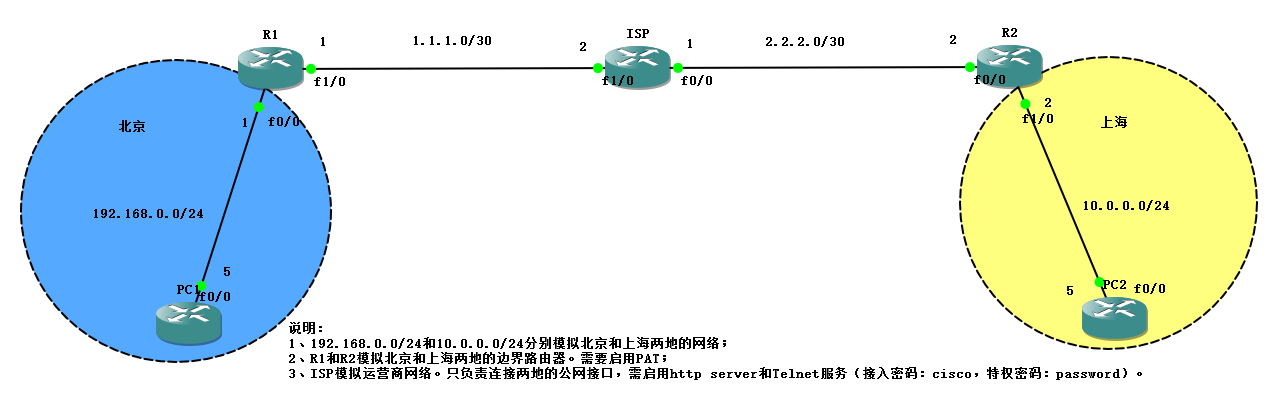
拓扑如下:
要求:
1、PC1可以通过IPSec ×××与PC2通信。
2、PC1和PC2通过边界路由器的PAT与Internet上的ISP通信。
配置说明:
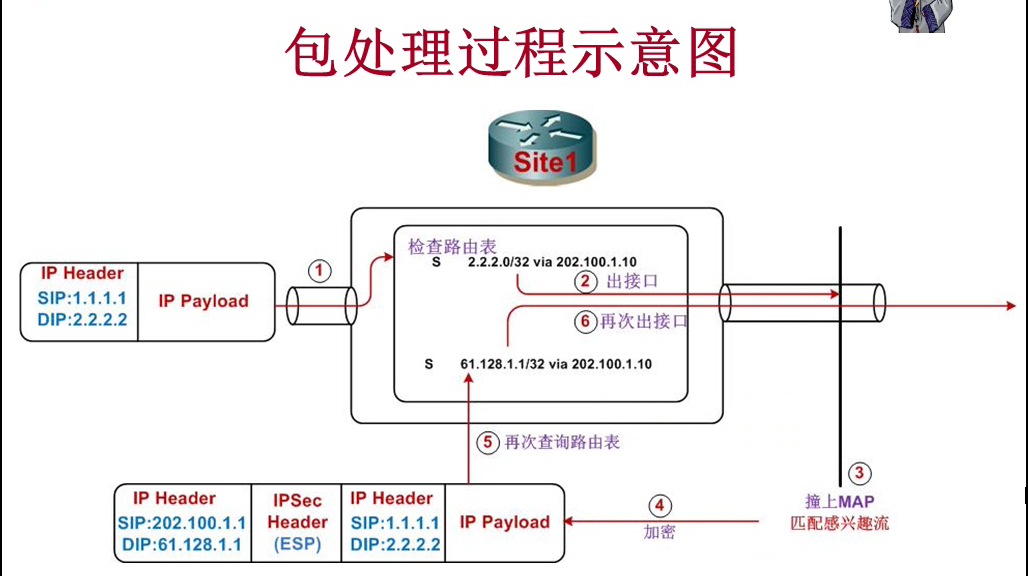
在配置IPSec ×××前,要先解决三个路由问题,从加密设备角度看:
1、本地通讯点路由;
2、远端加密点路由;
3、远端通讯点路由。 //该路由的目的不是为了让本加密点与远端通信点实现通信,是为了确保数据包匹配IPSEC SA的感兴趣流,从而撞击出端口上的crypto map来实现加密。否则路由器不知道从哪个端口送出数据包,也就无法匹配crypto map的感兴趣流。
(图片来自现任明教教主***教学视频)
配置脚本:
ISP:
en
conf t
no ip domain-lookup
line console 0
logging synchronous
exec-timeout 0 0
exit
line vty 0 15
logging synchronous
exec-timeout 0 0
password cisco
exit
enable password password
ip subnet-zero
hostname ISP
int f1/0
ip add 1.1.1.2 255.255.255.252
no shut
int f0/0
ip add 2.2.2.1 255.255.255.252
no shut
exit
ip http server
endR1:
en
conf t
no ip domain-lookup
line console 0
logging synchronous
exec-timeout 0 0
exit
line vty 0 15
logging synchronous
exec-timeout 0 0
password cisco
exit
ip subnet-zero
hostname R1
int f1/0
ip add 1.1.1.1 255.255.255.252
no shut
int f0/0
ip add 192.168.0.1 255.255.255.0
no shut
exit
ip route 0.0.0.0 0.0.0.0 1.1.1.2 //该条目同时解决了远端加密点和远端通讯点的路由问题,本地通讯点路由为直连无需添加。
end
ping 1.1.1.2L2L IPSec***配置:
conf t
crypto isakmp enable
crypto isakmp policy 10
encryption 3des
hash md5
group 2
authentication pre-share
exit
crypto isakmp key 0 cisco123 address 2.2.2.2
