BUUCTF [极客大挑战 2019] PHP
启动靶机,打开页面:

提示为备份,尝试使用脚本扫描备份文件:
Python备份文件扫描脚本参考本篇文章
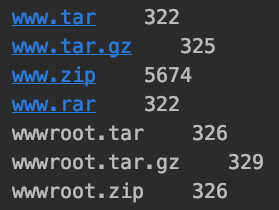
判断应该存在备份文件:www.zip
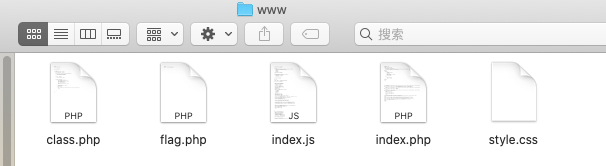
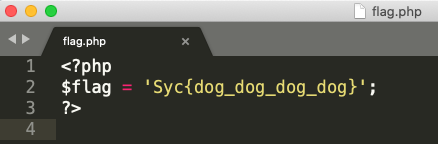
下载得到源码,打开其中的flag.php,得到假flag:
继续查看index.php文件,其中包括源码:
<?php
include 'class.php';
$select = $_GET['select'];
$res=unserialize(@$select);
?>
包含有class.php,并且通过GET方式传入了参数select
查看class.php文件:
<?php
include 'flag.php';
error_reporting(0);
class Name{
private $username = 'nonono';
private $password = 'yesyes';
public function __construct($username,$password){
$this->username = $username;
$this->password = $password;
}
function __wakeup(){
$this->username = 'guest';
}
function __destruct(){
if ($this->password != 100) {
echo "</br>NO!!!hacker!!!</br>";
echo "You name is: ";
echo $this->username;echo "</br>";
echo "You password is: ";
echo $this->password;echo "</br>";
die();
}
if ($this->username === 'admin') {
global $flag;
echo $flag;
}else{
echo "</br>hello my friend~~</br>sorry i can't give you the flag!";
die();
}
}
}
?>
由__destruct()方法可知,需要满足变量password = 100和username = 'admin'






















 3104
3104











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








