版本
app:V12.0.2
so:libjdbitmapkit.so
启动hluda
adb forward tcp:9999 tcp:9999
nohup ./hluda-server-16.0.9-android-arm64 -l 0.0.0.0:9999 &
java层
通过jadx分析得知:
com.jingdong.common.network.JDNetworkDependencyFactory.signature
public String signature(Context context, String str, String str2, String str3, String str4, String str5)
frida hook 入参
// frida -H 127.0.0.1:9999 app -l hook_java_getSignFromJni.js
Java.perform(function () {
let AnonymousClass3 = Java.use("com.jingdong.common.network.JDNetworkDependencyFactory$3");
AnonymousClass3["signature"].implementation = function (context, str, str2, str3, str4, str5) {
console.log(`AnonymousClass3.signature is called: context=${context}, str=${str}, str2=${str2}, str3=${str3}, str4=${str4}, str5=${str5}`);
let result = this["signature"](context, str, str2, str3, str4, str5);
console.log(`AnonymousClass3.signature result=${result}`);
return result;
};
});
分析入参
context=com.jingdong.app.mall.JDApp@8396b65 // app上下文
str=subCartCount // functionId
str2={"cartuuid":"0d07bdf0-6c17-46ed-8f5a-a328ae6be62b","coord_type":"","latitude":"27.708","longitude":"107.073","refer":"1","type":"ecard","userType":"0"} // 未加密body
str3=2467d615834a8deb // 未加密uuid
str4=android // 系统平台
str5=12.0.2 // app版本
result=st=1685465570295&sign=8f56a9aca21628f36f4b552a64cac72a&sv=101
ok frida prc可直接调用
ida分析
静态绑定:
Java_com_jingdong_common_utils_BitmapkitUtils_getSignFromJni 00002EA8
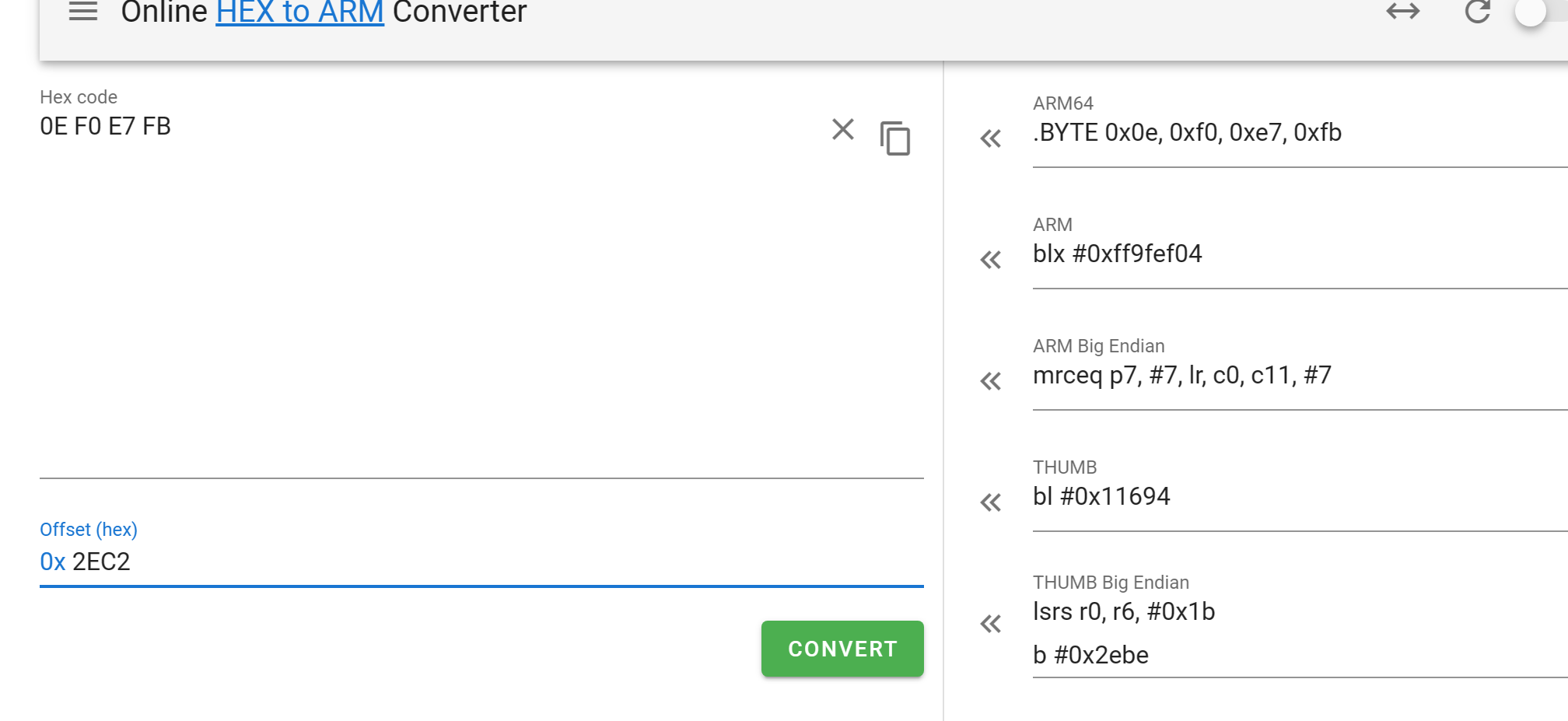
跳转:
.text:00002EC2 BL sub_11694
frida hook Java_com_jingdong_common_utils_BitmapkitUtils_getSignFromJni
// frida -H 127.0.0.1:9999 app -l hook_so_Java_com_jingdong_common_utils_BitmapkitUtils_getSignFromJni.js
const moduleName = 'libjdbitmapkit.so'
let baseAddr = Module.findBaseAddress(moduleName)
let getSignFromJni = baseAddr.add(0x2EA8 + 1)
Interceptor.attach(getSignFromJni, {
onEnter: function (args) {
// pass
},
onLeave: function (retval) {
// pass
},
})
再配合 IDA 分析 即可还原

q交流: MTc2ODEzMzM5Mw==




















 611
611











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








