前话:ida7.6设置栏内没有general,可以通过ctrl+shift+p打开命令面板,搜索option打开设置选项,于Disassembly设置堆栈显示
正文:

ida打开后发现堆栈不平衡,先把堆栈调平衡

将call函数那行alt+k后改为0
堆栈调平衡后,发现主函数引用了wrong,omg,encrypt,finally四个函数。

奇数位向减,偶数位异或

检验由wrong函数处理后数据是否与unk_4030C0相等。据此可以先推测下Str是什么。
#include<iostream>
#include<cstdio>
using namespace std;
int a1[100] = { 0x66,0x6B,0x63,0x64,0x7F,0x61,0x67,0x64,0x3B,0x56,0x6B,0x61,0x7B,0x26,0x3B,0x50,0x63,0x5F,0x4D,0x5A,0x71,0x0C,0x37,0x66 };
int main()
{
for (int i = 0; i <= 23; ++i)
{
if ((i & 1) != 0)
a1[i] += i;
else
a1[i] ^= i;
cout << char(a1[i]) ;
}
}
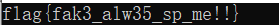
得到了个虚假的flag
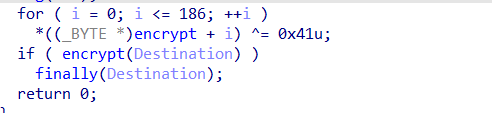
对于encrypt函数,发现被异或操作了,写idc脚本异或回来
#include <idc.idc>
static main()
{
auto addr = 0x00401500;
auto i = 0;
for ( i = 0; i <= 186; ++i )
{
PatchByte(addr+i,Byte(addr+i)^0x41);
}
}
解密后对,数据选中按c后,变成了这样

选中不正常的一段按U转换为未定义,再按c转变为代码即变回正常汇编。
封装为函数后即可反编译

对着写解密脚本:
a = [0x0E,0x0D,0x09,0x06,0x13,0x05,0x58,0x56,0x3E,0x06,0x0C,0x3C,0x1F,0x57,0x14,0x6B,0x57,0x59,0x0D]
b = 'hahahaha_do_you_find_me?'
c = ''
for i in range(len(a)):
c += chr(a[i] ^ ord(b[i]))
print(c)
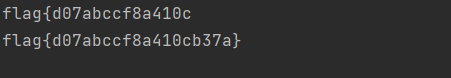
发现少了一段flag。
主函数最后一个函数

此处不是伪加密,大师傅的wp说这里存在异或关系,我实在看不出来。脚本:
a = [0x0E,0x0D,0x09,0x06,0x13,0x05,0x58,0x56,0x3E,0x06,0x0C,0x3C,0x1F,0x57,0x14,0x6B,0x57,0x59,0x0D]
b = 'hahahaha_do_you_find_me?'
c = ''
for i in range(len(a)):
c += chr(a[i] ^ ord(b[i]))
print(c)
p = '%tp&:'
q = ord(p[-1]) ^ ord('}')
for i in range(len(p)):
c+=chr(q^ord(p[i]))
print(c)






















 931
931











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








