0x01题目
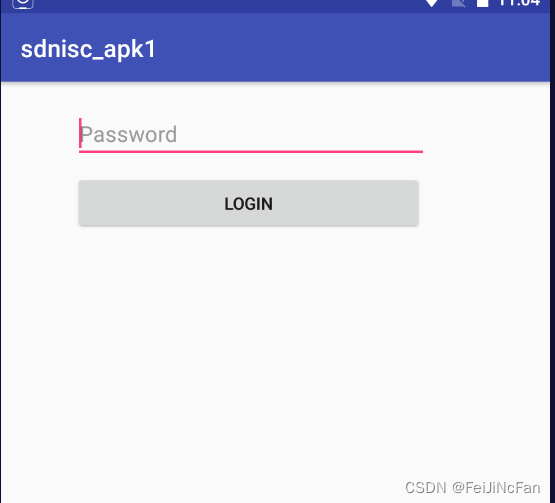
apk运行结果:
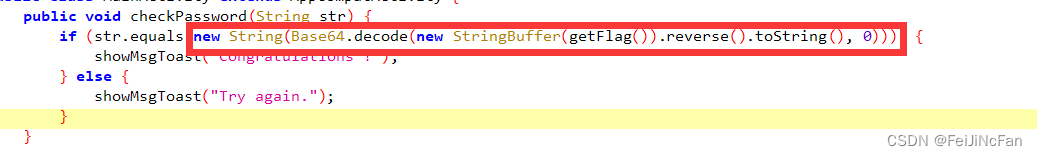
jadx反编译后:
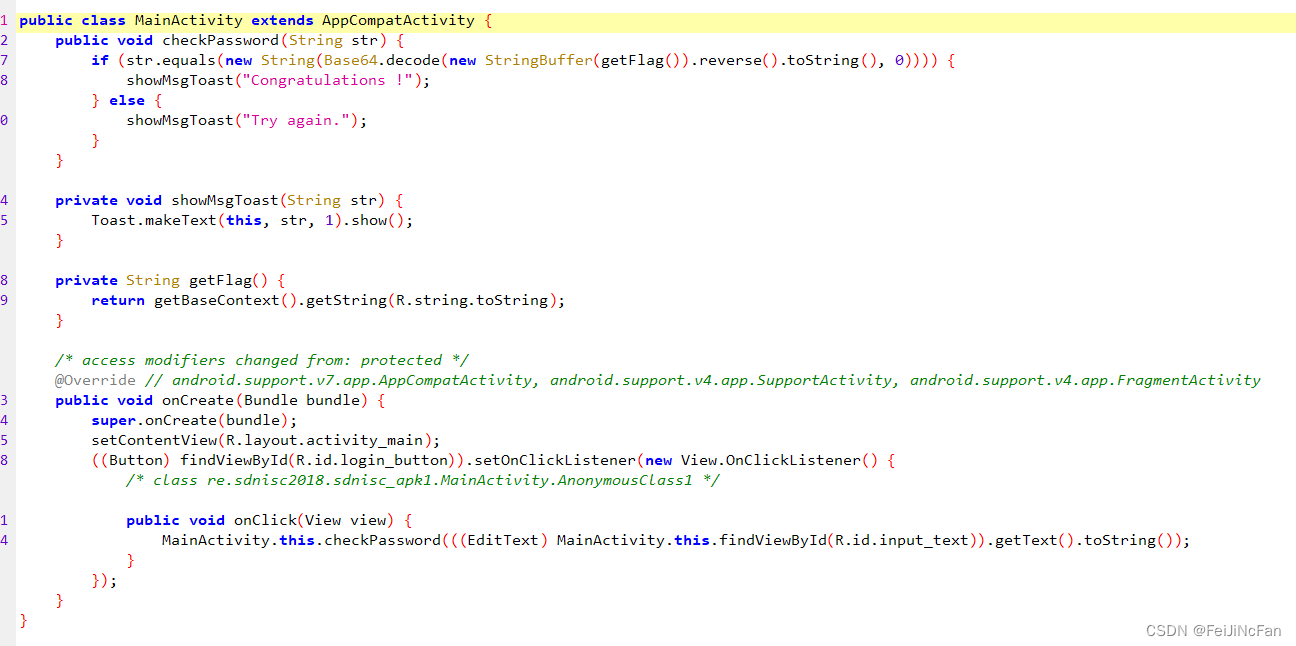
可以看到只要拿到getFlag后的结果逆序经过b64decode即可
可以在res下找到tostring字符,但是我这里选择使用frida来尝试一下
0x02启动frida
1.adb shell 进入/data/local/tmp 后运行frida-server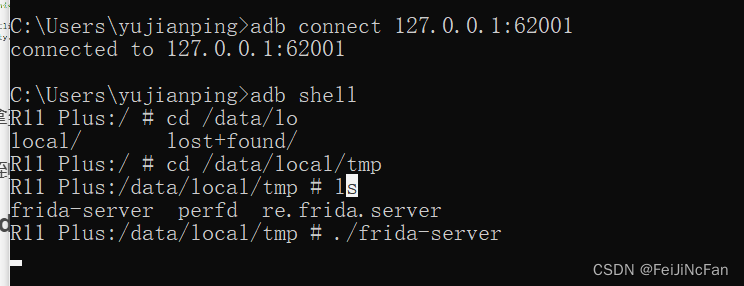
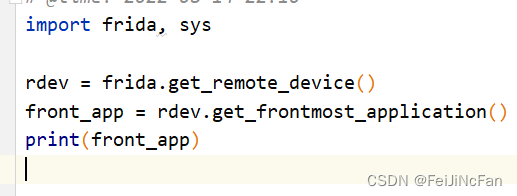
2.获取进程pid
运行app后,运行如下代码

