IPsec VPN 精致版
配置前注意事项:
-
本实验路由器两端地址固定,采用IKE的主模式进行 //野蛮模式适用于两端地址不固定采用动态地址
//所有提到的缺省配置都可以省略
实验需求:
-
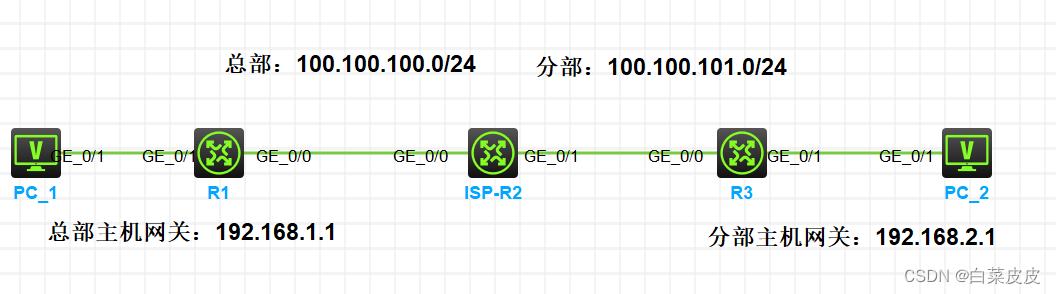
R1模拟总部,R3模拟分部,因业务需要两端内网需要通过VPN相互访问
IP地址规划如下,主机1 GE0/0为.1,R2 GE0/0为.2,R2 GE0/1为.2,R3 GE0/0为.3,以设备名数字为IP地址
配置流程与思路
首先保证路由可达,总部和分部各配置一条缺省路由至互联网
1、ike提议
2、IKE密钥
3、IKE绑定
4、acl
5、ipsec提议
6、ipsec绑定
7、调用
首先建立IKE对等体隧道,内部建立IPsec隧道,形成外层保护内层
-
R1基础配置
<H3C>sys System View: return to User View with Ctrl+Z. [H3C]sysn R1 [R1] [R1]int g0/1 [R1-GigabitEthernet0/1]ip add 192.168.1.1 24 [R1-GigabitEthernet0/1]int g 0/0 [R1-GigabitEthernet0/0]ip add 100.100.100.1 24 [R1-GigabitEthernet0/0]qu [R1]ip rou [R1]ip route-s [R1]ip route-static 0.0.0.0 0 100.100.100.2 [R1]ike proposal 1 //IKe提议 [R1-ike-proposal-1]encryption-algorithm 3des [R1-ike-proposal-1]encryption-algorithm 3des-cbc //缺省为CBC模式的56-bit DES加密算法 [R1-ike-proposal-1]authentication-algorithm sha512 //缺省为HMAC-SHA1认证算法 [R1-ike-proposal-1]dh group1 //缺省为group1 [R1-ike-proposal-1]qu [R1] [R1]ike keychain 1 [R1-ike-keychain-1]pre-shared-key address 100.100.101.3 key simple 123456 #创建IKE密钥,地址填写分部侧设备的公网IP,密码设置为123456。 [R1-ike-keychain-1]qu [R1]ike profile 1 创建IKE安全框架 [R1-ike-profile-1]keychain 1 [R1-ike-profile-1]proposal 1 [R1-ike-profile-1]local-identity address 100.100.100.1 #缺省情况下,未配置本端身份信息。此时使用系统视图下通过ike identity命令配置的身份信息作为本端身份信息。若两者都没有配置,则使用IP地址标识本端的身份,该IP地址为IPsec安全策略或IPsec安全策略模板应用的接口的IP地址。 [R1-ike-profile-1]match remote identity address 100.100.101.3 [R1-ike-profile-1]qu [R1] [R1]acl advanced 3001 [R1-acl-ipv4-adv-3001]rule permit ip source 192.168.1.0 0.0.0.255 destination 192.168.2.0 0.0.0.255 [R1] [R1]ipsec transform-set 1 protocol { ah | ah-esp | esp }缺省情况下,采用ESP安全协议。 [R1-ipsec-transform-set-1]encapsulation-mode tunnel #缺省为隧道模式 [R1-ipsec-transform-set-1]esp encryption-algorithm aes-cbc-128 加密 [R1-ipsec-transform-set-1]esp authentication-algorithm sha1 认证 [R1-ipsec-transform-set-1] [R1]ipsec policy 1 10 isa IPSEC安全策略 名字1,节点10 [R1]ipsec policy 1 10 isakmp [R1-ipsec-policy-isakmp-1-10]ike-profile 1 [R1-ipsec-policy-isakmp-1-10]security acl 3001 [R1-ipsec-policy-isakmp-1-10]transform-set 1 [R1-ipsec-policy-isakmp-1-10]local-address 100.100.100.1 #可省略,有缺省配置 [R1-ipsec-policy-isakmp-1-10]remote-address 100.100.101.3 [R1-ipsec-policy-isakmp-1-10] [R1-ipsec-policy-isakmp-1-10]int g0/0 [R1-GigabitEthernet0/0]ipsec apply policy 1 接口调用
ISP_R2
<H3C>sys
System View: return to User View with Ctrl+Z.
[H3C]sysn ISP_R2
[ISP_R2]int g 0/0
[ISP_R2-GigabitEthernet0/0]ip add 100.100.100.2 24
[ISP_R2-GigabitEthernet0/0]qu
[ISP_R2]int g 0/1
[ISP_R2-GigabitEthernet0/1]ip add 100.100.101.2 24
[ISP_R2-GigabitEthernet0/1]
R3
<H3C>sys
System View: return to User View with Ctrl+Z.
[H3C]sysn R3
[R3]int g 0/0
[R3-GigabitEthernet0/0]ip add 100.100.101.3 24
[R3-GigabitEthernet0/0]int g 0/1
[R3-GigabitEthernet0/1]ip add 192.168.2.1 24
[R3-GigabitEthernet0/1]qu
[R3]ip route-static 0.0.0.0 0 100.100.101.2
[R3-ike-proposal-1]encryption-algorithm 3des-cbc
[R3-ike-proposal-1]authentication-algorithm sha512
[R3-ike-proposal-1]dh group1
[R3-ike-proposal-1]qu
[R3]ike key
[R3]ike keychain 1
[R3-ike-keychain-1]pre-shared-key address 100.100.100.1 key simple 123456
[R3-ike-keychain-1]qu
[R3]acl advanced 3001
[R3-acl-ipv4-adv-3001]rule permit ip source 192.168.2.0 0.0.0.255 destination 19
2.168.1.0 0.0.0.255
quit
[R3-acl-ipv4-adv-3001]
[R3]ike profile 1
[R3-ike-profile-1]keychain 1
[R3-ike-profile-1]proposal 1
[R3-ike-profile-1]match remote identity address 100.100.100.1
[R3-ike-profile-1]qu
[R3]ipsec transform-set 1
[R3-ipsec-transform-set-1]esp encryption-algorithm aes-cbc-128
[R3-ipsec-transform-set-1]esp authentication-algorithm sha1
[R3-ipsec-transform-set-1]qu
[R3]ipsec policy 1 10 isakmp
[R3-ipsec-policy-isakmp-1-10]ike-profile 1
[R3-ipsec-policy-isakmp-1-10]security acl 3001
[R3-ipsec-policy-isakmp-1-10]transform-set 1
[R3-ipsec-policy-isakmp-1-10]remote-address 100.100.100.1
[R3-ipsec-policy-isakmp-1-10]int g 0/0
[R3-GigabitEthernet0/0]ipsec apply policy 1
[R3-GigabitEthernet0/0]qu






















 4818
4818











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