ip access-list extended l2l***
permit ip 192.168.0.0 0.0.0.255 10.0.0.0 0.0.0.255
exit
crypto ipsec transform-set l2ltrans esp-aes esp-sha-hmac
mode tunnel
exit
crypto map outmap 1 ipsec-isakmp
set peer 2.2.2.2
set transform-set l2ltrans
match address l2l***
exit
int f1/0
crypto map outmap
end启用PAT:
conf t
ip access-list extended PAT
deny ip 192.168.0.0 0.0.0.255 10.0.0.0 0.0.0.255 //注意:必须从PAT的流量中排除掉IPSEC SA流量,否则IPSEC SA流量无法穿越IPSEC ***
permit ip 192.168.0.0 0.0.0.255 any
exit
int f1/0
ip nat outside
int f0/0
ip nat inside
exit
ip nat inside source list PAT interface f1/0 overload
endR2:
en
conf t
no ip domain-lookup
line console 0
logging synchronous
exec-timeout 0 0
exit
line vty 0 15
logging synchronous
exec-timeout 0 0
password cisco
exit
ip subnet-zero
hostname R2
int f0/0
ip add 2.2.2.2 255.255.255.252
no shut
int f1/0
ip add 10.0.0.2 255.255.255.0
no shut
exit
ip route 0.0.0.0 0.0.0.0 2.2.2.1
end
ping 2.2.2.1L2L IPSec***配置:
conf t
crypto isakmp enable
crypto isakmp policy 10
encryption 3des
hash md5
group 2
authentication pre-share
exit
crypto isakmp key 0 cisco123 address 1.1.1.1
ip access-list extended l2l***
permit ip 10.0.0.0 0.0.0.255 192.168.0.0 0.0.0.255
exit
crypto ipsec transform-set l2ltrans esp-aes esp-sha-hmac
mode tunnel
exit
crypto map outmap 1 ipsec-isakmp
