基于官方指导教程。ubuntu18.04,已安装vpp并测试,已有startup1.conf、startup2.conf(可以放在/etc/vpp路径下)。root权限操作。
一 运行VPP
- 启动
/usr/bin/vpp -c startup1.conf
- 运行VPP shell,进入
vpp#
vppctl -s /run/vpp/cli-vpp1.sock
二 创建Interface
(vpp1,连接linux系统的veth interface通过AF_PACKET)
- 在 Linux 中,有一种接口调用“veth”。将“veth”接口视为具有两端(而不是一个)的接口。创建一个 veth 接口,一端名为vpp1out,另一端名为vpp1host
$ ip link add name vpp1out type veth peer name vpp1host
- 启动interface
$ ip link set dev vpp1out up
$ ip link set dev vpp1host up
- 配置ip地址
$ ip addr add 10.10.1.1/24 dev vpp1host
$ ip addr show vpp1host
# 删除接口ipv4地址
vpp# set interface ip address del eth0 172.16.2.12/24
# 删除接口ipv4 and ipv6
vpp# set interface ip address del eth0 all
- VPP创建interface(类型:host-interface,连接到vpp1out上),查看Interface已创建
vpp# create host-interface name vpp1out
vpp# show hardware
- VPP启动interface,查看interface状态(比
show hardware多看到MTU)
vpp# set int state host-vpp1out up
vpp# show int
- VPP配置interface IP地址,查看interface的IP地址
vpp# set int ip address host-vpp1out 10.10.1.2/24
vpp# show int addr
三 trace追踪包
- VPP先查看记录,清除之前的记录
vpp# show trace
vpp# clear trace
- VPP设置trace过滤器(没用到)
vpp# trace filter <include NODE COUNT | exclude NODE COUNT | none>
Q:trace filter none可以,其他的好像不行?是过滤节点数量吗?参考trace filter
- VPP建立trace(指定追踪节点,追踪包数量)
vpp# trace add af-packet-input 10
支持trace的节点
af-packet-inputavf-input
bond-process
dpdk-crypto-input
dpdk-input
handoff-trace
ixge-input
memif-input
mrvl-pp2-input
netmap-input
p2p-ethernet-input
pg-input
punt-socket-rx
rdma-input
session-queue
tuntap-rx
vhost-user-input
virtio-input
vmxnet3-input
- linux ping或者vpp ping,查看trace
vpp 中的ping不可以用-c指定数量
$ ping -c 1 10.10.1.2
vpp# ping 10.10.1.1
vpp# show trace
trace内容解释(待补充)
时间、节点、包格式……(主要看下节点ip4-lookup、ip4-rewrite)
Packet 1
05:05:52:711808: af-packet-input
af_packet: hw_if_index 1 next-index 4
tpacket2_hdr:
status 0x20000001 len 98 snaplen 98 mac 66 net 80
sec 0x6205d002 nsec 0x5f8011d vlan 0 vlan_tpid 0
05:05:52:711853: ethernet-input
IP4: f6:e3:e8:ef:9a:8d -> 02:fe:1b:ef:0a:d4
05:05:52:711863: ip4-input
ICMP: 10.10.1.1 -> 10.10.2.2
tos 0x00, ttl 64, length 84, checksum 0x7d7f dscp CS0 ecn NON_ECN
fragment id 0xa613, flags DONT_FRAGMENT
ICMP echo_request checksum 0xfaed id 21893
05:05:52:711873: ip4-lookup
fib 0 dpo-idx 5 flow hash: 0x00000000
ICMP: 10.10.1.1 -> 10.10.2.2
tos 0x00, ttl 64, length 84, checksum 0x7d7f dscp CS0 ecn NON_ECN
fragment id 0xa613, flags DONT_FRAGMENT
ICMP echo_request checksum 0xfaed id 21893
05:05:52:711883: ip4-rewrite
tx_sw_if_index 2 dpo-idx 5 : ipv4 via 10.10.2.2 memif0/0: mtu:9000 next:4 02fe5f8a02f702fe42b3b6930800 flow hash: 0x00000000
