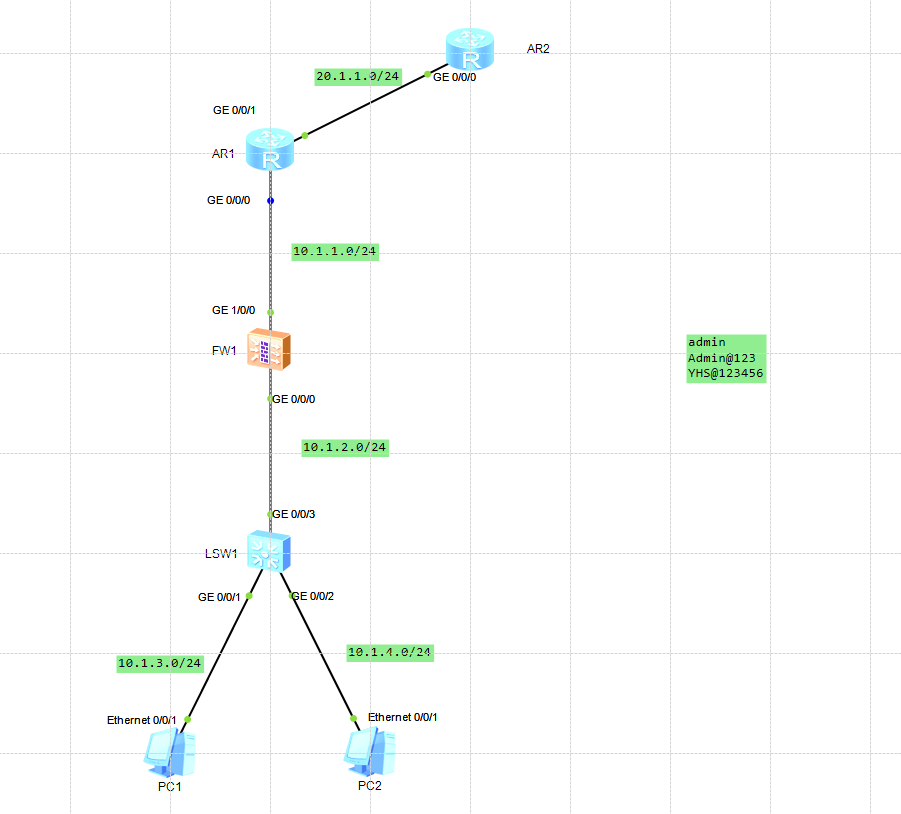
1、网络拓扑图
2、firewall核心配置
1)第一步:基础配置
int g0/0/0
ip address 10.1.2.2 24
int g1/0/1
ip address 10.1.1.2 24
2)将端口划分到对应区域
firewall zone trust
add int g0/0/0
firewall zone untrust
add int g1/0/0
3)应用策略
security-policy
rule name intoout
source-zone trust
destination-zone untrust
service http
service https
service icmp
service ssh
action permit
rule name outtoin
source-zone untrust
destination-zone trust
service http
service https
service icmp
service ssh
service telnet
action permit
4)配置静态路由
ip route-static 0.0.0.0 0.0.0.0 10.1.1.2
ip route-static 10.1.3.0 255.255.255.0 10.1.2.1
ip route-static 10.1.4.0 255.255.255.0 10.1.2.1
3、配置实例
R1:
<r1>display current-configuration
[V200R003C00]
#
sysname r1
#
snmp-agent local-engineid 800007DB03000000000000
snmp-agent
#
clock timezone China-Standard-Time minus 08:00:00
#
portal local-server load portalpage.zip
#
drop illegal-mac alarm
#
set cpu-usage threshold 80 restore 75
#
acl number 2000
rule 5 permit
#
aaa
authentication-scheme default
authorization-scheme default
accounting-scheme default
domain default
domain default_admin
local-user admin password cipher %$%$K8m.Nt84DZ}e#<0`8bmE3Uw}%$%$
local-user admin service-type http
#
firewall zone Local
priority 15
#
interface GigabitEthernet0/0/0
ip address 10.1.1.2 255.255.255.0
#
interface GigabitEthernet0/0/1
ip address 20.1.1.1 255.255.255.0
nat outbound 2000
#
interface GigabitEthernet0/0/2
#
interface NULL0
#
ip route-static 0.0.0.0 0.0.0.0 20.1.1.2
ip route-static 10.1.2.0 255.255.255.0 10.1.1.1
ip route-static 10.1.3.0 255.255.255.0 10.1.1.1
ip route-static 10.1.4.0 255.255.255.0 10.1.1.1
#
user-interface con 0
authentication-mode password
user-interface vty 0 4
user-interface vty 16 20
#
wlan ac
#
return
<r1>
FW1:
<firewall>display current-configuration
2024-08-25 08:54:52.240
!Software Version V500R005C10SPC300
#
sysname firewall
#
l2tp domain suffix-separator @
#
ipsec sha2 compatible enable
#
undo telnet server enable
undo telnet ipv6 server enable
