往期博文:
DVWA靶场-Brute Force Source 暴力破解
靶场环境搭建
目录
File Upload
Low File Upload
核心代码
<?php
if( isset( $_POST[ 'Upload' ] ) ) {
// Where are we going to be writing to?
$target_path = DVWA_WEB_PAGE_TO_ROOT . "hackable/uploads/";
$target_path .= basename( $_FILES[ 'uploaded' ][ 'name' ] );
// Can we move the file to the upload folder?
if( !move_uploaded_file( $_FILES[ 'uploaded' ][ 'tmp_name' ], $target_path ) ) {
echo '<pre>Your image was not uploaded.</pre>';
}
else {
// Yes!
echo "<pre>{$target_path} succesfully uploaded!</pre>";
}
}
?>low 级别对上传的文件没有任何的过滤,并且会输出文件上传成功后保存的路径
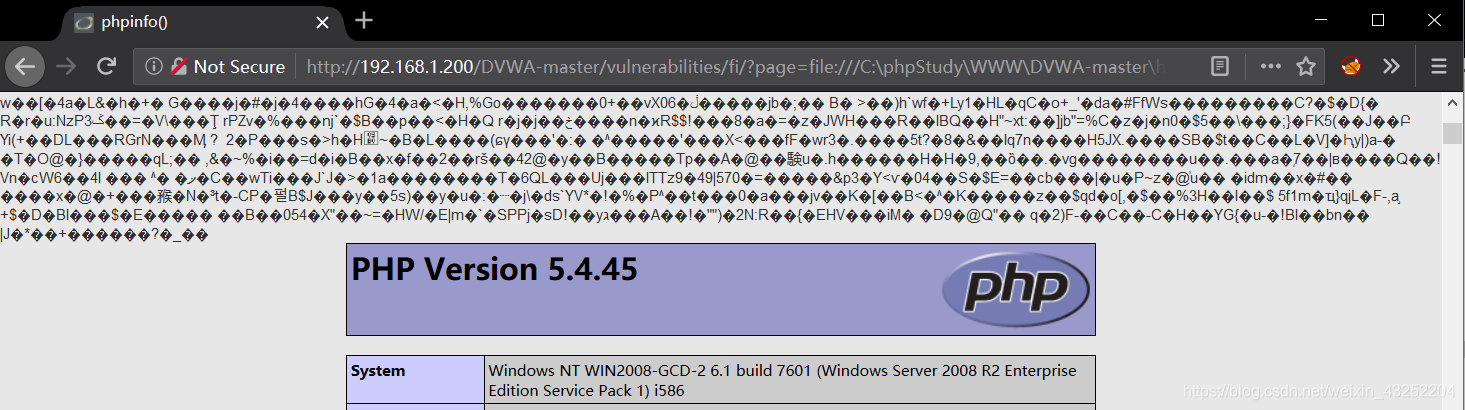
我们本地构造info.php 文件
<?php phpinfo(); ?>
将其上传
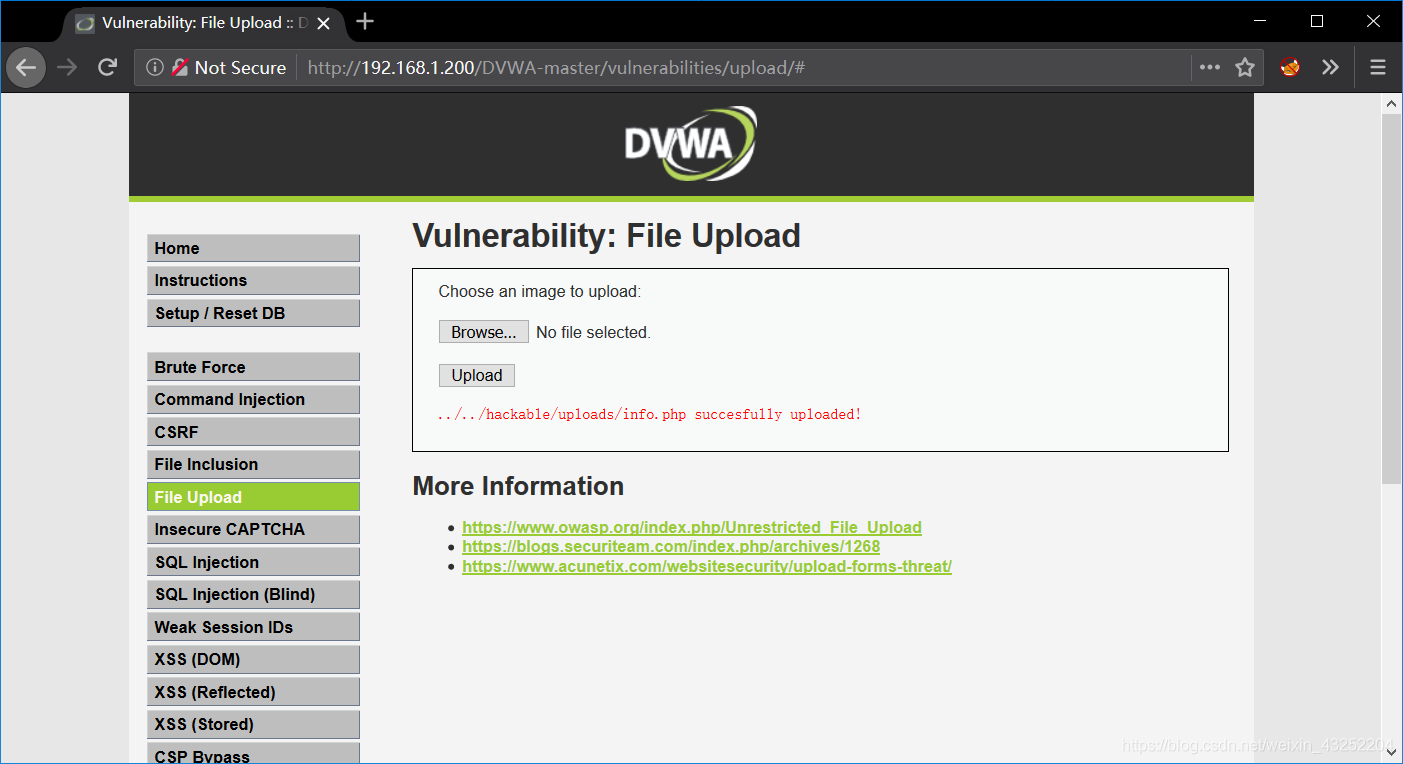
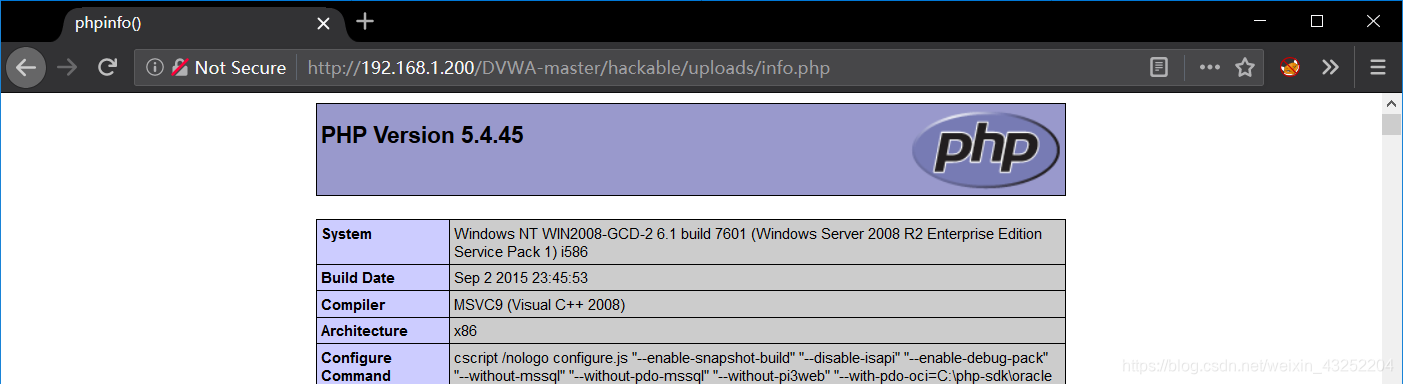
上传成功后,使用输出的路径直接追加到当前页面的url 之后
../../hackable/uploads/info.php
Medium File Upload
核心代码
<?php
// File information
$uploaded_name = $_FILES[ 'uploaded' ][ 'name' ];
$uploaded_type = $_FILES[ 'uploaded' ][ 'type' ];
$uploaded_size = $_FILES[ 'uploaded' ][ 'size' ];
// Is it an image?
