参考链接:
github 输出中的特殊元素转义处理不恰当(注入)
github 在命令中使用的特殊元素转义处理不恰当(命令注入)
Vulnerability Details : CVE-2020-10518
Vulnerability Details : CVE-2020-10519
漏洞影响范围:
GitHub Enterprise Server < 2.22
漏洞级别:
阿里云ARMS显示高级
阿里云漏洞库未评级
cvedetails评分:
CVE-2020-10518
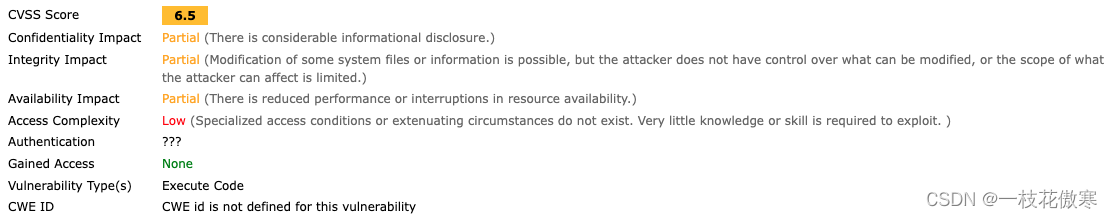
CVE-2020-10519

备注:
CVSS得分基于一系列维度上的测量结果,这些测量维度被称为量度(Metrics)。
漏洞的最终得分最大为10,最小为0。
得分7~10的漏洞通常被认为比较严重
得分在4~6.9之间的是中级漏洞
得分0~3.9的则是低级漏洞
漏洞描述:
A remote code execution vulnerability was identified in GitHub Enterprise Server that could be exploited when building a GitHub Pages site. User-controlled configuration of the underlying parsers used by GitHub Pages were not sufficiently restricted and made it possible to execute commands on the GitHub Enterprise Server instance. To exploit this vulnerability, an attacker would need permission to create and build a GitHub Pages site on the GitHub Enterprise Server instance. This vulnerability affected all versions of GitHub Enterprise Server prior to 2.22 and was fixed in 2.21.6, 2.20.15, and 2.19.21. The underlying issues contributing to this vulnerability were identified both internally and through the GitHub Security Bug Bounty program.
解决方案:
如果未使用GitHub Enterprise Server,则不需要修复
如果使用了,更新当前系统或软件至最新版,完成漏洞的修复























 90
90











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








