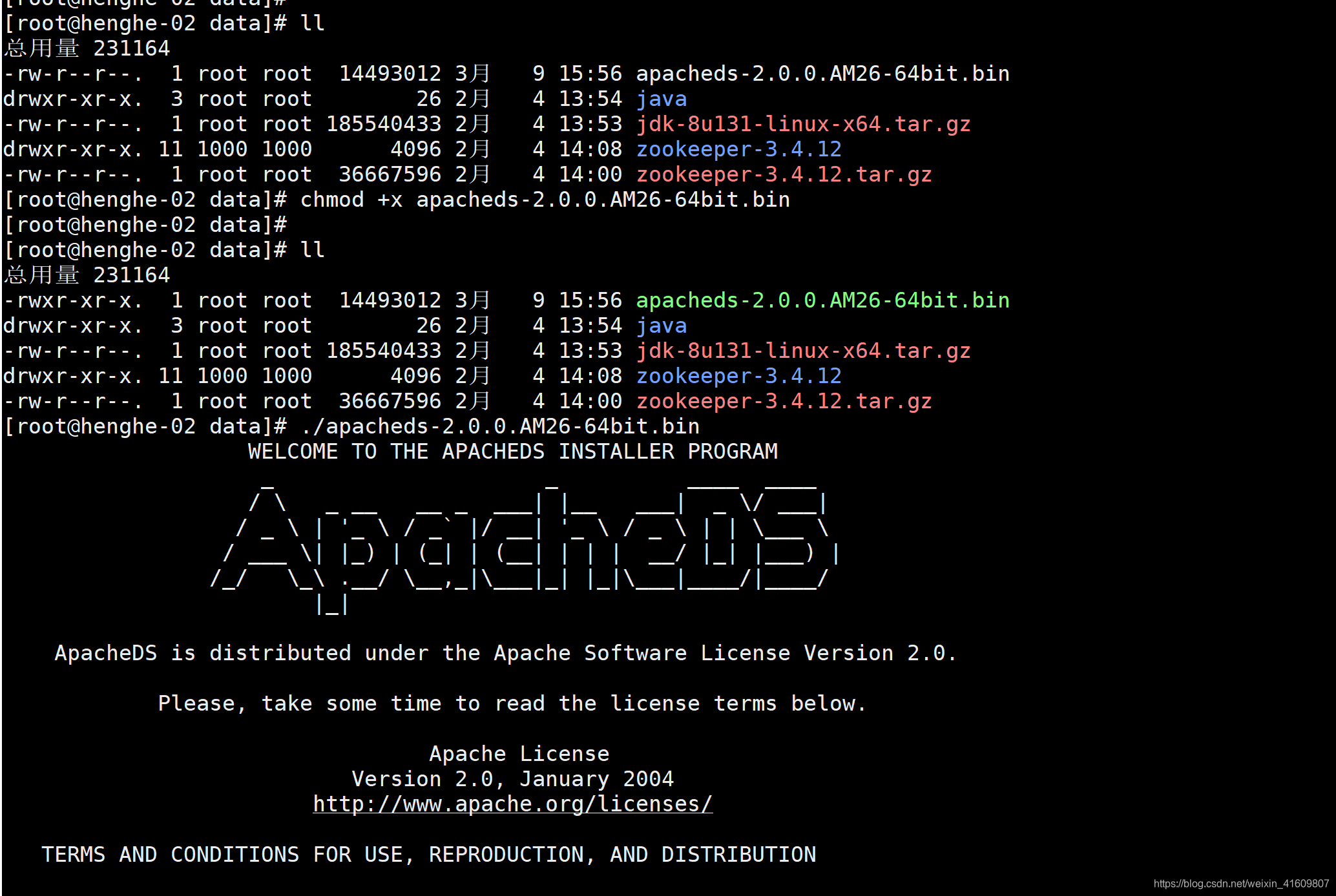
1、安装apacheDS
1.1执行安装脚本
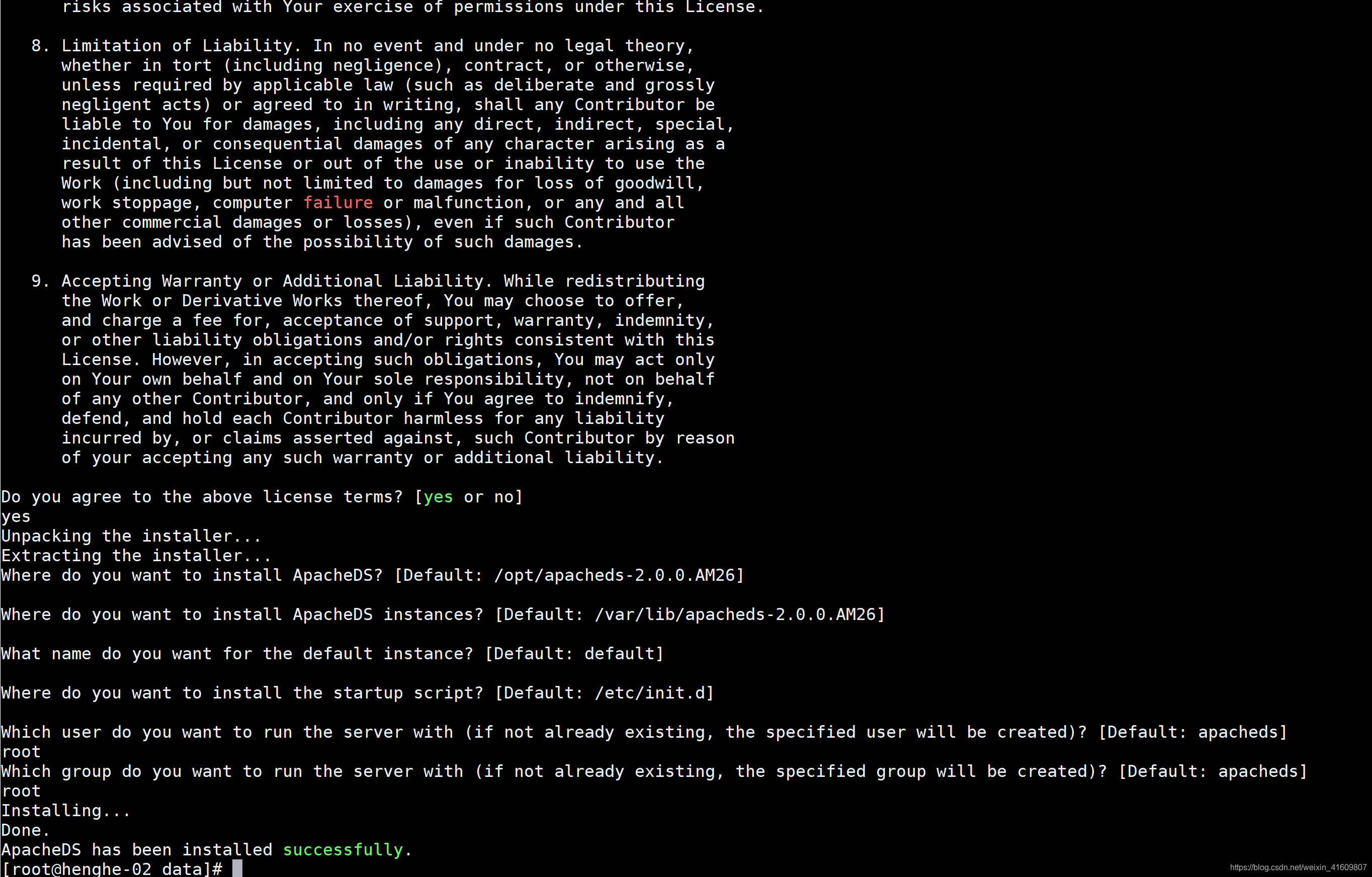
1.2 默认安装配置
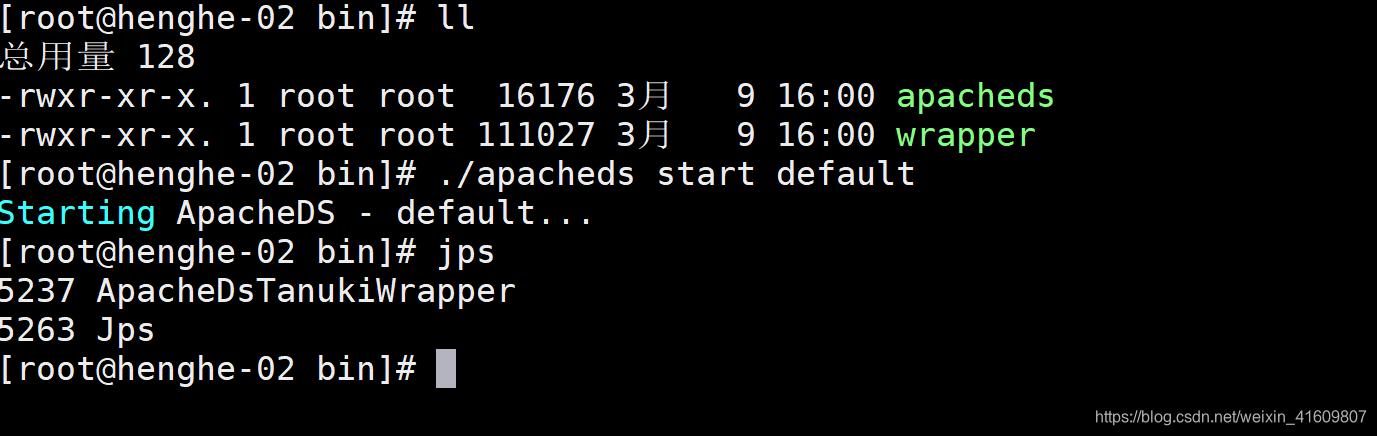
1.3 启动ApacheDS
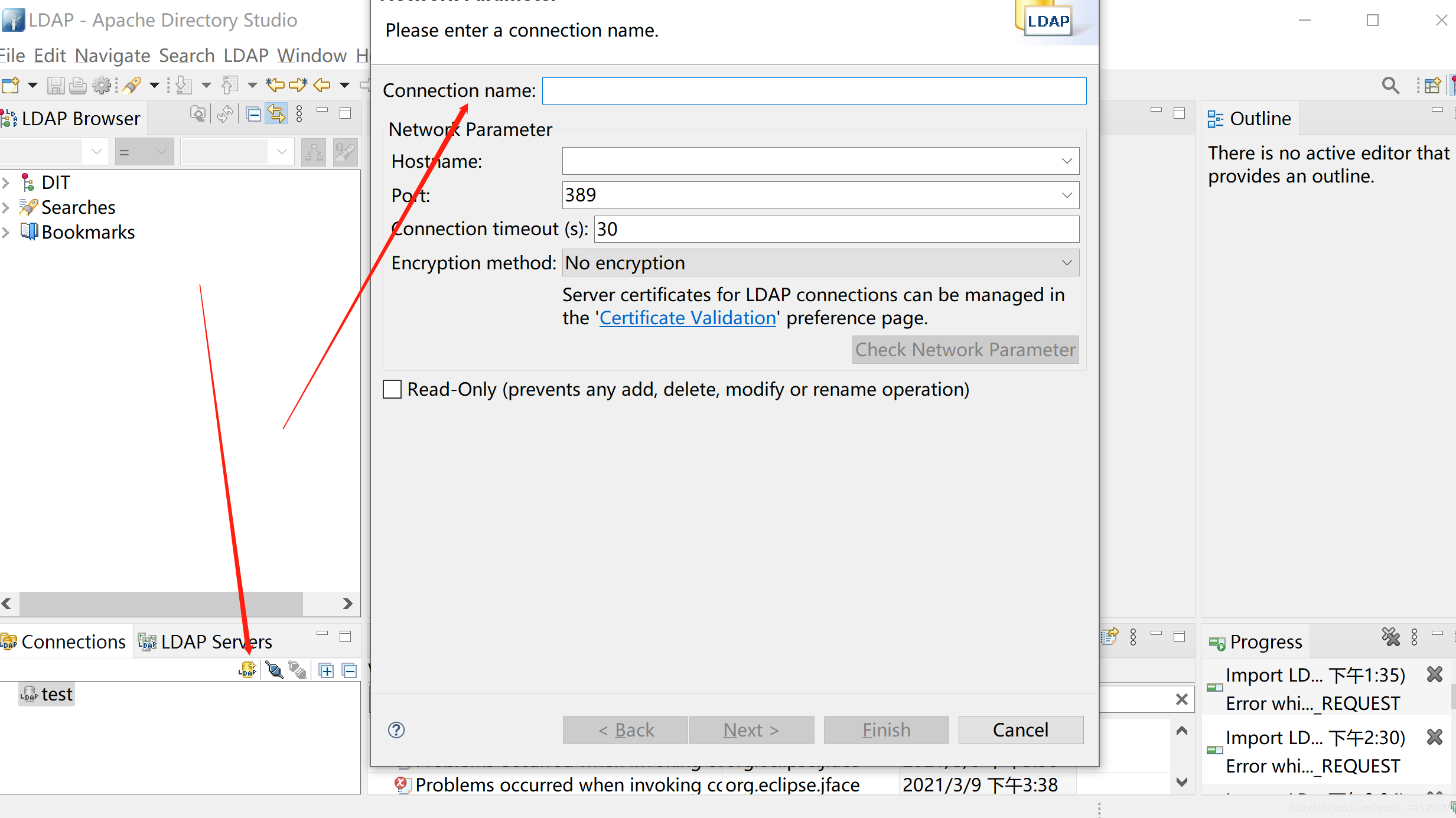
1.4 添加Apache服务端连接
