 10 //IKE一阶段策略
authentication pre-share
encryption 3des
hash sha
group 2
!
group-policy ez***.policy internal //定义EZ×××的用户策略
group-policy ez***.policy attributes
split-tunnel-policy tunnelspecified
split-tunnel-network-list value ez***.acl
address-pools value ez***.pool
username cisco password 3USUcOPFUiMCO4Jk encrypted
tunnel-group ez*** type remote-access //定义EZ×××的隧道组及属性
tunnel-group ez*** general-attributes
default-group-policy ez***.policy
tunnel-group ez*** ipsec-attributes
ikev1 pre-shared-key *****
tunnel-group 202.100.1.2 type ipsec-l2l //定义L2L×××的隧道组及ipsec属性
tunnel-group 202.100.1.2 ipsec-attributes
ikev1 pre-shared-key *****
!
ASA1(config)# sh ***-sessiondb l2l
Session Type: LAN-to-LAN
Connection : 202.100.1.2
Index : 3 IP Addr : 202.100.1.2
Protocol : IKEv1 IPsec
Encryption : 3DES DES Hashing : SHA1 MD5
Bytes Tx : 62496 Bytes Rx : 62496
Login Time : 17:21:42 UTC Fri Mar 8 2013
Duration : 0h:11m:26s
ASA1(config)# sh ***-sessiondb ra-ikev1-ipsec
Session Type: IKEv1 IPsec
Username : cisco Index : 4
Assigned IP : 10.1.2.1 Public IP : 202.100.1.100
Protocol : IKEv1 IPsec
License : Other ×××
Encryption : 3DES DES Hashing : SHA1 MD5
Bytes Tx : 37740 Bytes Rx : 37740
Group Policy : ez***.policy Tunnel Group : ez***
Login Time : 17:22:24 UTC Fri Mar 8 2013
Duration : 0h:10m:48s
Inactivity : 0h:00m:00s
NAC Result : Unknown
VLAN Mapping : N/A VLAN : none
ASA1(config)# sh ro
Codes: C - connected, S - static, I - IGRP, R - RIP, M - mobile, B - BGP
D - EIGRP, EX - EIGRP external, O - OSPF, IA - OSPF inter area
N1 - OSPF NSSA external type 1, N2 - OSPF NSSA external type 2
E1 - OSPF external type 1, E2 - OSPF external type 2, E - EGP
i - IS-IS, L1 - IS-IS level-1, L2 - IS-IS level-2, ia - IS-IS inter area
* - candidate default, U - per-user static route, o - ODR
P - periodic downloaded static route
Gateway of last resort is not set
C 202.100.1.0 255.255.255.0 is directly connected, outside
S 10.1.2.1 255.255.255.255 [1/0] via 202.100.1.100, outside
S 10.2.1.0 255.255.255.0 [1/0] via 202.100.1.2, outside
C 10.1.1.0 255.255.255.0 is directly connected, inside
ASA1(config)# sh ip add
System IP Addresses:
Interface Name IP address Subnet mask Method
GigabitEthernet0 outside 202.100.1.1 255.255.255.0 manual
GigabitEthernet1 inside 10.1.1.1 255.255.255.0 manual
Current IP Addresses:
Interface Name IP address Subnet mask Method
GigabitEthernet0 outside 202.100.1.1 255.255.255.0 manual
GigabitEthernet1 inside 10.1.1.1 255.255.255.0 manual
ASA2(config)# sh run
: Saved
:
ASA Version 8.4(2)
!
hostname ASA2
enable password 8Ry2YjIyt7RRXU24 encrypted
passwd 2KFQnbNIdI.2KYOU encrypted
names
!
interface GigabitEthernet0
nameif outside
security-level 0
ip address 202.100.1.2 255.255.255.0
!
interface GigabitEthernet1
shutdown
no nameif
no security-level
no ip address
!
interface GigabitEthernet2
nameif inside
security-level 100
ip address 10.2.1.1 255.255.255.0
!
interface GigabitEthernet3
shutdown
no nameif
no security-level
no ip address
!
ftp mode passive
object network nat
subnet 10.2.1.0 255.255.255.0
object network l2l***
subnet 10.1.1.0 255.255.255.0
access-list outside extended permit icmp any any
access-list l2l***.acl extended permit ip 10.2.1.0 255.255.255.0 10.1.1.0 255.255.255.0
pager lines 24
logging console emergencies
mtu outside 1500
mtu inside 1500
no failover
icmp unreachable rate-limit 1 burst-size 1
no asdm history enable
arp timeout 14400
nat (inside,outside) source static nat nat destination static l2l*** l2l***
!
