SSH的架构
SSH的架构为客户端-服务器架构,向服务器发出请求的部分,称为客户端(client),OpenSSH 的实现为 ssh;接收客户端发出的请求的部分,称为服务器(server),OpenSSH 的实现为 sshd。
ssh的登陆流程:
- 客户端使用ssh-keygen命令生成公钥和私钥
- 手动将公钥复制到服务器上
- 客户端向服务器端发送请求
- 服务器端收到客户端发送的请求之后,发送一些数据给客户端,要求客户端证明身份
- 客户端收到数据之后使用私钥进行签名,并发送给服务器
- 服务器端收到客户端发送的加密签名数据之后,使用公钥进行解密,然后对比原始数据,一致的话就允许客户端进行登录

生成SSH key
1、创建公钥,打开终端输入命令行
ssh-keygen -t rsa -C "xxx@xxx.com"
-b:指定秘钥的二进制位数。参数越大,秘钥越难破解,当然解密开销也会更大
-t:参数用于指定生成秘钥的算法
-C:指定密匙文件的注释
其中:“xxx@xxx.com”为你的邮箱。

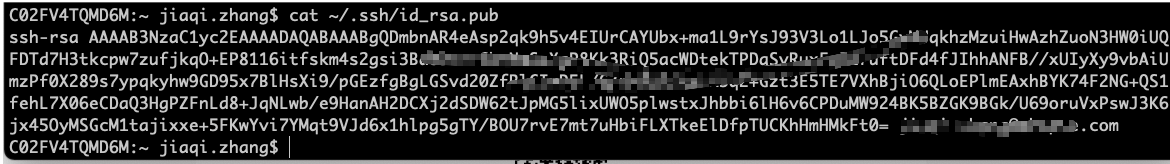
打开公钥
cat ~/.ssh/id_rsa.pub
得到一段编码:
手动上传公钥到服务器
将公钥复制到服务器端的~/.ssh/authorized_keys文件中
自动上传公钥
ssh-copy-id -i id_rsa user@host
配置之后如果在登录过程中显示失败,记得配置ssh_config。
sshd_config详解
# $OpenBSD: sshd_config,v 1.101 2017/03/14 07:19:07 djm Exp $
# This is the sshd server system-wide configuration file. See
# sshd_config(5) for more information.
# This sshd was compiled with PATH=/usr/bin:/bin:/usr/sbin:/sbin
# The strategy used for options in the default sshd_config shipped with
# OpenSSH is to specify options with their default value where
# possible, but leave them commented. Uncommented options override the
# default value.
#Port 22
#AddressFamily any
#ListenAddress 0.0.0.0
#ListenAddress ::
#HostKey /etc/ssh/ssh_host_rsa_key
#HostKey /etc/ssh/ssh_host_ecdsa_key
#HostKey /etc/ssh/ssh_host_ed25519_key
# Ciphers and keying
#RekeyLimit default none
# Logging
#SyslogFacility AUTH
#LogLevel INFO
# Authentication:
#LoginGraceTime 2m
#StrictModes yes
#MaxAuthTries 6
#MaxSessions 10
#PubkeyAuthentication yes
# Expect .ssh/authorized_keys2 to be disregarded by default in future.
#AuthorizedKeysFile .ssh/authorized_keys .ssh/authorized_keys2
#AuthorizedPrincipalsFile none
#AuthorizedKeysCommand none
#AuthorizedKeysCommandUser nobody
# For this to work you will also need host keys in /etc/ssh/ssh_known_hosts
#HostbasedAuthentication no
# Change to yes if you don't trust ~/.ssh/known_hosts for
# HostbasedAuthentication
#IgnoreUserKnownHosts no
# Don't read the user's ~/.rhosts and ~/.shosts files
#IgnoreRhosts yes
# To disable tunneled clear text passwords, change to no here!
# Change to yes to enable challenge-response passwords (beware issues with
# some PAM modules and threads)
# Kerberos options
#KerberosAuthentication no
#KerberosOrLocalPasswd yes
#KerberosTicketCleanup yes
#KerberosGetAFSToken no
# GSSAPI options
#GSSAPICleanupCredentials yes
#GSSAPIStrictAcceptorCheck yes
#GSSAPIKeyExchange no
# Set this to 'yes' to enable PAM authentication, account processing,
# and session processing. If this is enabled, PAM authentication will
# If you just want the PAM account and session checks to run without
#AllowAgentForwarding yes
#AllowTcpForwarding yes
#GatewayPorts no
X11Forwarding yes
#X11DisplayOffset 10
#X11UseLocalhost yes
#PermitTTY yes
PrintMotd no
#PrintLastLog yes
#TCPKeepAlive yes
#UseLogin no
#PermitUserEnvironment no
#Compression delayed
#ClientAliveInterval 0
#ClientAliveCountMax 3
#PidFile /var/run/sshd.pid
#MaxStartups 10:30:100
#PermitTunnel no
#ChrootDirectory none
#VersionAddendum none
# no default banner path
#Banner none
# Allow client to pass locale environment variables
AcceptEnv LANG LC_*
# override default of no subsystems
Subsystem sftp /usr/lib/openssh/sftp-server
# Example of overriding settings on a per-user basis
#Match User anoncvs
# X11Forwarding no
# AllowTcpForwarding no
# PermitTTY no
# ForceCommand cvs server
遇到的问题
连接服务器时,提示如下错误信息:
@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@
@ WARNING: REMOTE HOST IDENTIFICATION HAS CHANGED! @
@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@
IT IS POSSIBLE THAT SOMEONE IS DOING SOMETHING NASTY!
Someone could be eavesdropping on you right now (man-in-the-middle attack)!
It is also possible that a host key has just been changed.
The fingerprint for the ECDSA key sent by the remote host is
SHA256:1vXv9I7BzalAj6JfMfkIQZ0fLD+0gw7x1UoTVQ9D7gE.
Please contact your system administrator.
Add correct host key in /Users/jiaqi.zhang/.ssh/known_hosts to get rid of this message.
Offending ECDSA key in /Users/jiaqi.zhang/.ssh/known_hosts:9
ECDSA host key for xxx.xxx.xxx.xx has changed and you have requested strict checking.
解决办法:
将本地客户端的known_hosts中连接目标服务器相关信息都删掉即可。vi ~/.ssh/known_hosts
ssh-keygen -R hostname
参考文章:






















 312
312











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