1.5 密码处填写 secret
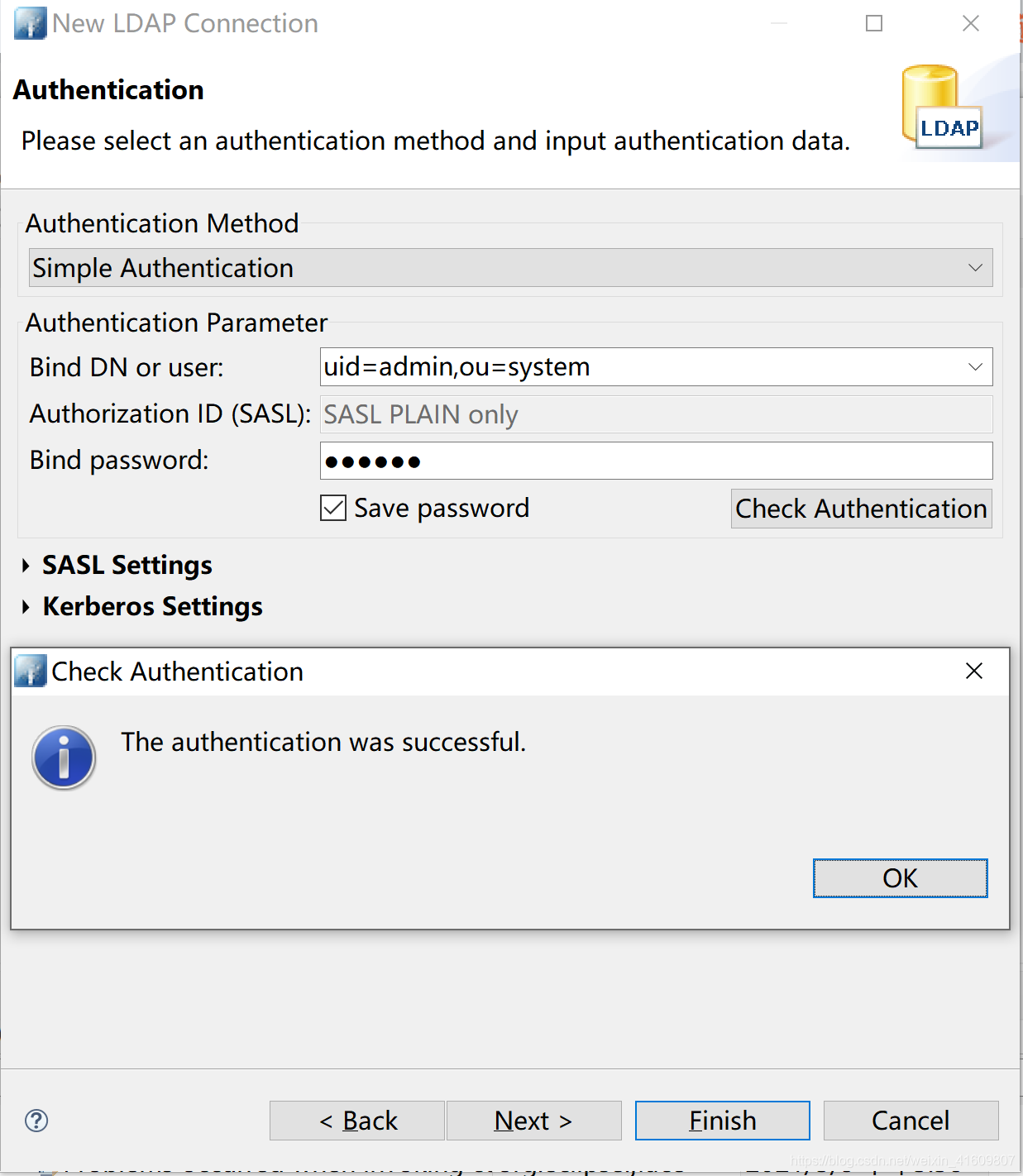
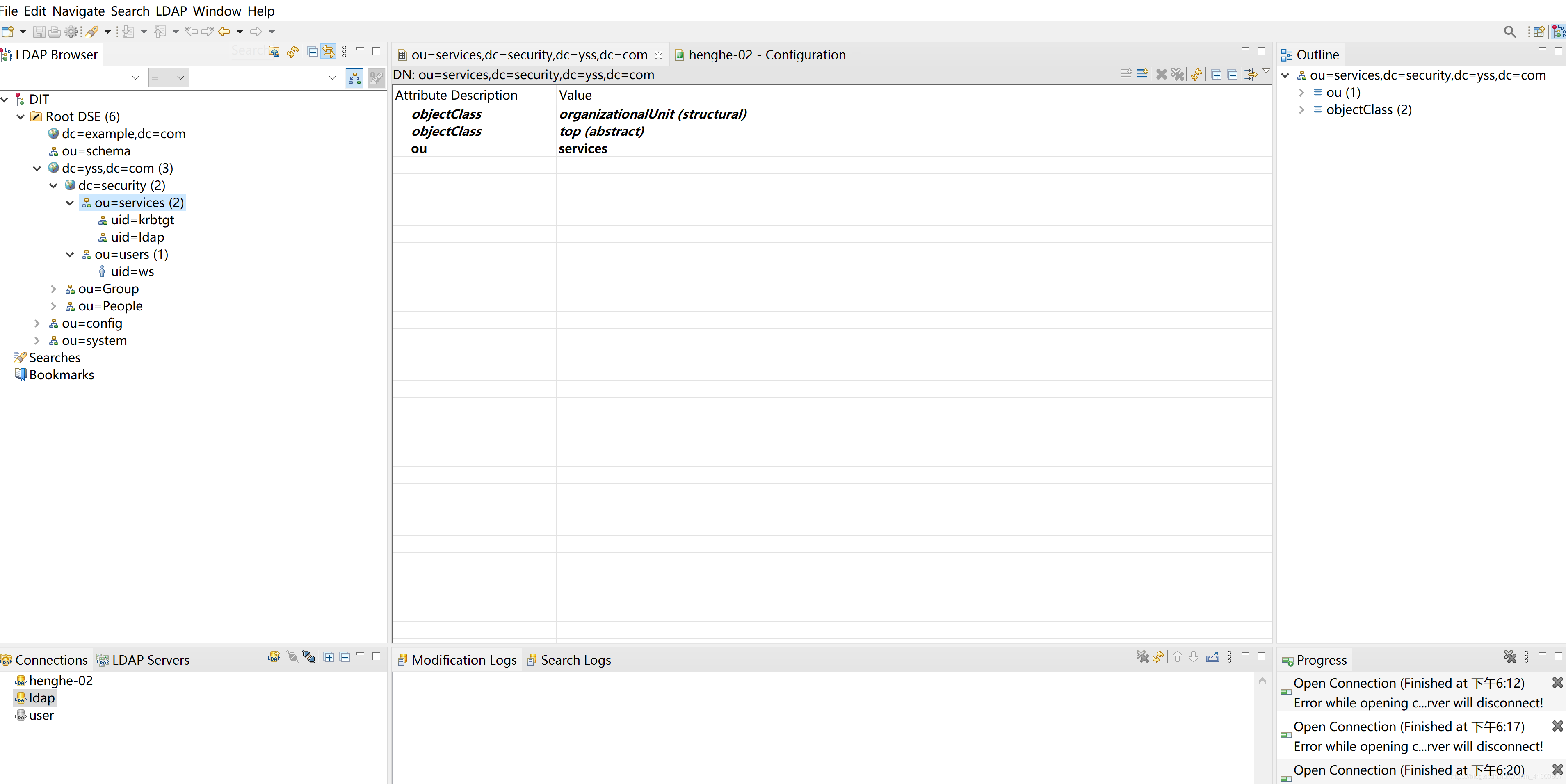
1.6 连接成功并打开
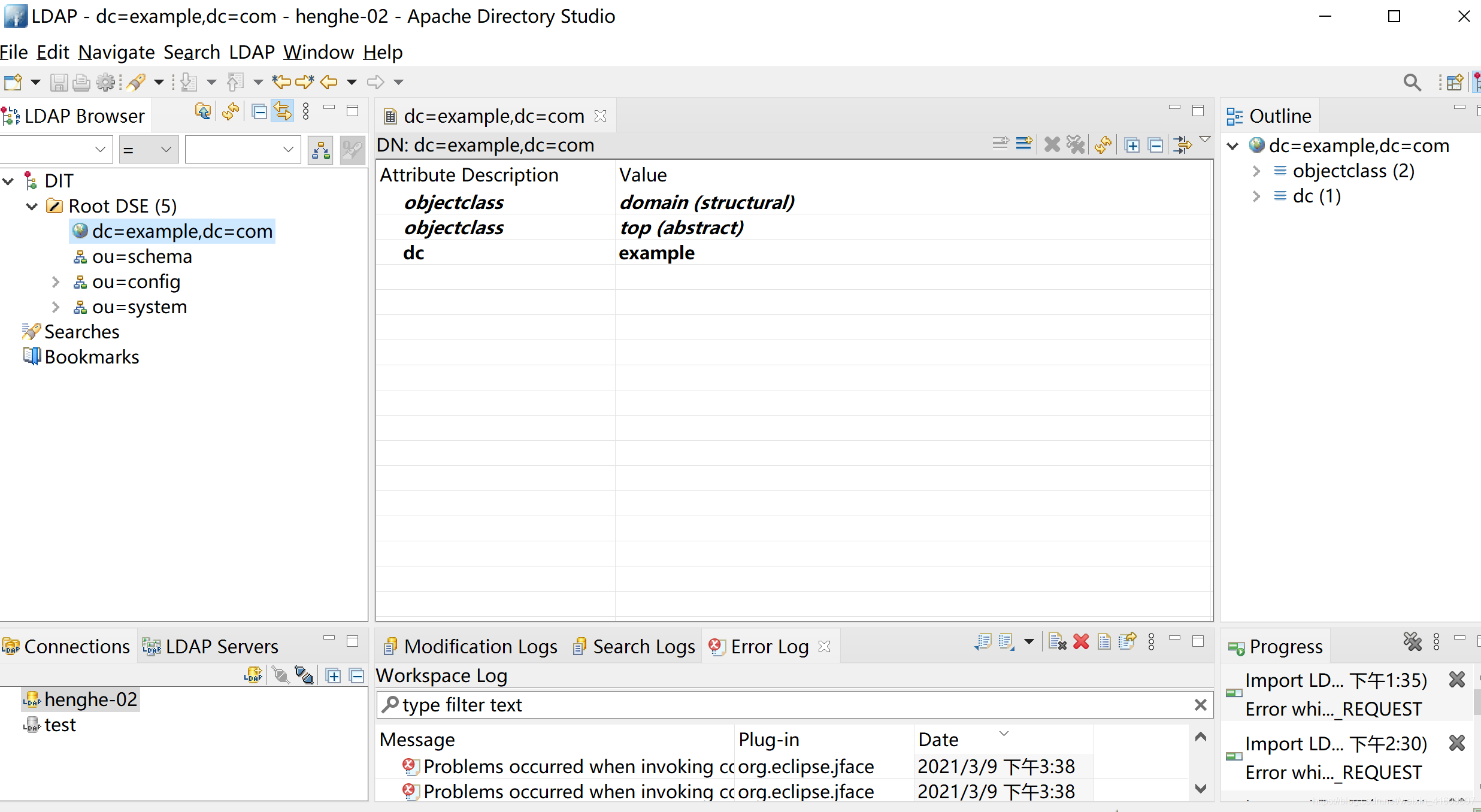
2、添加自定义分区
2.1 打开配置添加自定义分区
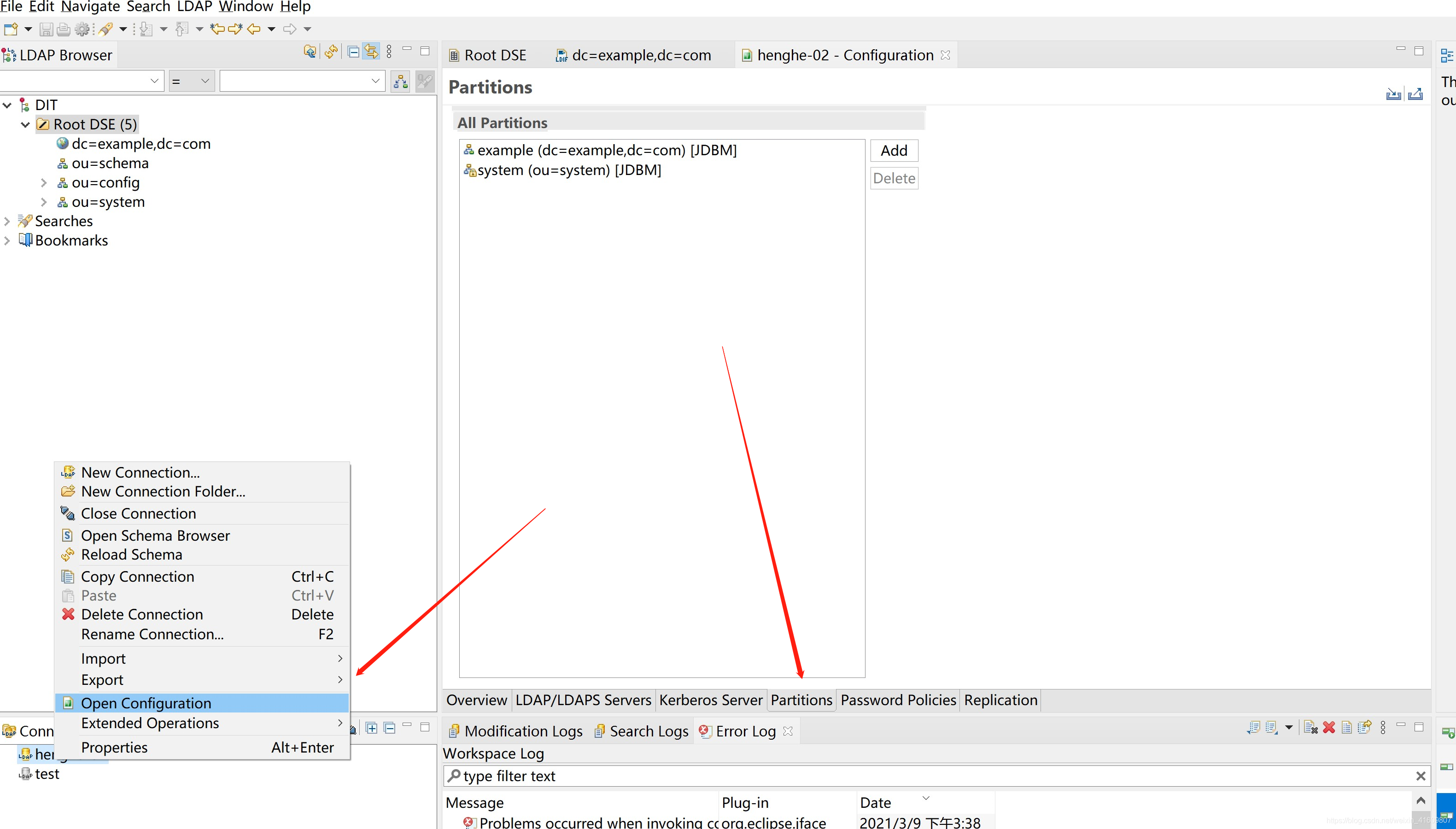
