一.用gpg生成秘钥对和导出公钥过程
生成秘钥对
执行命令:gpg --gen-key
Please select what kind of key you want:
(1) RSA and RSA (default)
(2) DSA and Elgamal
(3) DSA (sign only)
(4) RSA (sign only)
Your selection? 4
RSA keys may be between 1024 and 4096 bits long.
What keysize do you want? (2048) 4096
Requested keysize is 4096 bits
Please specify how long the key should be valid.
0 = key does not expire
<n> = key expires in n days
<n>w = key expires in n weeks
<n>m = key expires in n months
<n>y = key expires in n years
Key is valid for? (0) 0
Key does not expire at all
Is this correct? (y/N) y
GnuPG needs to construct a user ID to identify your key.
Real name: test
Name must be at least 5 characters long
Real name: testxsf
Email address: 123@qq.com
Comment:
You selected this USER-ID:
"testxsf <123@qq.com>"
Change (N)ame, (C)omment, (E)mail or (O)kay/(Q)uit? O
输入密码,确认密码(没有截图)
生成用于加密的子项
[root@agent07 new27]# gpg --edit-key testxsf
gpg (GnuPG) 2.0.22; Copyright (C) 2013 Free Software Foundation, Inc.
This is free software: you are free to change and redistribute it.
There is NO WARRANTY, to the extent permitted by law.
Secret key is available.
pub 4096R/38B98186 created: 2021-04-27 expires: never usage: SC
trust: ultimate validity: ultimate
[ultimate] (1). testxsf <123@qq.com>
gpg> addkey
Key is protected.
You need a passphrase to unlock the secret key for
user: "testxsf <123@qq.com>"
4096-bit RSA key, ID 38B98186, created 2021-04-27
Please select what kind of key you want:
(3) DSA (sign only)
(4) RSA (sign only)
(5) Elgamal (encrypt only)
(6) RSA (encrypt only)
Your selection? 6
RSA keys may be between 1024 and 4096 bits long.
What keysize do you want? (2048) 4096
Requested keysize is 4096 bits
Please specify how long the key should be valid.
0 = key does not expire
<n> = key expires in n days
<n>w = key expires in n weeks
<n>m = key expires in n months
<n>y = key expires in n years
Key is valid for? (0) 0
Key does not expire at all
Is this correct? (y/N) y
Really create? (y/N) y
We need to generate a lot of random bytes. It is a good idea to perform
some other action (type on the keyboard, move the mouse, utilize the
disks) during the prime generation; this gives the random number
generator a better chance to gain enough entropy.
pub 4096R/38B98186 created: 2021-04-27 expires: never usage: SC
trust: ultimate validity: ultimate
sub 4096R/3499E23C created: 2021-04-27 expires: never usage: E
[ultimate] (1). testxsf 123@qq.com
中间有输入密码的过程,需要输入步骤1中设置的密码
列出秘钥
gpg -k
导出ASCII形式的公钥
gpg --armor --output xsftest-pub-sub.asc --export testxsf
