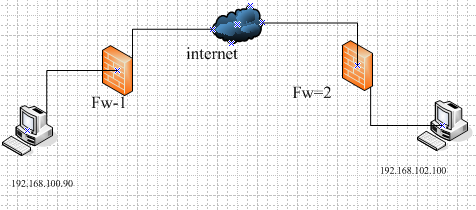
野蛮模式—基于名字的ipsec动态配置
由于网络地址的动态改变,可以使用基于名字的ipsec配置实现虚连接。
说明:由于实验条件有限,Internet有一台华为路由器代替模拟,并在其上配置DHCP服务器,使fw-2动态获取地址以实现地址不固定仍达到通信的效果。
一、Fw-1的配置
[fw-1]inter eth0/0
[fw-1-Ethernet0/0]ip add 192.168.101.55 255.255.255.0
[fw-1-Ethernet0/0]inter eth0/4
[fw-1-Ethernet0/4]ip add 1.1.1.1 255.255.255.0
[fw-1-Ethernet0/4]quit
[fw-1]ip route 0.0.0.0 0.0.0.0 1.1.1.2 //配置一条默认路由
配置访问控制列表,起过滤作用
[fw-1]acl number 3000
[fw-1-acl-adv-3000]rule 10 permit ip source 192.168.101.0 0.0.0.255 dest 192.168.102.0 0.0.0.255
[fw-1-acl-adv-3000]rule 20 deny ip source any dest any
配置安全提议(系统默认,可选)
[fw-1]ipsec proposal tran1
[fw-1-ipsec-proposal-tran1]encapsulation-mode tunnel
[fw-1-ipsec-proposal-tran1]transform esp
[fw-1-ipsec-proposal-tran1]esp encryption-algorithm des
[fw-1-ipsec-proposal-tran1]esp authentication-algorithm md5
配置邻居参数
[fw-1]ike peer fw-2
[fw-1-ike-peer-fw-2]exchange-mode aggressive //启用野蛮模式
[fw-1-ike-peer-fw-2]id-type name
[fw-1-ike-peer-fw-2]pre-shared-key simple 123456
[fw-1-ike-peer-fw-2]remote-name fw-2
[fw-1-ike-peer-fw-2]local-address 1.1.1.1
[fw-1-ike-peer-fw-2]q
[fw-1]ike local-name fw-1 //创建本地名字
配置安全策略
[fw-1]ipsec policy policy1 10 isakmp
[fw-1-ipsec-policy-isakmp-policy1-10]security acl 3000
[fw-1-ipsec-policy-isakmp-policy1-10]proposal tran1
[fw-1-ipsec-policy-isakmp-policy1-10]ike-peer fw-2
应用安全策略
[fw-1]inter eth0/4
[fw-1-Ethernet0/4]ipsec policy policy1
二、路由器配置
[Router]inter e0
[Router-Ethernet0]ip add 1.1.1.2 255.255.255.0
[Router-Ethernet0]inter e1
[Router-Ethernet1]ip add 1.1.2.1 255.255.255.0
配置DHCP服务器
[Router]dhcp enable
[Router]dhcp server ip-pool xxx
[Router-dhcp-xxx]network 1.1.2.0
[Router-dhcp-xxx]gateway-list 1.1.2.1
[Router-dhcp-xxx]dns-list 222.88.88.88
三、Fw-2的配置
[fw-2]int eth0/0
[fw-2-Ethernet0/0]ip add 192.168.102.90 ?
[fw-2-Ethernet0/0]ip add 192.168.102.90 24
[fw-2-Ethernet0/0]int eth0/4
[fw-2-Ethernet0/4]ip add dhcp-alloc //自动获得地址
[fw-2-Ethernet0/4]quit
[fw-2]ip route 0.0.0.0 0.0.0.0 1.1.2.1 //配置一条默认路由
把端口加入区域(如系统默认已加入,可选)
[fw-2]firewall zone untrust
[fw-2-zone-untrust]add int eth0/4
[fw-2]ip route 0.0.0.0 0 1.1.2.1
设置访问控制列表,起过滤作用
[fw-2]acl number 3000
[fw-2-acl-adv-3000]rule 10 permit ip source 192.168.102.0 0.0.0.255 destination 192.168.101.0 0.0.0.255
[fw-2-acl-adv-3000]rule 20 deny ip source any destination any
创建安全协议(如系统默认,可选)
[fw-2]ipsec proposal tran1
[fw-2-ipsec-proposal-tran1]encapsulation-mode tunnel
[fw-2-ipsec-proposal-tran1]transform esp
[fw-2-ipsec-proposal-tran1]esp authentication-algorithm md5
[fw-2-ipsec-proposal-tran1]esp encryption-algorithm des
配置邻居参数
[fw-2]ike peer fw-1
[fw-2-ike-peer-fw-1]exchange-mode aggressive //启用野蛮模式
[fw-2-ike-peer-fw-1]id-type name
[fw-2-ike-peer-fw-1]pre-shared-key 123456
[fw-2-ike-peer-fw-1]remote-address 1.1.1.1
[fw-2-ike-peer-fw-1]remote-name fw-1
[fw-2-ike-peer-fw-1]q
[fw-2]ike local-name fw-2 //创建本地名字
创建安全策略
[fw-2]ipsec policy policy1 10 isakmp //安全策略实为一表格,每条策略需表序号
[fw-2-ipsec-policy-isakmp-policy1-10]security acl 3000
[fw-2-ipsec-policy-isakmp-policy1-10]proposal tran1
[fw-2-ipsec-policy-isakmp-policy1-10]ike-peer fw-1
把策略应用到端口
[fw-2]int eth0/4
[fw-2-Ethernet0/4]ipsec policy policy1
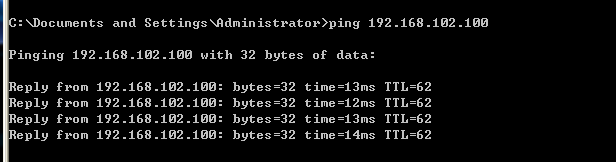
测试结果如下:
可能遇到问题:第一次从fw-1 ping fw-2不通怎么办?
问题回答:由于防火墙是三层设备,数据以包的形式转发,fw-2地址不固定,fw-1无法知道其ip地址,故无法通信,所以先在fw-2端ping fw-1端建立sa后,再在fw-1端ping fw-2端就通了。
转载于:https://blog.51cto.com/nshao/1088923





















 1929
1929











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