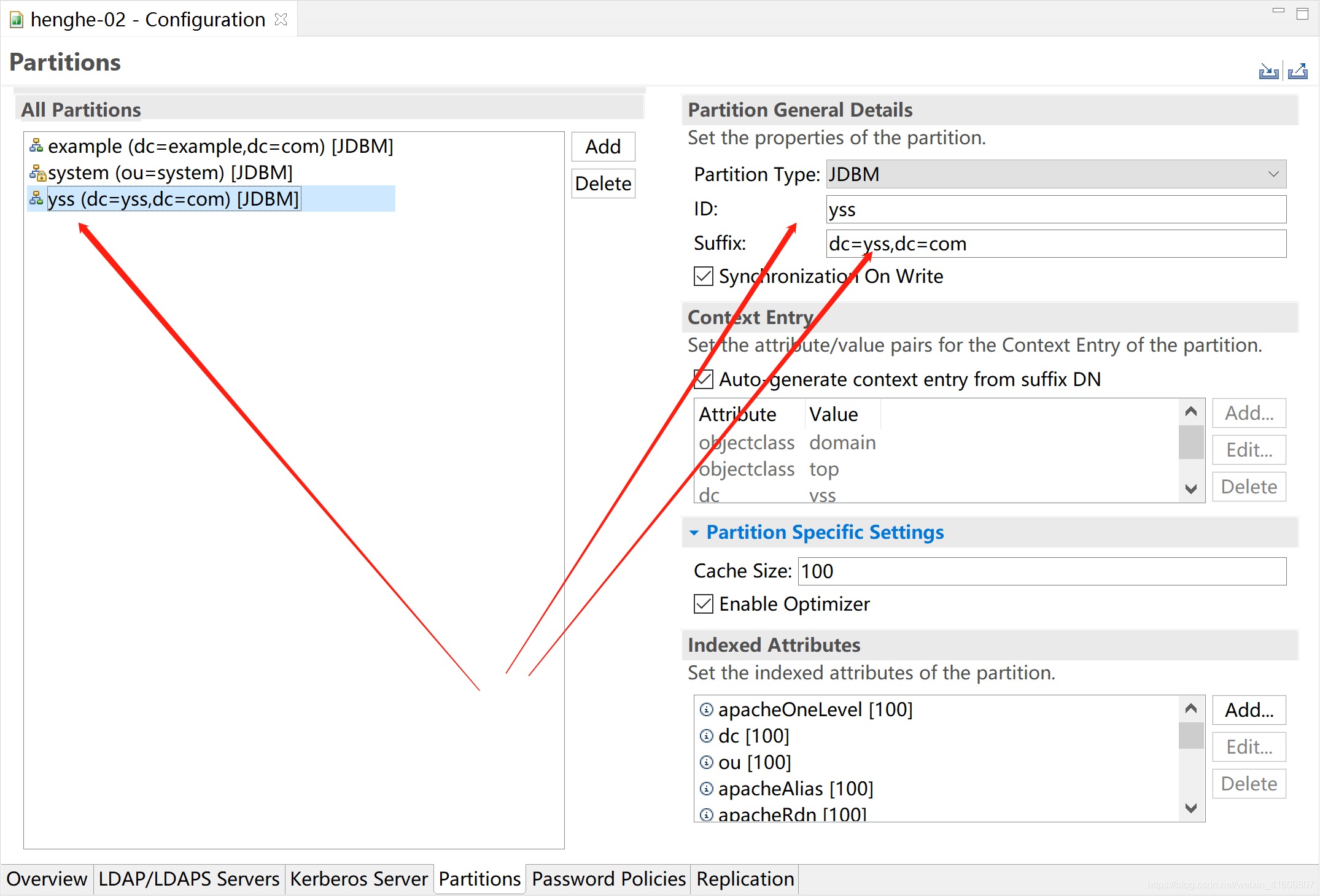
2.2 重启服务刷新连接

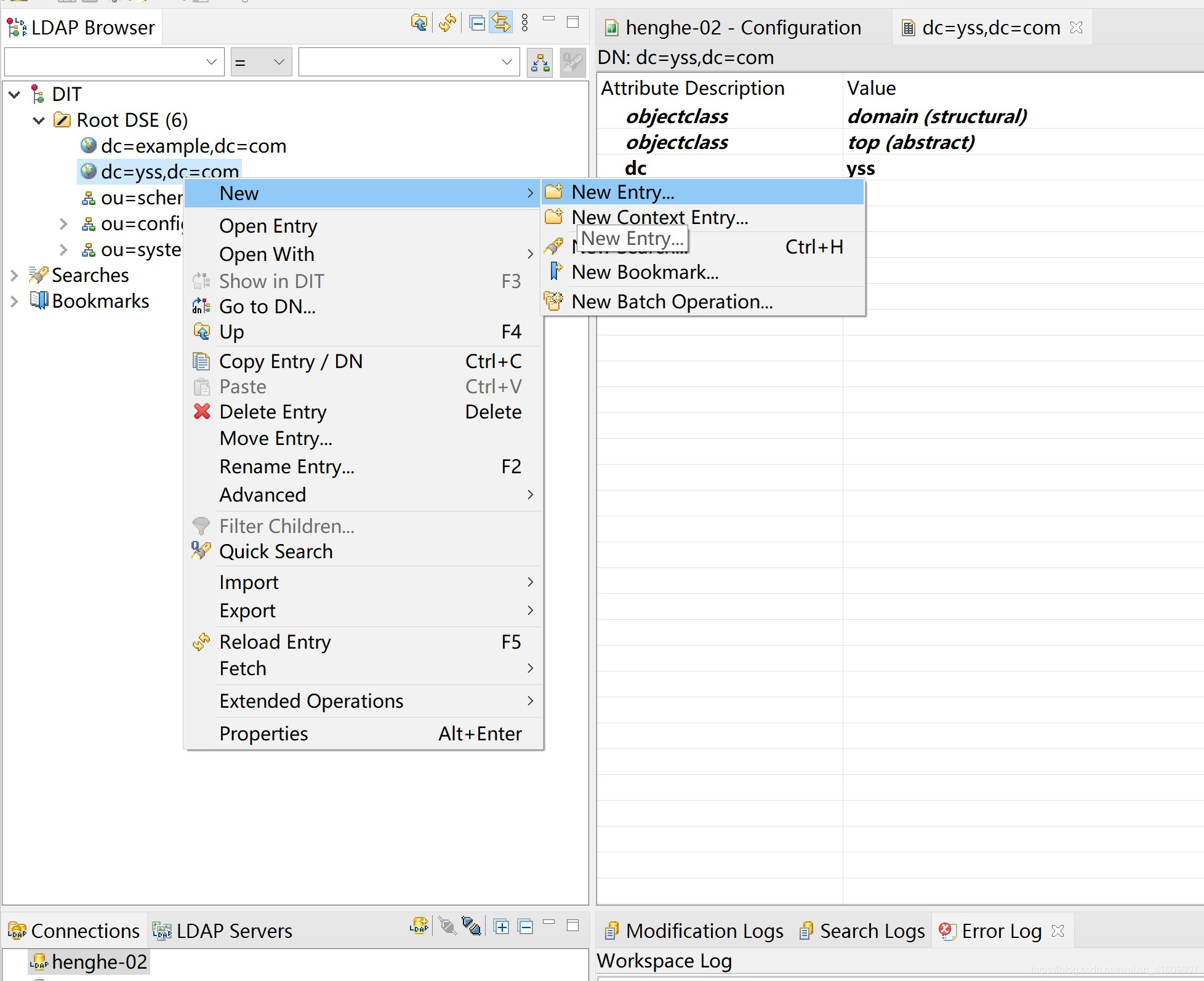
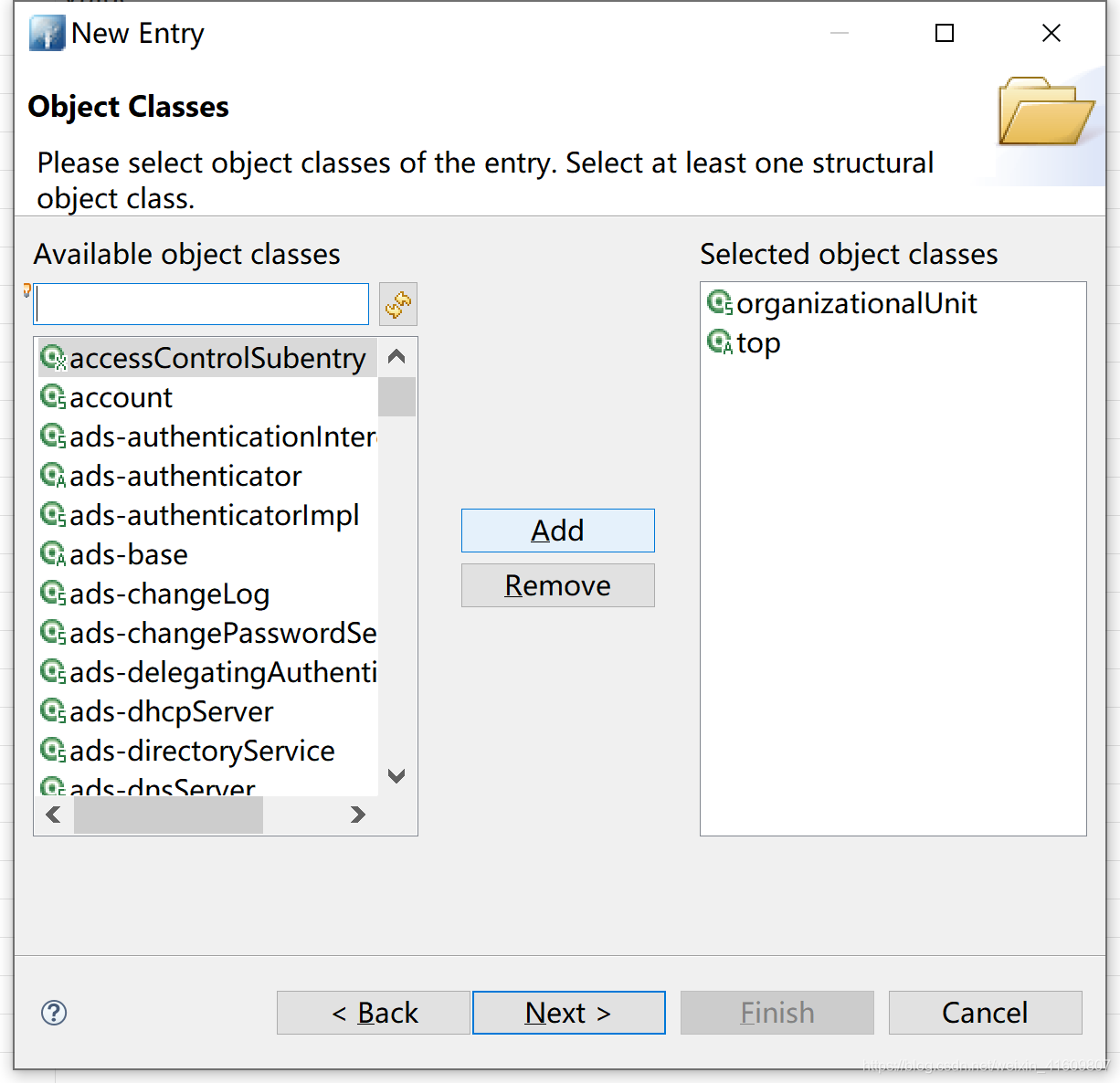
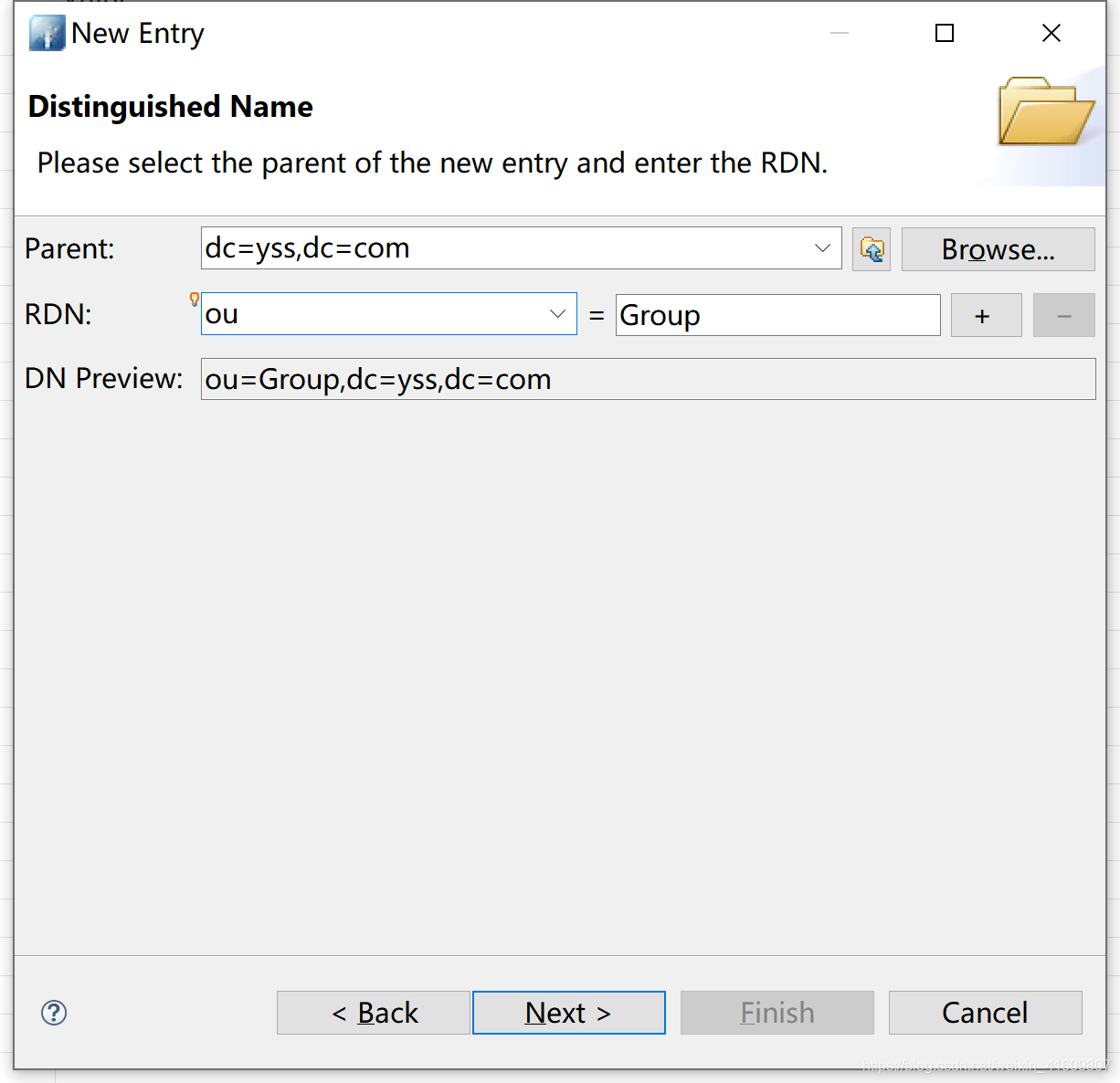
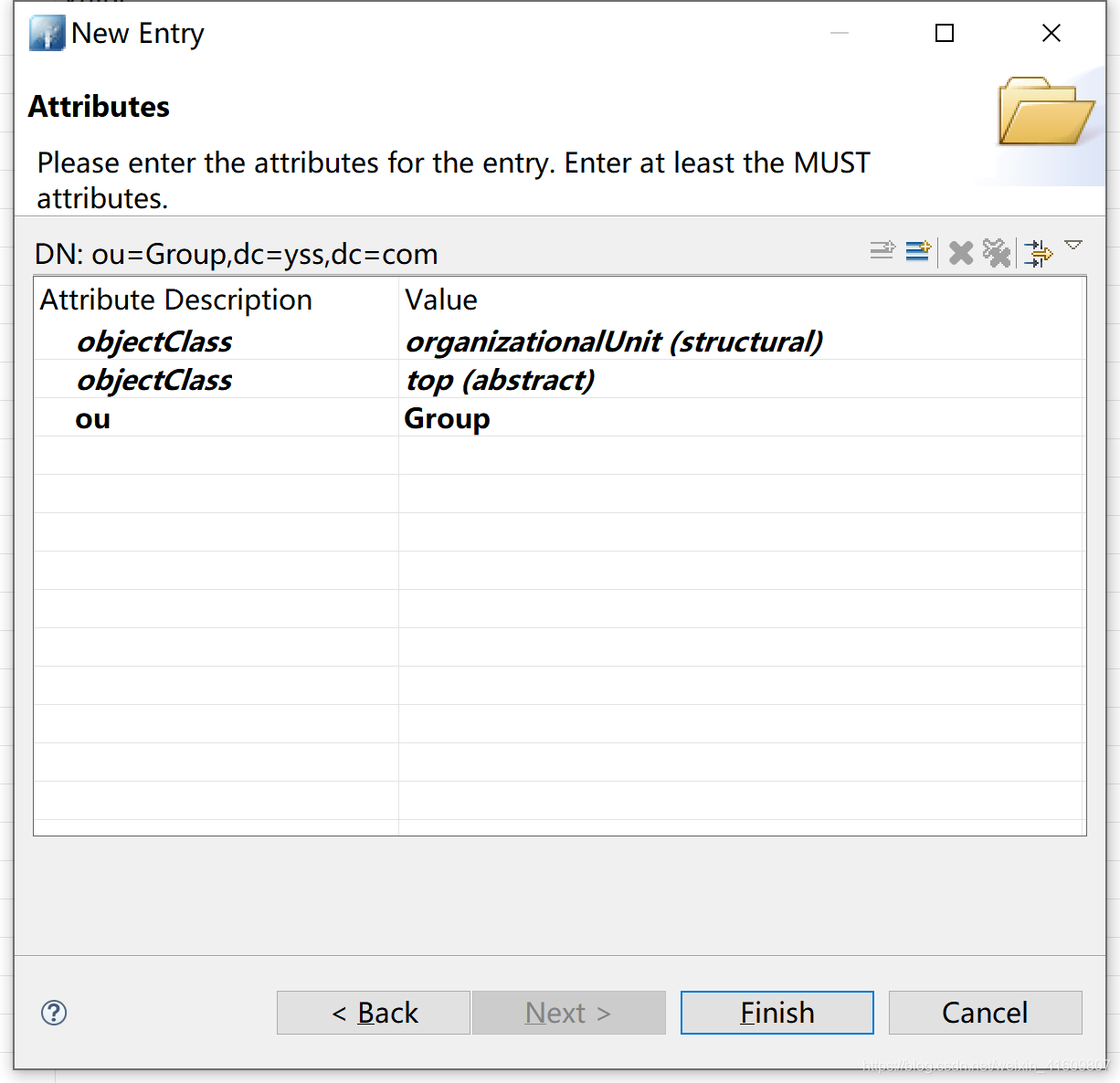