此步骤会产生:xsftest-pub-sub.asc
导出私钥(保存起来,不发给客户)
gpg --a -o womende-private_0426.asc --export-secret-key womende
查看公钥文件
[root@agent07 new27]# cat xsftest-pub-sub.asc
-----BEGIN PGP PUBLIC KEY BLOCK-----
Version: GnuPG v2.0.22 (GNU/Linux)
mQINBGCHpGsBEACmdxBF89+ua9pTN1Brh5PJfxTGwfCqgrpdvRc6shBWefPR2SAZ
jTYNNMRij215k5FVDSwu8OAAOBiifOF04xjrMP3m9gxbTh44iy2pm3eKRd1IH8rL
zLleMJAkiUCpOeafA0LXoqM7u3aAABh08pbZZm4EutSi79SM/wJpOR/aiRuEkqxl
uw6s9LJGwjSBP//sPSL4u5F4eu5PIIqMB7OymJuuPncOLtFSArGHPImQ8PStPQOH
tJ0X8fa29x5u2YPfAAIPgAKEpkscZ2n1pjN2BUi6tQ2HREGCxHk8PZWMXJHqssUH
Dz5cXgIdcmEyvhqnFuZ5sKfZzu7FAjPzbRVS21sCe8/tO6aWyMv28dwZO38XmvA5
cioVUTavclxNAc3RDamMUXNKInXo/ucgmCOEo/Hj1139hOxMVXqPe8X0j+6tC5ei
WZwFbGFH99W5IHfRIPXMsN4FmdflwxF0d9m+J20BTnStC5FaA78YSLNGhbj1ngtY
vjDjXeY9wxKQwGb9yX2I9bAzDAKypAkQ8GfrGaBMNIlHE4nUkosAtbG4PALcM/EY
JLflwgy7YHhIKSgaXMFujGhBw6DG2nyLH4364jt9vSqXVDQha09QVCZqyvnT/8aw
UZraoITG6KFYm2PwXJ/jgSMVrplWV/YJEnN/njNpJe8aHQCXWd4GPr3BPQARAQAB
tBR0ZXN0eHNmIDwxMjNAcXEuY29tPokCOQQTAQIAIwUCYIekawIbAwcLCQgHAwIB
BhUIAgkKCwQWAgMBAh4BAheAAAoJEENfC584uYGGHnwP/j+xSDPFJCSuFF2BRvYf
37PzE91FH37ba7qCtLAq6fEpvwk7Q6lx/D1pVjvRmeHnDSdVAk+htrCH9oKaxU5i
yJ669MKY8Sb/QX3E5rhpnopYUDPJwNPG3x3rvx0/GOB3Ixo8cFlvI2uUgEcZOApK
uXapAw5sXFQHcmG0vm0N8SXKE+ixpzzO3Yl7tdMKDp54iz3qWQG4sy/wnYNnToRM
npMl6J2tvvrSIMkbnPCmkK/pbzRT2d0V9giXrBoqWC3UwF/9kAYI2qMhAMG76JL/
AhjmesjyVDbN/rHJpu6t2OOkoI/H+QZzruzk2eP3EFpYPk6WHRlMCJIyVPuqEu50
Go7LuKHjMsTIqkuLmVuWUknm7wD0He3jiWGVZIZhMbVkUYXzY87NZc+OZydjno5q
RiU270YirrTW2hST0AW/YGfzwjUAFadsO4XssjZxsVe0HaNxraeS0B1Cfl7AoTDt
QsBXBb+/dPHXls8UczzI42YlROMGDprswM8zZrl2ZzTVU5gYwZdkII+OMwiLG6h8
ynVhdMKr7idugFVeSlsIvApVb088zBUndunPxnQZlCL03GzH5vaNRflJl90/HMmQ
DF+/mkGsAephXmu4Lvnv/aRQ0klQX73C5YAEZbJfwPaO15Rt398wCJUPt4gw9Fjj
moGxHGkx/HbK1/TlmzV8MJWr
=XXsa
-----END PGP PUBLIC KEY BLOCK-----
二.用secp384r1算法生成证书请求文件
1.生成app私钥
openssl ecparam -name secp384r1 -genkey -out womende_20210427_private.pem
2.生成证书请求文件
openssl req -new -key womende_20210427_private.pem -out womende_20210427.csr -subj "/C=CN/ST=DD/L=sh/O=NI/OU=CN/CN=CN"
三. 用1步骤生成的秘钥中的私钥将证书请求文件加签
加签:
gpg -o womende_20210427.csr.sig -s womende_20210427.csr
此步骤会生成: womende_20210427.csr.sig
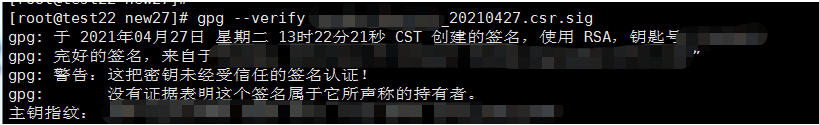
验签(可以将1步骤导出的公钥导入另一台服务器,然后验证是否能验签):
gpg --verify womende_20210427.csr.sig
如下表明验签完整
四. 用对方的公钥将证书请求文件加密
gpg --encrypt --recipient duifangdegongyaowenjian womende_20210427.csr
(“\”是转义用,否则会报错)
此步骤会生成: womende_20210427.csr.gpg
























 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