object network nat
nat (inside,outside) dynamic interface
access-group outside in interface outside
route outside 10.1.1.0 255.255.255.0 202.100.1.1 1
timeout xlate 3:00:00
timeout conn 1:00:00 half-closed 0:10:00 udp 0:02:00 icmp 0:00:02
timeout sunrpc 0:10:00 h323 0:05:00 h225 1:00:00 mgcp 0:05:00 mgcp-pat 0:05:00
timeout sip 0:30:00 sip_media 0:02:00 sip-invite 0:03:00 sip-disconnect 0:02:00
timeout sip-provisional-media 0:02:00 uauth 0:05:00 absolute
timeout tcp-proxy-reassembly 0:01:00
timeout floating-conn 0:00:00
dynamic-access-policy-record DfltAccessPolicy
user-identity default-domain LOCAL
no snmp-server location
no snmp-server contact
snmp-server enable traps snmp authentication linkup linkdown coldstart warmstart
crypto ipsec ikev1 transform-set ***.tran esp-des esp-md5-hmac
crypto map ***.map 10 match address l2l***.acl
crypto map ***.map 10 set peer 202.100.1.1
crypto map ***.map 10 set ikev1 transform-set ***.tran
crypto map ***.map interface outside
crypto ikev1 enable outside
crypto ikev1 policy 10
authentication pre-share
encryption 3des
hash sha
group 2
lifetime 86400
crypto ikev1 policy 65535
authentication pre-share
encryption 3des
hash sha
group 2
lifetime 86400
telnet timeout 5
ssh timeout 5
console timeout 0
threat-detection basic-threat
threat-detection statistics access-list
no threat-detection statistics tcp-intercept
tunnel-group 202.100.1.1 type ipsec-l2l
tunnel-group 202.100.1.1 ipsec-attributes
ikev1 pre-shared-key *****
!
class-map inspection_default
match default-inspection-traffic
!
!
policy-map type inspect dns preset_dns_map
parameters
message-length maximum client auto
message-length maximum 512
policy-map global_policy
class inspection_default
inspect dns preset_dns_map
inspect ftp
inspect h323 h225
inspect h323 ras
inspect ip-options
inspect netbios
inspect rsh
inspect rtsp
inspect skinny
inspect esmtp
inspect sqlnet
inspect sunrpc
inspect tftp
inspect sip
inspect xdmcp
!
service-policy global_policy global
prompt hostname context
call-home reporting anonymous prompt 2
call-home
profile CiscoTAC-1
no active
destination address http https://tools.cisco.com/its/service/oddce/services/DDCEService
destination address email callhome@cisco.com
destination transport-method http
subscribe-to-alert-group diagnostic
subscribe-to-alert-group environment
subscribe-to-alert-group inventory periodic monthly
subscribe-to-alert-group configuration periodic monthly
subscribe-to-alert-group telemetry periodic daily
crashinfo save disable
Cryptochecksum:3b4e368d62bd8ac75576dd90bf61afb8
: end
ASA2(config)#
ASA2(config)# sh ***-
ASA2(config)# sh ***-sessiondb l2l
Session Type: LAN-to-LAN
Connection : 202.100.1.1
Index : 2 IP Addr : 202.100.1.1
Protocol : IKEv1 IPsec
Encryption : 3DES DES Hashing : SHA1 MD5
Bytes Tx : 67116 Bytes Rx : 67116
Login Time : 01:22:12 UTC Sat Mar 9 2013
Duration : 0h:12m:20s
ASA2(config)# sh ro
Codes: C - connected, S - static, I - IGRP, R - RIP, M - mobile, B - BGP
D - EIGRP, EX - EIGRP external, O - OSPF, IA - OSPF inter area
N1 - OSPF NSSA external type 1, N2 - OSPF NSSA external type 2
E1 - OSPF external type 1, E2 - OSPF external type 2, E - EGP
i - IS-IS, L1 - IS-IS level-1, L2 - IS-IS level-2, ia - IS-IS inter area
* - candidate default, U - per-user static route, o - ODR
P - periodic downloaded static route
Gateway of last resort is not set
C 202.100.1.0 255.255.255.0 is directly connected, outside
C 10.2.1.0 255.255.255.0 is directly connected, inside
S 10.1.1.0 255.255.255.0 [1/0] via 202.100.1.1, outside
ASA2(config)# sh ip add
System IP Addresses:
Interface Name IP address Subnet mask Method
GigabitEthernet0 outside 202.100.1.2 255.255.255.0 manual
GigabitEthernet2 inside 10.2.1.1 255.255.255.0 manual
Current IP Addresses:
Interface Name IP address Subnet mask Method
GigabitEthernet0 outside 202.100.1.2 255.255.255.0 manual
GigabitEthernet2 inside 10.2.1.1 255.255.255.0 manual
转载于:https://blog.51cto.com/19055/1151387





















 122
122











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