2.3添加组
3、修改配置
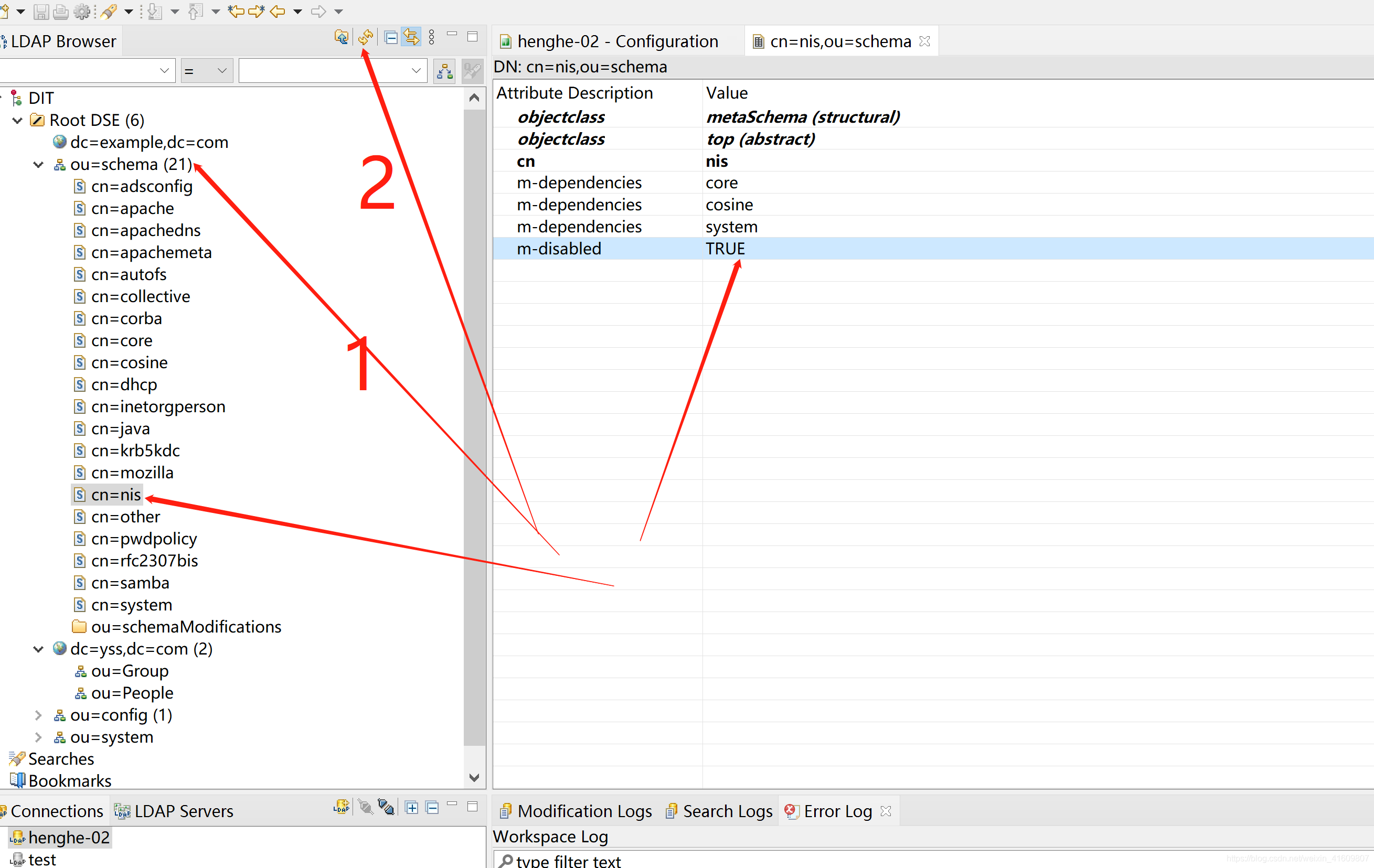
3.1 linux用户schema
将m-disabled配置修改为false,修改之后就可以有posixAccount、posixGroup相关属性。切记修改后要断开重新连接
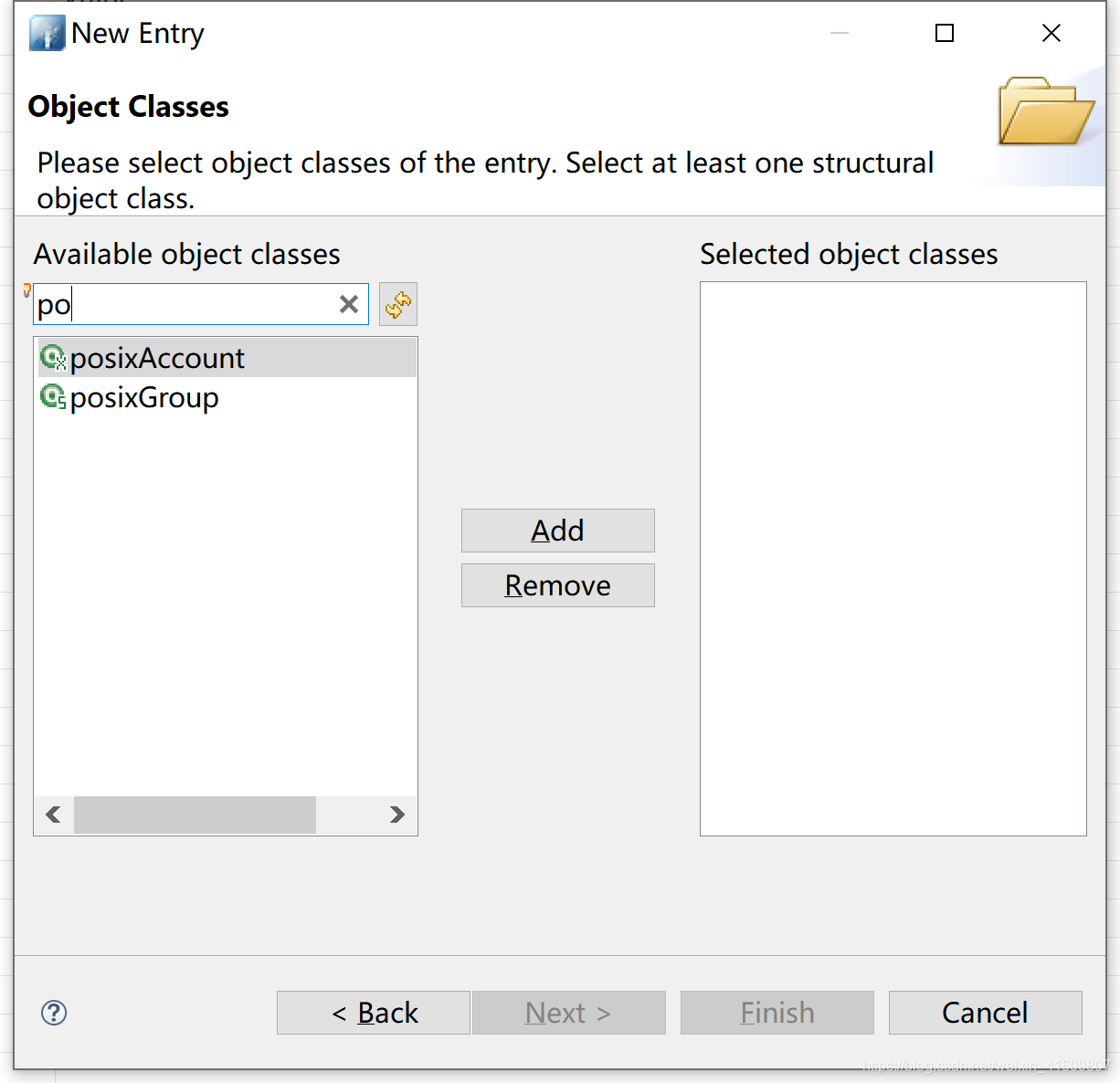
3.2 添加测试组
不存在相关配置时要及时刷新。

