Linux修炼之旅第二章!
在这一章的内容里,对Selinux进行了详细的介绍,下面就结合实例来介绍一下Selinux
文章目录
一、Selinux的功能
在第一章的实验中,实验一开始就关闭了Selinux,接下来就针对Selinux进行一个功能上的介绍
对于文件的影响
当selinux开启时,内核会对每个文件及每个开启的程序进行标签加载
标签内记录程序和文件的安全上下文(context)
对于程序功能的影响
当selinux开启会对程序的功能加载开关,并设定此开关的状态为关闭
当需要此功能时需要手动开启功能开关
此开关叫做sebool
二、Selinux的状态及管理
1.selinux的开启
vim /etc/selinux/config
SELINUX=disabled #selinux关闭
SELINUX=enforcing #selinux开机设定为强制状态此状态为selinux开启
SELINUX=permissive #selinux开机设定为警告状态此状态为selinux开启
selinux开启或关闭需要重启系统!!!!
下面通过一个例子说明警告模式与强制模式的区别
可以看到在警告模式下安全上下文有问题的情况下是可以正常显示到test文件的

调整为强制模式以后

就看不到了
selinux日志位置
记录了警告的信息
/var/log/audit/audit.log

二、Selinux的安全上下文
1.查看
ls -Z ##查看文件的安全上下文
ls -Zd ##查看目录的安全上下文
ps axZ ##查看进程的安全上下文
2.修改安全上下文
1.临时修改
此方式更改的安全上下文在selinux重启后会还原
mkdir test #创建测试文件
ls -Zd test/
unconfined_u:object_r:admin_home_t:s0 test/ #若为用户的家目录安全上下文显示admin
chcon -Rt public_content_t test/
ls -Zd test/
unconfined_u:object_r:public_content_t:s0 test/
mkdir /test #在根下创建测试文件
ls -Zd /test
unconfined_u:object_r:default_t:s0 /test #可以看到时default
chcon -Rt public_content_t /test #临时更改安全上下文,重启时无效
ls -Zd /test #可以看到已经更改为public,立即生效
unconfined_u:object_r:public_content_t:s0 /test

重启时会在这里卡一会
在前面暂时修改

2.永久修改安全上下文
[root@westoslinux ~] ls -Zd /test/
unconfined_u:object_r:default_t:s0 /test/
[root@westoslinux ~] semanage fcontext -a -t public_content_t '/test(/.*)?' #管理安全上下文,设置为public,不会立即生效,需要刷新
[root@westoslinux ~] semanage fcontext -l | grep test #查看验证是否更改成功
/\.ismount-test-file regular file system_u:object_r:sosreport_tmp_t:s0
/opt/sartest(/.*)? all files system_u:object_r:sysstat_log_t:s0
/test(/.*)? all files system_u:object_r:public_content_t:s0
/usr/lib/pgsql/test/regress(/.*)? all files system_u:object_r:postgresql_db_t:s0
/usr/lib/pgsql/test/regress/.*\.sh regular file system_u:object_r:bin_t:s0
/usr/lib/pgsql/test/regress/.*\.so.* regular file system_u:object_r:lib_t:s0
/usr/lib/pgsql/test/regress/pg_regress regular file system_u:object_r:postgresql_exec_t:s0
[root@westoslinux ~] ls -Zd /test/
unconfined_u:object_r:default_t:s0 /test/
[root@westoslinux ~] restorecon -RvvF /test/ #刷新一下就可以看到效果,degault变成public
Relabeled /test from unconfined_u:object_r:default_t:s0 to system_u:object_r:public_content_t:s0
[root@westoslinux ~] ls -Zd /test/
system_u:object_r:public_content_t:s0 /test/