if( ( $uploaded_type == "image/jpeg" || $uploaded_type == "image/png" ) &&
( $uploaded_size < 100000 ) )
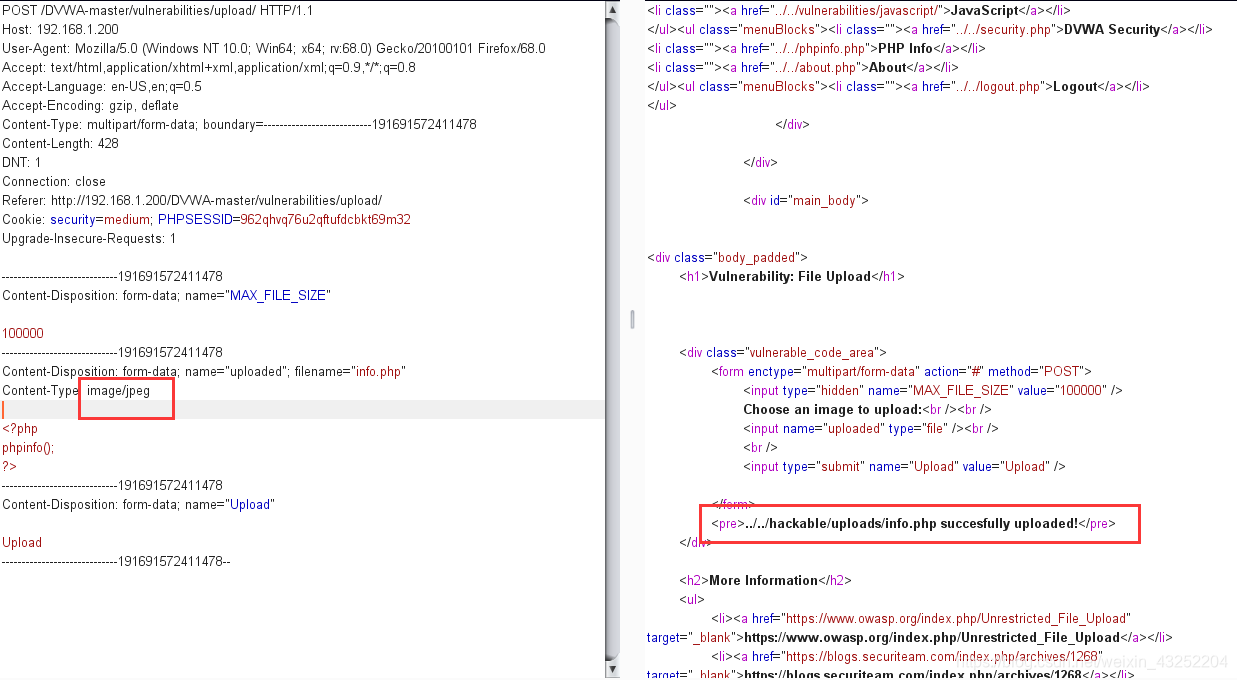
?>中级相较于初级增加了文件类型检测机制,我们只需要通过bp 抓包,修改tyoe 参数即可绕过
High File Upload
核心代码
<?php
if( isset( $_POST[ 'Upload' ] ) ) {
$uploaded_name = $_FILES[ 'uploaded' ][ 'name' ];
//取得文件后缀名
$uploaded_ext = substr( $uploaded_name, strrpos( $uploaded_name, '.' ) + 1);
$uploaded_size = $_FILES[ 'uploaded' ][ 'size' ];
$uploaded_tmp = $_FILES[ 'uploaded' ][ 'tmp_name' ];
// 判断后缀名是否为jpg,jpeg,png
if( ( strtolower( $uploaded_ext ) == "jpg" || strtolower( $uploaded_ext ) == "jpeg" || strtolower( $uploaded_ext ) == "png" ) &&
( $uploaded_size < 100000 ) &&
//getimagesize 进行图片检测
getimagesize( $uploaded_tmp ) ) {
?>这里的getimagesize 函数会对我们上传的图片进行验证,我们可以通过制作图片木马来绕过这个函数,
windows下 制作图片木马
copy pic.png/b+info.php/a info.png
linux下 制作图片木马
# 将 info.php 内容追加到 pic.png
cat info.php >> pic.png
# png + php 合成 png 图马
cat pic.png info.php >> info.png
# 直接 echo 追加
echo '<?php phpinfo();?>' >> pic.png
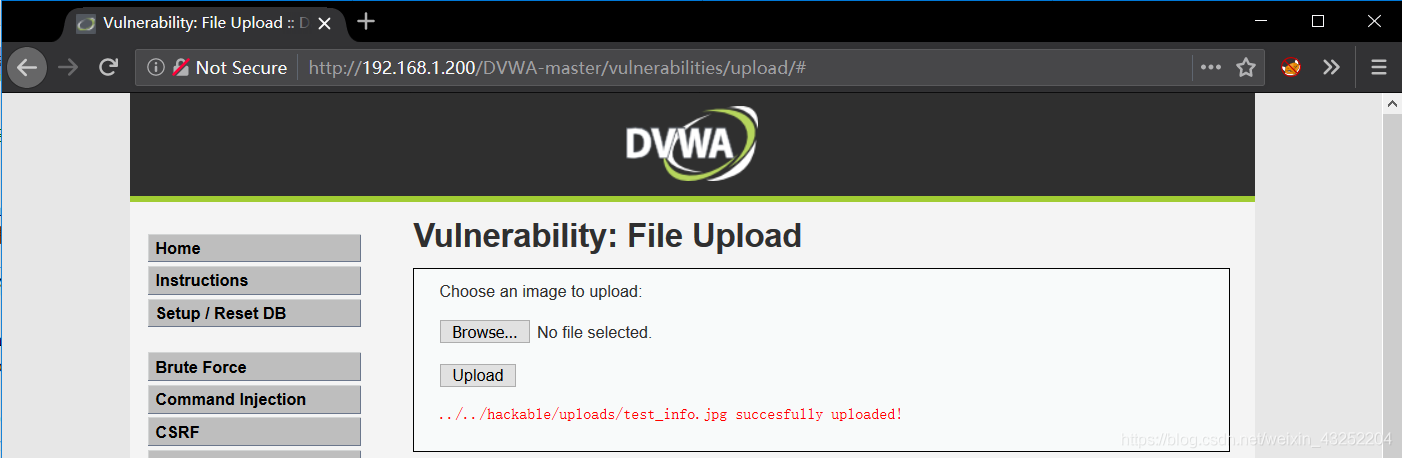
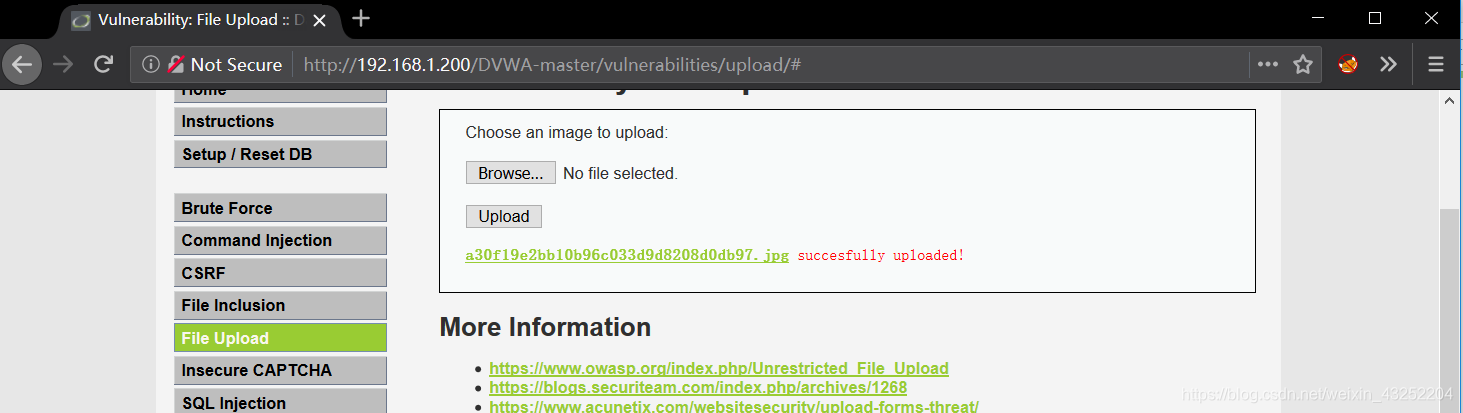
上传成功
这里我们结合文件包含漏洞去验证我们上传的图片木马
