背景
案例JXU4RDFEJXU1OEYzJTIwMy4wMC42MA==
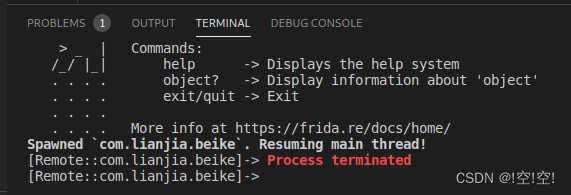
尝试对其frida hook 失败。
定位检测so
function hook_dlopen() {
let is_hook = false;
Interceptor.attach(Module.findExportByName(null, "android_dlopen_ext"),
{
onEnter: function (args) {
var pathptr = args[0];
if (pathptr !== undefined && pathptr != null) {
var path = ptr(pathptr).readCString();
console.log(path)
}
}
}
);
}
setImmediate(hook_dlopen)
frida -H ip:port -f com.lianjia.beike --no-pause -l beike.js
定位到libmsaoaidsec.so
常见解决方法尝试
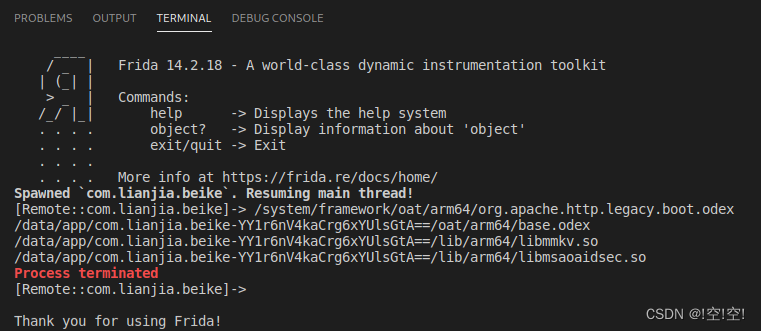
首先对常见检测字段进行hook,发现会打印多次。判断是启动了另外的检测线程。所以尝试去hook创建线程。
寻找检测开启多线程的位置
function hook_pthread(){
var pthread_create_addr = Module.findExportByName(null, 'pthread_create')
var pthread_create = new NativeFunction(pthread_create_addr, "int", ["pointer", "pointer", "pointer", "pointer"]);
Interceptor.replace(pthread_create_addr, new NativeCallback(function (parg0, parg1, parg2, parg3) {
if(Process.findModuleByAddress(parg2)==null){
PC = pthread_create(parg0, parg1, parg2, parg3);
}
var so_name = Process.findModuleByAddress(parg2).name;
var so_path = Process.findModuleByAddress(parg2).path;
var so_base = Module.getBaseAddress(so_name);
var offset = parg2 - so_base;
var PC = 0;
if ((so_name.indexOf("libmsaoaidsec.so") > -1)) {
console.log("find thread func offset", so_name, offset.toString(16));
} else {
PC = pthread_create(parg0, parg1, parg2, parg3);
}
return PC;
}, "int", ["pointer", "pointer", "pointer", "pointer"]))
}
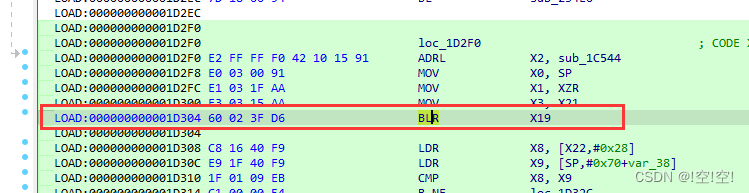
nop掉 创建这个检测线程
多次实验0x1D304这个地方创建检测线程的地方
完整代码
function nop(addr) {
Memory.patchCode(ptr(addr), 8, code => {
const cw = new Arm64Writer(code, { pc: ptr(addr) });
cw.putNop();
cw.putNop();
cw.putNop();
cw.putNop();
cw.flush();
});
}
function bypass(){
let module = Process.findModuleByName("libmsaoaidsec.so")
nop(module.base.add(0x1D304))
}
function hook_dlopen(soName = '') {
Interceptor.attach(Module.findExportByName(null, "android_dlopen_ext"),
{
onEnter: function (args) {
var pathptr = args[0];
if (pathptr !== undefined && pathptr != null) {
var path = ptr(pathptr).readCString();
if (path.indexOf(soName) >= 0) {
// 刚要加载libmsaoaidsec.so
locate_init()
}
}
}
}
);
}
function locate_init() {
let secmodule = null
Interceptor.attach(Module.findExportByName(null, "__system_property_get"),
{
onEnter: function (args) {
var name = args[0];
if (name !== undefined && name != null) {
name = ptr(name).readCString();
if (name.indexOf("ro.build.version.sdk") >= 0) {
// 这是.init_proc刚开始执行的地方,是一个比较早的时机点
bypass()
}
}
}
}
);
}
// 找到检测的so,寻找检测开启多线程的位置,然后nop掉
hook_dlopen("libmsaoaidsec.so")
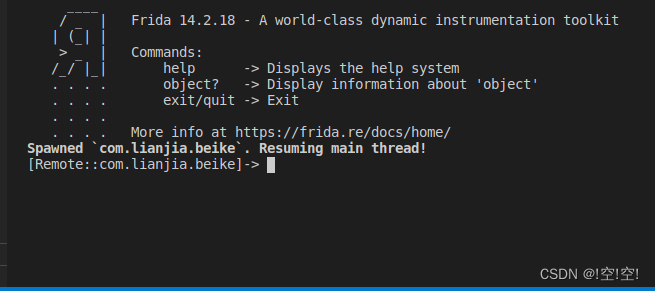
效果展示





















 888
888











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