三、SEBOOL
bool值的控制:内核enforcing下调整完vsftpd.conf文件后,匿名用户上传文件仍然报错问题
[root@westoslinux ~] vim /etc/vsftpd/vsftpd.conf #开启匿名用户上传
anon_upload_enable=YES
[root@westoslinux ~] systemctl restart vsftpd
[root@westoslinux ~] ls -Zd /var/ftp/pub/ -l
drwxrwxr-x. 3 root ftp system_u:object_r:public_content_t:s0 94 11月 13 11:53 /var/ftp/pub/ 没有读写权限
[root@westoslinux ~] chcon -t public_content_rw_t /var/ftp/pub/ #给rw权限
[root@westoslinux ~] ls -Zd /var/ftp/pub/ -l
drwxrwxr-x. 3 root ftp system_u:object_r:public_content_rw_t:s0 94 11月 13 11:53 /var/ftp/pub/
[root@westoslinux ~] lftp 172.25.254.126
lftp 172.25.254.126:~> ls
drwxrwxr-x 3 0 50 94 Nov 13 03:53 pub
-rw-r--r-- 1 0 0 0 Nov 13 09:15 testfile
lftp 172.25.254.126:/> cd pub/
lftp 172.25.254.126:/pub> ls
-rw-r--r-- 1 1000 50 988 Nov 13 03:38 group
-rw-r--r-- 1 14 50 490 Nov 13 03:31 inittab
-rw-r--r-- 1 1000 50 54809483 Nov 13 04:02 install.img
-rw------- 1 14 50 2664 Nov 13 03:02 passwd
-rw------- 1 1000 50 2123 Nov 13 03:35 profile
drwx------ 2 14 50 6 Nov 13 03:00 test
lftp 172.25.254.126:/pub> put /etc/shadow
put: /etc/shadow: 访问失败: 553 Could not create file. (shadow)
lftp 172.25.254.126:/pub> exit
[root@westoslinux ~] getsebool -a | grep ftp #查ftp的bool
ftpd_anon_write --> off
ftpd_connect_all_unreserved --> off
ftpd_connect_db --> off
ftpd_full_access --> off
ftpd_use_cifs --> off
ftpd_use_fusefs --> off
ftpd_use_nfs --> off
ftpd_use_passive_mode --> off
httpd_can_connect_ftp --> off
httpd_enable_ftp_server --> off
tftp_anon_write --> off
tftp_home_dir --> off
[root@westoslinux ~] setsebool -P ftpd_anon_write on #打开ftpd_anon_write
[root@westoslinux ~] getsebool -a | grep ftp
ftpd_anon_write --> on
ftpd_connect_all_unreserved --> off
ftpd_connect_db --> off
ftpd_full_access --> off
ftpd_use_cifs --> off
ftpd_use_fusefs --> off
ftpd_use_nfs --> off
ftpd_use_passive_mode --> off
httpd_can_connect_ftp --> off
httpd_enable_ftp_server --> off
tftp_anon_write --> off
tftp_home_dir --> off
[root@westoslinux ~] lftp 172.25.254.126
lftp 172.25.254.126:~> ls
drwxrwxr-x 3 0 50 94 Nov 13 03:53 pub
-rw-r--r-- 1 0 0 0 Nov 13 09:15 testfile
lftp 172.25.254.126:/> cd /pub/
lftp 172.25.254.126:/pub> put /etc/shadow
1491 bytes transferred
lftp 172.25.254.126:/pub> ls
-rw-r--r-- 1 1000 50 988 Nov 13 03:38 group
-rw-r--r-- 1 14 50 490 Nov 13 03:31 inittab
-rw-r--r-- 1 1000 50 54809483 Nov 13 04:02 install.img
-rw------- 1 14 50 2664 Nov 13 03:02 passwd
-rw------- 1 1000 50 2123 Nov 13 03:35 profile
-rw-r--r-- 1 1000 50 1491 Nov 14 02:06 shadow
drwx------ 2 14 50 6 Nov 13 03:00 test
lftp 172.25.254.126:/pub> exit
下面来图解上面的代码步骤
首先去打开匿名用户的上传权限

匿名用户仍然上传失败

此时需要我们查看修改bool值


可以上传了

四、SEPORT
端口值的控制:在/etc/ssh/sshd_config中开启新端口号但是restart报错怎么办?
[root@westoslinux ~] vim /etc/ssh/sshd_config
PORT 2222
[root@westoslinux ~] systemctl restart sshd #在文件中改端口号为2222重启sshd服务会报错
Job for sshd.service failed because the control process exited with error code.
See "systemctl status sshd.service" and "journalctl -xe" for details.
[root@westoslinux ~] semanage port -l | grep ssh
ssh_port_t tcp 22
[root@westoslinux ~] semanage port -a -t ssh_port_t -p tcp 2222 #把端口值2222加上
[root@westoslinux ~] semanage port -l | grep ssh
ssh_port_t tcp 2222, 22
[root@westoslinux ~] systemctl restart sshd #不会报错
[root@westoslinux ~] semanage port -d -t ssh_port_t -p tcp 2222 #删除2222端口
[root@westoslinux ~] netstat -antlupe | grep sshd
tcp 0 0 0.0.0.0:22 0.0.0.0:* LISTEN 0 42731 2289/sshd
tcp 0 0 172.25.254.126:22 172.25.254.26:46668 ESTABLISHED 0 31943 1586/sshd: root [pr
tcp6 0 0 :::22 :::* LISTEN 0 42733 2289/sshd
[root@westoslinux ~] semanage port -l | grep ssh
ssh_port_t tcp 22
[root@westoslinux ~] systemctl restart sshd #就会报错
Job for sshd.service failed because the control process exited with error code.
See "systemctl status sshd.service" and "journalctl -xe" for details.
免掉查询步骤的精简版实验步骤,结果更直观
[root@westoslinux ~] vim /etc/ssh/sshd_config
PORT 2222
[root@westoslinux ~] semanage port -a -t ssh_port_t -p tcp 2222
[root@westoslinux ~] systemctl restart sshd
[root@westoslinux ~] semanage port -d -t ssh_port_t -p tcp 2222
[root@westoslinux ~] systemctl restart sshd
Job for sshd.service failed because the control process exited with error code.
See "systemctl status sshd.service" and "journalctl -xe" for details.
端口修改为2222