vulnerabilities/fi/?page=file:///C:\phpStudy\WWW\DVWA-master\hackable\uploads\test_info.jpg
Impossible File Upload
核心代码
<?php
// token 防御csrf
checkToken( $_REQUEST[ 'user_token' ], $_SESSION[ 'session_token' ], 'index.php' );
//使用时间戳的md5值作为文件名
$target_file = md5( uniqid() . $uploaded_name ) . '.' . $uploaded_ext;
// 检测文件的后缀名,文件大小,getimagesize()检测
if( ( strtolower( $uploaded_ext ) == 'jpg' || strtolower( $uploaded_ext ) == 'jpeg' || strtolower( $uploaded_ext ) == 'png' ) && ( $uploaded_size < 100000 ) &&
( $uploaded_type == 'image/jpeg' || $uploaded_type == 'image/png' ) &&
getimagesize( $uploaded_tmp ) ) {
// 删除源数据,重新生成图片
if( $uploaded_type == 'image/jpeg' ) {
$img = imagecreatefromjpeg( $uploaded_tmp );
imagejpeg( $img, $temp_file, 100);
}
else {
$img = imagecreatefrompng( $uploaded_tmp );
imagepng( $img, $temp_file, 9);
}
//销毁图像资源
imagedestroy( $img );
// Generate Anti-CSRF token
generateSessionToken();
?>
可以看到,Impossible级别的代码对上传文件进行了重命名(为md5值,导致%00截断无法绕过过滤规则),加入token防护CSRF攻击,同时对文件的内容作了严格的检查,过滤了图片中的恶意代码,导致攻击者无法上传含有恶意脚本的文件。

























 5853
5853











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?