00000000: 02fe5f8a02f702fe42b3b693080045000054a61340003f017e7f0a0a01010a0a
00000020: 02020800faed5585000102d0056200000000df860100000000001011
05:05:52:711887: memif0/0-output
memif0/0
IP4: 02:fe:42:b3:b6:93 -> 02:fe:5f:8a:02:f7
ICMP: 10.10.1.1 -> 10.10.2.2
tos 0x00, ttl 63, length 84, checksum 0x7e7f dscp CS0 ecn NON_ECN
fragment id 0xa613, flags DONT_FRAGMENT
ICMP echo_request checksum 0xfaed id 21893
在vpp里可以抓包,文件在/tmp路径
# 抓1000个包,写入文件vppcapture
pcap dispatch trace on max 1000 file vppcapture buffer-trace dpdk-input 1000
pcap dispatch trace off
- VPP查看ARP表(邻接表)
vpp# show ip neighbors
Time IP4 Flags Ethernet Interface
1101.5636 10.10.1.1 D e2:0f:1e:59:ec:f7 host-vpp1out
- VPP查看路由表
(第一行vrf没看懂)
目的网络
单播/多播
Q:dpo-load-balance
dpo-load-balance[协议 序号 Q:buckets 单播反向路由查找 to via ]
Q:动作?dpo-drop / ipv4 via 10.10.1.1 host-vpp1out / ipv4-glean/dpo-receive
vpp# show ip fib
ipv4-VRF:0, fib_index:0, flow hash:[src dst sport dport proto ] locks:[src:plugin-hi:2, src:adjacency:1, src:default-route:1, ]
0.0.0.0/0
unicast-ip4-chain
[@0]: dpo-load-balance: [proto:ip4 index:1 buckets:1 uRPF:0 to:[0:0]]
[0] [@0]: dpo-drop ip4
0.0.0.0/32
unicast-ip4-chain
[@0]: dpo-load-balance: [proto:ip4 index:2 buckets:1 uRPF:1 to:[0:0]]
[0] [@0]: dpo-drop ip4
10.10.1.0/32
unicast-ip4-chain
[@0]: dpo-load-balance: [proto:ip4 index:10 buckets:1 uRPF:9 to:[0:0]]
[0] [@0]: dpo-drop ip4
10.10.1.1/32
unicast-ip4-chain
[@0]: dpo-load-balance: [proto:ip4 index:13 buckets:1 uRPF:12 to:[5:420] via:[2:168]]
[0] [@5]: ipv4 via 10.10.1.1 host-vpp1out: mtu:9000 e20f1e59ecf702fed975d5b40800
10.10.1.0/24
unicast-ip4-chain
[@0]: dpo-load-balance: [proto:ip4 index:9 buckets:1 uRPF:8 to:[0:0]]
[0] [@4]: ipv4-glean: host-vpp1out: mtu:9000 ffffffffffff02fed975d5b40806
10.10.1.2/32
unicast-ip4-chain
[@0]: dpo-load-balance: [proto:ip4 index:12 buckets:1 uRPF:13 to:[7:588]]
[0] [@2]: dpo-receive: 10.10.1.2 on host-vpp1out
10.10.1.255/32
unicast-ip4-chain
[@0]: dpo-load-balance: [proto:ip4 index:11 buckets:1 uRPF:11 to:[0:0]]
[0] [@0]: dpo-drop ip4
224.0.0.0/4
unicast-ip4-chain
[@0]: dpo-load-balance: [proto:ip4 index:4 buckets:1 uRPF:3 to:[0:0]]
[0] [@0]: dpo-drop ip4
240.0.0.0/4
unicast-ip4-chain
[@0]: dpo-load-balance: [proto:ip4 index:3 buckets:1 uRPF:2 to:[0:0]]
[0] [@0]: dpo-drop ip4
255.255.255.255/32
unicast-ip4-chain
[@0]: dpo-load-balance: [proto:ip4 index:5 buckets:1 uRPF:4 to:[0:0]]
[0] [@0]: dpo-drop ip4
四 连接两个VPP
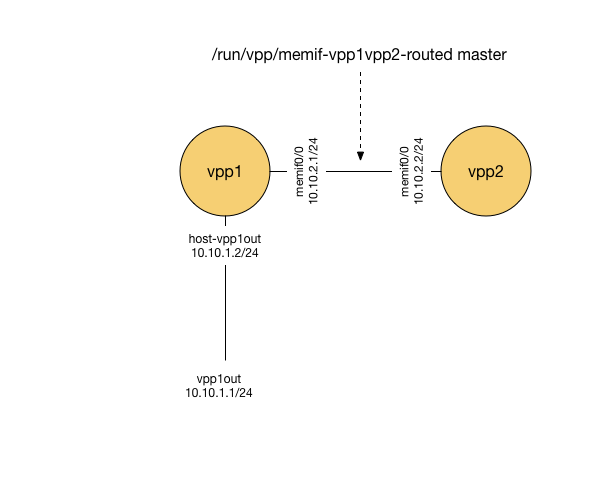
vpp1和vpp2都已运行
- VPP1创建interface(类型:memif ;id ;角色:master)