#
clock timezone UTC add 00:00:00
#
update schedule location-sdb weekly Sun 01:32
#
firewall defend action discard
#
banner enable
#
user-manage web-authentication security port 8887
undo privacy-statement english
undo privacy-statement chinese
page-setting
user-manage security version tlsv1.1 tlsv1.2
password-policy
level high
user-manage single-sign-on ad
user-manage single-sign-on tsm
user-manage single-sign-on radius
user-manage auto-sync online-user
#
web-manager security version tlsv1.1 tlsv1.2
web-manager enable
web-manager security enable
#
firewall dataplane to manageplane application-apperceive default-action drop
#
undo ips log merge enable
#
decoding uri-cache disable
#
update schedule ips-sdb daily 06:48
update schedule av-sdb daily 06:48
update schedule sa-sdb daily 06:48
update schedule cnc daily 06:48
update schedule file-reputation daily 06:48
#
ip vpn-instance default
ipv4-family
#
time-range worktime
period-range 08:00:00 to 18:00:00 working-day
#
ike proposal default
encryption-algorithm aes-256 aes-192 aes-128
dh group14
authentication-algorithm sha2-512 sha2-384 sha2-256
authentication-method pre-share
integrity-algorithm hmac-sha2-256
prf hmac-sha2-256
#
aaa
authentication-scheme default
authentication-scheme admin_local
authentication-scheme admin_radius_local
authentication-scheme admin_hwtacacs_local
authentication-scheme admin_ad_local
authentication-scheme admin_ldap_local
authentication-scheme admin_radius
authentication-scheme admin_hwtacacs
authentication-scheme admin_ad
authorization-scheme default
accounting-scheme default
domain default
service-type internetaccess ssl-vpn l2tp ike
internet-access mode password
reference user current-domain
manager-user audit-admin
password cipher @%@%0>UMSe#CFZUK[*27`yNPb13|,2G]~`6x`+ro,n*s(B8P13"b@%@%
service-type web terminal
level 15
manager-user api-admin
password cipher @%@%%jaM/e;ln~7^4}DyDq<-$;-.nZ*9+OTmNA|i7/D3&-V8;-1$@%@%
level 15
manager-user admin