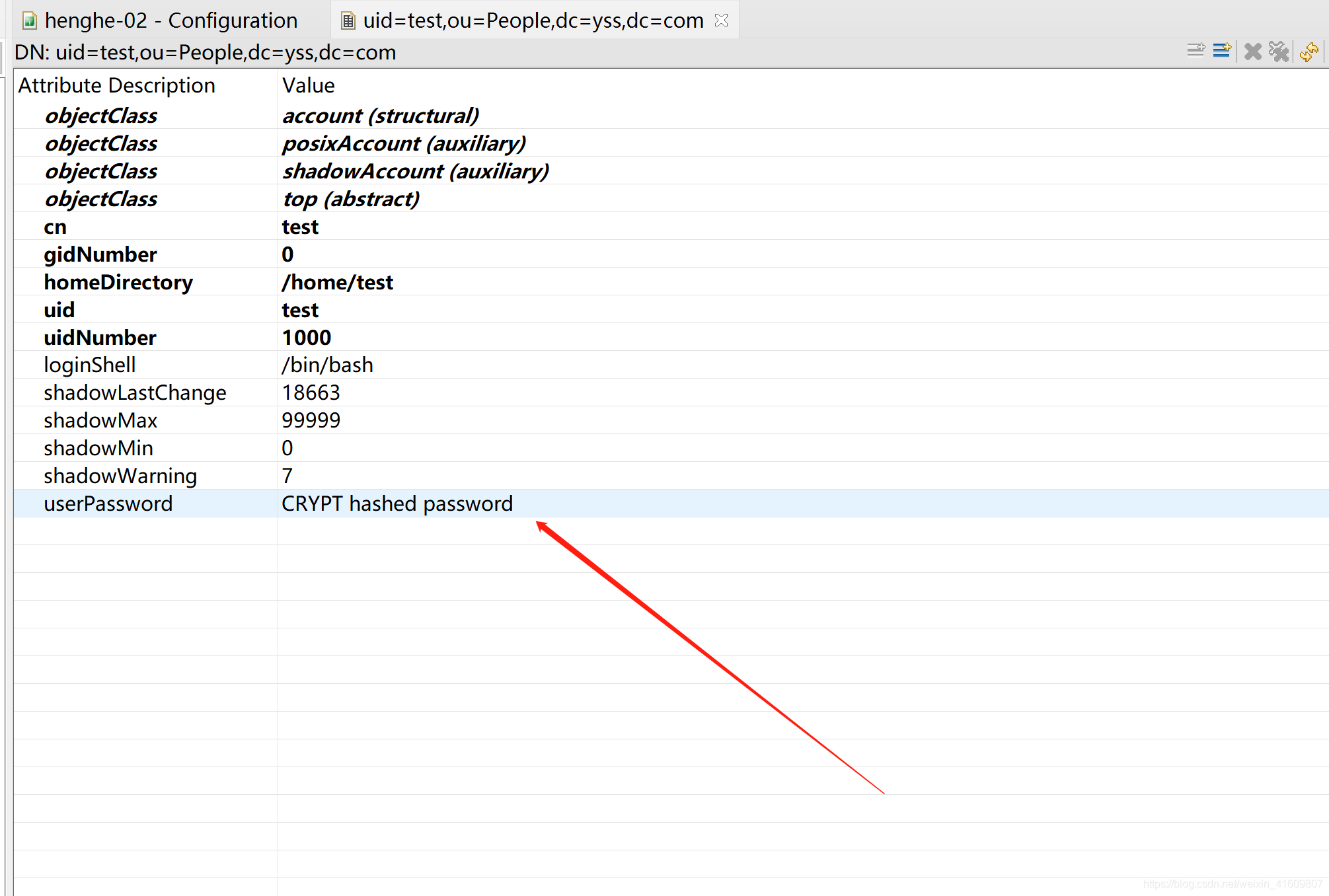
4、添加用户
4.1 创建test.ldif文件
dn: uid=test,ou=People,dc=yss,dc=com
uid: test
cn: test
objectClass: account
objectClass: posixAccount
objectClass: top
objectClass: shadowAccount
userPassword: {crypt}!!