这个interface name是memif0/0,master是vpp1在memif0/0中的角色
vpp# create interface memif id 0 master
- VPP1启动memif0/0,添加IP,查看interface
vpp# set int state memif0/0 up
vpp# set int ip address memif0/0 10.10.2.1/24
vpp# show int
vpp# show int addr
- VPP2创建interface(类型:memif ;id ;角色:slave)
vpp# create interface memif id 0 slave
- VPP2启动memif0/0,添加IP,查看interface(除了IP,其他和VPP1一样)
vpp# set int ip address memif0/0 10.10.2.2/24
- VPP1与2互相ping
vpp# ping 10.10.2.2
vpp# ping 10.10.2.1
五 添加路由,拉通linux到VPP2(通过VPP1)
- linux添加路由,目的地址是10.10.2.0/24,下一跳是10.10.1.2(vpp1)
$ ip route add 10.10.2.0/24 via 10.10.1.2
$ ip route
- VPP2设置返回路由,目的地址是10.10.1.0/24,下一跳是10.10.2.1(vpp1)
vpp# ip route add 10.10.1.0/24 via 10.10.2.1
- 主机pingVPP2,trace追踪包
VPP1与VPP2之间用 memif driver,主机和VPP1之间用af-packet driver(Q:这两个是啥?)
要跟踪来自主机的数据包,使用af-packet-input;从vpp1到vpp2,使用memif-input。
# VPP1
vpp# trace add af-packet-input 10
# VPP2
vpp# trace add memif-input 10
# host ping vpp2
$ ping 10.10.2.2
# show trace
vpp# show trace
vpp# clear trace
六 switch
- 清除之前的配置
$ ps -ef | grep vpp | awk '{print $2}'| xargs sudo kill
$ sudo ip link del dev vpp1host
$ # do the next command if you are cleaning up from this example
$ sudo ip link del dev vpp1vpp2
- 运行 FD.io VPP 实例
运行一个名为vpp1的 vpp 实例
$ /usr/bin/vpp -c startup1.conf
$ vppctl -s /run/vpp/cli-vpp1.sock
运行一个名为vpp2的 vpp 实例
$ /usr/bin/vpp -c startup2.conf
$ vppctl -s /run/vpp/cli-vpp2.sock
- 将 vpp1 连接到主机
创建一个 veth,一端命名为 vpp1host,另一端命名为 vpp1out。
将 vpp1out 连接到 vpp1
在vpp1host上添加ip地址10.10.1.1/24
$ ip link add name vpp1out type veth peer name vpp1host
$ ip link set dev vpp1out up
$ ip link set dev vpp1host up
$ ip addr add 10.10.1.1/24 dev vpp1host
vpp# create host-interface name vpp1out
host-vpp1out
vpp# set int state host-vpp1out up
- 将 vpp1 连接到 vpp2
创建一个 veth,一端命名为 vpp1vpp2,另一端命名为 vpp2vpp1。
将 vpp1vpp2 连接到 vpp1。
将 vpp2vpp1 连接到 vpp2。
$ ip link add name vpp2vpp1 type veth peer name vpp1vpp2
$ ip link set dev vpp1vpp2 up
$ ip link set dev vpp2vpp1 up
vpp1
vpp# create host-interface name vpp1vpp2
host-vpp1vpp2
vpp# set int state host-vpp1vpp2 up
vpp# show bridge-domin
vpp2
vpp# create host-interface name vpp2vpp1
host-vpp2vpp1
vpp# set int state host-vpp2vpp1 up
- 在 vpp1 上配置网桥域
如果只有默认的0,创建bridge domain 1
vpp# show bridge-domain
vpp# set int l2 bridge host-vpp1out 1
vpp# set int l2 bridge host-vpp1vpp2 1
vpp# show bridge-domain 1 detail
BD-ID Index BSN Age(min) Learning U-Forwrd UU-Flood Flooding ARP-Term arp-ufwd BVI-Intf
1 1 off on on flood on off off N/A
