First do the preparation as described in Attack DVWA weak session IDs
先按照https://pentestsuite.blogspot.com/2021/06/attack-dvwa-weak-session-ids.html?m=1
提到的完成准备工作
Then come to XSS(reflected) section and try some normal payload.
去到对应位置并尝试一般操作
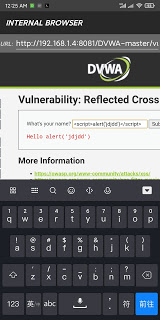
We don’t know what happened here, so come to PentestSuite and check the Javascript code.
Find the request in Proxy-Message list, and click resend button, finally send the message through Message Generator.
我们不知道发生了啥,所以检查一下js.
看到请求列表,找到对应的消息,然后点一下resend

Find the
<script>
has been removed by WAF. Then try








 最低0.47元/天 解锁文章
最低0.47元/天 解锁文章















 559
559











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