shadowLastChange: 18663
shadowMin: 0
shadowMax: 99999
shadowWarning: 7
loginShell: /bin/bash
uidNumber: 1000
gidNumber: 0
homeDirectory: /home/test
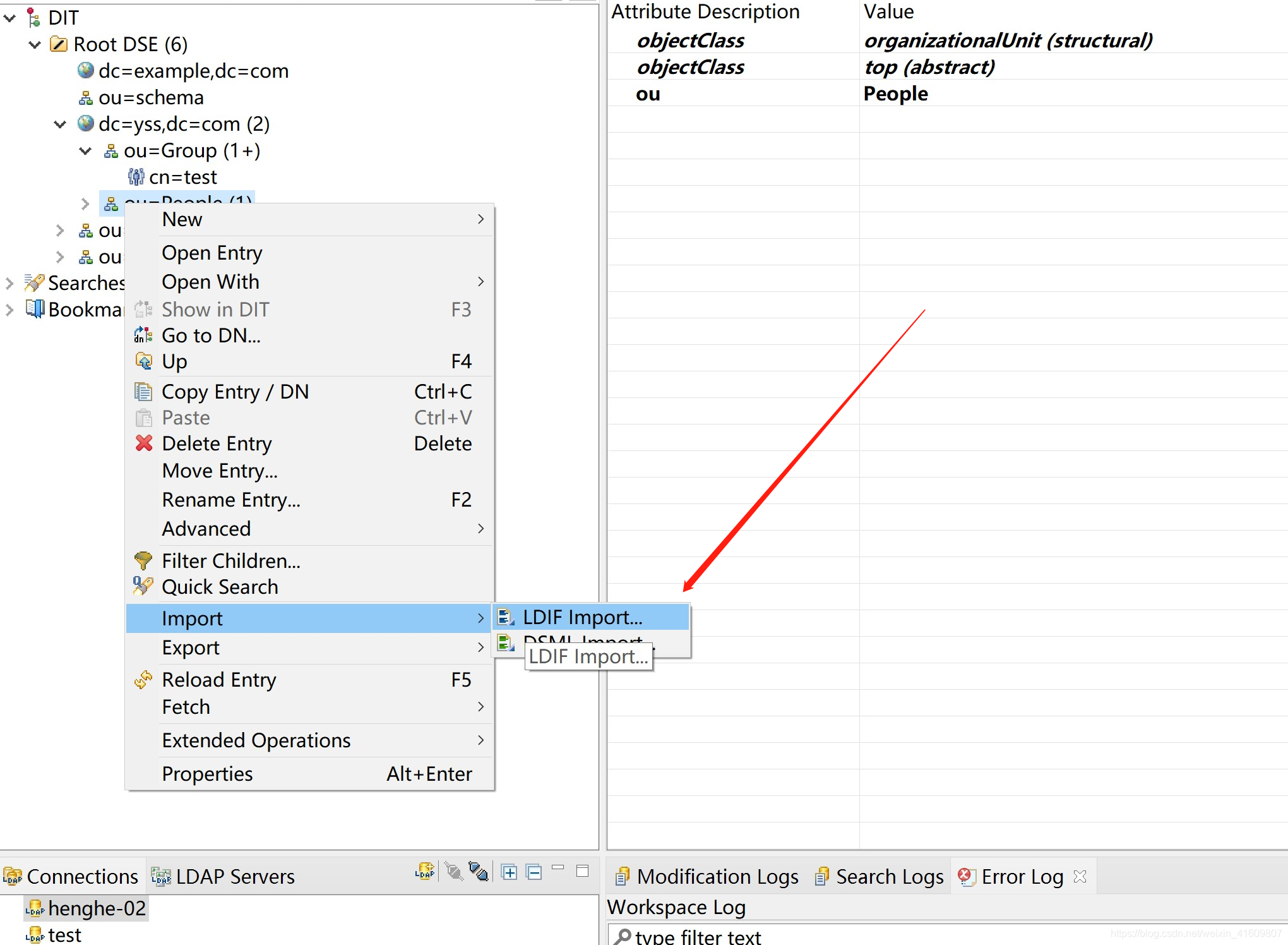
选择刚创建的文件生成用户
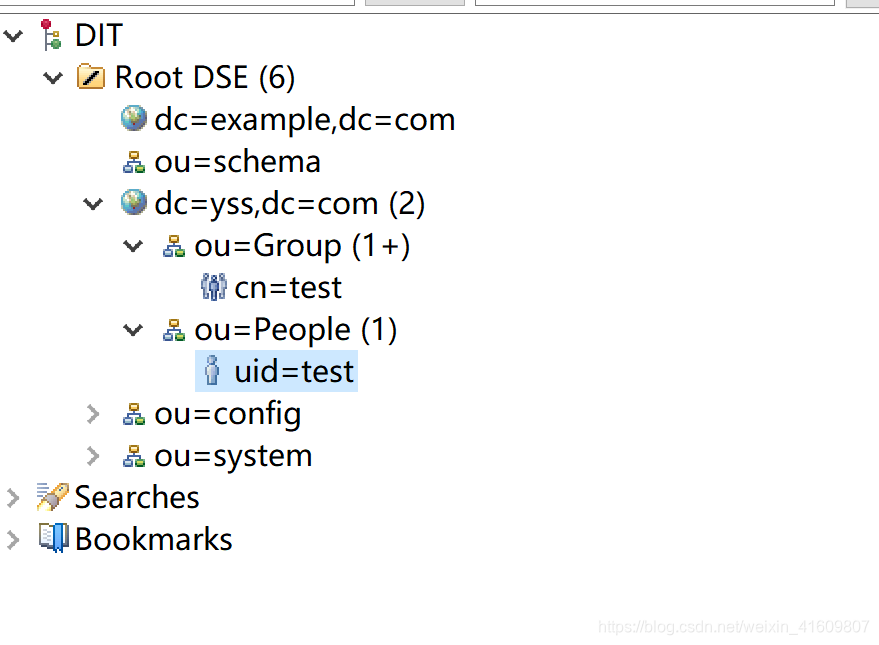
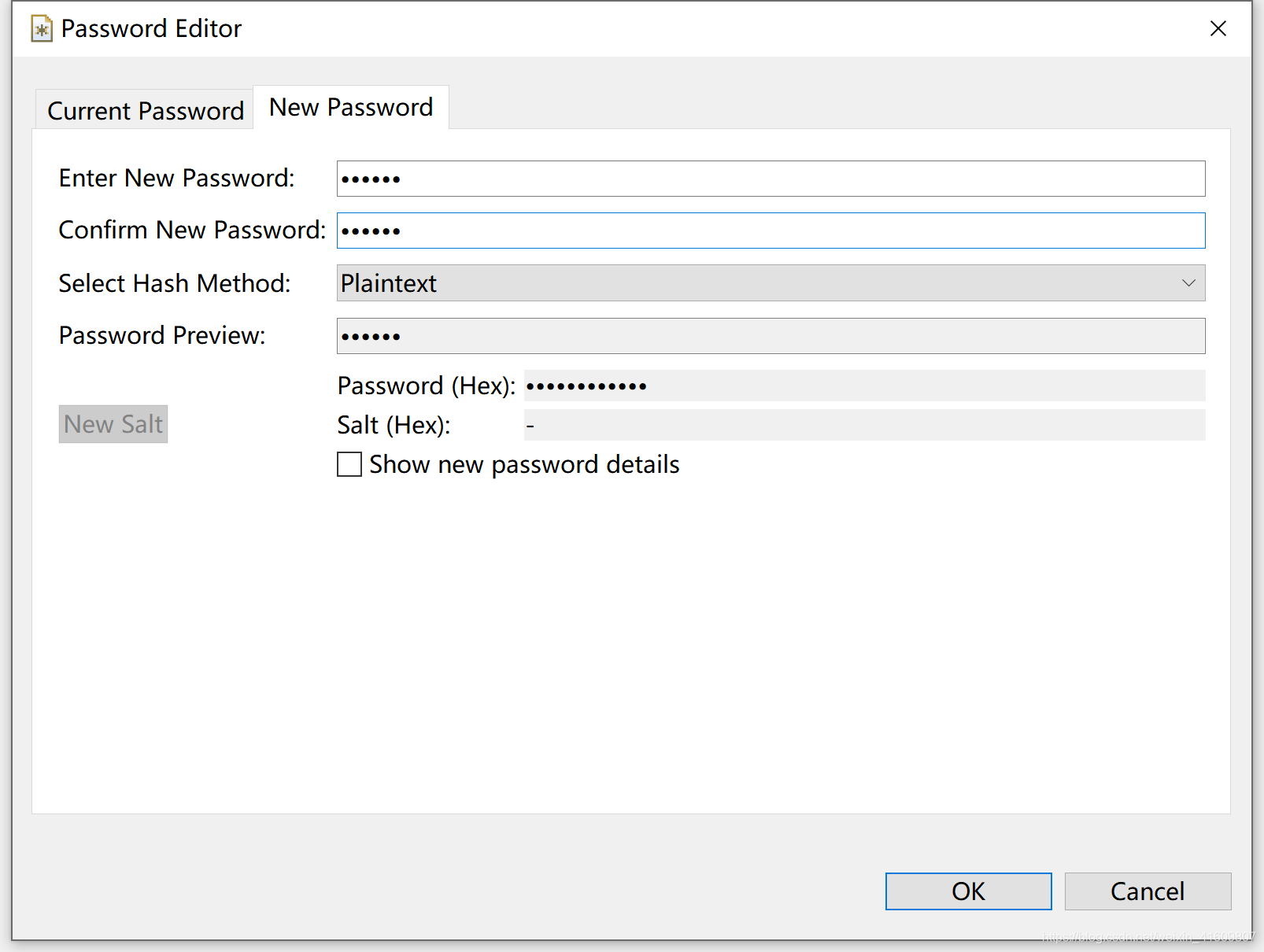
4.2 双击修改用户密码
5、用户同步
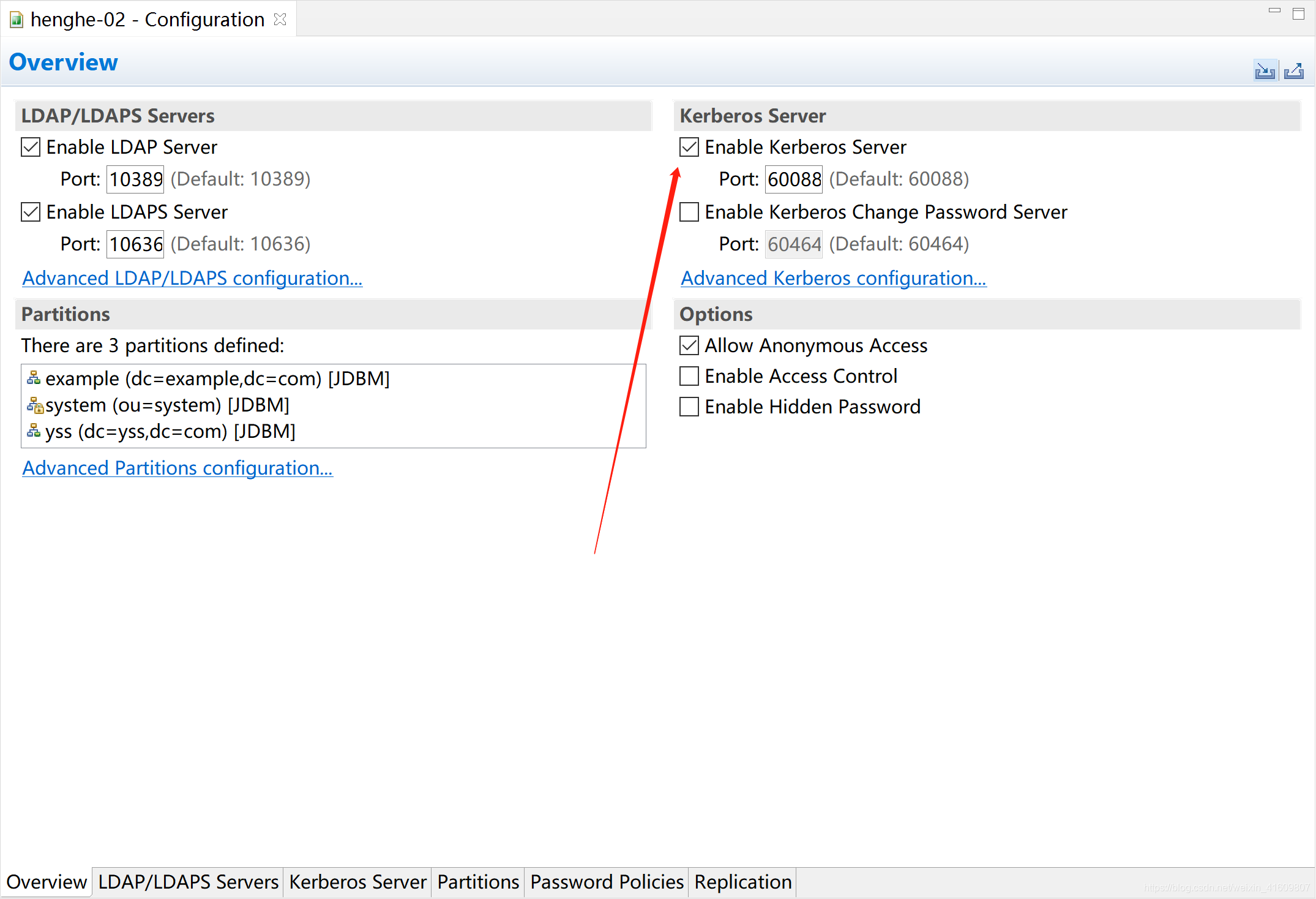
6、ApacheDS 开启Kerberos
6.1 开启Kerberos
-
1.开启kerberos
-
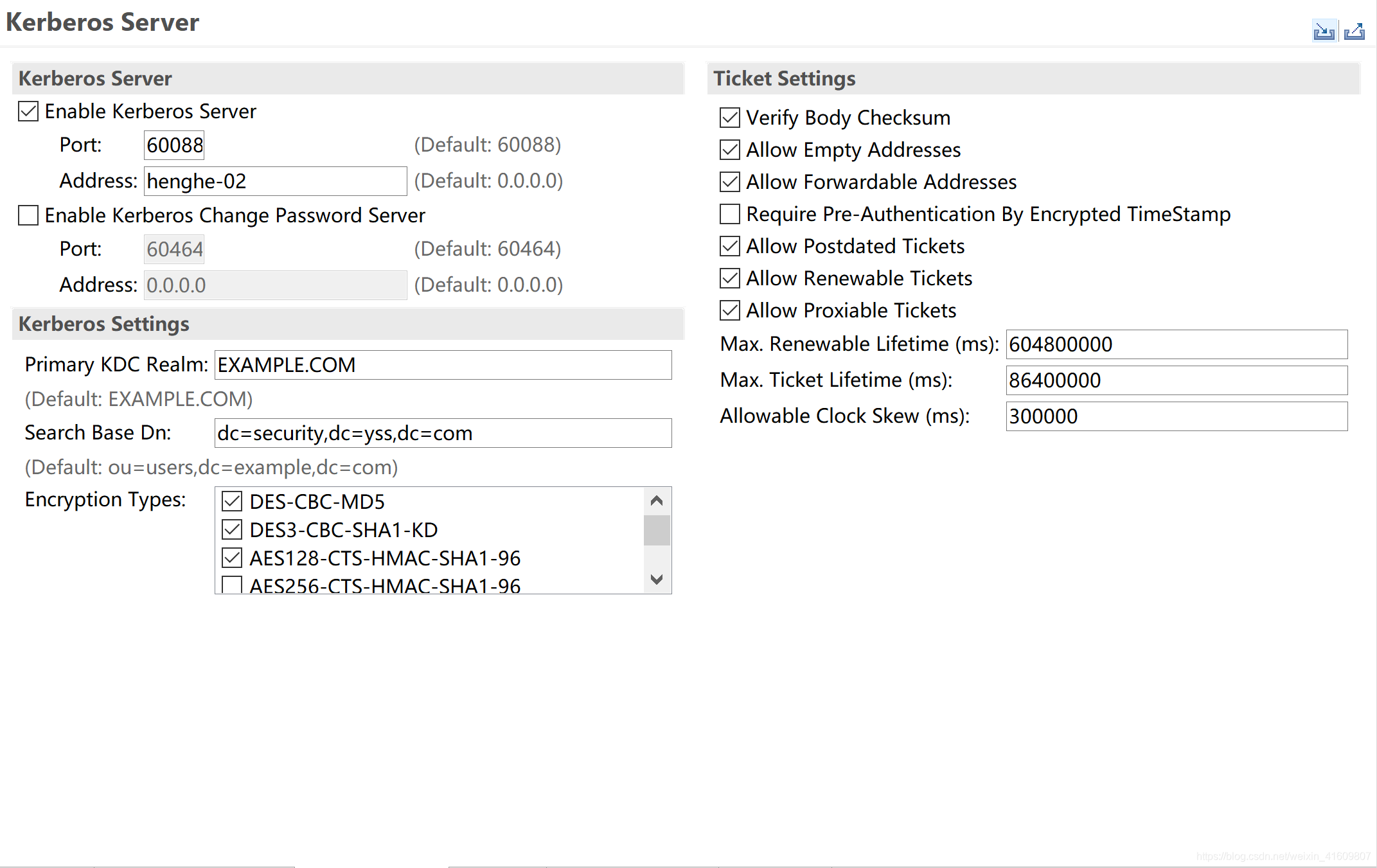
2 kerberos服务器配置
-
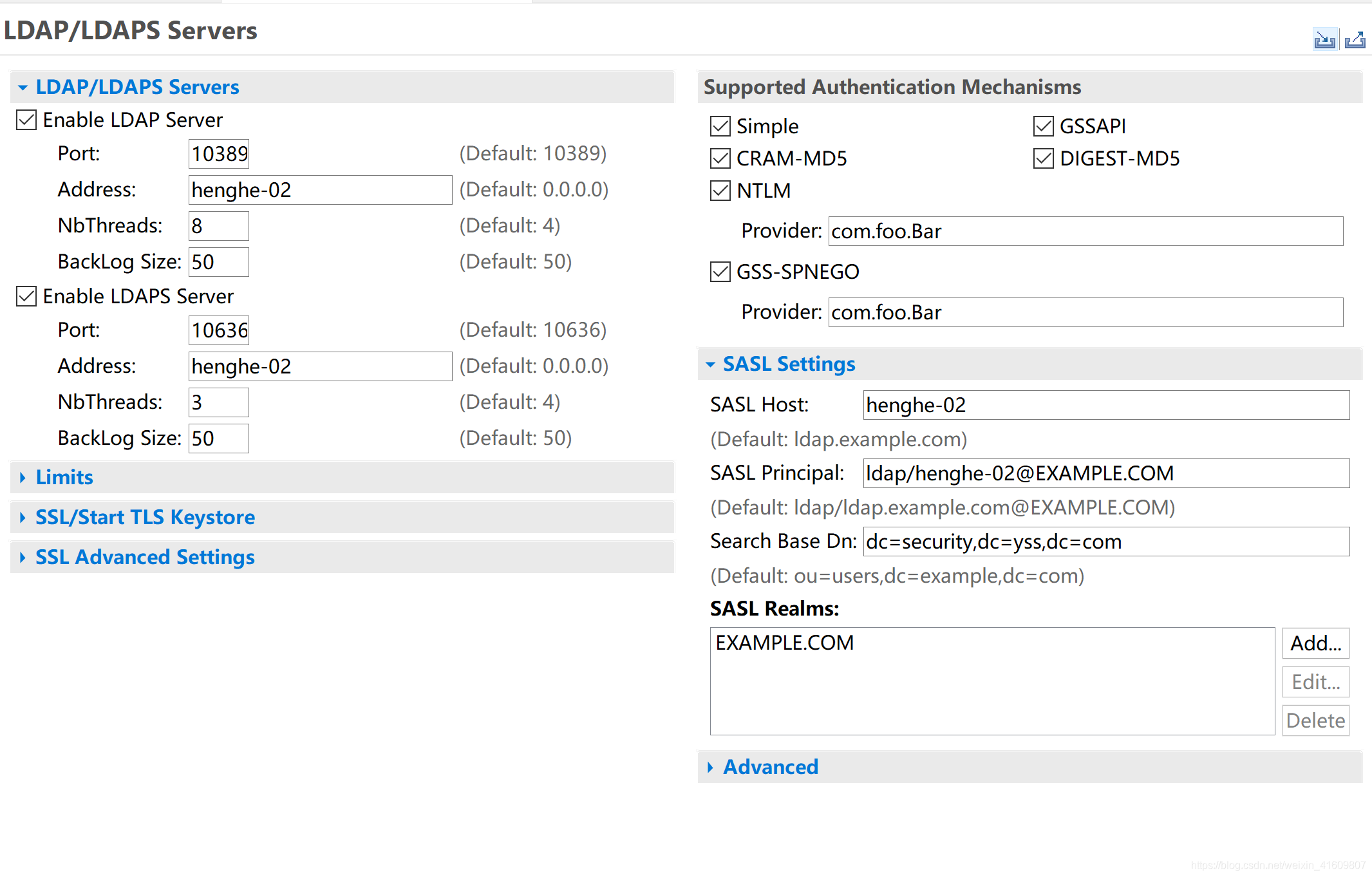
3 LDAP服务器配置
6.2 kerberos client
-
- 安装client
yum install krb5-workstation krb5-libs krb5-auth-dialog
-
- 修改/etc/krb5.conf文件
# Configuration snippets may be placed in this directory as well
#includedir /etc/krb5.conf.d/
#[logging]
# default = FILE:/var/log/krb5libs.log
# kdc = FILE:/var/log/krb5kdc.log
# admin_server = FILE:/var/log/kadmind.log
[libdefaults]
# dns_lookup_realm = false
# ticket_lifetime = 24h
# renew_lifetime = 7d
# forwardable = true
# rdns = false
default_realm = EXAMPLE.COM
# default_ccache_name = KEYRING:persistent:%{uid}
[realms]
EXAMPLE.COM = {
kdc = henghe-02:60088
#admin_server = henghe-02:60088
}