会出现报错
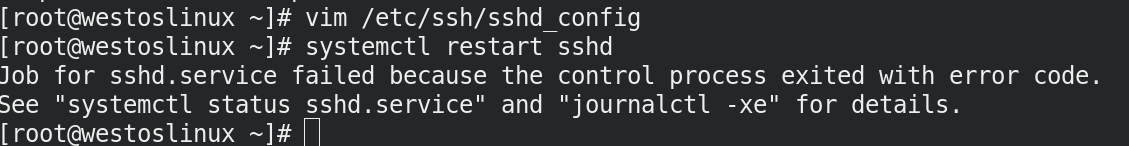
但是还想加端口值怎么解决?
用semanage来加

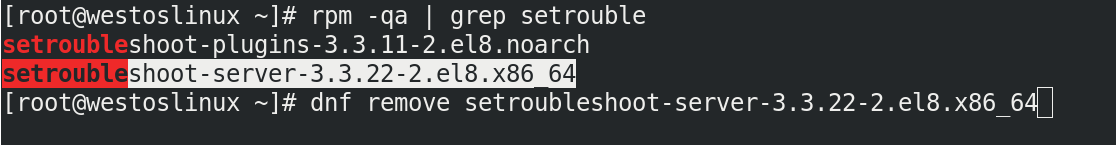
五、setrouble
实验时先删除这个软件
[root@westoslinux ~] > /var/log/messages
[root@westoslinux ~] > /var/log/audit/audit.log
[root@westoslinux ~] touch /mnt/testfile1
[root@westoslinux ~] mv /mnt/testfile1 /var/ftp/
[root@westoslinux ~] ls /var/ftp/
pub testfile testfile1
[root@westoslinux ~] lftp 172.25.254.126
lftp 172.25.254.126:~> ls
drwxrwxr-x 3 0 50 108 Nov 14 02:06 pub
-rw-r--r-- 1 0 0 0 Nov 13 09:15 testfile
lftp 172.25.254.126:/> quit
[root@westoslinux ~] cat /var/log/messages
Nov 14 10:40:36 westoslinux systemd[1]: sshd.service: Service RestartSec=42s expired, scheduling restart.
Nov 14 10:40:36 westoslinux systemd[1]: sshd.service: Scheduled restart job, restart counter is at 37.
Nov 14 10:40:36 westoslinux systemd[1]: Stopped OpenSSH server daemon.
Nov 14 10:40:36 westoslinux systemd[1]: Stopped target sshd-keygen.target.
Nov 14 10:40:36 westoslinux systemd[1]: Stopping sshd-keygen.target.
Nov 14 10:40:36 westoslinux systemd[1]: Reached target sshd-keygen.target.
Nov 14 10:40:36 westoslinux systemd[1]: Starting OpenSSH server daemon...
Nov 14 10:40:36 westoslinux systemd[1]: sshd.service: Main process exited, code=exited, status=255/n/a
Nov 14 10:40:36 westoslinux systemd[1]: sshd.service: Failed with result 'exit-code'.
Nov 14 10:40:36 westoslinux systemd[1]: Failed to start OpenSSH server daemon.
Nov 14 10:41:19 westoslinux systemd[1]: sshd.service: Service RestartSec=42s expired, scheduling restart.
Nov 14 10:41:19 westoslinux systemd[1]: sshd.service: Scheduled restart job, restart counter is at 38.
Nov 14 10:41:19 westoslinux systemd[1]: Stopped OpenSSH server daemon.
Nov 14 10:41:19 westoslinux systemd[1]: Stopped target sshd-keygen.target.
Nov 14 10:41:19 westoslinux systemd[1]: Stopping sshd-keygen.target.
Nov 14 10:41:19 westoslinux systemd[1]: Reached target sshd-keygen.target.
Nov 14 10:41:19 westoslinux systemd[1]: Starting OpenSSH server daemon...
Nov 14 10:41:19 westoslinux systemd[1]: sshd.service: Main process exited, code=exited, status=255/n/a
Nov 14 10:41:19 westoslinux systemd[1]: sshd.service: Failed with result 'exit-code'.
Nov 14 10:41:19 westoslinux systemd[1]: Failed to start OpenSSH server daemon.
[root@westoslinux ~]# cat /var/log/audit/audit.log
type=SERVICE_START msg=audit(1636857679.043:380): pid=1 uid=0 auid=4294967295 ses=4294967295 subj=system_u:system_r:init_t:s0 msg='unit=sshd comm="systemd" exe="/usr/lib/systemd/systemd" hostname=? addr=? terminal=? res=success'UID="root" AUID="unset"
type=SERVICE_STOP msg=audit(1636857679.043:381): pid=1 uid=0 auid=4294967295 ses=4294967295 subj=system_u:system_r:init_t:s0 msg='unit=sshd comm="systemd" exe="/usr/lib/systemd/systemd" hostname=? addr=? terminal=? res=success'UID="root" AUID="unset"