set peer 1.1.1.1
set transform-set l2ltrans
match address l2l***
exit
int f0/0
crypto map outmap
end启用PAT:
conf t
ip access-list extended PAT
deny ip 10.0.0.0 0.0.0.255 192.168.0.0 0.0.0.255
permit ip 10.0.0.0 0.0.0.255 any
exit
int f0/0
ip nat outside
int f1/0
ip nat inside
exit
ip nat inside source list PAT interface f0/0 overload
endPC1:
en
conf t
no ip domain-lookup
line console 0
logging synchronous
exec-timeout 0 0
exit
line vty 0 15
logging synchronous
exec-timeout 0 0
password cisco
exit
ip subnet-zero
hostname PC1
enable password password
int f0/0
ip add 192.168.0.5 255.255.255.0
no shut
exit
no ip routing
ip default-gateway 192.168.0.1
end
ping 192.168.0.1PC2:
en
conf t
no ip domain-lookup
line console 0
logging synchronous
exec-timeout 0 0
exit
line vty 0 15
logging synchronous
exec-timeout 0 0
password cisco
exit
ip subnet-zero
hostname PC2
enable password password
int f0/0
ip add 10.0.0.5 255.255.255.0
no shut
exit
no ip routing
ip default-gateway 10.0.0.2
end
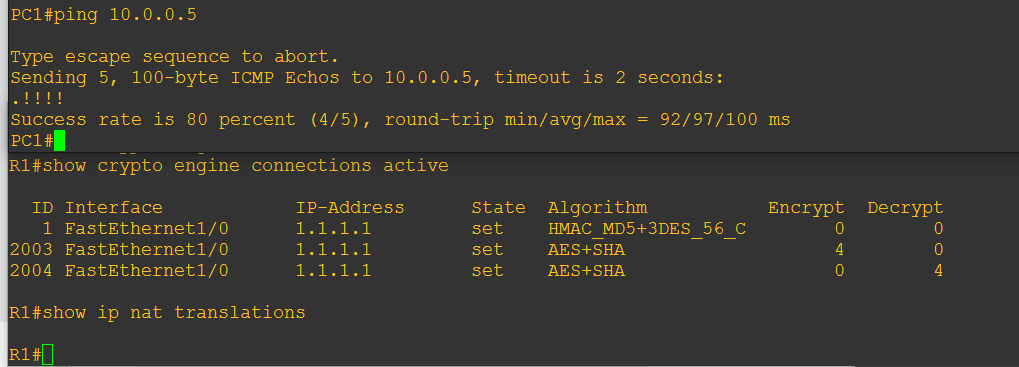
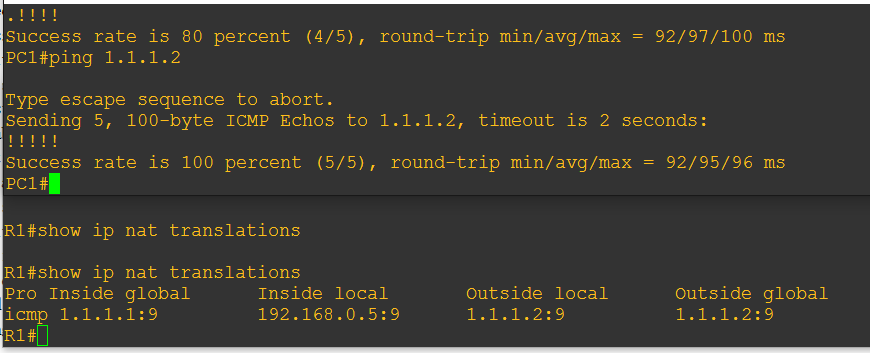
ping 10.0.0.2验证:
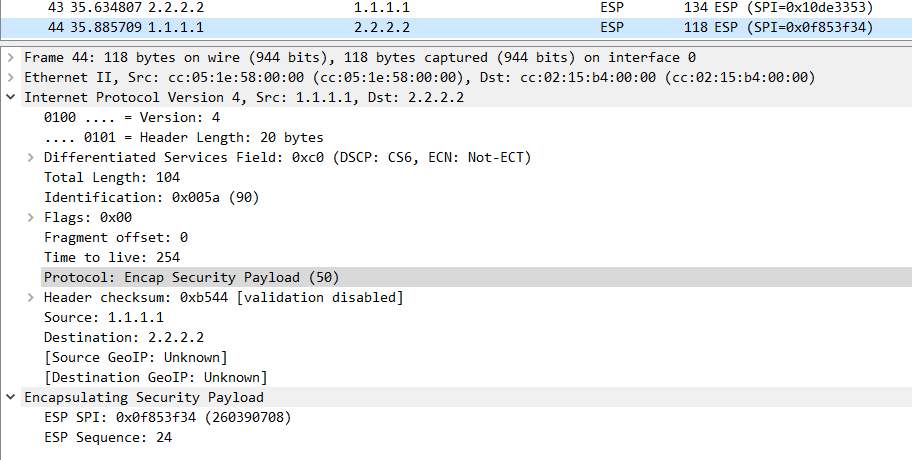
抓包截图:
转载于:https://blog.51cto.com/yinkai/1791410





















 3812
3812











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