password cipher @%@%a45C0r7xJ!q(7)KKJx}%3.9d9n{n)kYPv)tPyCKrO#yV.9g3@%@%
service-type web terminal
level 15
role system-admin
role device-admin
role device-admin(monitor)
role audit-admin
bind manager-user audit-admin role audit-admin
bind manager-user admin role system-admin
#
l2tp-group default-lns
#
interface GigabitEthernet0/0/0
undo shutdown
ip address 10.1.2.2 255.255.255.0
alias GE0/METH
#
interface GigabitEthernet1/0/0
undo shutdown
ip address 10.1.1.1 255.255.255.0
#
interface GigabitEthernet1/0/1
undo shutdown
#
interface GigabitEthernet1/0/2
undo shutdown
#
interface GigabitEthernet1/0/3
undo shutdown
#
interface GigabitEthernet1/0/4
undo shutdown
#
interface GigabitEthernet1/0/5
undo shutdown
#
interface GigabitEthernet1/0/6
undo shutdown
#
interface Virtual-if0
#
interface NULL0
#
firewall zone local
set priority 100
#
firewall zone trust
set priority 85
add interface GigabitEthernet0/0/0
#
firewall zone untrust
set priority 5
add interface GigabitEthernet1/0/0
#
firewall zone dmz
set priority 50
#
ip route-static 0.0.0.0 0.0.0.0 10.1.1.2
ip route-static 10.1.3.0 255.255.255.0 10.1.2.1
ip route-static 10.1.4.0 255.255.255.0 10.1.2.1
#
undo ssh server compatible-ssh1x enable
ssh authentication-type default password
ssh server cipher aes256_ctr aes128_ctr
ssh server hmac sha2_256 sha1
ssh client cipher aes256_ctr aes128_ctr
ssh client hmac sha2_256 sha1
#
firewall detect ftp
#
user-interface con 0
authentication-mode aaa
user-interface vty 0 4
authentication-mode aaa
protocol inbound ssh
user-interface vty 16 20
#
pki realm default
#
sa
#
location
#
multi-linkif
mode proportion-of-weight
#
right-manager server-group
#
device-classification
device-group pc
device-group mobile-terminal
device-group undefined-group
#
user-manage server-sync tsm
#
security-policy
rule name intoout
source-zone trust
destination-zone untrust
service http
service https
service icmp
service ssh
action permit
rule name outtoin
source-zone untrust
destination-zone trust
service http
service https
service icmp