[domain_realm]
.example.com = EXAMPLE.COM
example.com = EXAMPLE.COM
- 修改hostname映射
- 重启ApacheDS使配置生效
./apacheds restart default
6.3 添加kerberos认证用户
- 为添加TGT服务

- 添加TGT服务
创建tgt.ldif文件
dn: uid=krbtgt,ou=services,dc=security,dc=yss,dc=com
objectClass: top
objectClass: organizationalUnit
objectClass: krb5KDCEntry
objectClass: uidObject
objectClass: krb5Principal
krb5KeyVersionNumber: 0
krb5PrincipalName: krbtgt/EXAMPLE.COM@EXAMPLE.COM
uid: krbtgt
userPassword:: randomkey
ou: LDAP
- 创建kerberos认证用户
创建ws.ldif文件
dn: uid=ws,ou=users,dc=security,dc=yss,dc=com
objectClass: top
objectClass: krb5KDCEntry
objectClass: inetOrgPerson
objectClass: krb5Principal
objectClass: person
objectClass: organizationalPerson
cn: Horatio Nelson
krb5KeyVersionNumber: 1
krb5PrincipalName: ws@EXAMPLE.COM
sn: Nelson
uid: ws
userPassword: ws
- 创建ldap认证服务
创建ldap.ldif文件
dn: uid=ldap,ou=services,dc=security,dc=yss,dc=com
objectClass: top
objectClass: organizationalUnit
objectClass: krb5KDCEntry
objectClass: uidObject
objectClass: krb5Principal
krb5KeyVersionNumber: 0
krb5PrincipalName: ldap/henghe-02@EXAMPLE.COM
uid: ldap
userPassword: randomKey
ou: TGT