span-l2-input l2-input-classify l2-input-feat-arc l2-policer-classify l2-input-acl vpath-input-l2 l2-ip-qos-record l2-input-vtr l2-gbp-lpm-classify gbp-src-classify gbp-null-classify l2-gbp-lpm-anon-classify gbp-learn-l2 l2-emulation l2-learn l2-rw l2-fwd gbp-fwd l2-flood l2-flood l2-output
Interface If-idx ISN SHG BVI TxFlood VLAN-Tag-Rewrite
host-vpp1out 1 1 0 - * none
host-vpp1vpp2 2 1 0 - * none
- 在 vpp2 上配置环回接口
vpp# create loopback interface
loop0
将ip地址10.10.1.2/24添加到vpp2接口loop0。将 vpp2 上的接口 loop0 的状态设置为“up”
vpp# set int ip address loop0 10.10.1.2/24
vpp# set int state loop0 up
删除用del loopback interface intfc loop0
- 在 vpp2 上配置网桥域
检查以查看第一个可用的网桥域 ID(在这种情况下为 1)将接口 loop0 作为网桥虚拟接口 (bvi) 添加到网桥域 1,将接口 vpp2vpp1 添加到桥接域 1
vpp# set int l2 bridge loop0 1 bvi
vpp# set int l2 bridge host-vpp2vpp1 1
- 从主机 ping 到 vpp 和 vpp 到主机
在 vpp1 和 vpp2 上添加跟踪
从主机 ping 到 10.10.1.2
检查并清除 vpp1 和 vpp2 上的跟踪
vpp1&vpp2
vpp# show trace
------------------- Start of thread 0 vpp_main -------------------
No packets in trace buffer
vpp# clear trace
vpp# trace add af-packet-input 10
vpp1
vpp# show trace
------------------- Start of thread 0 vpp_main -------------------
Packet 1
00:37:05:332912: af-packet-input
af_packet: hw_if_index 1 next-index 4
tpacket2_hdr:
status 0x20000001 len 98 snaplen 98 mac 66 net 80
sec 0x6209b8f7 nsec 0x2c877061 vlan 0 vlan_tpid 0
00:37:05:332955: ethernet-input
IP4: 12:9c:88:4f:ee:2d -> de:ad:00:00:00:00
00:37:05:332963: l2-input
l2-input: sw_if_index 1 dst de:ad:00:00:00:00 src 12:9c:88:4f:ee:2d [l2-learn l2-fwd l2-flood l2-flood ]
00:37:05:332969: l2-learn
l2-learn: sw_if_index 1 dst de:ad:00:00:00:00 src 12:9c:88:4f:ee:2d bd_index 1
00:37:05:332973: l2-fwd
l2-fwd: sw_if_index 1 dst de:ad:00:00:00:00 src 12:9c:88:4f:ee:2d bd_index 1 result [0x1220000000002, 2] none
00:37:05:332978: l2-output
l2-output: sw_if_index 2 dst de:ad:00:00:00:00 src 12:9c:88:4f:ee:2d data 08 00 45 00 00 54 d5 9e 40 00 40 01
00:37:05:332981: host-vpp1vpp2-output
host-vpp1vpp2
IP4: 12:9c:88:4f:ee:2d -> de:ad:00:00:00:00
ICMP: 10.10.1.1 -> 10.10.1.2
tos 0x00, ttl 64, length 84, checksum 0x4ef4 dscp CS0 ecn NON_ECN
fragment id 0xd59e, flags DONT_FRAGMENT
ICMP echo_request checksum 0xbe0d id 23197
Packet 2
00:37:05:333367: af-packet-input
af_packet: hw_if_index 2 next-index 4
tpacket2_hdr:
status 0x20000001 len 98 snaplen 98 mac 66 net 80
sec 0x6209b8f7 nsec 0x2c968233 vlan 0 vlan_tpid 0
00:37:05:333374: ethernet-input
IP4: de:ad:00:00:00:00 -> 12:9c:88:4f:ee:2d
00:37:05:333379: l2-input
l2-input: sw_if_index 2 dst 12:9c:88:4f:ee:2d src de:ad:00:00:00:00 [l2-learn l2-fwd l2-flood l2-flood ]
