思维导图:


1、重定向练习:将根目录下的文件的文件名写入/test/file文件中
[root@localhost test]# ls / #查看更目录下的文件名
bin dev home lib64 mnt proc run srv test usr
boot etc lib media opt root sbin sys tmp var
[root@localhost test]# ls / > file #使用重定向将文件名存到file文件中
[root@localhost test]# cat file #查看file文件
bin
boot
dev
etc
home
lib
lib64
media
mnt
opt
proc
root
run
sbin
srv
sys
test
tmp
usr
var2、vim命令练习:将/root/.bashrc文件内容读入/test/bashrc,删除#号开头的行内容
[root@localhost test]# cat /root/.bashrc #查看
# .bashrc
# User specific aliases and functions
alias rm='rm -i'
alias cp='cp -i'
alias mv='mv -i'
# Source global definitions
if [ -f /etc/bashrc ]; then
. /etc/bashrc
fi
[root@localhost test]# cat /root/.bashrc >> bashrc #将/root/.bashrc读入bashrc
[root@localhost test]# cat bashrc #查看bashrc
# .bashrc
# User specific aliases and functions
alias rm='rm -i'
alias cp='cp -i'
alias mv='mv -i'
# Source global definitions
if [ -f /etc/bashrc ]; then
. /etc/bashrc
fi
[root@localhost test]# vim /root/.bashrc #进入编辑,删除#开头的行内容
在命令行输入 :g/#/d 然后enter,就删除了含有#的行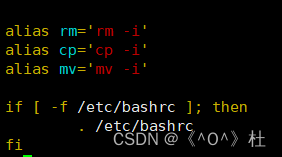
3、查看/etc/selinux/config 以 SELINUX开头的行
[root@localhost ~]# cat /etc/selinux/config
# This file controls the state of SELinux on the system.
# SELINUX= can take one of these three values:
# enforcing - SELinux security policy is enforced.
# permissive - SELinux prints warnings instead of enforcing.
# disabled - No SELinux policy is loaded.
SELINUX=enforcing
# SELINUXTYPE= can take one of these three values:
# targeted - Targeted processes are protected,
# minimum - Modification of targeted policy. Only selected processes are protected.
# mls - Multi Level Security protection.
SELINUXTYPE=targeted
[root@localhost ~]# grep ^[SELINUX] /etc/selinux/config
SELINUX=enforcing
SELINUXTYPE=targeted4、文本处理命令:使用cut命令将当前主机的ip地址切割显示
[root@localhost ~]# ip a show ens160 | grep inet -w| tr -s " " | cut -d " " -f 3
192.168.41.129/24




















 727
727











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