0x03hook代码
因为这里比较简单我直接放代码了
hook1
import frida, sys
rdev = frida.get_remote_device()
front_app = rdev.get_frontmost_application()
print(front_app)
def on_message(message, data):
if message['type'] == 'send':
print("[*] {0}".format(message['payload']))
else:
print(message)
jscode_hook = """
Java.perform(
function(){
console.log("1. start hook");
var MainActivity = Java.use("re.sdnisc2018.sdnisc_apk1.MainActivity");
if (MainActivity != undefined) {
console.log("2. find class");
MainActivity.getFlag.implementation = function () {
var res = this.getFlag();
console.log("计算result:" + res);
return res;
}
}
}
)
"""
#
process = frida.get_usb_device().attach(6654)
script = process.create_script(jscode_hook)
script.on('message', on_message)
print('[*] Hook Start Running')
script.load()
sys.stdin.read()

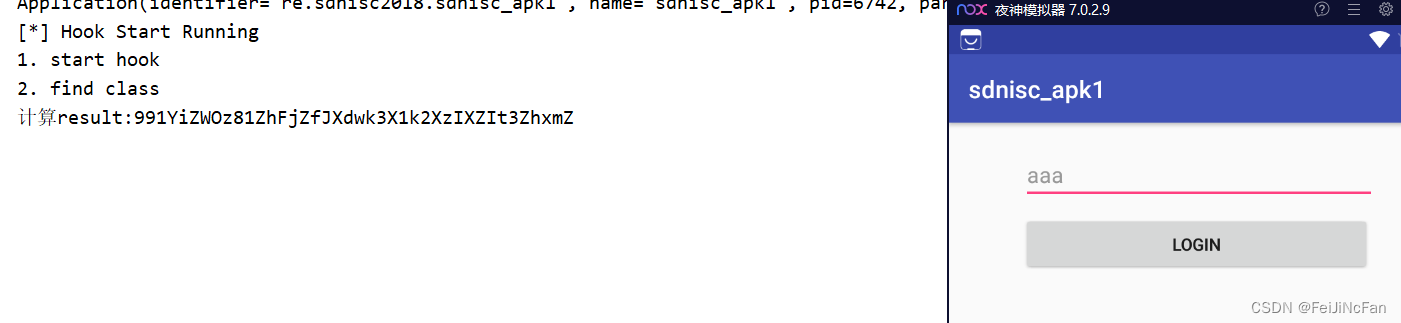
991YiZWOz81ZhFjZfJXdwk3X1k2XzIXZIt3ZhxmZ
hook2
我们来直接hook equals的参数内容
python代码:
import frida,sys
def on_message(message, data):
if message['type'] == 'send':
print("[*] {0}".format(message['payload']))
else:
print(message)
rdev = frida.get_remote_device()
front_app = rdev.get_frontmost_application()
print(front_app)
jscode_hook = """
console.log("script loaded successfully")
Java.perform(function(){
var String = Java.use('java.lang.String')//定位到要hook的类名
String.equals.implementation = function (arg1) {//equals就是我们要hook的函数
console.log("your input : " + this.toString());
console.log("flag -> " + arg1);//打印出来真实的解锁码
var ret = this.equals(arg1);
return ret;//返回值
}
})
"""
process = frida.get_usb_device().attach(4639)
script = process.create_script(jscode_hook)
script.on('message', on_message)
print('[*] Hook Start Running')
script.load()
sys.stdin.read()
点击


0x04结语
frida的作用远不止于此,后续遇到较难分析的过程,可以选择frida来获取最终结果






















 5022
5022











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