00:37:05:333383: l2-learn
l2-learn: sw_if_index 2 dst 12:9c:88:4f:ee:2d src de:ad:00:00:00:00 bd_index 1
00:37:05:333385: l2-fwd
l2-fwd: sw_if_index 2 dst 12:9c:88:4f:ee:2d src de:ad:00:00:00:00 bd_index 1 result [0x1220000000001, 1] none
00:37:05:333387: l2-output
l2-output: sw_if_index 1 dst 12:9c:88:4f:ee:2d src de:ad:00:00:00:00 data 08 00 45 00 00 54 87 9f 40 00 40 01
00:37:05:333389: host-vpp1out-output
host-vpp1out
IP4: de:ad:00:00:00:00 -> 12:9c:88:4f:ee:2d
ICMP: 10.10.1.2 -> 10.10.1.1
tos 0x00, ttl 64, length 84, checksum 0x9cf3 dscp CS0 ecn NON_ECN
fragment id 0x879f, flags DONT_FRAGMENT
ICMP echo_reply checksum 0xc60d id 23197
vpp# show l2fib verbose
Mac-Address BD-Idx If-Idx BSN-ISN Age(min) static filter bvi Interface-Name
56:dd:cb:23:8c:da 1 2 0/1 - - - - host-vpp1vpp2
de:ad:00:00:00:00 1 2 0/1 - - - - host-vpp1vpp2
12:9c:88:4f:ee:2d 1 1 0/1 - - - - host-vpp1out
8a:1f:7d:cb:0e:3f 1 1 0/1 - - - - host-vpp1out
L2FIB total/learned entries: 4/4 Last scan time: 0.0000e0sec Learn limit: 16777216
vpp2
vpp# show trace
------------------- Start of thread 0 vpp_main -------------------
Packet 1
00:36:04:423430: af-packet-input
af_packet: hw_if_index 1 next-index 4
tpacket2_hdr:
status 0x20000001 len 98 snaplen 98 mac 66 net 80
sec 0x6209b8f7 nsec 0x2c922ba5 vlan 0 vlan_tpid 0
00:36:04:423456: ethernet-input
IP4: 12:9c:88:4f:ee:2d -> de:ad:00:00:00:00
00:36:04:423466: l2-input
l2-input: sw_if_index 1 dst de:ad:00:00:00:00 src 12:9c:88:4f:ee:2d [l2-learn l2-fwd l2-flood l2-flood ]
00:36:04:423470: l2-learn
l2-learn: sw_if_index 1 dst de:ad:00:00:00:00 src 12:9c:88:4f:ee:2d bd_index 1
00:36:04:423473: l2-fwd
l2-fwd: sw_if_index 1 dst de:ad:00:00:00:00 src 12:9c:88:4f:ee:2d bd_index 1 result [0x700000002, 2] static age-not bvi
00:36:04:423479: ip4-input
ICMP: 10.10.1.1 -> 10.10.1.2
tos 0x00, ttl 64, length 84, checksum 0x4ef4 dscp CS0 ecn NON_ECN
fragment id 0xd59e, flags DONT_FRAGMENT
ICMP echo_request checksum 0xbe0d id 23197
00:36:04:423489: ip4-lookup
fib 0 dpo-idx 7 flow hash: 0x00000000
ICMP: 10.10.1.1 -> 10.10.1.2
tos 0x00, ttl 64, length 84, checksum 0x4ef4 dscp CS0 ecn NON_ECN
fragment id 0xd59e, flags DONT_FRAGMENT
ICMP echo_request checksum 0xbe0d id 23197
00:36:04:423512: ip4-local
ICMP: 10.10.1.1 -> 10.10.1.2
tos 0x00, ttl 64, length 84, checksum 0x4ef4 dscp CS0 ecn NON_ECN
fragment id 0xd59e, flags DONT_FRAGMENT
ICMP echo_request checksum 0xbe0d id 23197
00:36:04:423518: ip4-icmp-input
ICMP: 10.10.1.1 -> 10.10.1.2
tos 0x00, ttl 64, length 84, checksum 0x4ef4 dscp CS0 ecn NON_ECN