- 将创建的文件依次导入
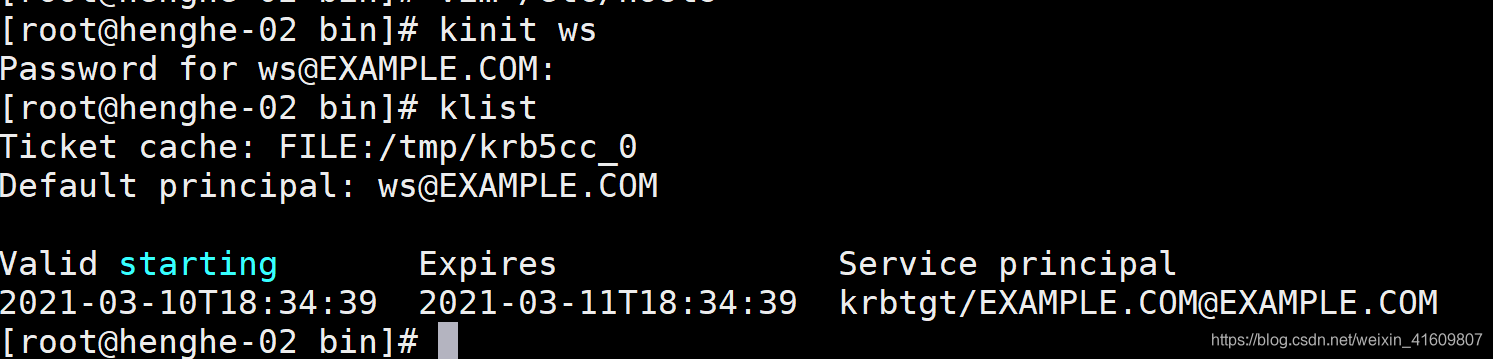
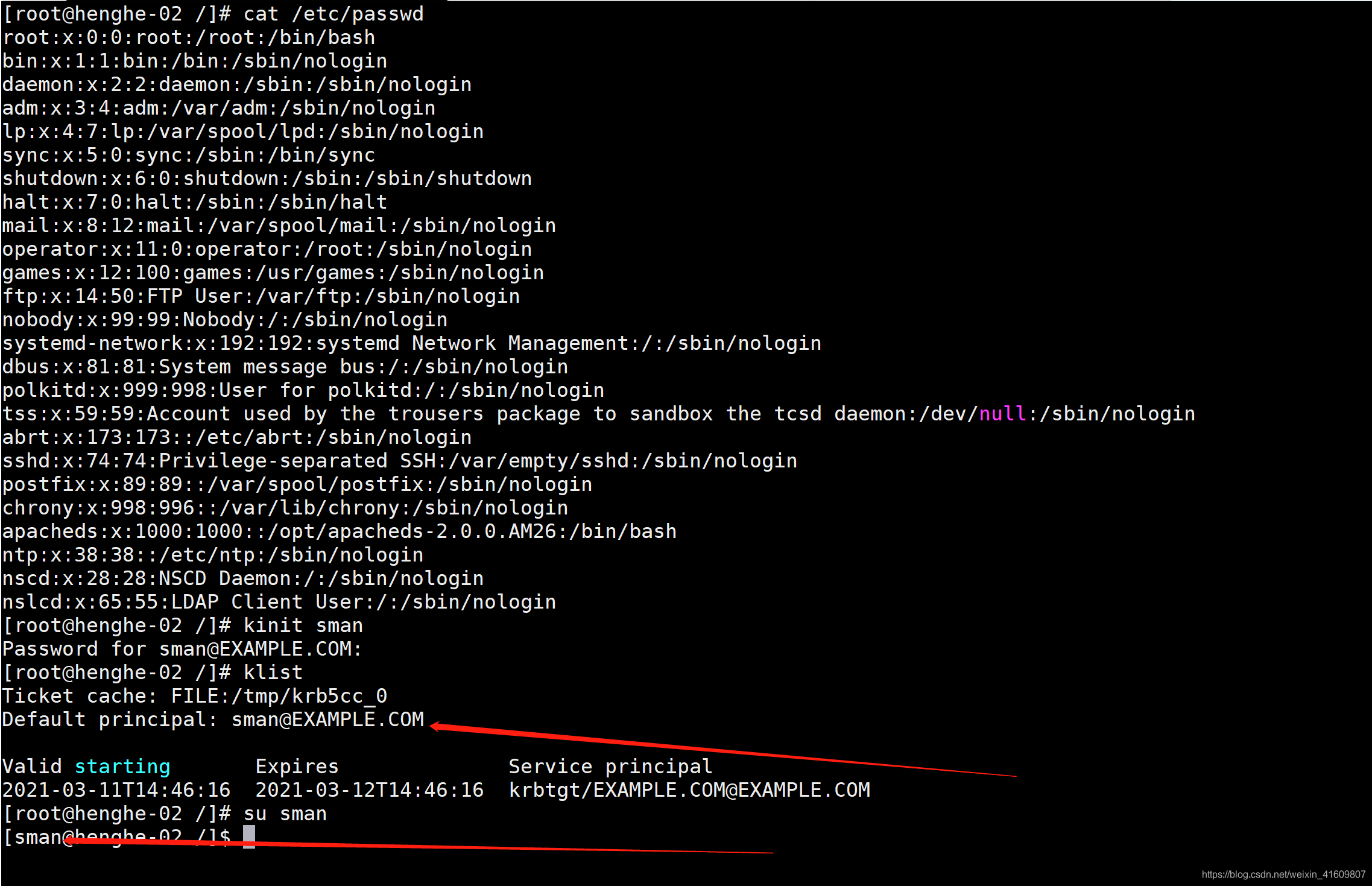
6.4 kinit认证
6.5 ldap登录认证
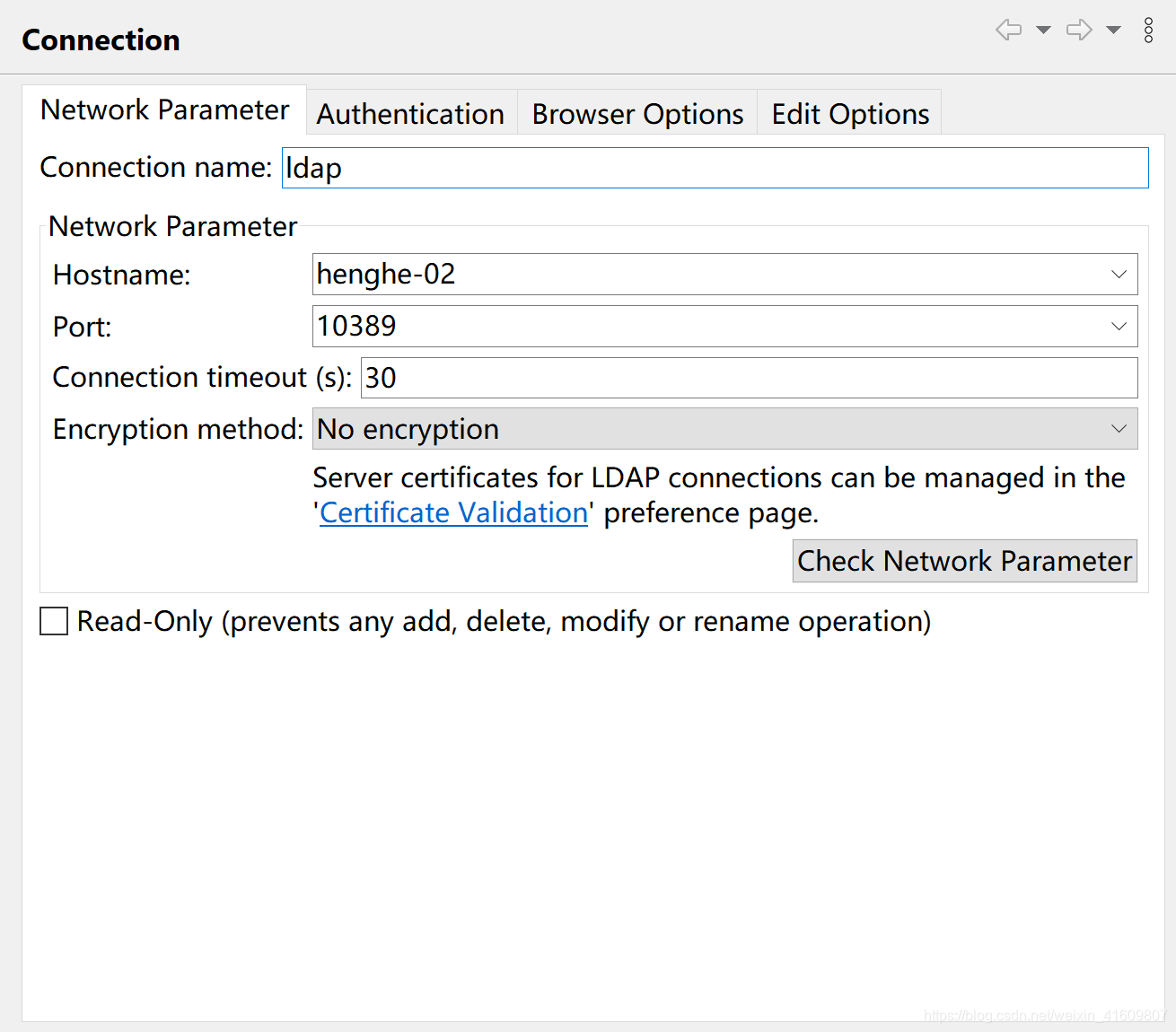
- 配置网络
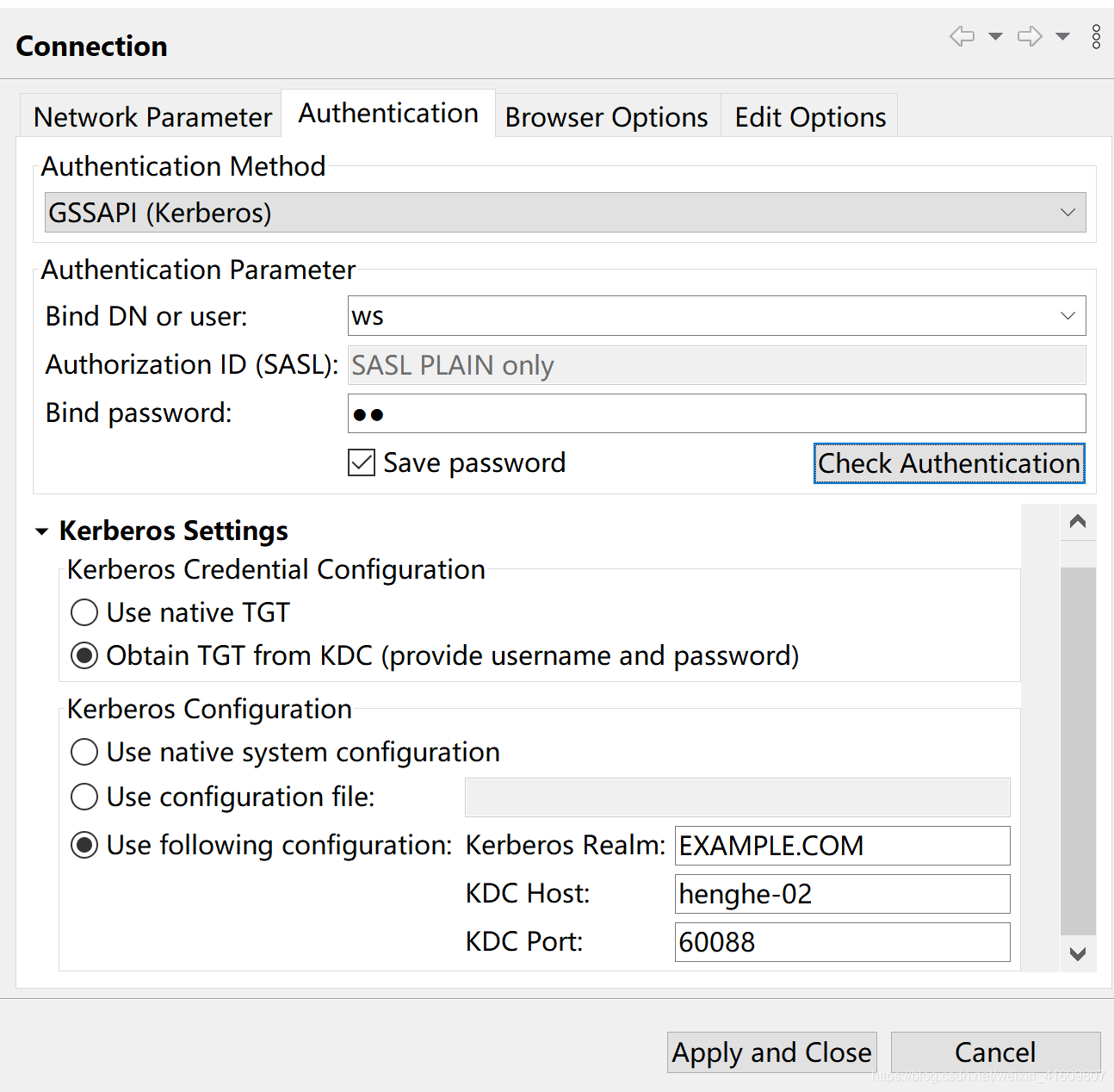
- 配置用户
- 登录成功
6.6 linux与kerberos用户统一
- sman用户的ldif配置
dn: uid=sman,ou=users,dc=security,dc=yss,dc=com
objectClass: inetOrgPerson
objectClass: krb5KDCEntry
objectClass: krb5Principal
objectClass: organizationalPerson
objectClass: person
objectClass: posixAccount
objectClass: shadowAccount
objectClass: top
cn: sman
gidNumber: 1009
homeDirectory: /home/sman
krb5KeyVersionNumber: 1
krb5PrincipalName: sman@EXAMPLE.COM
sn: sman
uid: sman
uidNumber: 10084
krb5Key:: MBGgAwIBA6EKBAgs3IwczpIjCA==
krb5Key:: MBmgAwIBEaESBBDZ4KQ8CUaBfkx/xz+Mo6nf
krb5Key:: MBmgAwIBF6ESBBA+wfd6dpePW9BH3npNz4gx
krb5Key:: MCGgAwIBEKEaBBhMSqjaSWQWy4yiAaQq6lgVdvhu1jjaFtM=
loginShell: /bin/bash
shadowLastChange: 18663
shadowMax: 99999
shadowMin: 0
shadowWarning: 7
userPassword:: e1NTSEF9eG5LRUJMNVljNTA4amtkQ3NBLzA2NW1QU3ltOEFVMS9KUjVOclE9P
Q==
- 验证用户























 959
959











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