type=AVC msg=audit(1636857679.057:382): avc: denied { name_bind } for pid=3620 comm="sshd" src=2222 scontext=system_u:system_r:sshd_t:s0-s0:c0.c1023 tcontext=system_u:object_r:unreserved_port_t:s0 tclass=tcp_socket permissive=0
type=AVC msg=audit(1636857679.058:383): avc: denied { name_bind } for pid=3620 comm="sshd" src=2222 scontext=system_u:system_r:sshd_t:s0-s0:c0.c1023 tcontext=system_u:object_r:unreserved_port_t:s0 tclass=tcp_socket permissive=0
type=SERVICE_START msg=audit(1636857679.060:384): pid=1 uid=0 auid=4294967295 ses=4294967295 subj=system_u:system_r:init_t:s0 msg='unit=sshd comm="systemd" exe="/usr/lib/systemd/systemd" hostname=? addr=? terminal=? res=failed'UID="root" AUID="unset"
type=AVC msg=audit(1636857692.933:385): avc: denied { getattr } for pid=3634 comm="vsftpd" path="/testfile1" dev="vda3" ino=17578462 scontext=system_u:system_r:ftpd_t:s0-s0:c0.c1023 tcontext=unconfined_u:object_r:mnt_t:s0 tclass=file permissive=0
type=SERVICE_START msg=audit(1636857721.294:386): pid=1 uid=0 auid=4294967295 ses=4294967295 subj=system_u:system_r:init_t:s0 msg='unit=sshd comm="systemd" exe="/usr/lib/systemd/systemd" hostname=? addr=? terminal=? res=success'UID="root" AUID="unset"
type=SERVICE_STOP msg=audit(1636857721.294:387): pid=1 uid=0 auid=4294967295 ses=4294967295 subj=system_u:system_r:init_t:s0 msg='unit=sshd comm="systemd" exe="/usr/lib/systemd/systemd" hostname=? addr=? terminal=? res=success'UID="root" AUID="unset"
type=AVC msg=audit(1636857721.309:388): avc: denied { name_bind } for pid=3644 comm="sshd" src=2222 scontext=system_u:system_r:sshd_t:s0-s0:c0.c1023 tcontext=system_u:object_r:unreserved_port_t:s0 tclass=tcp_socket permissive=0
type=AVC msg=audit(1636857721.309:389): avc: denied { name_bind } for pid=3644 comm="sshd" src=2222 scontext=system_u:system_r:sshd_t:s0-s0:c0.c1023 tcontext=system_u:object_r:unreserved_port_t:s0 tclass=tcp_socket permissive=0
type=SERVICE_START msg=audit(1636857721.311:390): pid=1 uid=0 auid=4294967295 ses=4294967295 subj=system_u:system_r:init_t:s0 msg='unit=sshd comm="systemd" exe="/usr/lib/systemd/systemd" hostname=? addr=? terminal=? res=failed'UID="root" AUID="unset"
type=AVC msg=audit(1636857754.084:391): avc: denied { getattr } for pid=3669 comm="vsftpd" path="/testfile1" dev="vda3" ino=17578462 scontext=system_u:system_r:ftpd_t:s0-s0:c0.c1023 tcontext=unconfined_u:object_r:mnt_t:s0 tclass=file permissive=0
type=SERVICE_START msg=audit(1636857763.543:392): pid=1 uid=0 auid=4294967295 ses=4294967295 subj=system_u:system_r:init_t:s0 msg='unit=sshd comm="systemd" exe="/usr/lib/systemd/systemd" hostname=? addr=? terminal=? res=success'UID="root" AUID="unset"
type=SERVICE_STOP msg=audit(1636857763.543:393): pid=1 uid=0 auid=4294967295 ses=4294967295 subj=system_u:system_r:init_t:s0 msg='unit=sshd comm="systemd" exe="/usr/lib/systemd/systemd" hostname=? addr=? terminal=? res=success'UID="root" AUID="unset"