fragment id 0xd59e, flags DONT_FRAGMENT
ICMP echo_request checksum 0xbe0d id 23197
00:36:04:423522: ip4-icmp-echo-request
ICMP: 10.10.1.1 -> 10.10.1.2
tos 0x00, ttl 64, length 84, checksum 0x4ef4 dscp CS0 ecn NON_ECN
fragment id 0xd59e, flags DONT_FRAGMENT
ICMP echo_request checksum 0xbe0d id 23197
00:36:04:423529: ip4-load-balance
fib 0 dpo-idx 2 flow hash: 0x00000000
ICMP: 10.10.1.2 -> 10.10.1.1
tos 0x00, ttl 64, length 84, checksum 0x9cf3 dscp CS0 ecn NON_ECN
fragment id 0x879f, flags DONT_FRAGMENT
ICMP echo_reply checksum 0xc60d id 23197
00:36:04:423532: ip4-rewrite
tx_sw_if_index 2 dpo-idx 2 : ipv4 via 10.10.1.1 loop0: mtu:9000 next:3 129c884fee2ddead000000000800 flow hash: 0x00000000
00000000: 129c884fee2ddead00000000080045000054879f400040019cf30a0a01020a0a
00000020: 01010000c60d5a9d0001f7b809620000000014660b00000000001011
00:36:04:423536: loop0-output
loop0
IP4: de:ad:00:00:00:00 -> 12:9c:88:4f:ee:2d
ICMP: 10.10.1.2 -> 10.10.1.1
tos 0x00, ttl 64, length 84, checksum 0x9cf3 dscp CS0 ecn NON_ECN
00
00000000: 129c884fee2ddead00000000080045000054879f400040019cf30a0a01020a0a
00000020: 01010000c60d5a9d0001f7b809620000000014660b00000000001011
00:36:04:423536: loop0-output
loop0
IP4: de:ad:00:00:00:00 -> 12:9c:88:4f:ee:2d
ICMP: 10.10.1.2 -> 10.10.1.1
tos 0x00, ttl 64, length 84, checksum 0x9cf3 dscp CS0 ecn NON_ECN
fragment id 0x879f, flags DONT_FRAGMENT
ICMP echo_reply checksum 0xc60d id 23197
00:36:04:423544: l2-input
l2-input: sw_if_index 2 dst 12:9c:88:4f:ee:2d src de:ad:00:00:00:00 [l2-fwd l2-flood l2-flood ]
00:36:04:423546: l2-fwd
l2-fwd: sw_if_index 2 dst 12:9c:88:4f:ee:2d src de:ad:00:00:00:00 bd_index 1 result [0x1210000000001, 1] none
00:36:04:423547: l2-output
l2-output: sw_if_index 1 dst 12:9c:88:4f:ee:2d src de:ad:00:00:00:00 data 08 00 45 00 00 54 87 9f 40 00 40 01
00:36:04:423550: host-vpp2vpp1-output
host-vpp2vpp1
IP4: de:ad:00:00:00:00 -> 12:9c:88:4f:ee:2d
ICMP: 10.10.1.2 -> 10.10.1.1
tos 0x00, ttl 64, length 84, checksum 0x9cf3 dscp CS0 ecn NON_ECN
fragment id 0x879f, flags DONT_FRAGMENT
ICMP echo_reply checksum 0xc60d id 23197
Packet 2
00:36:09:639349: af-packet-input
af_packet: hw_if_index 1 next-index 4
tpacket2_hdr:
status 0x20000001 len 42 snaplen 42 mac 66 net 80
sec 0x6209b8fc nsec 0x397195c8 vlan 0 vlan_tpid 0
00:36:09:639370: ethernet-input
ARP: 12:9c:88:4f:ee:2d -> de:ad:00:00:00:00
00:36:09:639381: l2-input
l2-input: sw_if_index 1 dst de:ad:00:00:00:00 src 12:9c:88:4f:ee:2d [l2-learn l2-fwd l2-flood l2-flood ]
00:36:09:639386: l2-learn