service ssh
service telnet
action permit
#
auth-policy
#
traffic-policy
#
policy-based-route
#
nat-policy
#
quota-policy
#
pcp-policy
#
dns-transparent-policy
#
rightm-policy
#
return
<firewall>
SW1:
<sw1>display current-configuration
#
sysname sw1
#
vlan batch 10 20 30
#
cluster enable
ntdp enable
ndp enable
#
drop illegal-mac alarm
#
diffserv domain default
#
drop-profile default
#
aaa
authentication-scheme default
authorization-scheme default
accounting-scheme default
domain default
domain default_admin
local-user admin password simple admin
local-user admin service-type http
#
interface Vlanif1
#
interface Vlanif10
ip address 10.1.3.1 255.255.255.0
#
interface Vlanif20
ip address 10.1.4.1 255.255.255.0
#
interface Vlanif30
ip address 10.1.2.1 255.255.255.0
#
interface MEth0/0/1
#
interface GigabitEthernet0/0/1
port link-type access
port default vlan 10
#
interface GigabitEthernet0/0/2
port link-type access
port default vlan 20
#
interface GigabitEthernet0/0/3
port link-type access
port default vlan 30
#
interface GigabitEthernet0/0/4
#
interface GigabitEthernet0/0/5
#
interface GigabitEthernet0/0/6
#
interface GigabitEthernet0/0/7
#
interface GigabitEthernet0/0/8
#
interface GigabitEthernet0/0/9
#
interface GigabitEthernet0/0/10
#
interface GigabitEthernet0/0/11
#
interface GigabitEthernet0/0/12
#
interface GigabitEthernet0/0/13
#
interface GigabitEthernet0/0/14
#
interface GigabitEthernet0/0/15
#
interface GigabitEthernet0/0/16
#
interface GigabitEthernet0/0/17
#
interface GigabitEthernet0/0/18
#
interface GigabitEthernet0/0/19
#
interface GigabitEthernet0/0/20
#
interface GigabitEthernet0/0/21
#
interface GigabitEthernet0/0/22
#
interface GigabitEthernet0/0/23
#
interface GigabitEthernet0/0/24
#
interface NULL0
#
ip route-static 0.0.0.0 0.0.0.0 10.1.2.2
#
user-interface con 0
user-interface vty 0 4
#
return
<sw1>
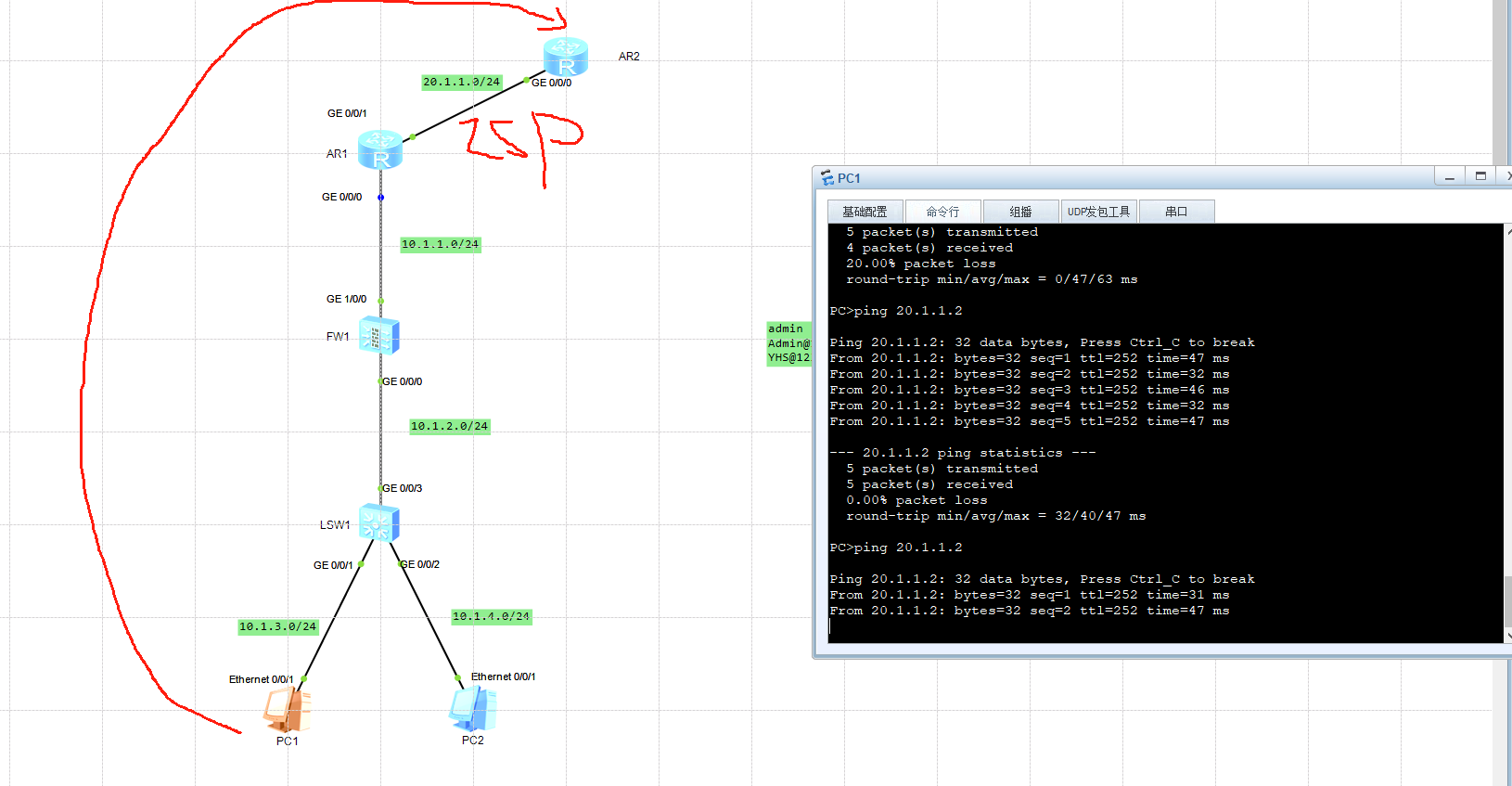
4、结果





















 6285
6285

 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