type=AVC msg=audit(1636857763.557:394): avc: denied { name_bind } for pid=3670 comm="sshd" src=2222 scontext=system_u:system_r:sshd_t:s0-s0:c0.c1023 tcontext=system_u:object_r:unreserved_port_t:s0 tclass=tcp_socket permissive=0
type=AVC msg=audit(1636857763.557:395): avc: denied { name_bind } for pid=3670 comm="sshd" src=2222 scontext=system_u:system_r:sshd_t:s0-s0:c0.c1023 tcontext=system_u:object_r:unreserved_port_t:s0 tclass=tcp_socket permissive=0
type=SERVICE_START msg=audit(1636857763.560:396): pid=1 uid=0 auid=4294967295 ses=4294967295 subj=system_u:system_r:init_t:s0 msg='unit=sshd comm="systemd" exe="/usr/lib/systemd/systemd" hostname=? addr=? terminal=? res=failed'UID="root" AUID="unset"
没有解决方案所以安装软件来提供纠错服务
[root@westoslinux ~] dnf search setrouble
Updating Subscription Management repositories.
Unable to read consumer identity
This system is not registered to Red Hat Subscription Management. You can use subscription-manager to register.
上次元数据过期检查:1:46:58 前,执行于 2021年11月14日 星期日 08时56分50秒。
================================= 名称 和 概况 匹配:setrouble =================================
setroubleshoot-plugins.noarch : Analysis plugins for use with setroubleshoot
===================================== 名称 匹配:setrouble =====================================
setroubleshoot.x86_64 : Helps troubleshoot SELinux problems
setroubleshoot-server.x86_64 : SELinux troubleshoot server
[root@westoslinux ~] dnf install setroubleshoot.x86_64
=================================================================================
再次清空测试
[root@westoslinux ~] > /var/log/messages
[root@westoslinux ~] > /var/log/audit/audit.log
[root@westoslinux ~] lftp 172.25.254.126
lftp 172.25.254.126:~> ls
drwxrwxr-x 3 0 50 108 Nov 14 02:06 pub
-rw-r--r-- 1 0 0 0 Nov 13 09:15 testfile
lftp 172.25.254.126:/> quit
这时候就会出现一串代码,复制后直接执行
此时就可以弹出解决方案
***** 插件 restorecon (88.2 置信度) 建议 ******************************************
如果要修复标签。/testfile1默认标签应该是 etc_runtime_t。
Then 你可以运行restorecon。由于访问父目录的权限不足,可能已停止访问尝试,在这种情况下尝试相应地更改以下命令。
Do
# /sbin/restorecon -v /testfile1
...
...
然后执行:
restorecon -v '/testfile1'
将这个指令的路径补齐输入就可以解决问题
[root@westoslinux ~] restorecon -v '/var/ftp/testfile1'
Relabeled /var/ftp/testfile1 from unconfined_u:object_r:mnt_t:s0 to unconfined_u:object_r:public_content_t:s0
[root@westoslinux ~] lftp 172.25.254.126
lftp 172.25.254.126:~> ls
drwxrwxr-x 3 0 50 108 Nov 14 02:06 pub
-rw-r--r-- 1 0 0 0 Nov 13 09:15 testfile
-rw-r--r-- 1 0 0 0 Nov 14 02:40 testfile1
lftp 172.25.254.126:/> quit
具体的步骤是什么意思,以及效果看图解
先清空警告日志和建议日志
然后在ftp文件夹中创建文件
由于Selinux的存在
没有完整安全上下文的文件会不予显示
警告模式下值警告不阻拦
但是强制模式不显示
但是会生成警告日志
但是不会生成解决方案
具体的效果看截图


没有解决方案
所以现在把setrouble下回来




问题得到了解决























 461
461











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








