其实MSF大部分都用来用ms17_010,其实MSF还有很多功能,比如用他来打打CMS的exp呀,还有对端口的攻击,生成payload,在此,我也记一个笔记,供大家分享。
1.首先基于MSF的资产收集
网络主机收集:
use auxiliary/scanner/discovery/udp_probe
use auxiliary/scanner/discovery/udp_sweep
use auxiliary/scanner/discovery/arp_sweep
use auxiliary/scanner/dns/dns_amp 基于DNS找存活主机,端口为53
use auxiliary/scanner/netbios/nbname 基于nbname找存活主机,端口为137
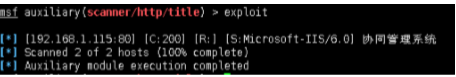
use auxiliary/scanner/http/title 端口为80
use auxiliary/scanner/portscan/ack
use auxiliary/scanner/portscan/tcp 指定网段探寻端口
use auxiliary/scanner/portscan/syn
use auxiliary/scanner/portscan/ftpbounce
use auxiliary/scanner/portscan/xmas
内网服务收集:
搜寻http服务:use auxiliary/scanner/http/http_version 端口80
搜寻smb服务:use auxiliary/scanner/smb/smb_version 端口445
搜寻ftp服务: use auxiliary/scanner/ftp/ftp_version 端口21
搜寻ssh服务: use auxiliary/scanner/ssh/ssh_version 端口22
搜寻talnet服务: use auxiliary/scanner/telnet/telnet_version 端口23
搜寻mysql服务: use auxiliary/scanner/mysql/mysql_version 端口3306
搜寻db2服务: use auxiliary/scanner/db2/db2_version 端口50000
搜寻rdp服务:use auxiliary/scanner/rdp/rdp_scanner 端口3389
搜寻smtp服务:use auxiliary/scanner/smtp/smtp_version 端口25
2.关于MSF攻击的命令
1.首先关于msf常用的payload
windows:
windows/meterpreter/reverse_tcp
windows/meterpreter/bind_tcp
windows/meterpreter/reverse_hop_http
windows/meterpreter/reverse_http
windows/meterpreter/reverse_http_proxy_pstore
windows/meterpreter/reverse_https
windows/meterpreter/reverse_https_proxy
windows/shell_reverse_tcp
windows/shell_bind_tcp
windows/x64/meterpreter/reverse_tcp
windows/x64/meterpreter/bind_tcp
windows/x64/shell_reverse_tcp
windows/x64/shell_








 最低0.47元/天 解锁文章
最低0.47元/天 解锁文章















 1132
1132











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