l2-learn: sw_if_index 1 dst de:ad:00:00:00:00 src 12:9c:88:4f:ee:2d bd_index 1
00:36:09:639390: l2-fwd
l2-fwd: sw_if_index 1 dst de:ad:00:00:00:00 src 12:9c:88:4f:ee:2d bd_index 1 result [0x700000002, 2] static age-not b
vi
00:36:09:639398: arp-input
request, type ethernet/IP4, address size 6/4
12:9c:88:4f:ee:2d/10.10.1.1 -> 00:00:00:00:00:00/10.10.1.2
00:36:09:639402: arp-reply
request, type ethernet/IP4, address size 6/4
12:9c:88:4f:ee:2d/10.10.1.1 -> 00:00:00:00:00:00/10.10.1.2
00:36:09:639443: loop0-output
loop0
ARP: de:ad:00:00:00:00 -> 12:9c:88:4f:ee:2d
reply, type ethernet/IP4, address size 6/4
de:ad:00:00:00:00/10.10.1.2 -> 12:9c:88:4f:ee:2d/10.10.1.1
00:36:09:639450: l2-input
l2-input: sw_if_index 2 dst 12:9c:88:4f:ee:2d src de:ad:00:00:00:00 [l2-fwd l2-flood l2-flood ]
00:36:09:639453: l2-fwd
l2-fwd: sw_if_index 2 dst 12:9c:88:4f:ee:2d src de:ad:00:00:00:00 bd_index 1 result [0x1210000000001, 1] none
00:36:09:639455: l2-output
l2-output: sw_if_index 1 dst 12:9c:88:4f:ee:2d src de:ad:00:00:00:00 data 08 06 00 01 08 00 06 04 00 02 de ad
00:36:09:639458: host-vpp2vpp1-output
host-vpp2vpp1
ARP: de:ad:00:00:00:00 -> 12:9c:88:4f:ee:2d
reply, type ethernet/IP4, address size 6/4
de:ad:00:00:00:00/10.10.1.2 -> 12:9c:88:4f:ee:2d/10.10.1.1
vpp# show l2fib verbose
Mac-Address BD-Idx If-Idx BSN-ISN Age(min) static filter bvi Interface-Name
de:ad:00:00:00:00 1 2 0/0 no * - * loop0
12:9c:88:4f:ee:2d 1 1 0/1 - - - - host-vpp2vpp1
8a:1f:7d:cb:0e:3f 1 1 0/1 - - - - host-vpp2vpp1
L2FIB total/learned entries: 3/2 Last scan time: 0.0000e0sec Learn limit: 16777216
- 从 vpp2 ping 到 10.10.1.1
检查并清除 vpp1 和 vpp2 上的跟踪
vpp1
vpp# show l2fib verbose
Mac-Address BD-Idx If-Idx BSN-ISN Age(min) static filter bvi Interface-Name
56:dd:cb:23:8c:da 1 2 0/1 - - - - host-vpp1vpp2
4e:db:02:b3:65:58 1 2 0/1 - - - - host-vpp1vpp2
de:ad:00:00:00:00 1 2 0/1 - - - - host-vpp1vpp2
12:9c:88:4f:ee:2d 1 1 0/1 - - - - host-vpp1out
8a:1f:7d:cb:0e:3f 1 1 0/1 - - - - host-vpp1out
L2FIB total/learned entries: 5/5 Last scan time: 0.0000e0sec Learn limit: 16777216
vpp2
vpp# show l2fib verbose
Mac-Address BD-Idx If-Idx BSN-ISN Age(min) static filter bvi Interface-Name
56:dd:cb:23:8c:da 1 1 0/1 - - - - host-vpp2vpp1
4e:db:02:b3:65:58 1 1 0/1 - - - - host-vpp2vpp1
de:ad:00:00:00:00 1 2 0/0 no * - * loop0
12:9c:88:4f:ee:2d 1 1 0/1 - - - - host-vpp2vpp1
8a:1f:7d:cb:0e:3f 1 1 0/1 - - - - host-vpp2vpp1
L2FIB total/learned entries: 5/4 Last scan time: 0.0000e0sec Learn limit: 16777216





















 285
285











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








