下面这个小实验也反映了ACL覆盖的导致的问题,他的情况是静态×××,一端的ACL覆盖了另一端,导致的结果是从一端可以发起连接,从另一端却无法发起。
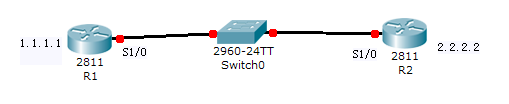
拓扑:
说明:
1. R1,R2点到点直连,分别开启loopback0接口模拟内部网络。
2. R2的感兴趣流ACL覆盖R1的感兴趣流ACL。
配置:
R1:
version 12.4
hostname R1
!
crypto isakmp policy 10
authentication pre-share
crypto isakmp key cisco address 12.1.1.2
!
!
crypto ipsec transform-set cisco esp-des esp-md5-hmac
!
crypto map cisco 10 ipsec-isakmp
set peer 12.1.1.2
set transform-set cisco
match address ***
!
interface Loopback0
ip address 1.1.1.1 255.255.255.0
!
interface Serial1/0
ip address 12.1.1.1 255.255.255.0
serial restart-delay 0
crypto map cisco
!
ip route 2.2.2.0 255.255.255.0 12.1.1.2
!
ip access-list extended ***
permit ip host 1.1.1.1 host 2.2.2.2
!
R2:
version 12.4
hostname R2
!
crypto isakmp policy 10
authentication pre-share
crypto isakmp key cisco address 12.1.1.1
!
!
crypto ipsec transform-set cisco esp-des esp-md5-hmac
!
crypto map cisco 10 ipsec-isakmp
set peer 12.1.1.1
set transform-set cisco
match address ***
!
interface Loopback0
ip address 2.2.2.2 255.255.255.0
!
interface Serial1/0
ip address 12.1.1.2 255.255.255.0
serial restart-delay 0
crypto map cisco
!
ip route 1.1.1.0 255.255.255.0 12.1.1.1
!
permit ip 2.2.2.0 0.0.0.255 1.1.1.0 0.0.0.255
!
下面测试先从R1发起连接:
R1#ping 2.2.2.2 sou l0 re 10
Type escape sequence to abort.
Sending 10, 100-byte ICMP Echos to 2.2.2.2, timeout is 2 seconds:
Packet sent with a source address of 1.1.1.1
.!!!!!!!!!
Success rate is 90 percent (9/10), round-trip min/avg/max = 8/27/76 ms
R1#ping 2.2.2.2 sou l0 re 10
Type escape sequence to abort.
Sending 10, 100-byte ICMP Echos to 2.2.2.2, timeout is 2 seconds:
Packet sent with a source address of 1.1.1.1
.!!!!!!!!!
Success rate is 90 percent (9/10), round-trip min/avg/max = 8/27/76 ms
R1#
R1#sh cry isa sa
dst src state conn-id slot status
12.1.1.2 12.1.1.1 QM_IDLE 1 0 ACTIVE
能够成功发起!
清掉连接,测试从R2发起连接。
R2#ping 1.1.1.1 sou l0 re 10
Type escape sequence to abort.
Sending 10, 100-byte ICMP Echos to 1.1.1.1, timeout is 2 seconds:
Packet sent with a source address of 2.2.2.2
..........
Success rate is 0 percent (0/10)
Ping不通!
R2#sh cry isa sa
dst src state conn-id slot status
12.1.1.1 12.1.1.2 MM_NO_STATE 2 0 ACTIVE (deleted)
从R2发起连接时就无法建立。原因还是出在ACL覆盖的问题上。
前面的实验中曾经总结了被覆盖的不能发起连接,但是这个实验中却是被覆盖的可以发起连接。但是他们具体的应用场景也不一样,我暂时还没有得到一个很好的技术解释。看到这篇博客的朋友如果了解的话请不吝赐教。
转载于:https://blog.51cto.com/edges/407383





















 66
66











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








